Mobile terminal and method for preventing faulty operation of virtual key
A mobile terminal, misoperation technology, applied in the input/output process of data processing, instruments, electrical digital data processing, etc. effect of operation
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
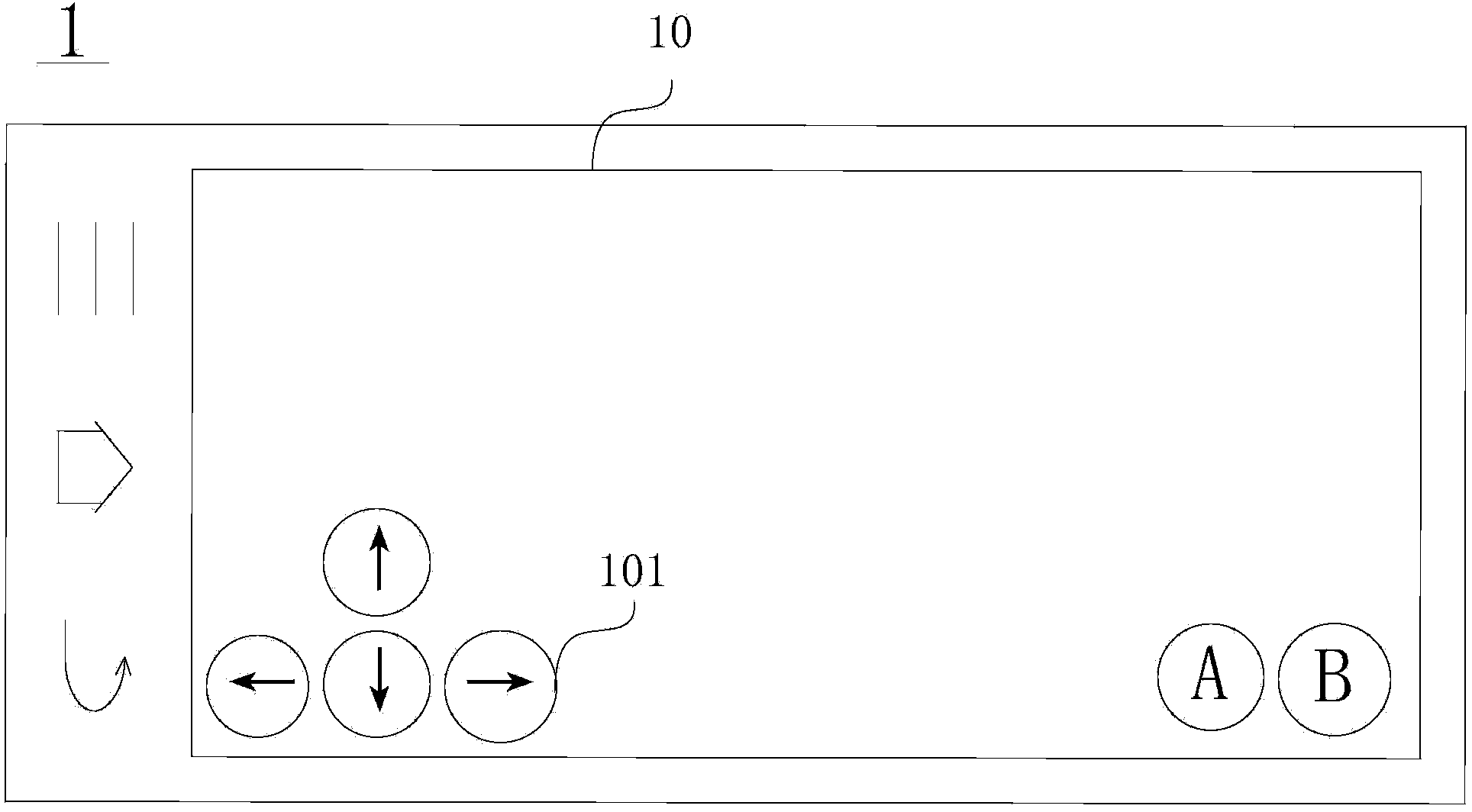
Embodiment 1
[0037] refer to image 3 , image 3 A block diagram of a mobile terminal according to Embodiment 1 of the present invention is shown. in particular, image 3 The mobile terminal 1 is shown, and the mobile terminal 1 includes a touch screen 10 with a fingerprint recognition function, a touch recognition module 11 , a fingerprint recognition module 12 , a fingerprint processing module 13 and a storage 14 . The touch recognition module 11 is configured to recognize a finger operating the touch screen 10 . The fingerprint identification module 12 is configured to identify the fingerprint of the finger identified by the touch identification module 11 as the first fingerprint. The fingerprint processing module 13 is configured to compare the first fingerprint with a pre-stored fingerprint, and if the first fingerprint matches the pre-stored fingerprint, execute the button function of the virtual button corresponding to the pre-stored fingerprint. The storage 14 is for the user t...
Embodiment 2
[0055] The block diagram of the mobile terminal of embodiment 2 and image 3 same. The flowchart reference of embodiment 2 Figure 6 . Figure 6 The flow chart shown with Figure 4 The flow chart shown differs in that the Figure 4 After step S103 shown and Figure 4 A step S204 is added before the step S104 shown.
[0056] In step S204, after it is determined that the first fingerprint matches the pre-stored fingerprint, it is further judged whether the area where the virtual button corresponding to the first fingerprint and the pre-stored fingerprint is located overlaps, and if so, step S205 is executed.
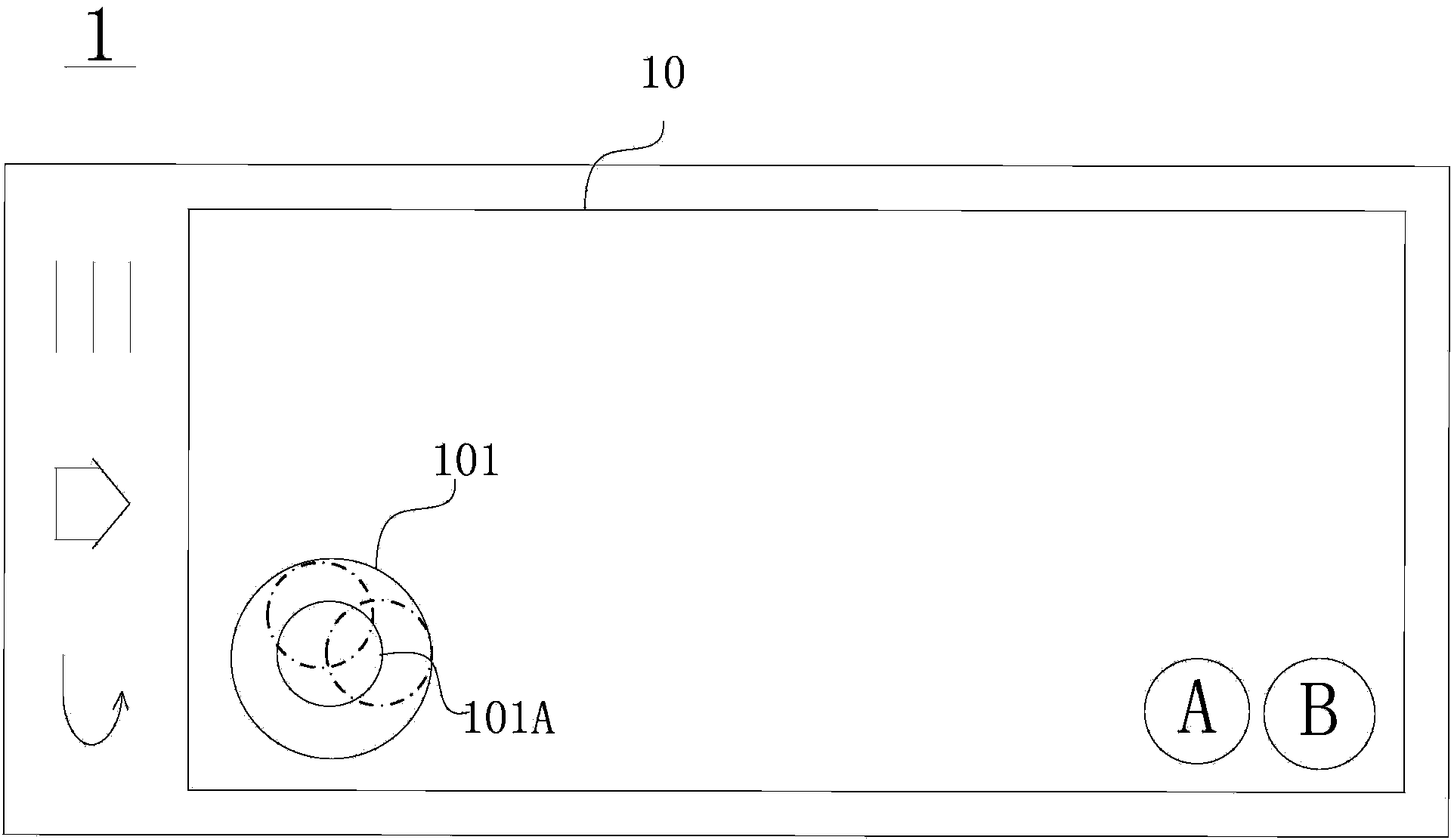
[0057] Specifically, for a schematic diagram of a display interface of the mobile terminal 1 in Embodiment 2, see Figure 7 . The user uses the fingerprint as the touch screen 10 with fingerprint identification function to control the object C on the screen of the mobile terminal 1 . Same as Embodiment 1, in this embodiment, four virtual keys 101A, 101B, 101C and 1...
Embodiment 3
[0060] The block diagram of the mobile terminal of embodiment 3 and image 3 same. The flowchart reference of embodiment 3 Figure 8 . Figure 8 The flow chart shown with Figure 4 The flow chart shown differs in that the Figure 4 After step S103 shown and Figure 4 A step S304 is added before the step S104 shown.
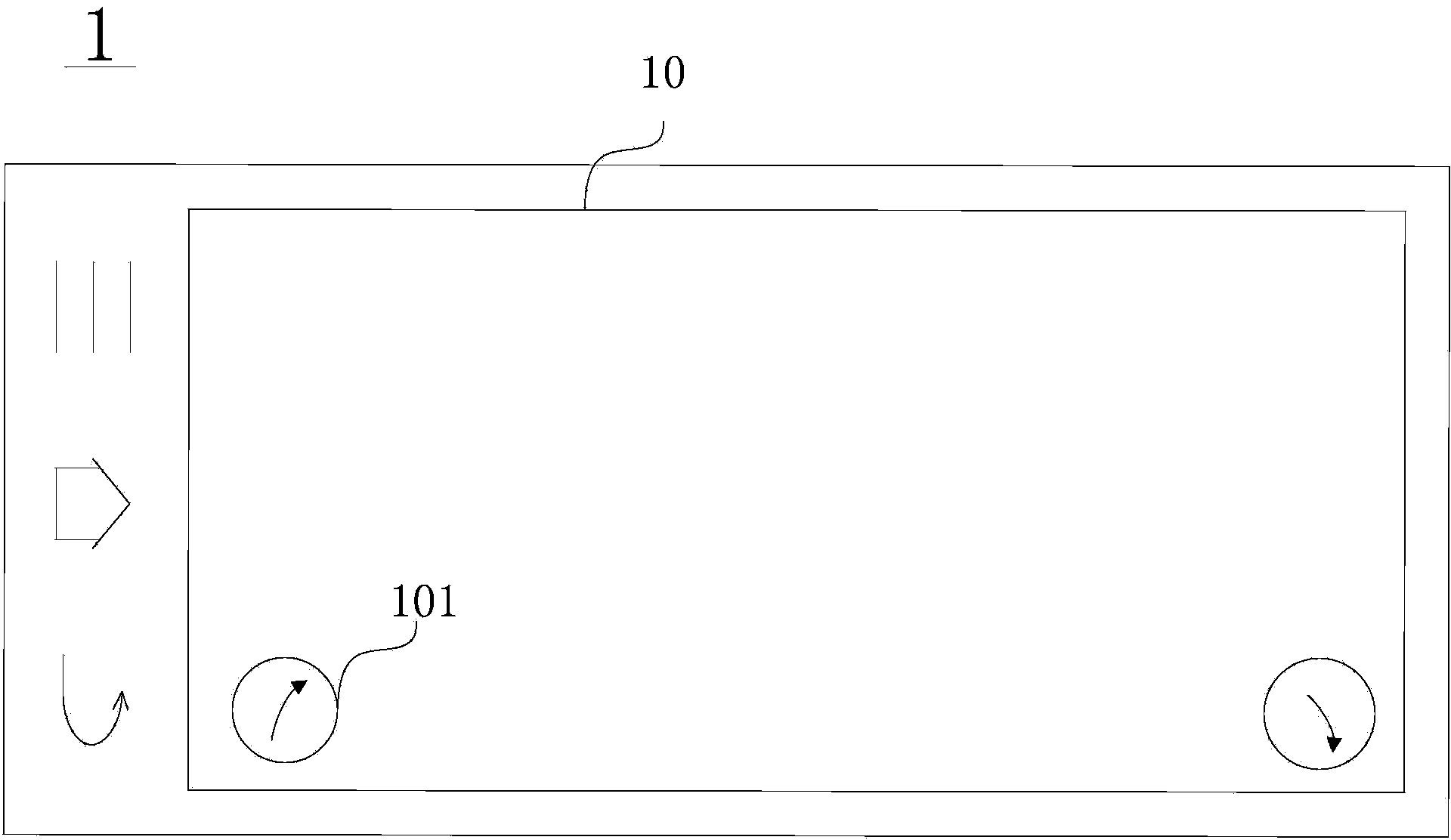
[0061] Step S304, after determining that the first fingerprint matches the pre-stored fingerprint, further judge whether the distance between the center of the first fingerprint and the center of the area where the virtual key corresponding to the pre-stored fingerprint is located is less than a predetermined distance, and if so, execute step S305.
[0062] Specifically, for a schematic diagram of a display interface of the mobile terminal 1 in Embodiment 3, see Figure 9 . The user uses the fingerprint as the touch screen 10 with fingerprint identification function to control the object C on the screen of the mobile terminal 1 . Same as Embodiment 1, in t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com