Method, device and browser for protecting webpage against malicious attack
A malicious attack, webpage technology, applied in computer security devices, instruments, electrical digital data processing, etc., can solve problems such as webpage Trojan horse attacks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0039] In order to make the above objects, features and advantages of the present application more clearly understood, the present application will be described in further detail below with reference to the accompanying drawings and specific embodiments.
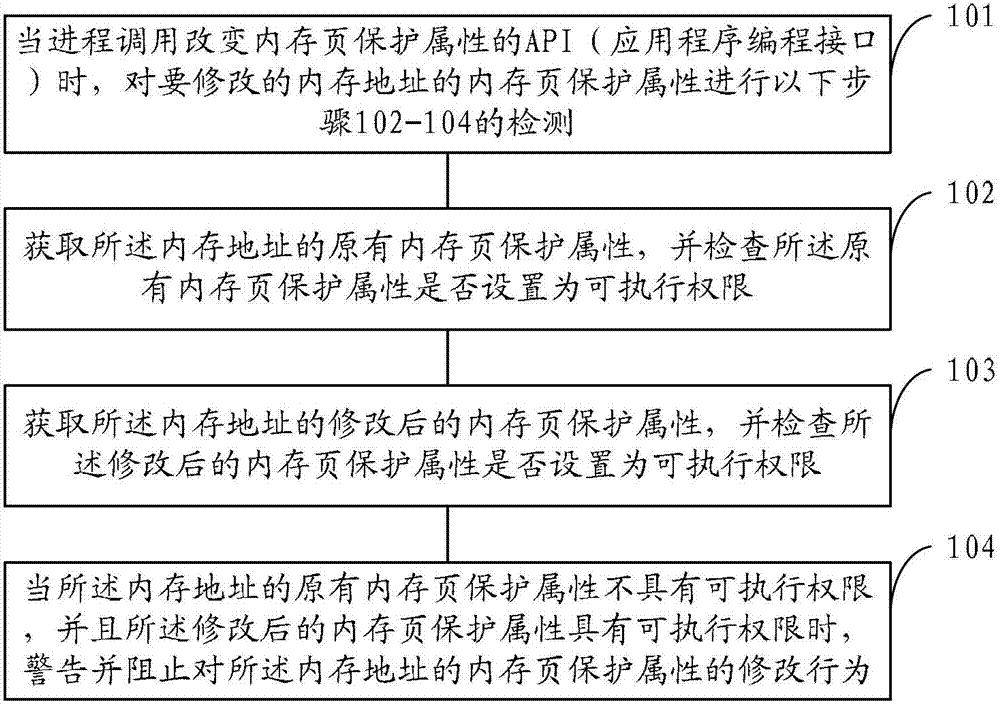
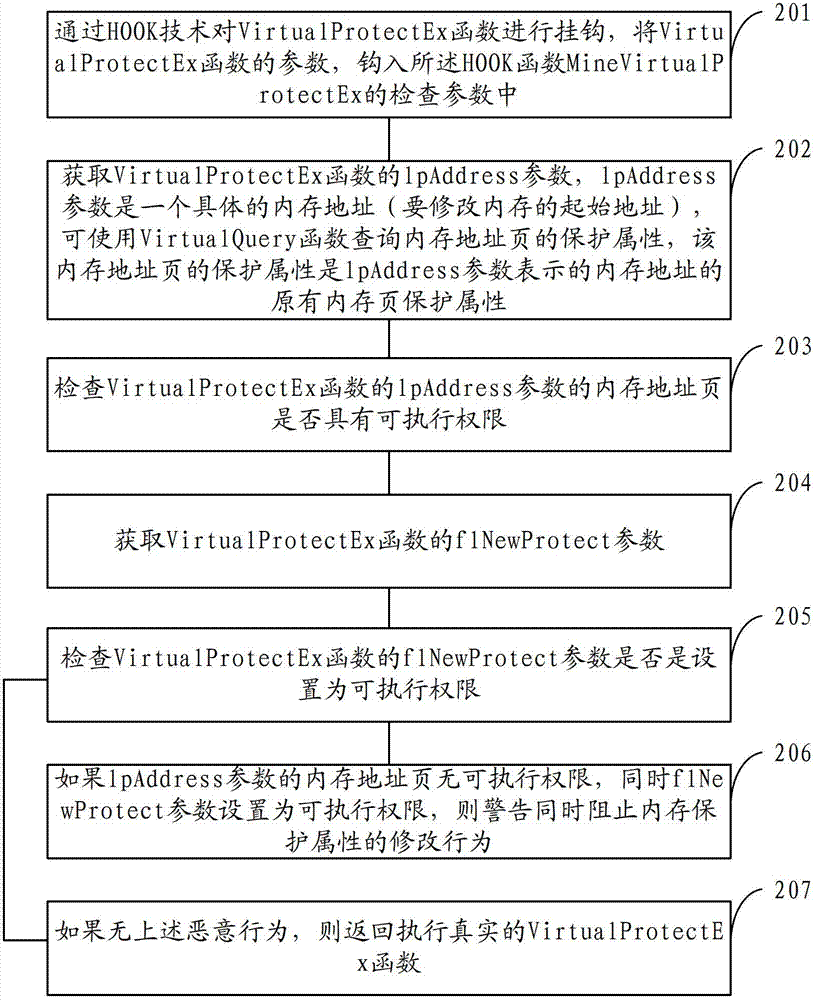
[0040] In order to solve the problem that attackers use ROP technology (return-oriented programming technology) to bypass DEP (Data Execution Prevention) to conduct web Trojan horse attacks, the present application first analyzes the process of using ROP technology to conduct malicious attacks, as follows.
[0041] As described in the prior art, DEP (Data Execution Prevention) cannot completely protect system security effectively, and new attack methods are still emerging one after another. Attackers can modify the memory of the memory address where the malicious code shellcode is located by using the ROP technology (return-oriented programming technology). The page protection attribute enables data memory pages to be execute...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More