Cloud storage data integrity service signature method
A data integrity, cloud storage server technology, applied in the direction of digital transmission system, user identity/authority verification, electrical components, etc., can solve unsuitable cloud platform architecture, complex signature calculation and data structure, increased calculation and communication overhead And other issues
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0025] The present invention will be further described below in conjunction with the accompanying drawings and embodiments.
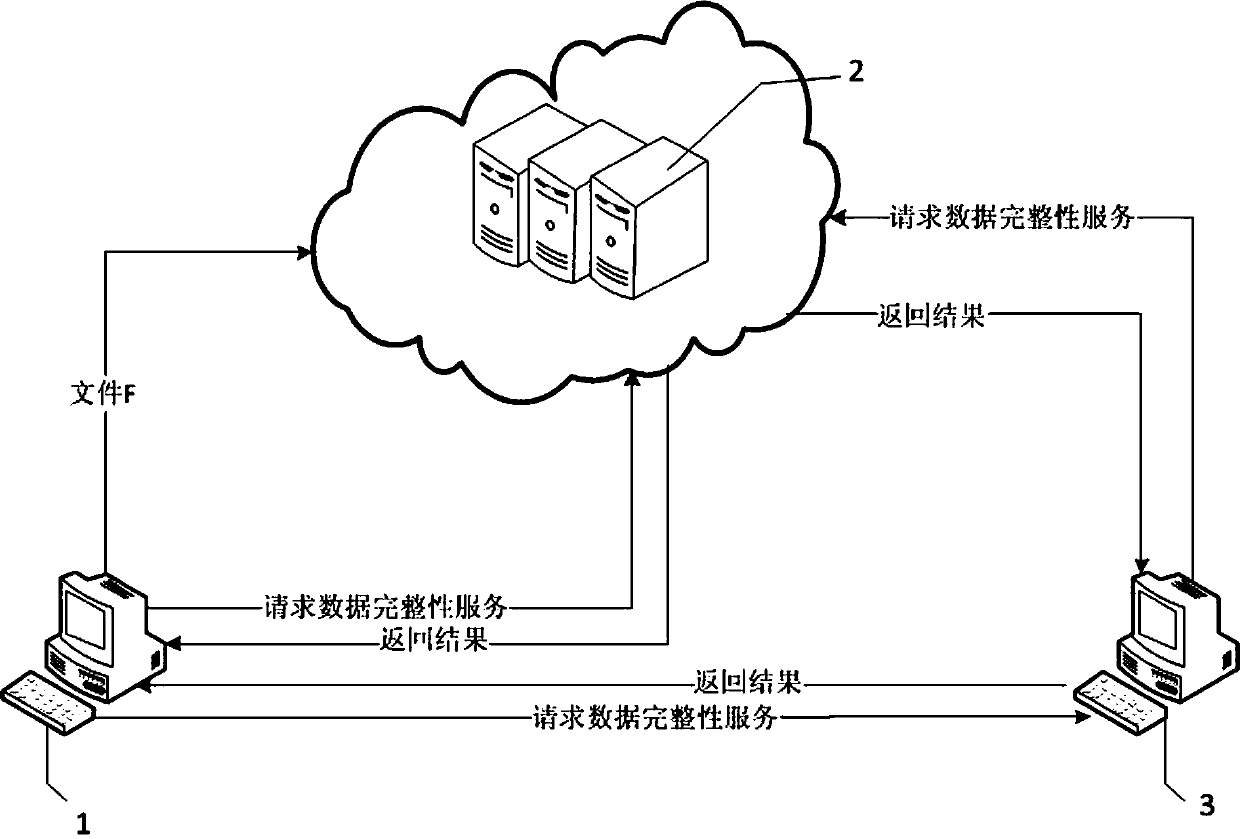
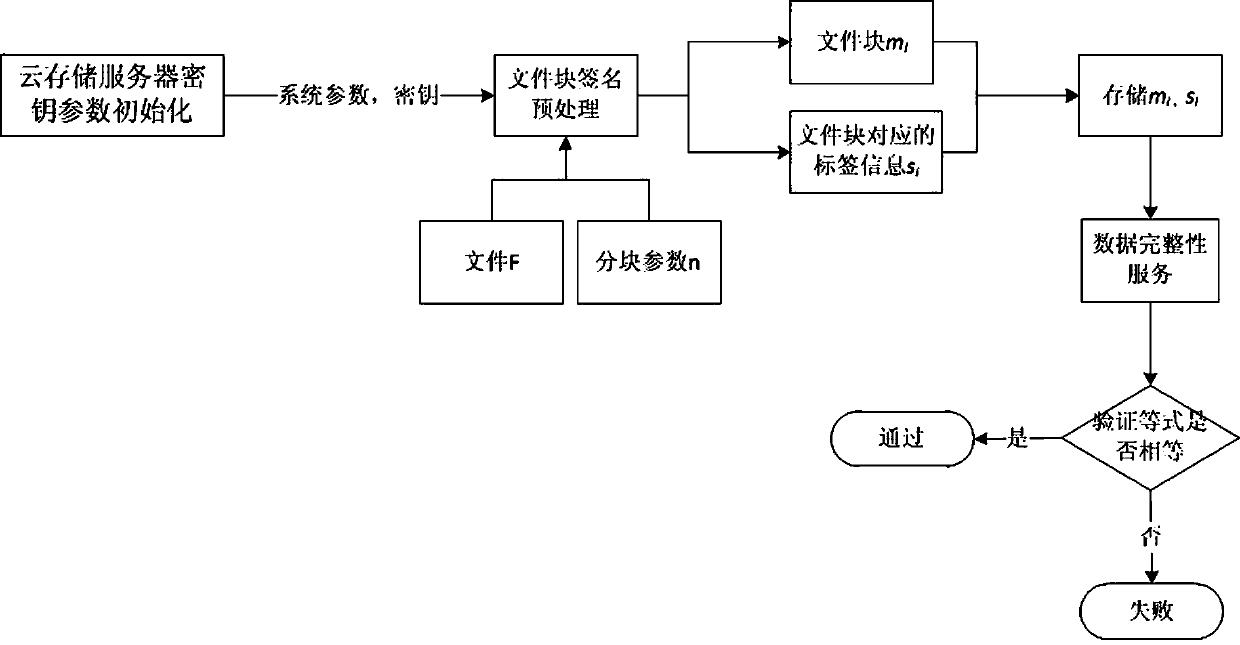
[0026] like figure 1 As shown, the cloud storage data integrity service signature method, in this architecture, includes three participants, user 1, cloud storage server 2 and trusted third-party detector 3, user 1 uploads the uploaded file F to the cloud storage server 2. There are two ways for user 1 to implement data integrity services: first, user 1 sends a request to cloud storage server 2 for data integrity services, and cloud storage server 2 returns the result to user 1 after calculating the signature method; In the second type, user 1 sends a request for data integrity service to trusted third-party detector 3, and trusted third-party detector 3 then sends a request for data integrity service to cloud storage server 2, and cloud storage server 2 calculates Afterwards, the result is returned to the trusted third-party detector 3, and the truste...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More