An attribute-based system and decryption method for keyword searchable outsourced key generation and decryption
A key generation, keyword technology, applied in the field of information security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
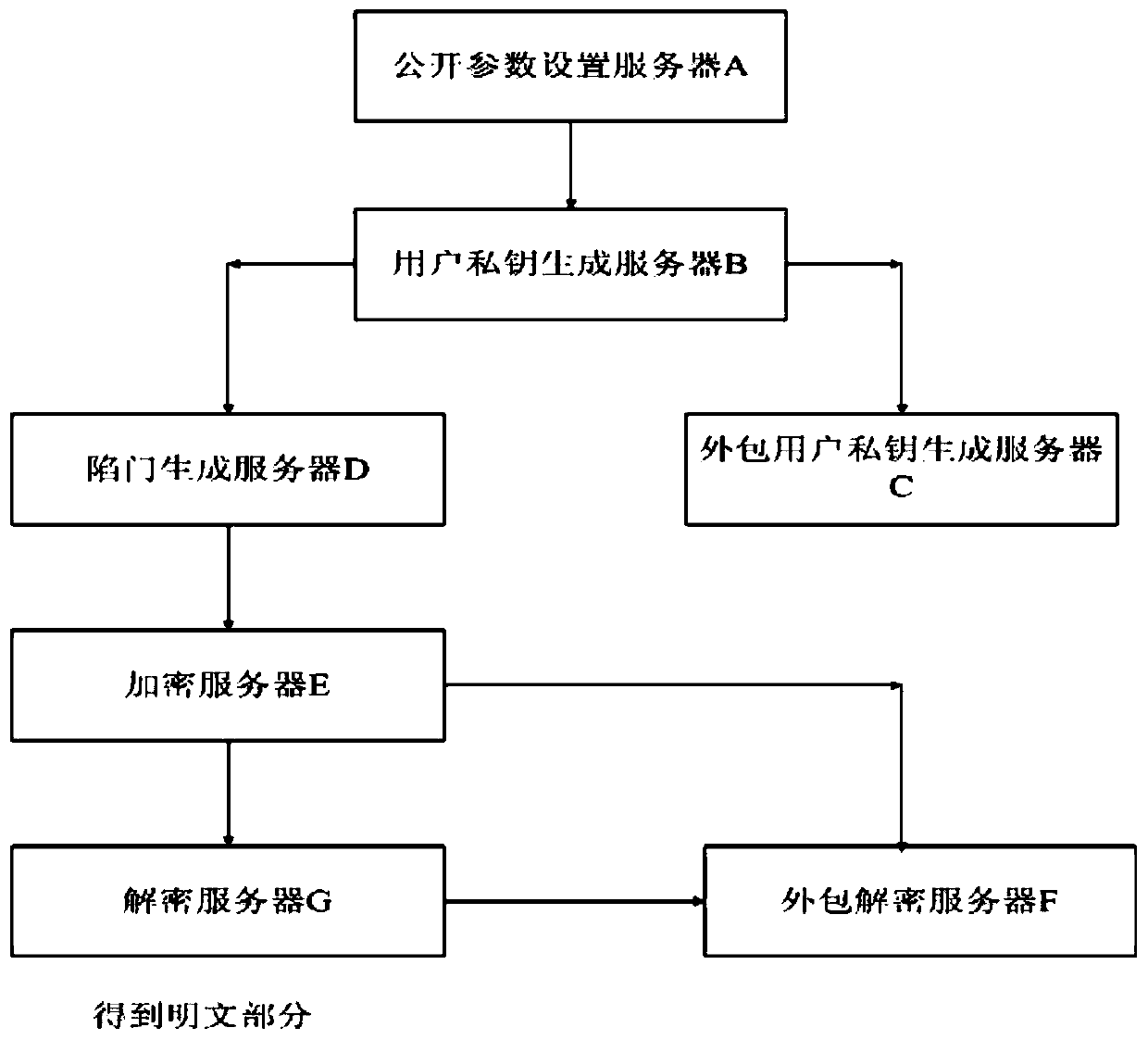
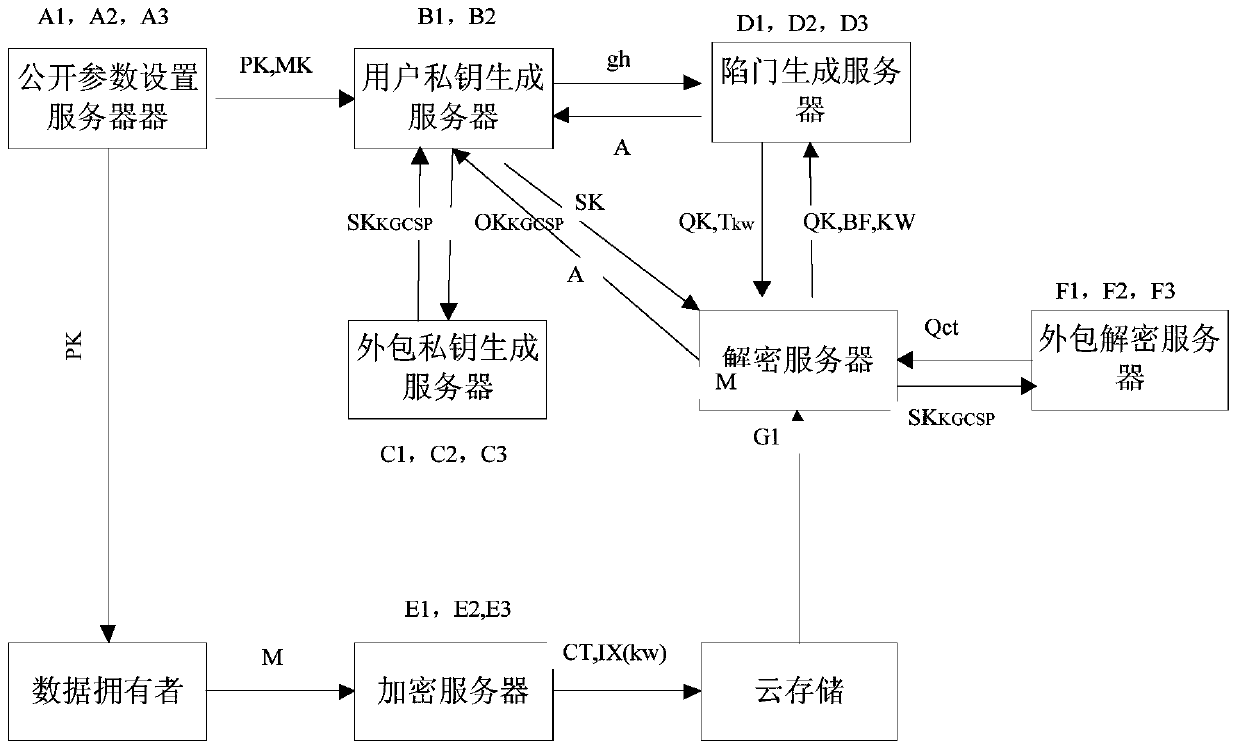
[0060] Below in conjunction with accompanying drawing, technical scheme of the present invention is described in further detail:
[0061] The attribute-based system of keyword searchable outsourced key generation and decryption in the present invention can be realized based on bilinear pairings. The following briefly introduces the related concepts of bilinear pairings and the properties to be satisfied:
[0062] Order G 1 , G 2 is a multiplicative cyclic group of order p, where p is a prime number and g is G 1 generator of . Suppose G 1 and G 2 The discrete logarithm problem on both groups is hard. Define the bilinear map on the group as: e:G 1 ×G 1 →G 2 , and satisfy the following properties:
[0063] 1. Bilinear.e(u a ,v b )=e(u,v) ab , for all u,v∈G 1 ,a,b∈Z p * and g∈G 1 are established.
[0064] 2. Non-degenerate. e(u,v)≠1, where 1 is G T The identity element of , there exists u,v∈G 1 .
[0065] 3. Computability. Efficient algorithms exist to compute ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More