Method and device for identity authentication
An identity authentication and identity technology, applied in the field of identity authentication methods and devices, can solve the problems of waste of resources and low service calls
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0032] The technical solutions of the present invention will be described in further detail below with reference to the accompanying drawings and embodiments.
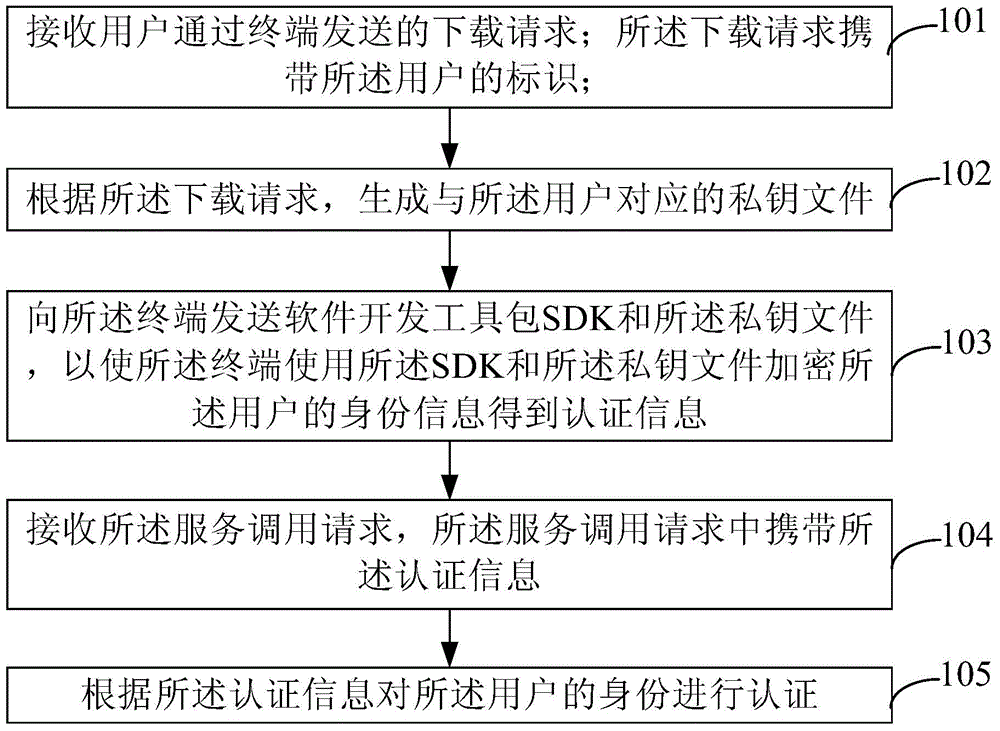
[0033] figure 1 It is a schematic diagram of an identity authentication method provided by an embodiment of the present invention. The subject of execution of the identity authentication method is the server. Such as figure 1 As shown, the method includes the following steps:
[0034] 101. Receive a download request sent by a user through a terminal; the download request carries an identifier of the user.
[0035] When attempting to call a service of a certain system, the user uses the user name registered in the server where the system is located to log in to the server through the terminal. After the user logs in to the server, a download request can be sent to the server. The download request carries the user's identity, which can be the user name registered by the user in the server. The download request is use...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More