Generation method and device for malicious software network intrusion detection feature codes
A network intrusion detection and malware technology, applied in the field of communication, can solve the problems of low extraction efficiency, Internet security danger, and slowing down the response speed of emerging malware.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0065] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
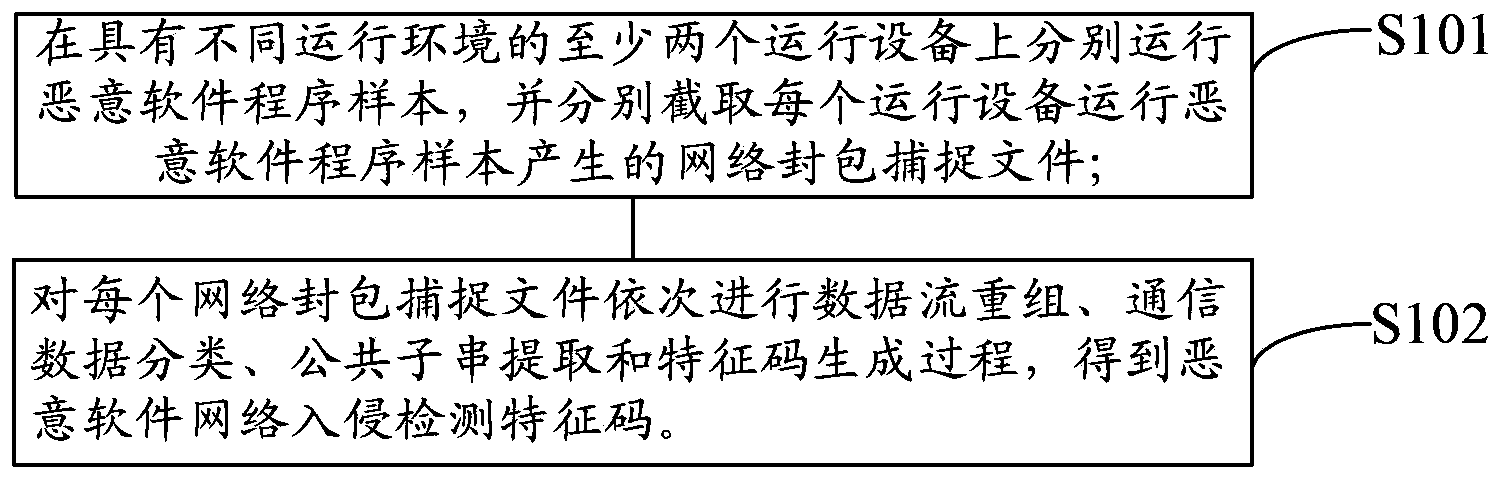
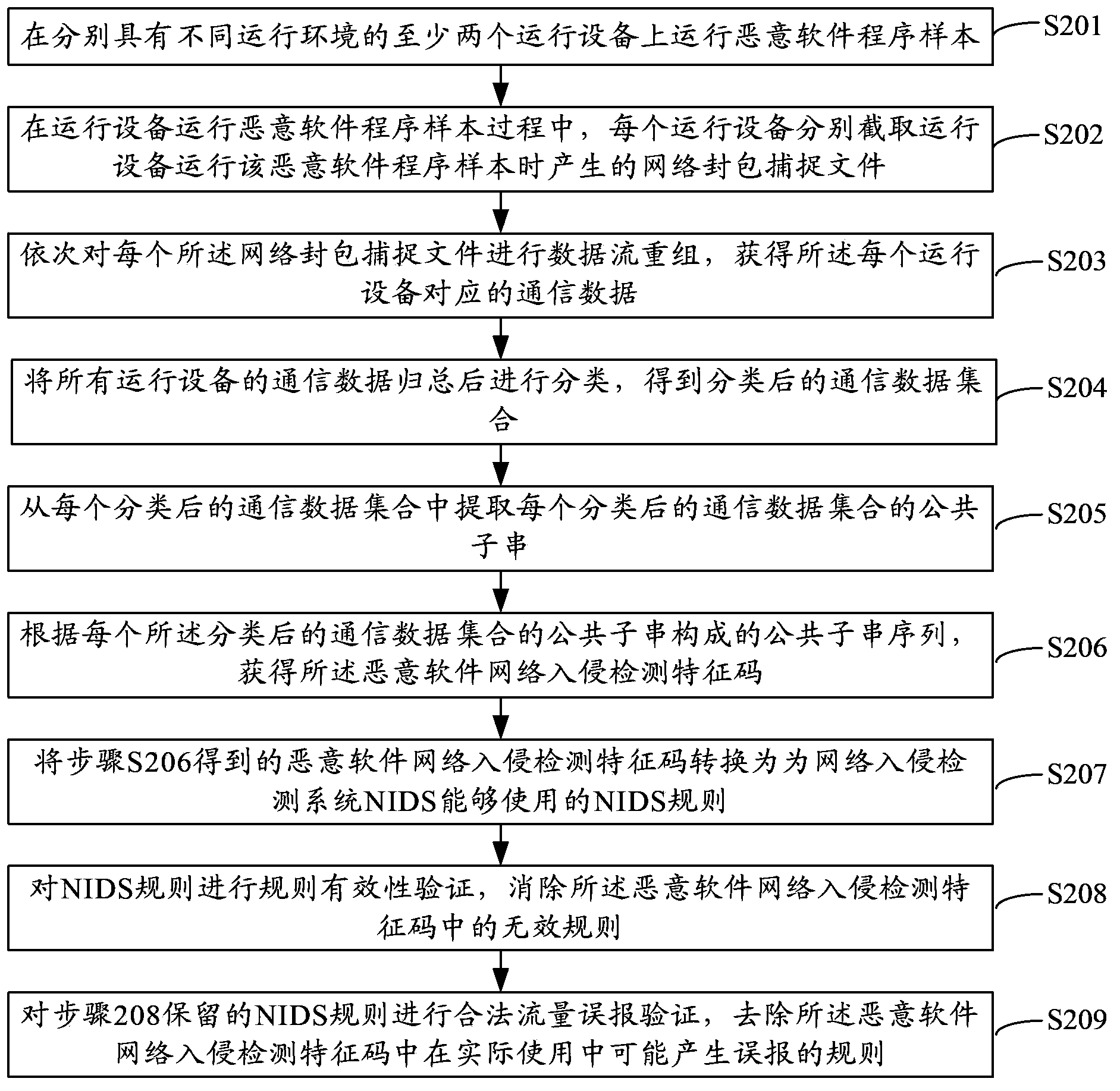
[0066] see figure 1 , which is a schematic flowchart of a method for generating a malware network intrusion detection feature code provided in an embodiment of the present invention, and may include the following steps:
[0067] S101: Run malware program samples on at least two running devices with different running environments, and respectively intercept network packet capture files generated by running the malware program samples on each running device;
...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More