Real-time video monitoring encryption and authentication method
An encryption authentication and real-time video technology, applied in the field of video processing, can solve the problems of low video security, ignoring the safe storage of video frame data, and the speed cannot meet real-time encryption and decryption, so as to prevent tampering and forgery, facilitate decryption and viewing, Guaranteed authenticity and anti-tampering effects
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0034] The present invention will be further described below in conjunction with the accompanying drawings.
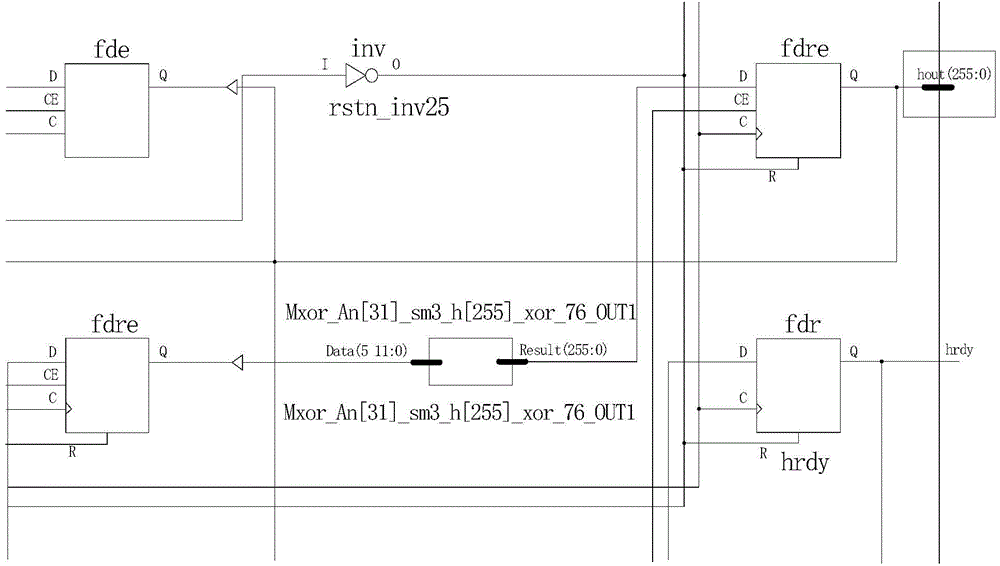
[0035] see figure 1 , which is a structural diagram of a real-time video surveillance encryption authentication method proposed by the present invention;
[0036] like figure 1 Shown, a kind of real-time video surveillance encryption authentication method comprises the following steps:
[0037] Encode the original video to form video frame data;
[0038] Calculate the hash value of the video frame data to obtain the video hash value;
[0039] Encrypt the video frame data to form an encrypted file containing the key stream;
[0040] Store and transmit encrypted files and video hash values.
[0041] Further, encoding the original video to form video frame data specifically includes: converting the original video into video frame data through a video data amplifier and a video encoder.
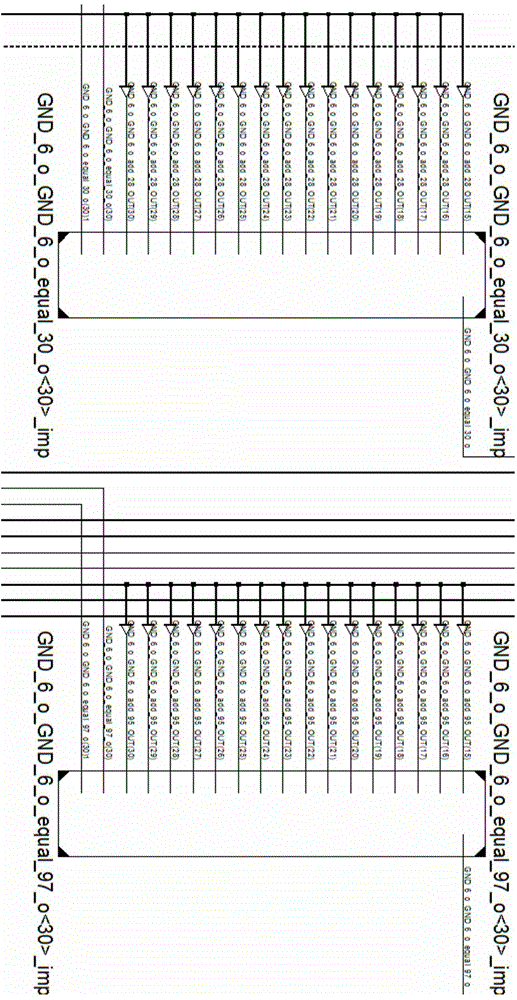
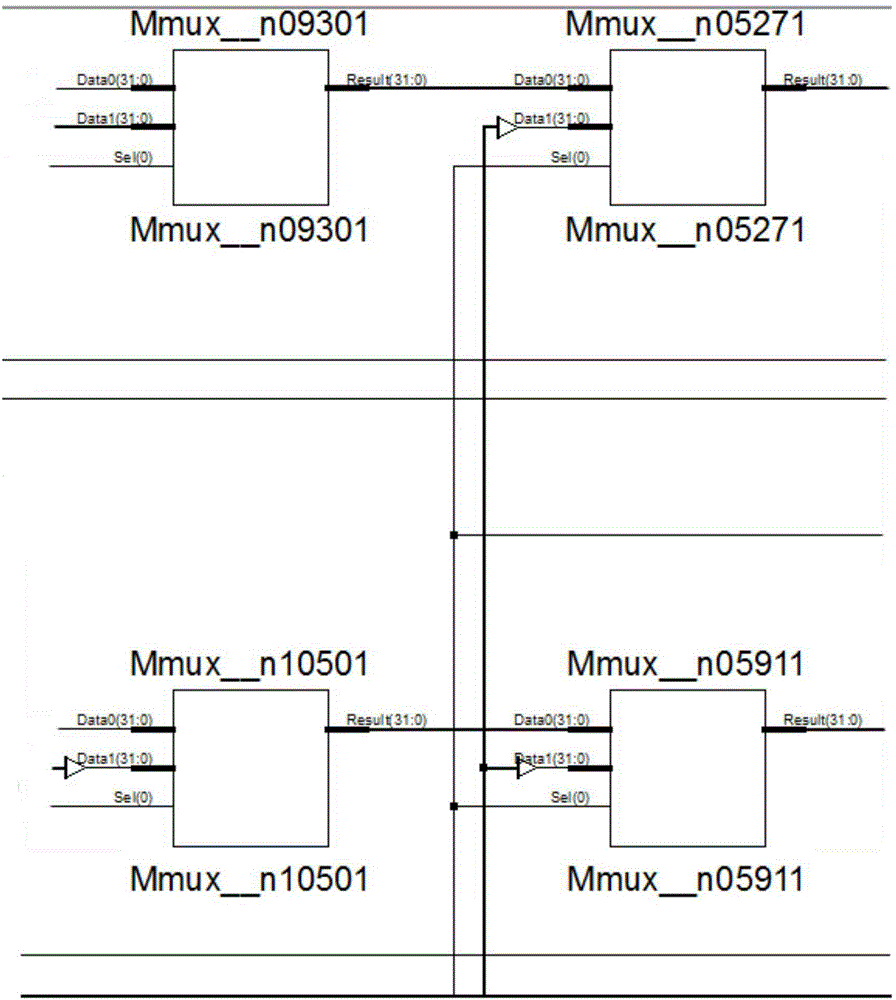
[0042] Further, the video hash value uses the SM3 hash chip to calculate the ha...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap