Access control method base on attribute encryption algorithm
An access control and attribute encryption technology, applied in the field of cloud computing, can solve the problem of no user data file integrity and consistency considerations, to avoid re-encryption work and improve the rate of permission change.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
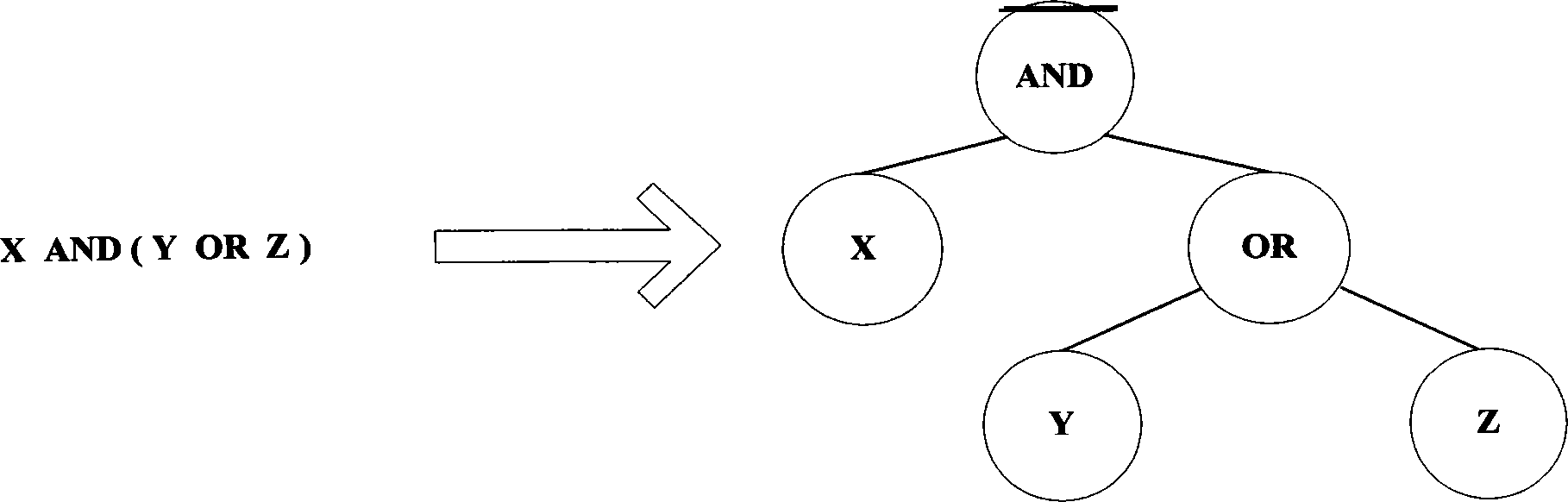
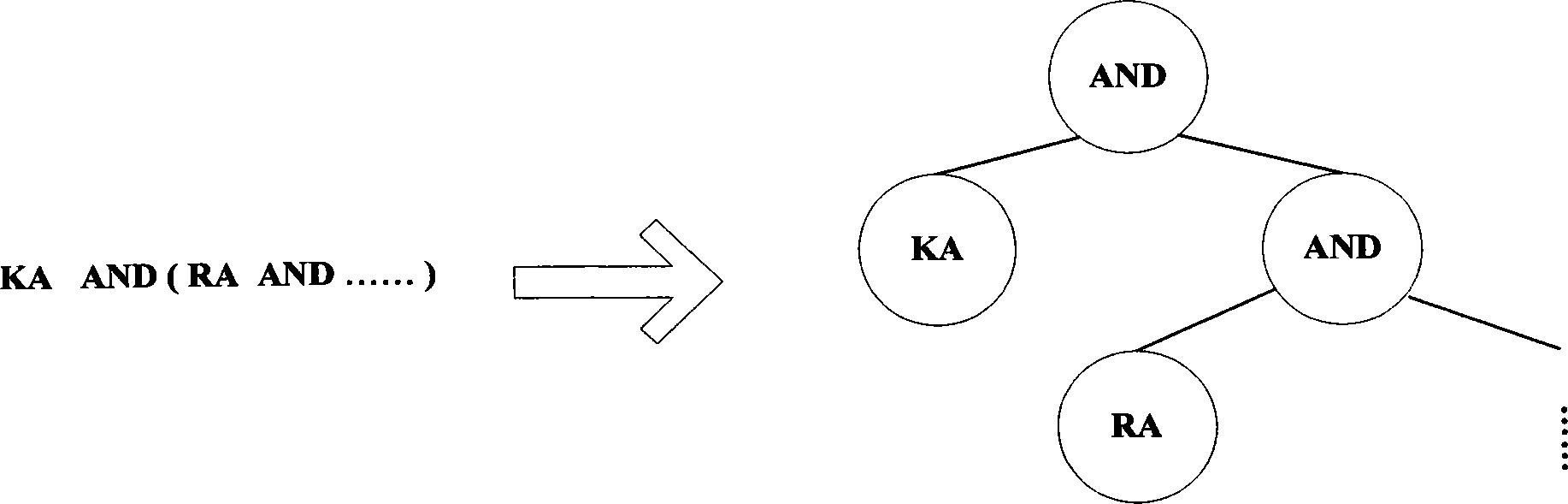
Method used
Image
Examples
Embodiment Construction
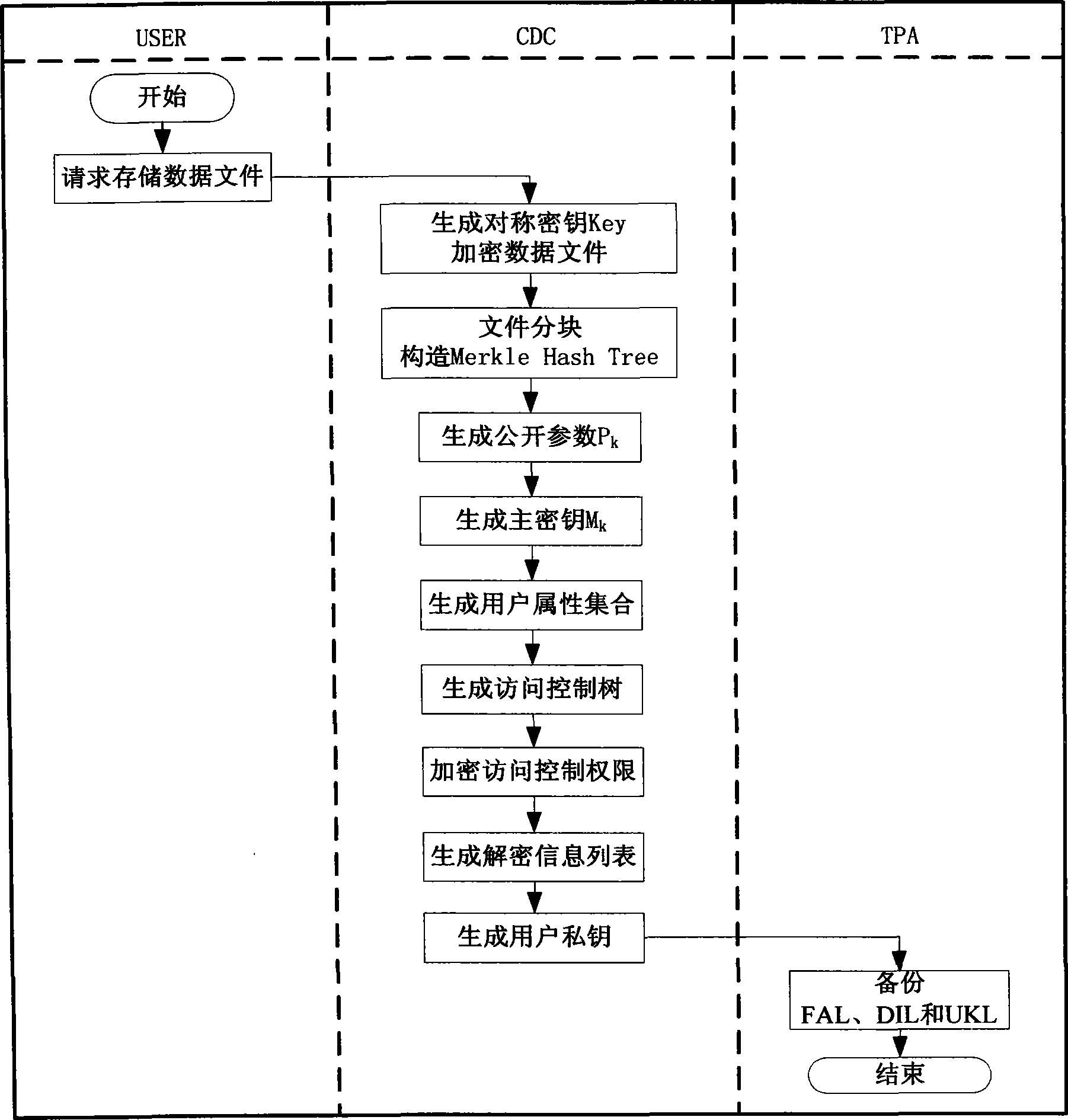
[0049] The technical solution of the present invention will be described in detail below in conjunction with the accompanying drawings and specific embodiments.
[0050] security assumption
[0051] The scheme assumes that there is no malicious packet loss in all communication channels (communication channels include three parts: between USER and CDC, between CDC and TPA, and between TPA and USER). At the same time, the TPA in the scheme is an unbiased and completely credible third-party audit organization, which can faithfully complete all tasks entrusted by USER. The CDC of the present invention is slightly different from the CDC in the previous scheme. Although the CDC in the scheme has curiosity, it can faithfully complete the task and is no longer completely untrustworthy. All parameter calculations, encryption tasks, and key generation and distribution undertaken by CDC can guarantee the absolute correctness, non-deception and non-repudiation of the results. CDC can un...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More