Method for pre-authentication and pre-configuration, and system thereof
A pre-configured and pre-authentication technology, applied in security devices, wireless communications, electrical components, etc., can solve problems such as inability to reduce delays, and achieve the effect of improving quality
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
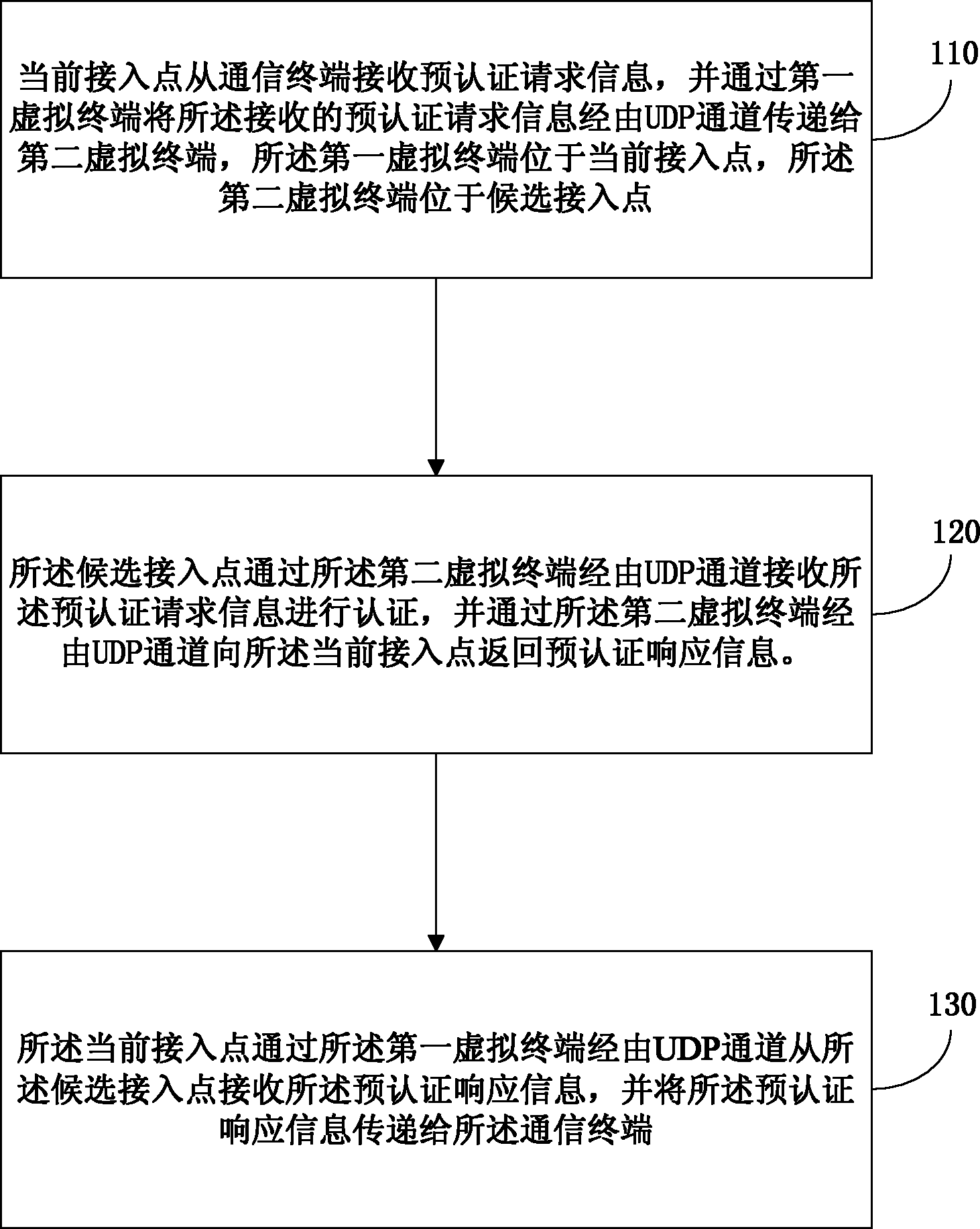
[0052] In order to make the object, technical solution and advantages of the present invention more clear, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
[0053] image 3 is a flowchart of a pre-authentication method for cross-subnet handover according to an embodiment of the present invention. In this embodiment, the pre-authentication method for inter-subnet handover starts at step 110 .
[0054] In step 110, the current access point receives the pre-authentication request information from the communication terminal, and transmits the received pre-authentication request information to the second virtual terminal through the UDP channel through the first virtual terminal, wherein the first virtual terminal is located at the current access point....
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More