Implementation method and device of application-type honeypot
An implementation method and honeypot technology, applied in the field of computer security, can solve the problems that are easily perceived as honeypots, services and data are too simple, and achieve the effect of ensuring credibility
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0030] In order to enable those skilled in the art to better understand the technical solutions in the embodiments of the present invention, and to make the above-mentioned purposes, features and advantages of the present invention more obvious and easy to understand, the technical solutions in the present invention will be further detailed below in conjunction with the accompanying drawings illustrate.
[0031] The present invention provides a method and device for implementing an application-type honeypot. By using processed real application services and real data, it solves the problem that the service and data in the existing honeypot technology are too simple and are easily perceived as honeypots. , while ensuring the activity of the data in the honeypot, achieving the purpose of attracting attackers or malicious codes to run in the honeypot.
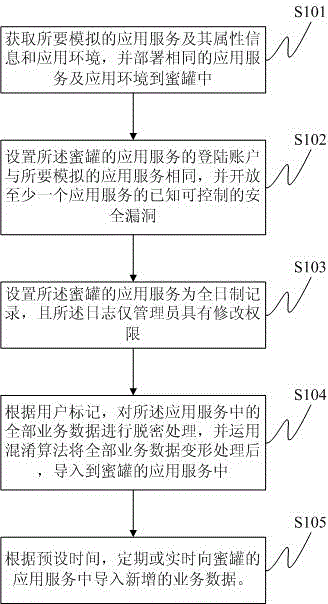
[0032] An application-type honeypot implementation method, such as figure 1 shown, including:
[0033] S101: Obtain the applica...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More