Third-party authorization method and third-party authorization system
An authorization system and authorization technology, applied in the field of third-party authorization methods and third-party authorization systems, can solve the problems of lack of behavior authorization, potential security risks, and cumbersome business processes.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
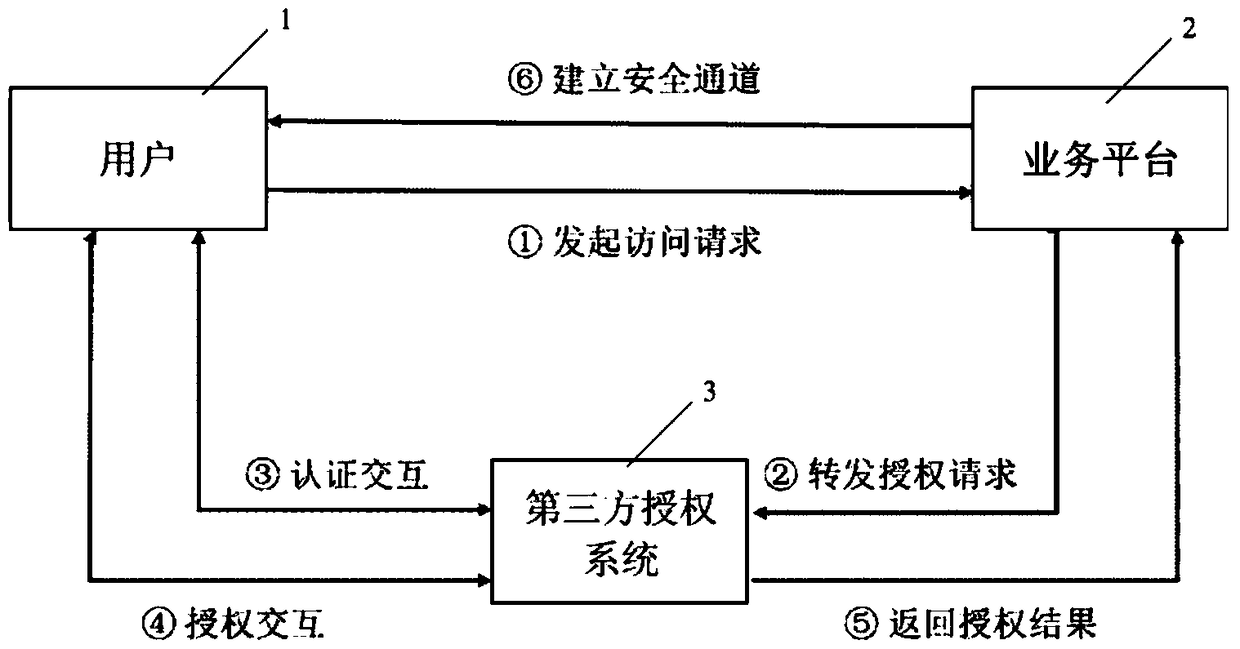
[0071] In order to enable those skilled in the art to better understand the technical solutions of the present invention, the third-party authorization method and third-party authorization system of the present invention will be further described in detail below in conjunction with the accompanying drawings and specific embodiments.
[0072] The technical idea of the present invention is: considering the unique security advantages of the mobile phone SIM card, combined with the universality and portability of the mobile terminal, the third-party authorization method of the present invention is based on the trust degree of the user and the service platform. The authorization method of the SIM card application uses a third-party authorization system to interact with the mobile terminal card application through data short messages to complete user identity authentication and authorization confirmation, improving the security and portability of the authentication and authorization...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More