Method, device and virtual machine for detecting rogue program
A malicious program and virtual machine technology, applied in the field of information security, can solve the problem of undetectable deformed malicious programs, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
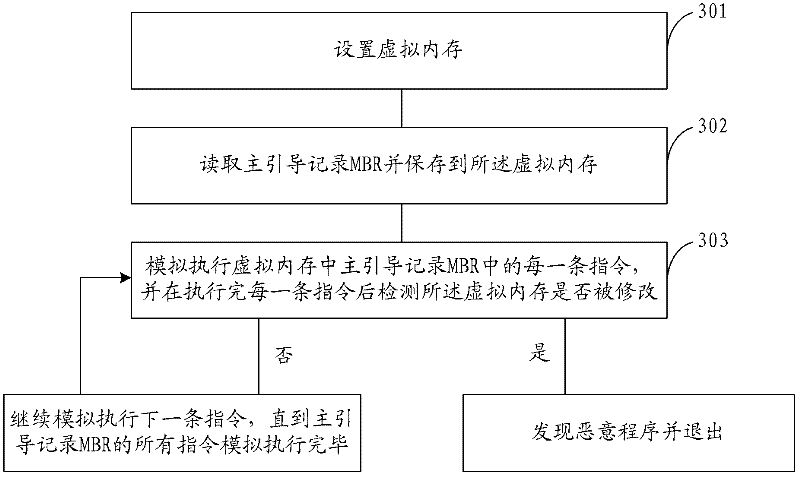
[0052] In order to make the above objects, features and advantages of the present application more obvious and comprehensible, the present application will be further described in detail below in conjunction with the accompanying drawings and specific implementation methods.
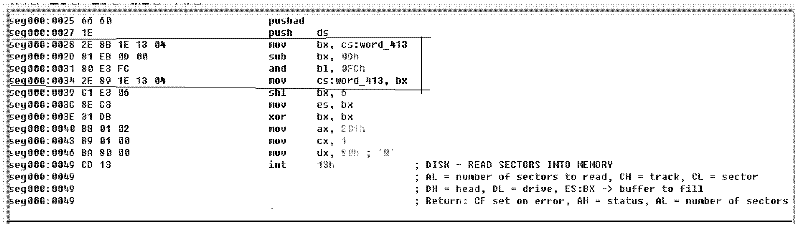
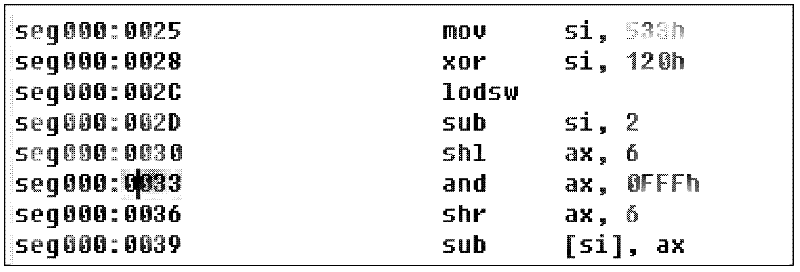
[0053] For the detection of malicious programs, especially for the detection of malicious programs such as MBR-based Bootkit or viruses similar to Bootkit, the present application proposes a detection method, which can detect these malicious programs no matter what kind of deformation they have.
[0054] Below at first introduce the thinking that this application proposes, as follows:
[0055] Under normal circumstances, the boot process of a computer system is:
[0056] Power-on self-test --> Mainboard BIOS starts from floppy disk, hard disk or CD-ROM according to user-specified startup sequence --> System BIOS reads Master Boot Record (MBR) into memory --> Hands over control to master boot program --> ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More