Running monitoring method of application system
A technology of operation monitoring and application system, applied in the field of IT operation and maintenance, can solve problems such as waste of manpower, inability to understand accurately and timely, subtle abnormalities are not obvious, and achieve powerful effects
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
specific Embodiment approach 1
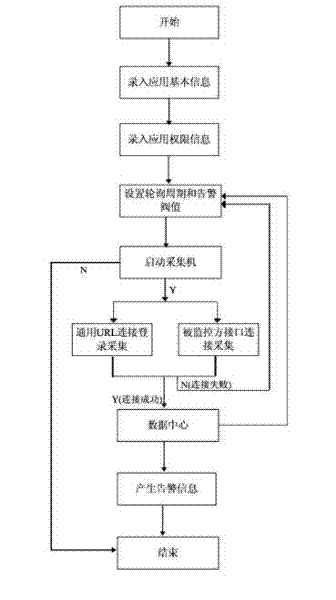
[0031] The present invention will be further described below in conjunction with the accompanying drawings
[0032] like figure 1 As shown, the general URL connection login method is used to collect Tomcat data. The steps to operate on the monitoring system are: 1) Select the type of Tomcat application to be monitored in the monitoring server, and enter the relevant basic information and permission login information of the application to be monitored. Including IP address, port number, background login account and password; 2) Set the monitoring collection timing polling cycle and alarm threshold filtering rules on the input monitoring information, such as setting the polling cycle to the default 10 minutes, Tomcat's current memory valve The value is 500M-1G for the warning level, 1G-1.5G for the severity level, etc.; 3) On the monitoring server, according to the application monitoring configuration information, start the monitoring program of the corresponding application ty...
specific Embodiment approach 2
[0035] The present invention will be further described below in conjunction with the accompanying drawings
[0036] The data collection of IIS application is carried out by SNMP. The collection steps are: 1) Select the type of IIS application to be monitored in the monitoring server, and enter the relevant basic information and permission login information of the application to be monitored, including IP address, port number, community word etc.; 2) Set the monitoring collection timing polling collection mode and the alarm threshold filtering rules of the monitoring indicators on the input monitoring information, such as setting the polling period to the default 10 minutes, the minimum number of bytes processed per second received by IIS, The indicators such as the highest number of bytes processed and received per second are set to different value segments as different alarm levels; 3) On the monitoring server, according to the application monitoring configuration information,...
specific Embodiment approach 3
[0039] The present invention will be further described below in conjunction with the accompanying drawings
[0040] The mailbox data collection of the mail server is carried out through the POP3 protocol. The collection steps are: 1) Select the type of POP3 application to be monitored in the monitoring server, and enter the relevant basic information and permission login information of the application to be monitored, including the mailbox IP address and port. 2) On the input monitoring information, set the monitoring collection timing polling period and the alarm threshold filtering rules for monitoring indicators, such as setting the polling period to the default 10 minutes, and setting the mailbox connection time and other indicators. Different value segments have different alarm levels; 3) On the monitoring server, according to the application monitoring configuration information, start the monitoring program of the corresponding application type for data collection; 4) Dat...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More