Token generation and authentication method and authentication server
An authentication server and token authentication technology, which is applied in the field of method and authentication server, token generation and authentication, can solve the problems of waste of authentication server cluster storage resources, consumption of authentication server cluster data transmission resources, and high authentication server capacity requirements
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0083] The technical solutions in the embodiments of the present invention will be clearly and completely described below in conjunction with the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
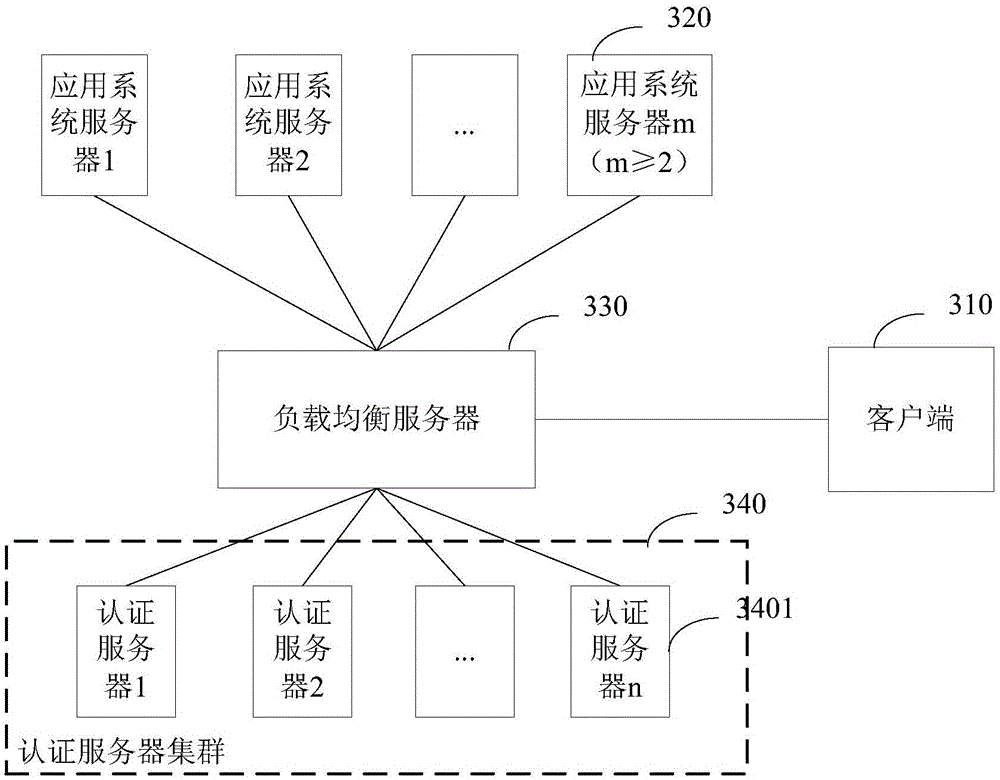
[0084] Among them, the network architecture applied by the token authentication method in the embodiment of the present invention can be found in image 3 As shown, it includes: an authentication server cluster 340 composed of a client 310, m application system servers 320 (m≥2), a load balancing server 330, and n authentication servers 3401 (n≥2); wherein, the load balancing servers 330 are respectively Connect with the client 310, each application system serve...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More