Security activation optimization method suitable for LTE access layer
An optimization method and access layer technology, applied in the field of security activation optimization of the LTE access layer, can solve problems such as incomplete protocol methods, affecting COUNT values, and link establishment failures.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0071] The specific embodiments of the present invention will be described in further detail below in conjunction with the drawings and embodiments. The following examples are used to illustrate the present invention, but not to limit the scope of the present invention.
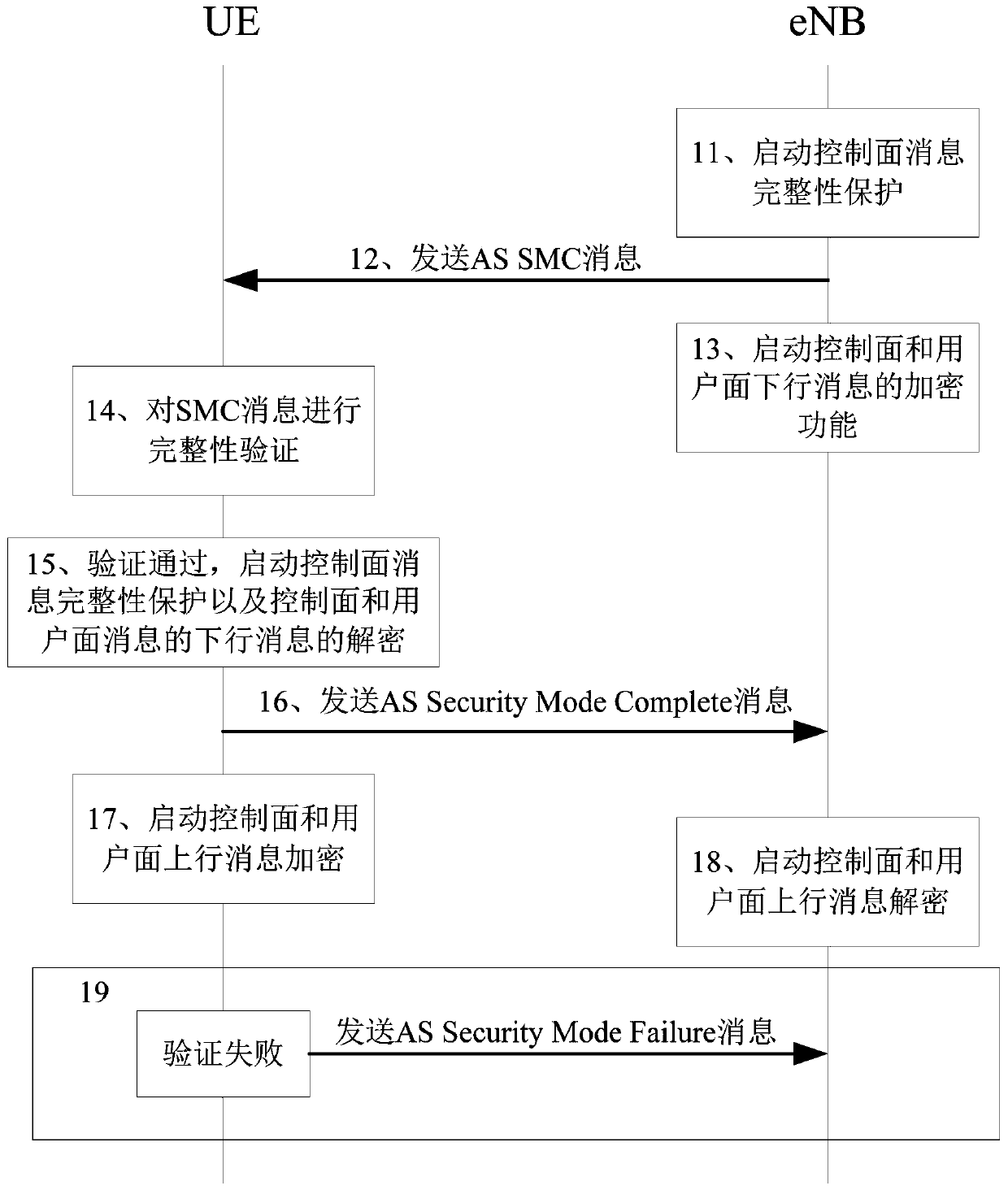
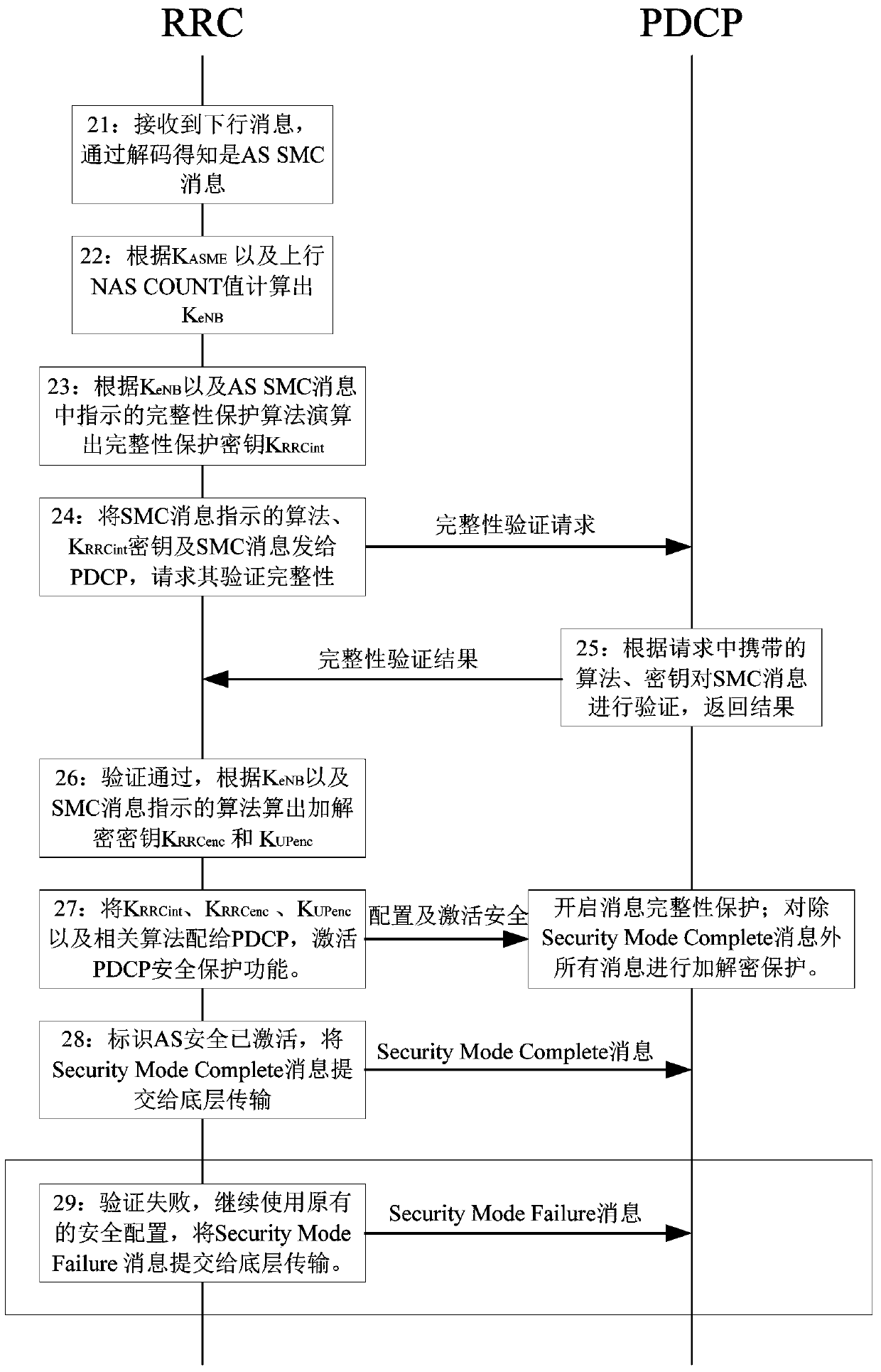
[0072] See figure 1 The security activation optimization method for LTE access layer is unique in that it includes the following steps:
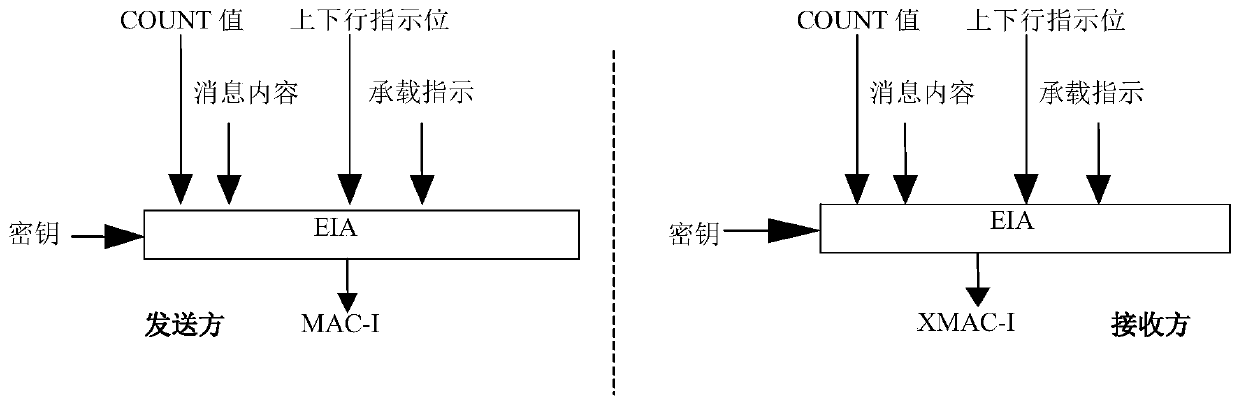
[0073] First, before the security protection mechanism is activated, all received downlink messages and their corresponding counter values are delivered to the radio resource control protocol module for processing through the packet data convergence protocol module. Specifically, the activation is before the radio resource control protocol module (Radio Resource Control, RRC) activates the security protection mechanism of the packet data convergence protocol module (PDCP). In addition, in this process, the corresponding Hyper Frame Number (Hyper Frame Number, HFN for short) ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More