File protecting method, file protecting device, file decryption method, file decryption device and terminal
A technology for protecting devices and files, which is applied in the direction of security devices, digital data protection, computer security devices, etc., can solve the problems of lack of convenient and effective data protection, and achieve the effect of convenient encryption process, privacy protection and security, and convenient decryption process
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0037] The embodiments of the present invention will be described in detail below with reference to the accompanying drawings, but the present invention can be implemented in many different ways defined and covered by the claims.
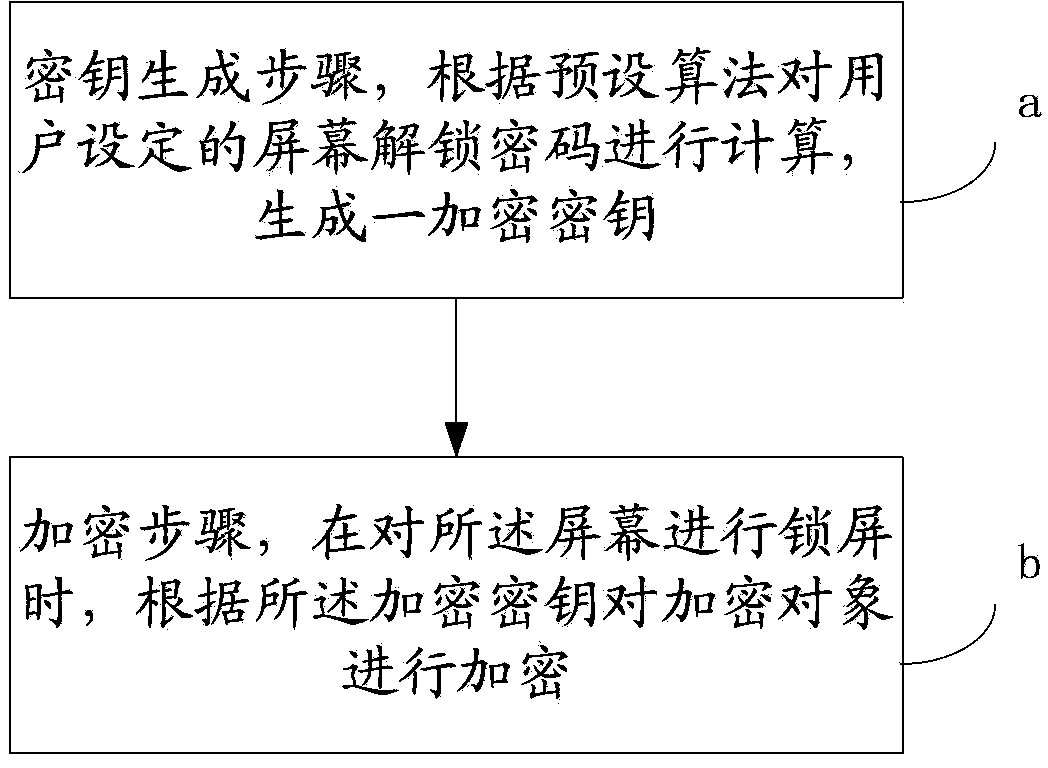
[0038] figure 1 It shows the flowchart of the file protection method described in the embodiment of the present invention.
[0039] see figure 1 As shown, file protection methods include:
[0040] The file protection method is applied to a terminal with a lock screen system, and the file protection method includes:
[0041] The key generation step a is to calculate the screen unlocking password set by the user according to a preset algorithm to generate an encryption key;
[0042] In the encryption step b, when the screen is locked, the encryption object is encrypted according to the encryption key.
[0043] First of all, for a terminal with a lock screen system, it can be a mobile phone with a lock screen system, a handheld tablet computer, etc...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More