Multi-network environment isolation method and terminal
A multi-network environment and terminal technology, applied in the multi-network environment isolation method and terminal field, can solve problems such as the inability to solve terminal data security well, and achieve the effects of meeting security isolation requirements, anti-virus data leakage, and simple deployment.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
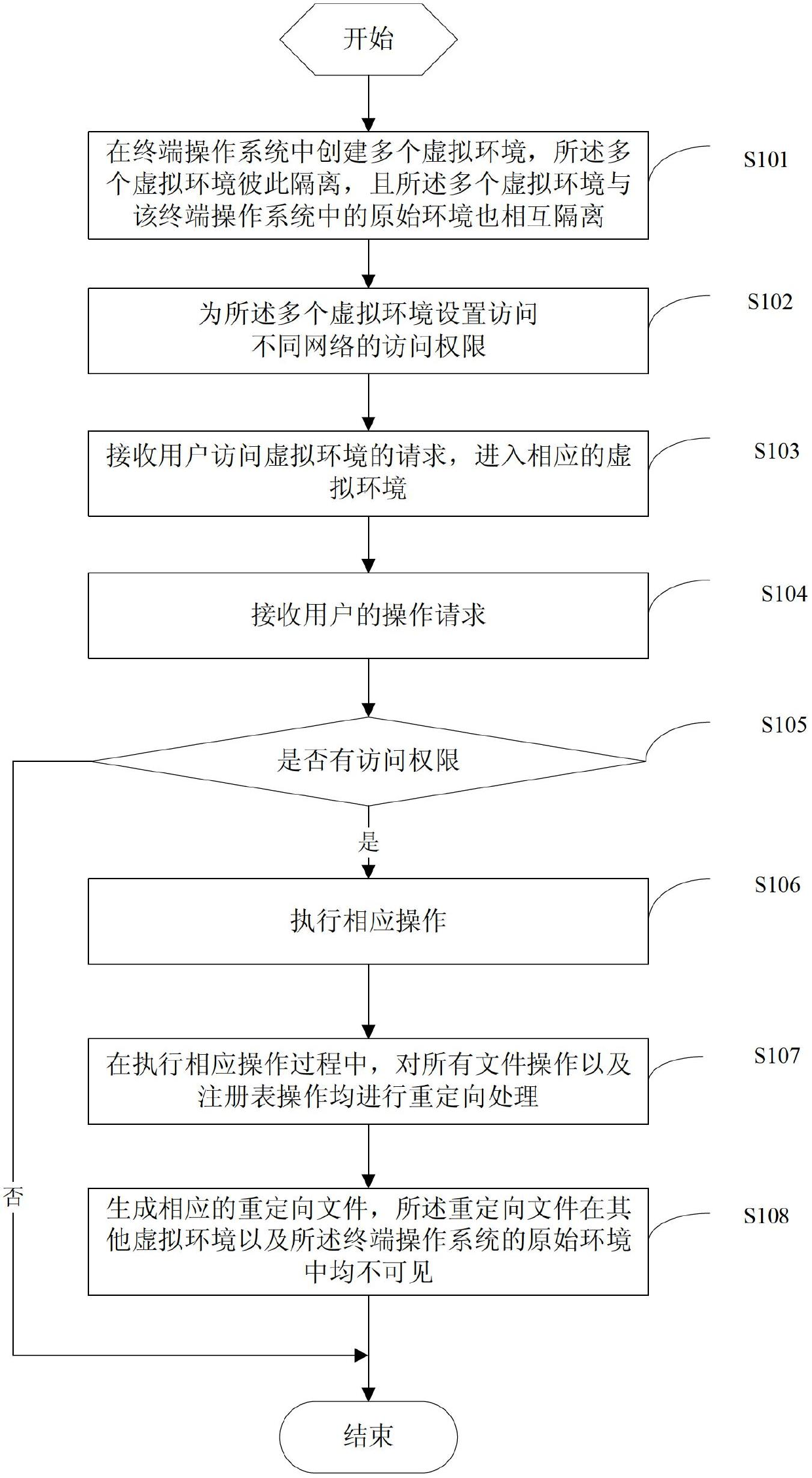
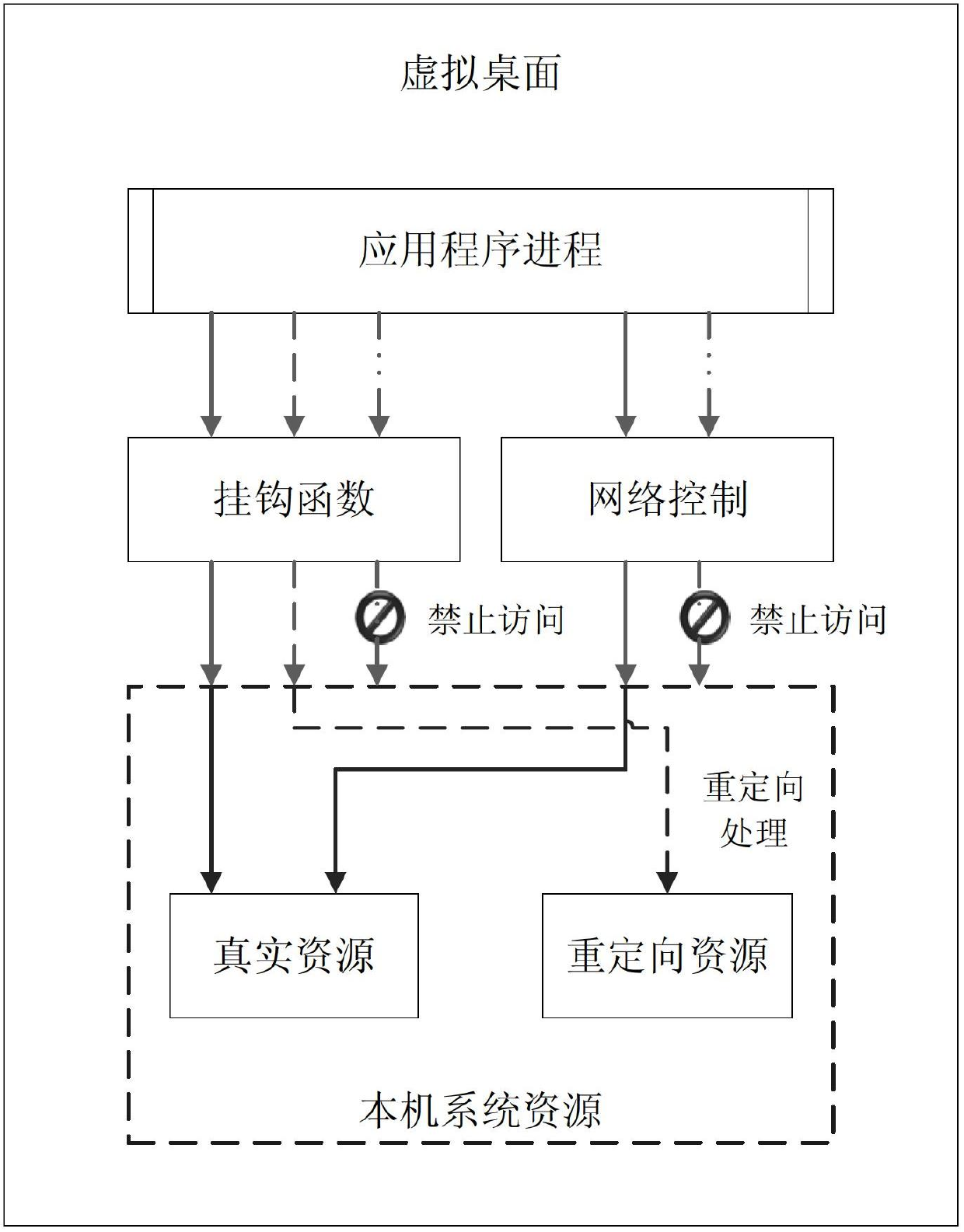
[0046] In order to make the objectives, technical solutions and advantages of the present invention clearer, the following further describes the present invention in detail with reference to the accompanying drawings and embodiments. It should be understood that the specific embodiments described herein are only used to explain the present invention, but not to limit the present invention.
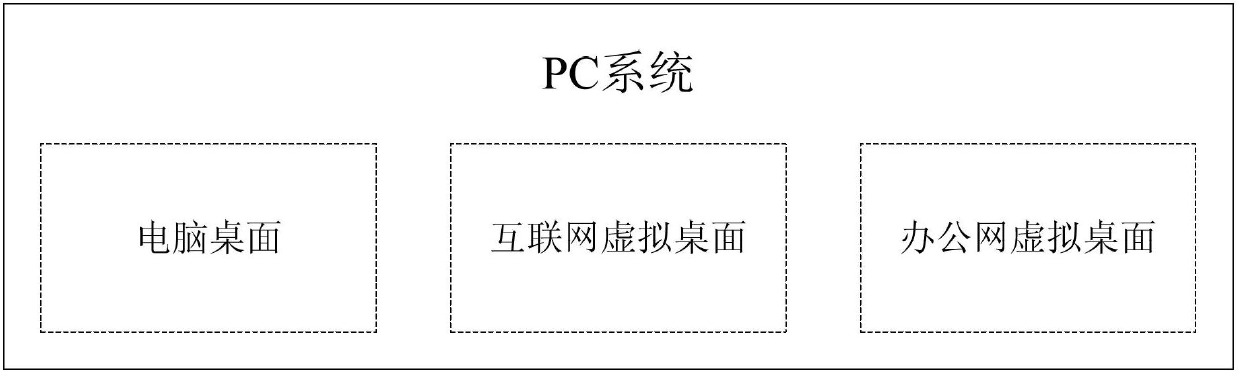
[0047] In the embodiment of the present invention, multiple isolated virtual environments are set in the same terminal, and different virtual environments are connected to different networks, thereby effectively ensuring data security in a multi-network environment, and is convenient for users to use, and reduces implementation costs. . The terminal in the embodiment of the present invention may be a personal PC or a mobile terminal such as a laptop computer and a smart phone. The following embodiments take a personal PC terminal as an example.
[0048] The multi-network environment isolation ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More