Automatic penetration testing method for information system security
A technology for penetration testing and information systems, applied in the field of automated penetration testing of information system security, it can solve problems such as high degree of manual participation, different data formats, and inability to interact autonomously, so as to improve integrity, efficiency and automation. Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0021] The present invention will be further described below in conjunction with the accompanying drawings.
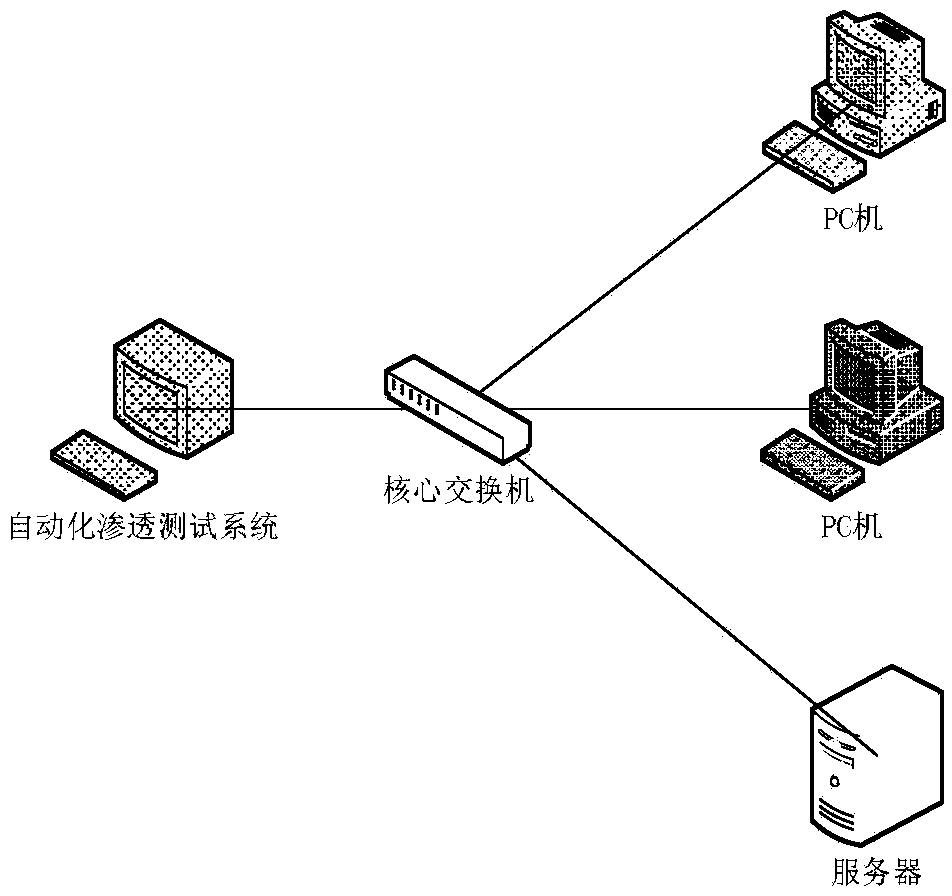
[0022] figure 1 It is a schematic diagram of the experimental configuration for automated penetration testing. The automated penetration testing network is deployed outside the network under test and connected to the LAN through a core switch. The LAN is composed of a server and several hosts. The server provides external services, and the host is connected to the server through the core switch. .
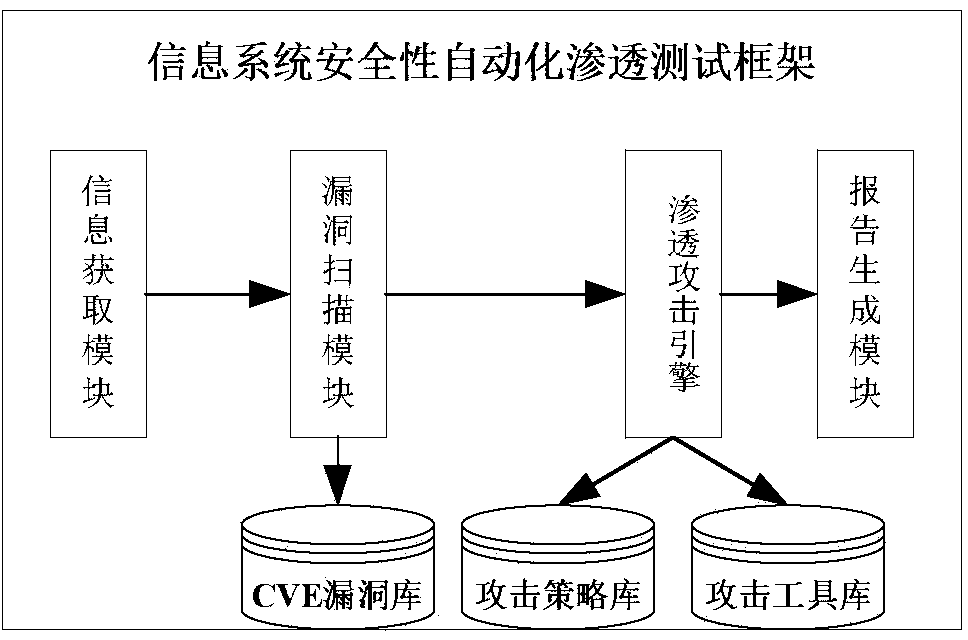
[0023] figure 2 It is a composition block diagram of a software system for realizing the testing method of the present invention, and is mainly composed of an information acquisition module, a vulnerability scanning module, an automatic penetration attack engine, and a report generation module.
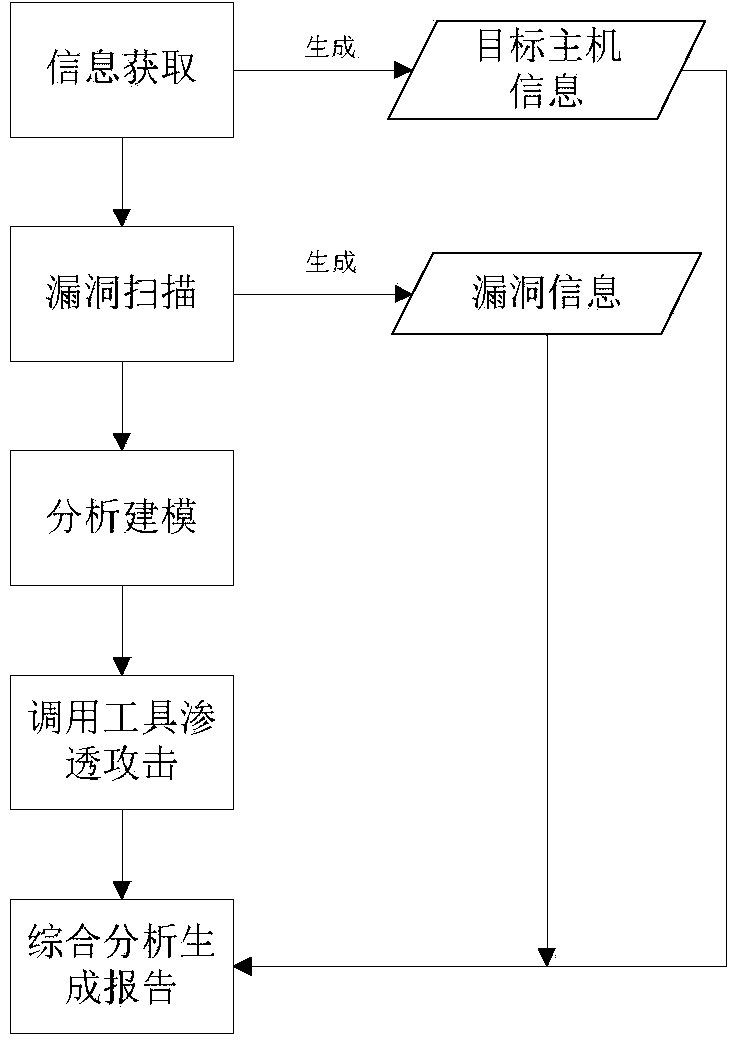
[0024] A flow chart of an automated penetration testing method for information system security is shown in image 3 As shown, it specifically includes the following steps:
[...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More