Four-particle GHZ state-based two-party quantum key agreement protocol
A quantum key agreement, four-particle technology, applied in the field of two-party quantum key agreement protocol, can solve problems such as low qubit efficiency, inability to resist Trojan horse attacks and delayed photon Trojan horse attacks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
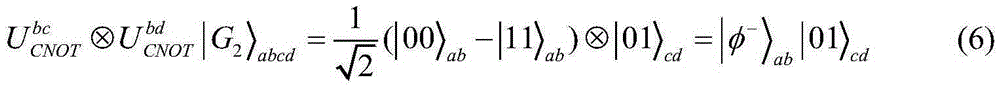
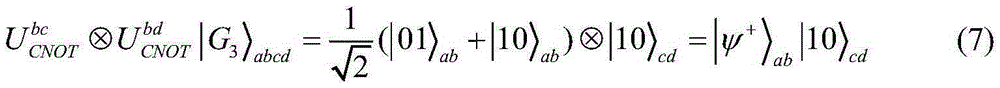
[0035] 1. Preliminary knowledge
[0036] First, introduce four unitary transformations U 00 ,U 01 ,U 10 and U 11 , namely U 00 =I=|0>01 =X=|0>10 =Z=|0>11 =iY=|0>,|1>} forms the Z base, and {|+>,|->} forms the X base, where, | + > = 1 / 2 ( | 0 > + | 1 > ) , | - > = 1 / 2 ( | 0 > - | 1 > ) . The four Bell states are defined as follows:
[0037] | φ + > = 1 / 2 ( | 00 > ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More