Security management method and device in cognitive radio system
A technology of cognitive radio and security management, applied in the field of wireless communication
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
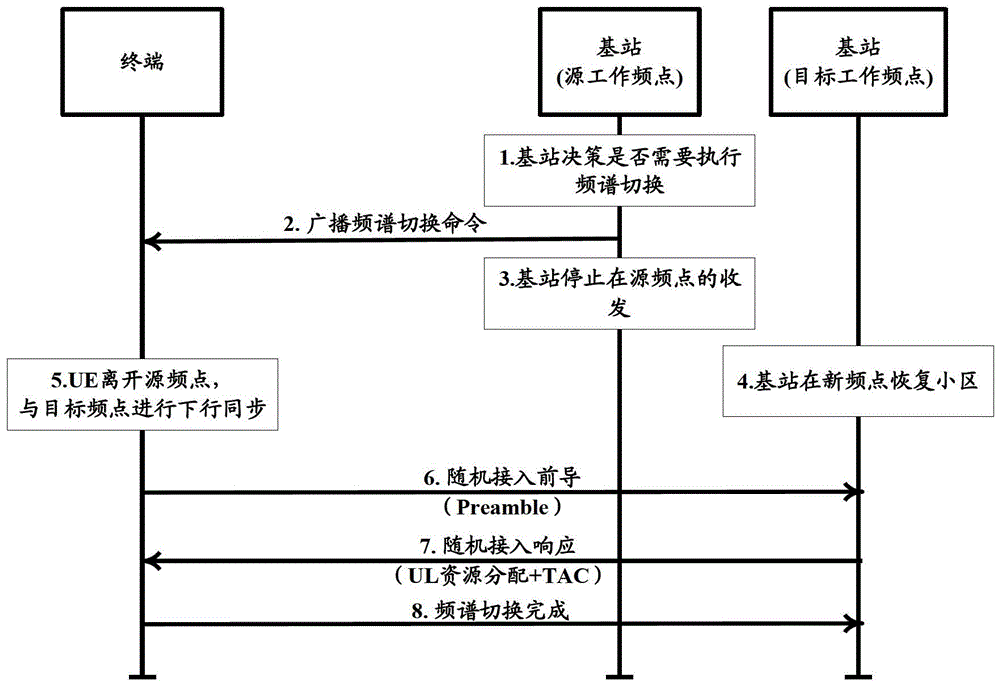
[0127] The specific implementation process of the base station side in this embodiment is as follows Figure 6a As shown, the description is as follows:
[0128] Step 601: the base station works in the source cell on the source frequency point.
[0129] Step 602: The base station and the terminal agree in advance on the calculation method of the access stratum key of the terminal's target cell after spectrum switching, and the calculation method uses the access stratum key or encryption key of the terminal's source cell before spectrum switching stored by the base station. key management parameters.
[0130] The base station and the terminal agree in advance on the calculation method of the access stratum key of the target cell of the terminal after spectrum switching in a statically stipulated manner in the agreement.
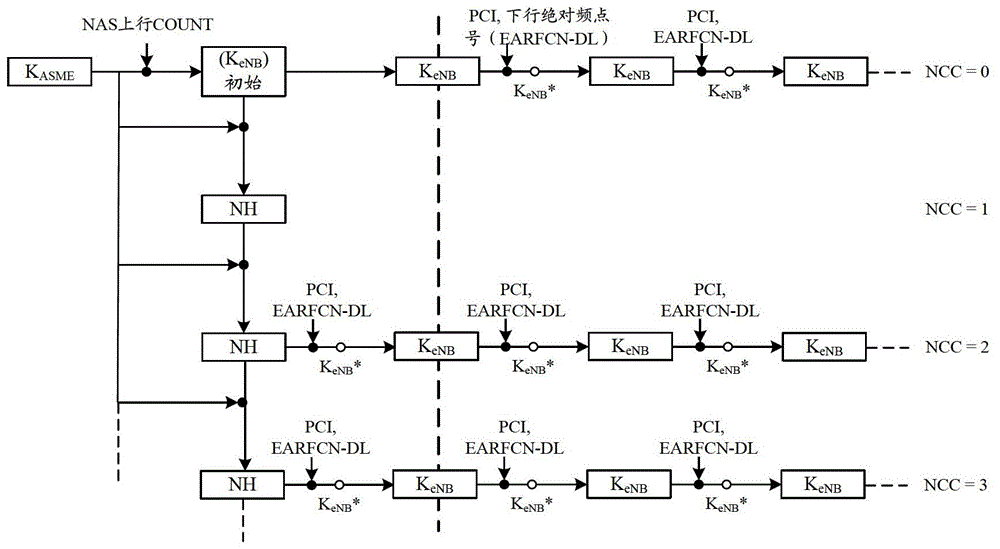
[0131] In the LTE system, the key management parameters include NCC parameter values and / or K eNB .
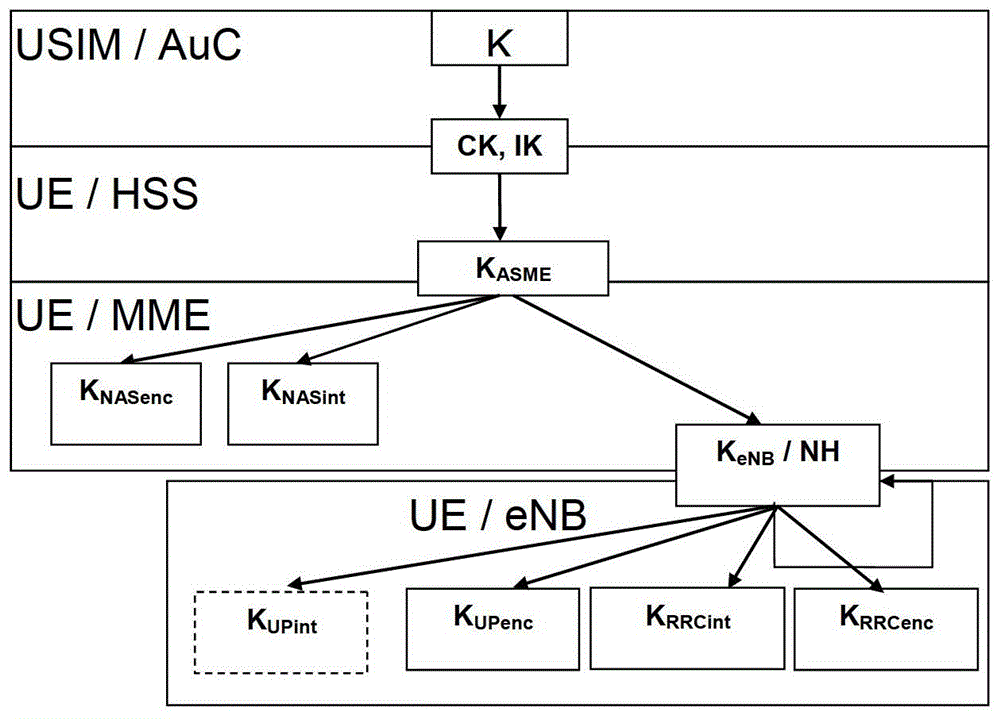
[0132] In an LTE system, the Access Stratum (AS) k...
Embodiment 2
[0153] This embodiment provides a calculation method for the base station and the terminal to pre-agree on the access stratum key of the terminal's target cell after spectrum switching: the terminal's target cell access stratum key after spectrum switching is The access stratum key of the source cell.
[0154] The specific implementation process of the base station side in this embodiment is shown in Figure 6c, and is described as follows:
[0155] Step 621: The base station works in the source cell on the source frequency point.
[0156] Step 622: The base station and the terminal agree in advance on the calculation method of the access stratum key of the terminal's target cell after spectrum switching: the access stratum key of the terminal's target cell after spectrum switching is that of the terminal's source cell before spectrum switching Access layer key.
[0157] The base station and the terminal agree in advance on the calculation method of the access stratum key of ...
Embodiment 3
[0172] This embodiment provides a calculation method for the base station and the terminal to pre-agree on the access layer key of the terminal's target cell after spectrum switching: the base station and the terminal use their own stored key management of the terminal's source cell before spectrum switching The parameter calculates the terminal's access stratum key of the target cell after spectrum switching.
[0173] The specific implementation process of the base station side in this embodiment is as follows Figure 6e As shown, the description is as follows:
[0174] Step 641: The base station works in the source cell on the source frequency point.
[0175] Step 642: The base station and the terminal agree in advance on the calculation method of the access stratum key of the terminal's target cell after the spectrum switching: the base station and the terminal respectively use the stored key management parameters of the terminal's source cell before the spectrum switching...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More