Privilege isolation method and device of Android third-party class library
A permission and class library technology, applied in the field of system security, can solve the problems of abuse of host application permissions, inability to use it in a wide range, user privacy leakage, etc., and achieve the effect of simple use.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0036] The present invention will be further described below in conjunction with the accompanying drawings and embodiments.
[0037] In order to solve the problems in the prior art, this embodiment provides a method and device for isolating permissions of an Android third-party class library. The following firstly introduces a method for isolating permissions of an Android third-party class library provided by an embodiment of the present invention.
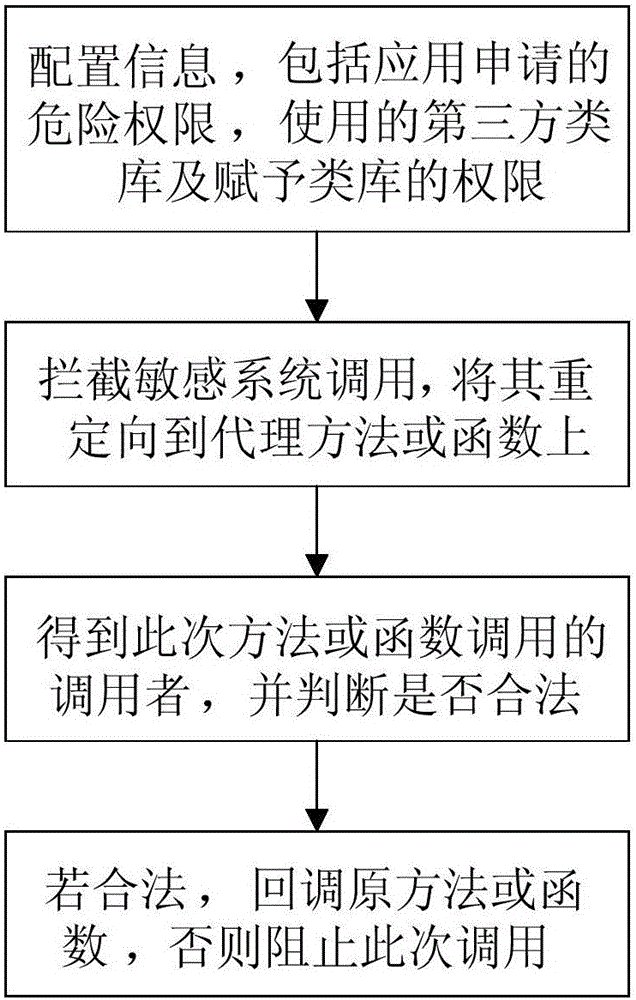
[0038] figure 1 It is a schematic flow chart of the Android third-party class library permission isolation method provided by the embodiment of the present invention. The method includes the following steps,
[0039] Step 1. Configure permission information, including the dangerous permissions applied for by the application, the third-party class library information used, and the permissions granted.
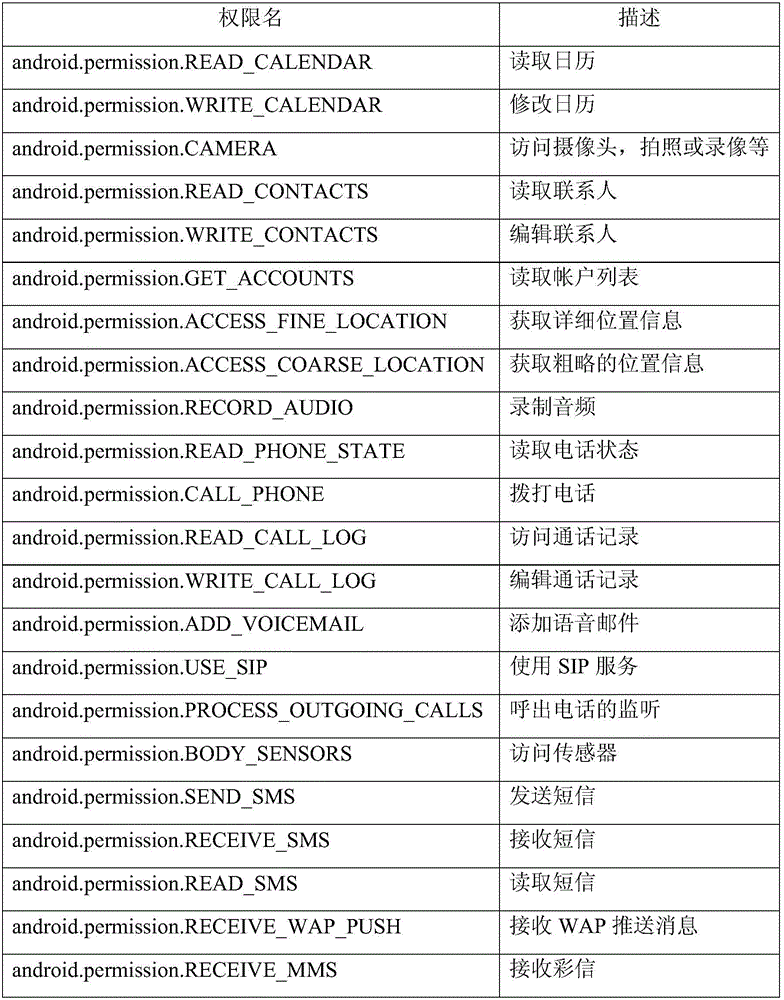
[0040] Among them, dangerous permissions refer to permissions that may obtain user privacy data, including the contents shown ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More