Method and system for realizing private VPLS (virtual private LAN (local area network) service)
A business and traffic technology, applied in the field of communication, can solve problems such as not supporting mutual isolation of nodes, increasing system burden and management complexity, and achieving the effect of ensuring business security and flexible networking applications
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
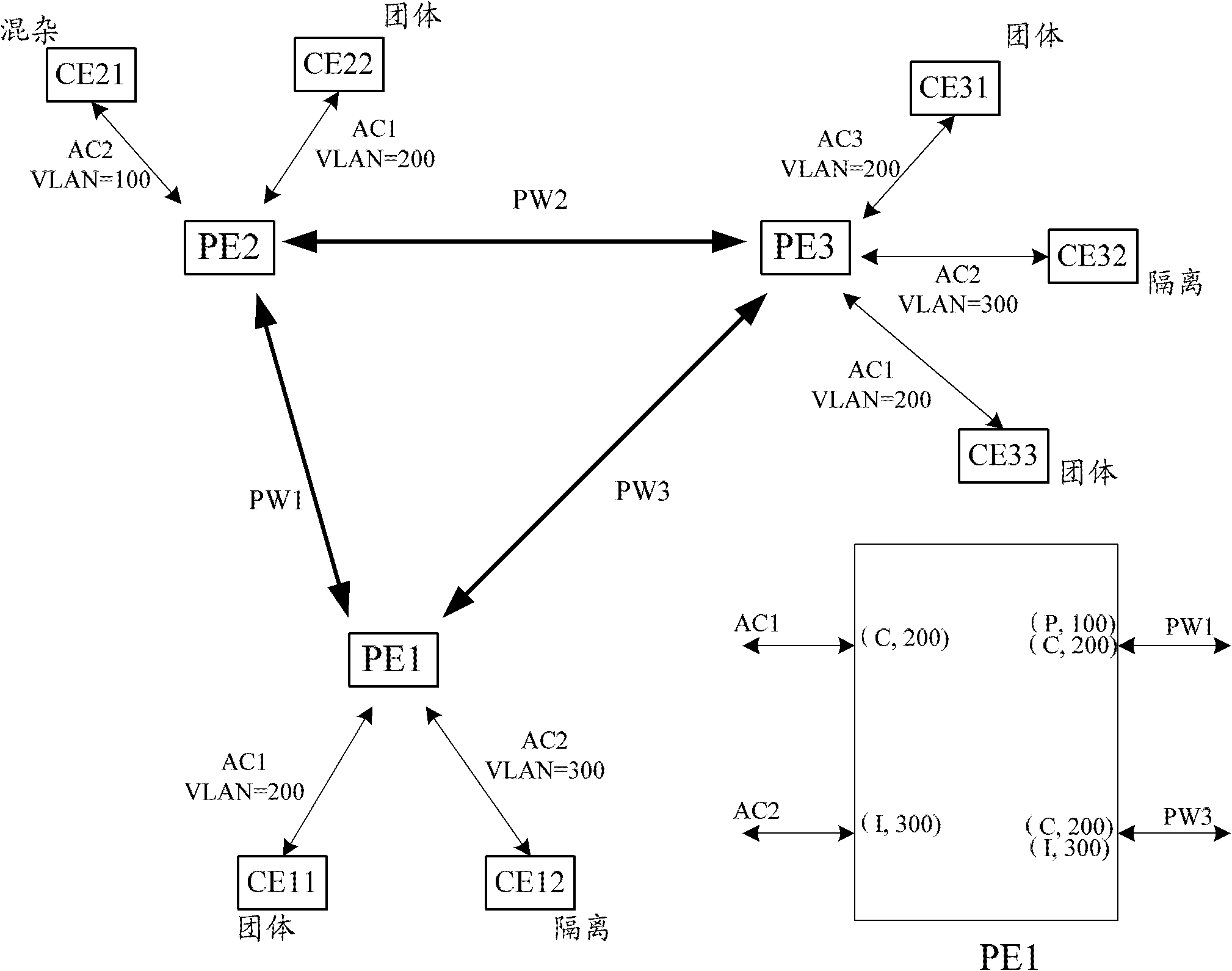
[0068] refer to figure 1 In this embodiment, CE12 and CE32 are isolated, that is, CE12 and CE32 are isolated from each other, and CE12 and CE32 can only communicate with CE21; CE11, CE31, CE33 and CE22 form a community, that is, CE11, CE31, CE33 and CE22 can communicate with each other. It can also communicate with CE21, but cannot communicate with the isolated nodes CE12 and CE32; PE21 is Promiscuous, equivalent to a sink node, all users can communicate with PE21, and communicate with the upper core device or server through PE21.
[0069] For example, PE1 is connected to CE11 and CE12. The attribute of CE12 is isolated, and the attribute of CE11 is community. The specific processing flow is as follows:
[0070] (1) When PE1 receives user traffic from CE11, the corresponding AC attribute is community, that is, PE1 can communicate with the AC with the same attribute as the local PE or remote PE, and can also communicate with promiscuous. Therefore, on the local PE, PE1 needs ...
Embodiment 2
[0077] refer to figure 2 , this embodiment is a subset of Embodiment 1. In this embodiment, CE21 is the root node (promicuous), and other ACs are leaf nodes (isolated); for example, on the PE1 device, the specific processing flow is as follows:
[0078] (1) When PE1 receives user traffic from CE11, the corresponding AC attribute is leaf (isolated), that is, PE1 can only communicate with AC2 of remote PE2, and is isolated from the local AC and ACs of other PEs; according to the local The AC mapping table finds the corresponding egress as PW1; in addition, the local AC1 and AC2 need to be isolated, which can be isolated through VLAN inspection at the L2 layer;
[0079] (2) When PE1 receives leaf AC traffic from PE2 or PE3, according to the local AC mapping table, it cannot be forwarded from the local AC, and traffic isolation can be realized through L2VLAN inspection;
[0080] (3) When PE1 receives the traffic of the remote rootAC from PE2, since the encapsulated VLAN ID=100,...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More