Login protocol operating method for inter-application user information transfer
A technology of user information and operating methods, applied in the field of communication, can solve problems such as limited scope of application, non-standard login authorization/association binding methods, inconsistent communication and authorization protocols, etc., to achieve a wide range of applications, compatibility and upgradeability Strong, wide-ranging effects
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0031] The present invention will be further described in detail below in conjunction with the accompanying drawings and through specific embodiments. The following embodiments are only descriptive, not restrictive, and cannot limit the protection scope of the present invention.
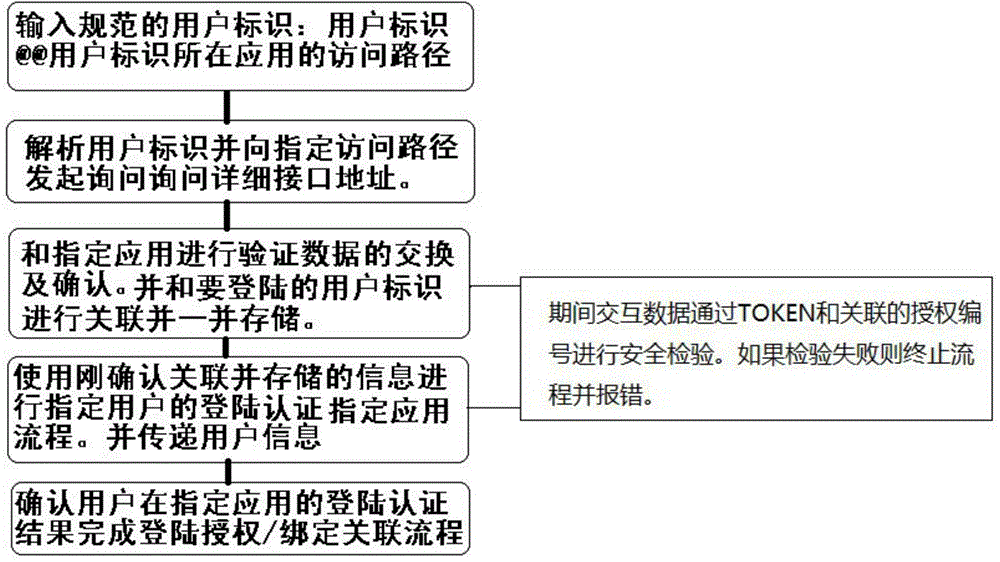
[0032] A login protocol operation method for cross-application user information transmission, including systems or devices (hereinafter collectively referred to as applications), users and their usernames, Email, Uid (user identity certificate), etc. can be used as the identification of user login (hereinafter collectively referred to as user name), and the specific steps are as follows:
[0033] ⑴ Standardized and unified cross-application login username structure, username@@the access address of the application where the username is located (hereinafter referred to as the protocol specification username), such as username@@domain.com, where username is the username, @@ is a separation symbol used t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com