Information security situation analysis method and system
An analysis method and information security technology, applied in the field of information security situation analysis
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
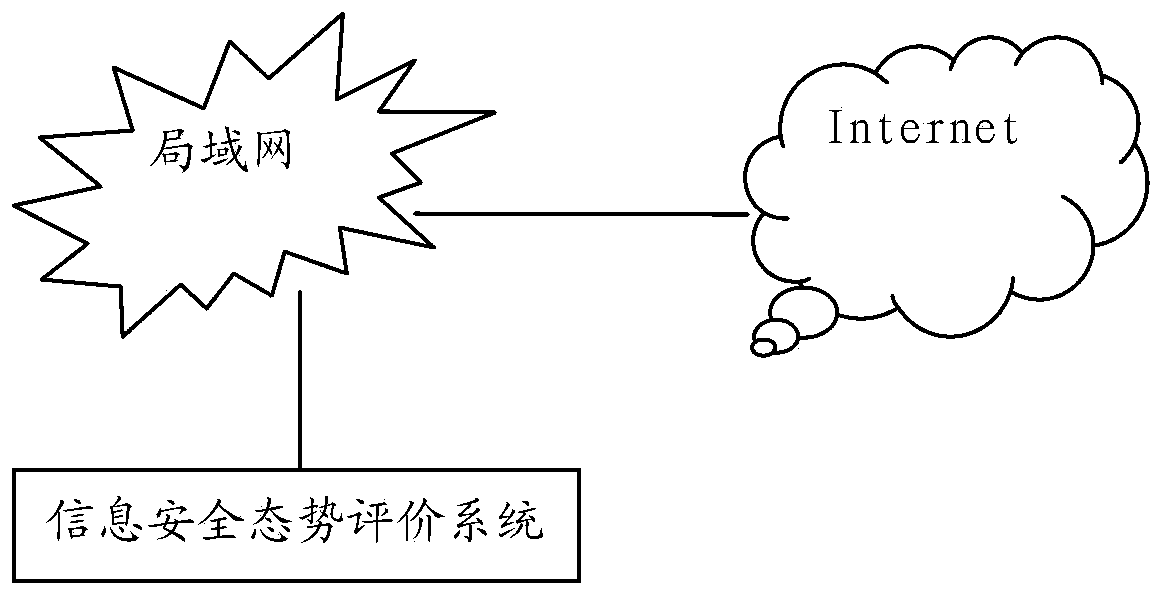
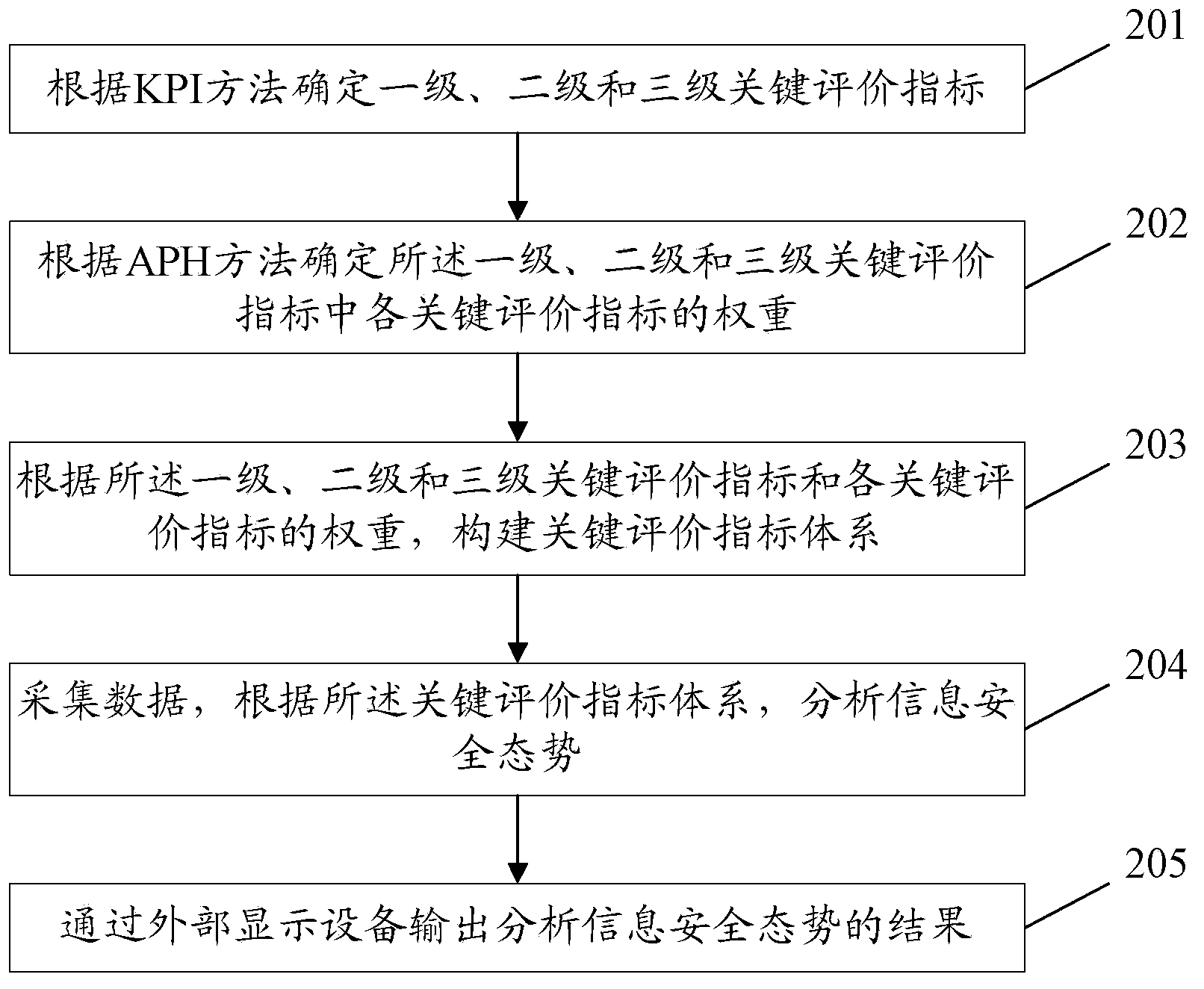
[0108] In order to effectively manage information security, the embodiments of the present invention provide an information security situation analysis method and system. Embodiments of the present invention will be described in detail below in conjunction with the accompanying drawings. It should be noted that, in the case of no conflict, the embodiments in the present application and the features in the embodiments can be combined arbitrarily with each other.
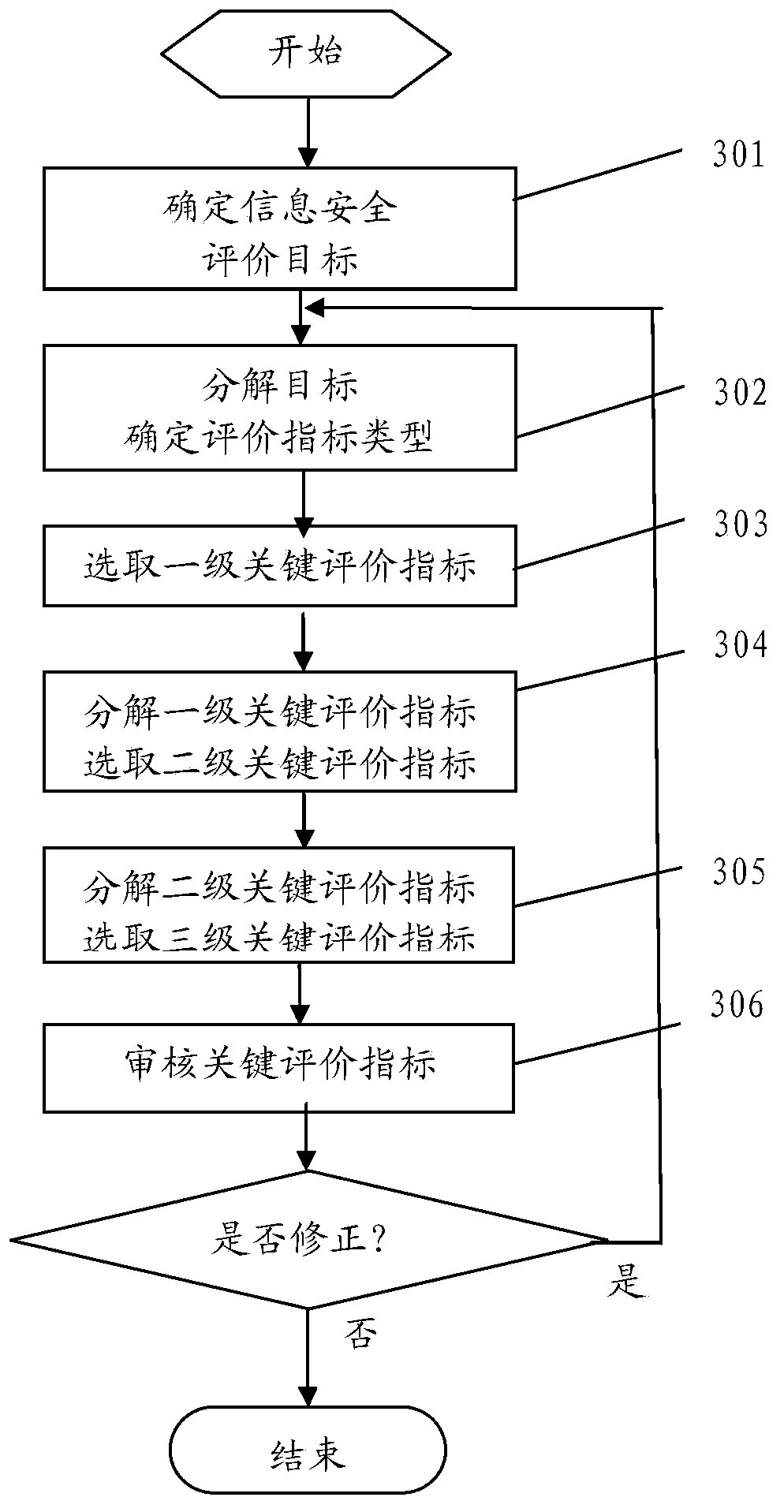
[0109] In order to better describe the technical solutions provided by the embodiments of the present invention, the Key Performance Indicator method (Key Performance Indicator, KPI) and the AHP method are firstly introduced.
[0110] KPI is the basis of enterprise strategy realization and performance management. It is a tool to decompose the enterprise's strategic goals into operational goals. It is set, sampled, calculated, analyzed and measured through the key parameters of the input and output of a certain process w...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More