Alarm transaction extracting method and system
An extraction method and transaction technology, applied in the field of network risk management and control, can solve problems such as low efficiency of alarm transaction extraction, and achieve the effect of high extraction efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
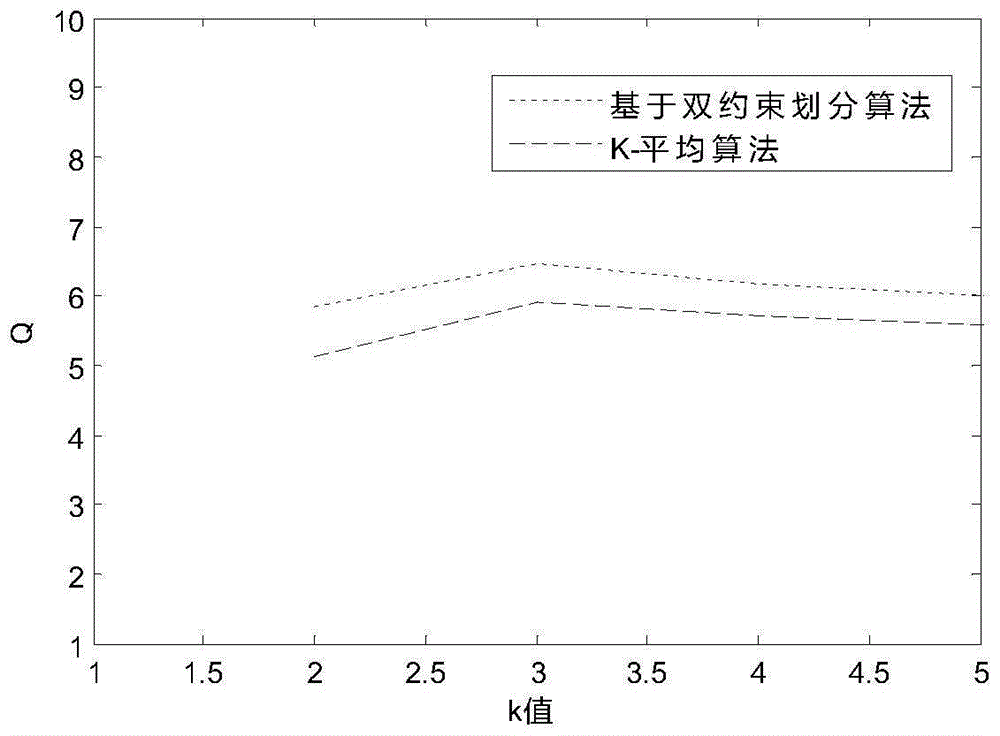
[0031] The technical solutions of the present invention will be described in detail below in conjunction with the accompanying drawings and preferred embodiments.
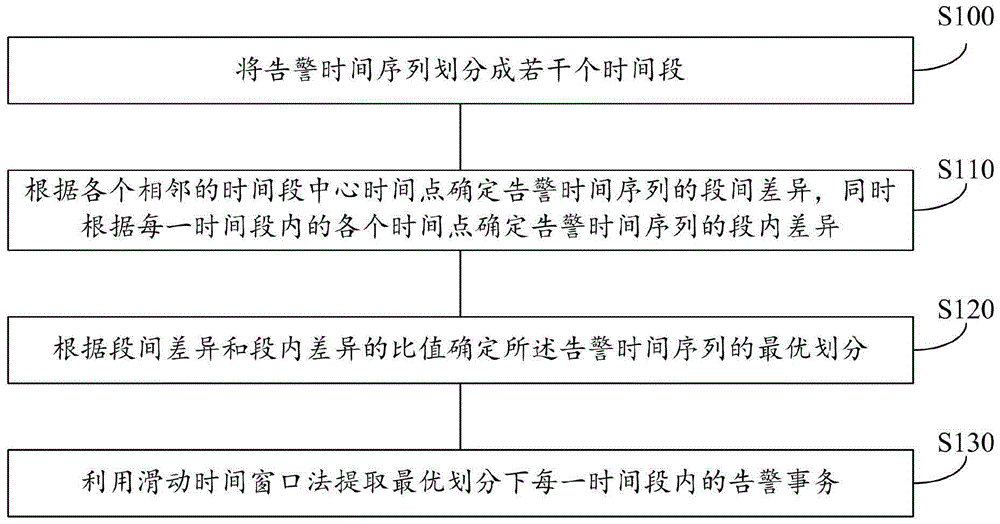
[0032] In one example, see figure 1 The flow diagram of the method for extracting alarm transactions is shown, and the method specifically includes the following steps:
[0033] S100 divides the alarm time series into several time periods;
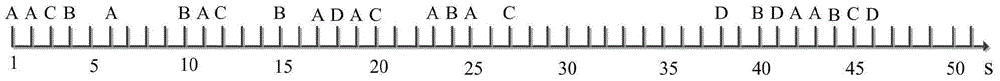
[0034] The alarm time series is a collection of time points where alarms occur in the original alarm data in the network, that is, the alarm time series is composed of alarm time or alarm time points, for example, the alarm time series V={t i},i=1,2,...,K, where, t i Indicates the moment when the i-th alarm occurs, and there are K alarms in the alarm time series; the so-called division of the alarm time series refers to the use of a certain algorithm to cluster each alarm time into several time series according to the distribution characteristics of the alarm time series par...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com