Method and device for protecting safety protection application program files and electronic equipment
An application program and security protection technology, which is applied in the field of information security, can solve the problem that the method of security protection application program files cannot be safely protected.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
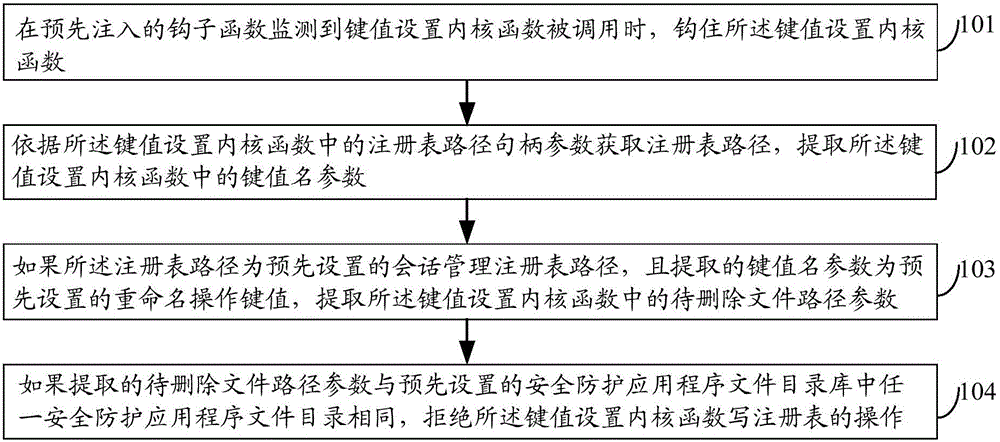
[0066] figure 1 It is a schematic flow diagram of a method for protecting a security application file according to an embodiment of the present invention, such as figure 1 As shown, the method of this embodiment may include:
[0067] Step 101, when the pre-injected hook function detects that the key value setting kernel function is called, hook the key value setting kernel function;
[0068] In this embodiment, through statistical analysis and mining, in the process of operating system initialization, if a certain application program deletes or uninstalls the security protection application program file, it is by calling the mobile operation kernel function of the application layer, that is, the MoveFileEx kernel function, MoveFileEx The kernel function calls the key-value setting kernel function to realize. Among them, the MoveFileEx kernel function includes multiple moving operation parameters, for example, the registry path handle parameter (filepath) where the file to be...
Embodiment 2
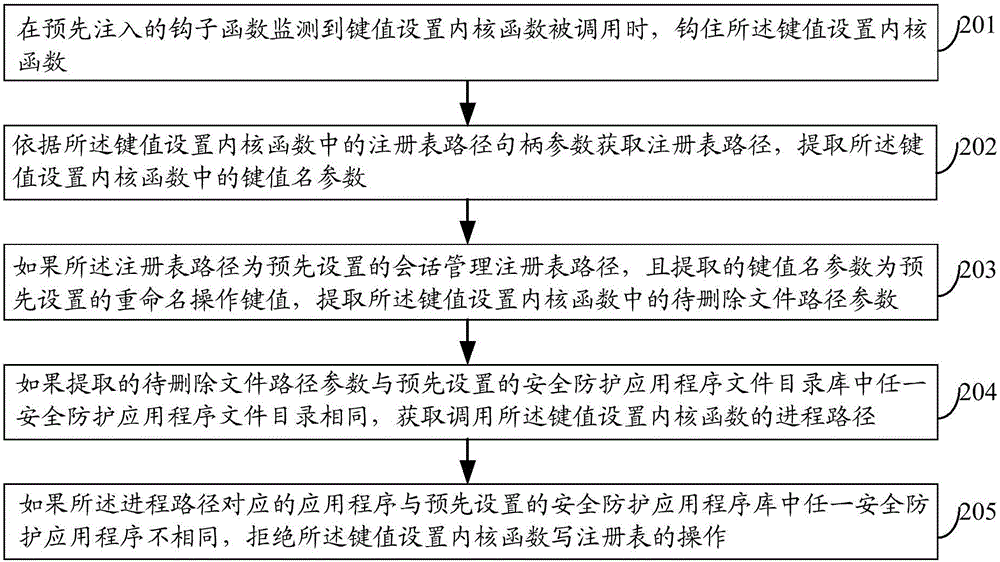
[0100] figure 2 It is a schematic flowchart of a method for protecting a security protection application program file in Embodiment 2 of the present invention, as figure 2 As shown, the method of this embodiment may include:
[0101] Step 201, when the pre-injected hook function detects that the key value setting kernel function is called, hook the key value setting kernel function;
[0102] Step 202, obtain the registry path according to the registry path handle parameter in the key setting kernel function, and extract the key name parameter in the key setting kernel function;
[0103] Step 203, if the registry path is a preset session management registry path, and the extracted key name parameter is a preset renaming operation key value, extract the key value and set the file path to be deleted in the kernel function parameter;
[0104] In this embodiment, the processes from step 201 to step 203 are respectively similar to steps 101 to 103 in the first method embodiment...
Embodiment 3
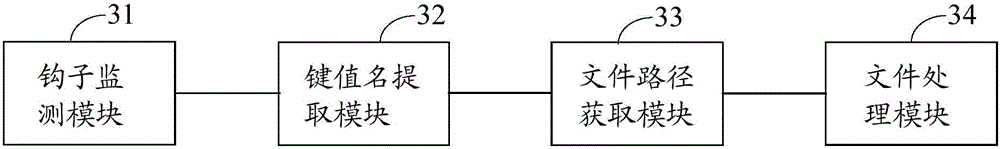
[0115] image 3 It is a schematic structural diagram of a device for protecting security protection application program files in Embodiment 3 of the present invention, as shown in image 3 As shown, the device of this embodiment may include: a hook monitoring module 31, a key name extraction module 32, a file path acquisition module 33 and a file processing module 34, wherein,
[0116] The hook monitoring module 31 is used to hook the key value setting kernel function when the pre-injected hook function monitors that the key value setting kernel function is called;
[0117] Key value name extracting module 32, for setting the registry path handle parameter in the kernel function according to the key value to obtain the registry path, extracting the key value name parameter in the kernel function for extracting the key value;
[0118] File path acquisition module 33, if the registry path is a preset session management registry path, and the extracted key value name parameter i...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More