Implementing method and system for could security service
A technology of security services and implementation methods, applied in the field of implementation methods and systems of cloud security services, can solve problems such as cloud computing security threats that cannot be well resolved, and achieve improved response effects
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
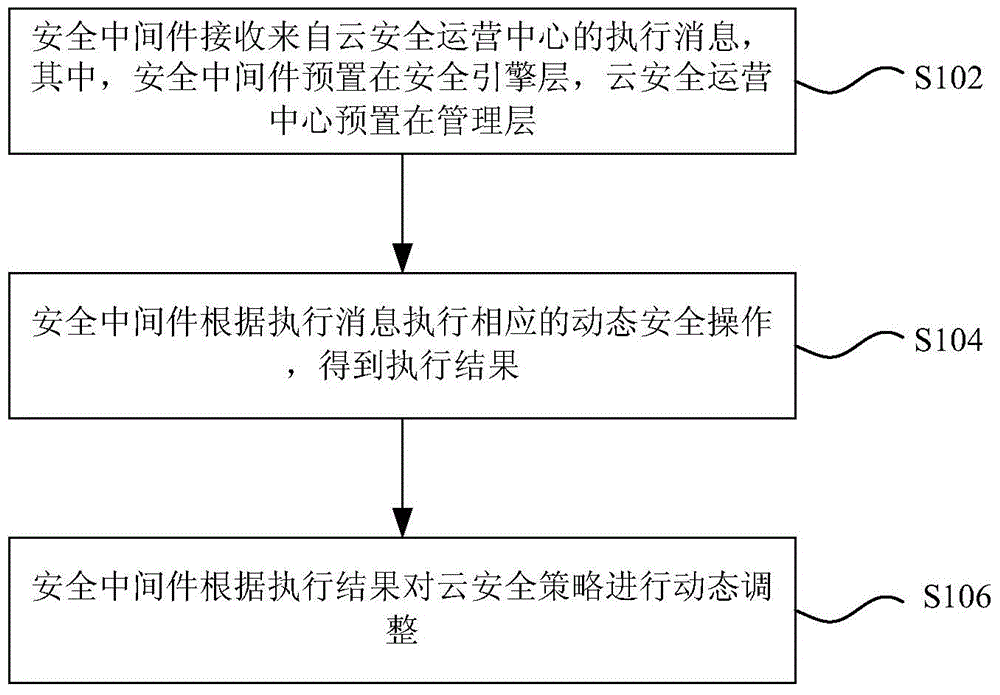
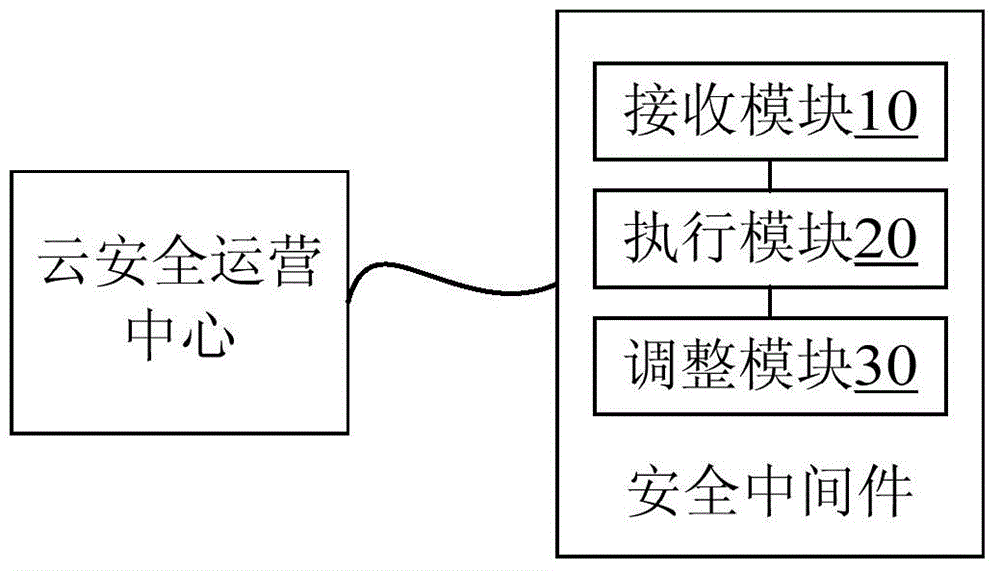
Method used
Image
Examples
Embodiment Construction
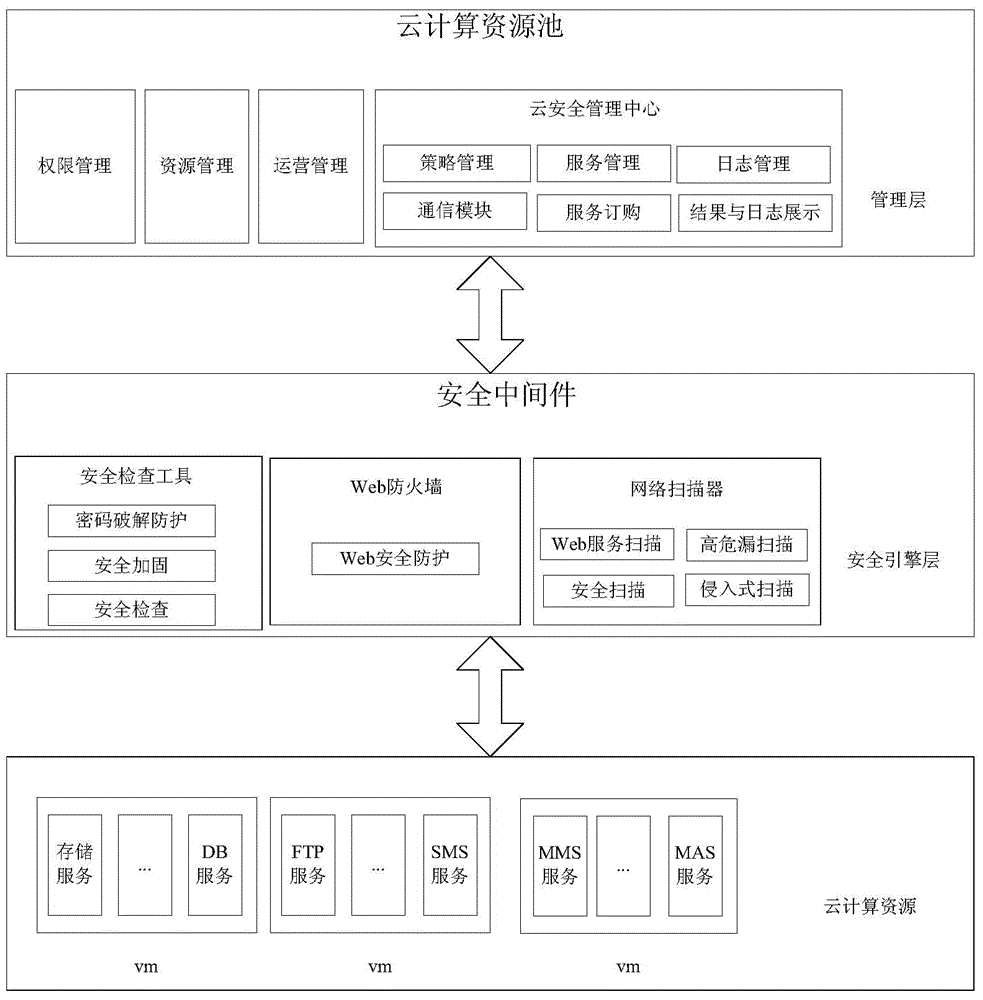
[0027] Hereinafter, the present invention will be described in detail with reference to the drawings and examples. It should be noted that, in the case of no conflict, the embodiments in the present application and the features in the embodiments can be combined with each other.
[0028] The embodiment of the present invention mainly relates to the security service technology in the cloud computing environment, and can deal with security threats in the cloud computing environment by combining existing traditional security devices. Specifically, integrate existing security devices through the cloud security center, shield the differences between different security devices of different manufacturers through security middleware, and call security devices or security services through security middleware to realize dynamic deployment of security devices or security services. Services are provided to hosts or network security services rented by tenants in the cloud computing environ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More