Network attack target prediction method based on neighbor similarity
A technology of neighbor similarity and network attack, applied in the field of network security, can solve problems such as restricting administrators' response strategies, attack target prediction, and insufficient prediction results, and achieve the effect of improving security
- Summary
- Abstract
- Description
- Claims
- Application Information
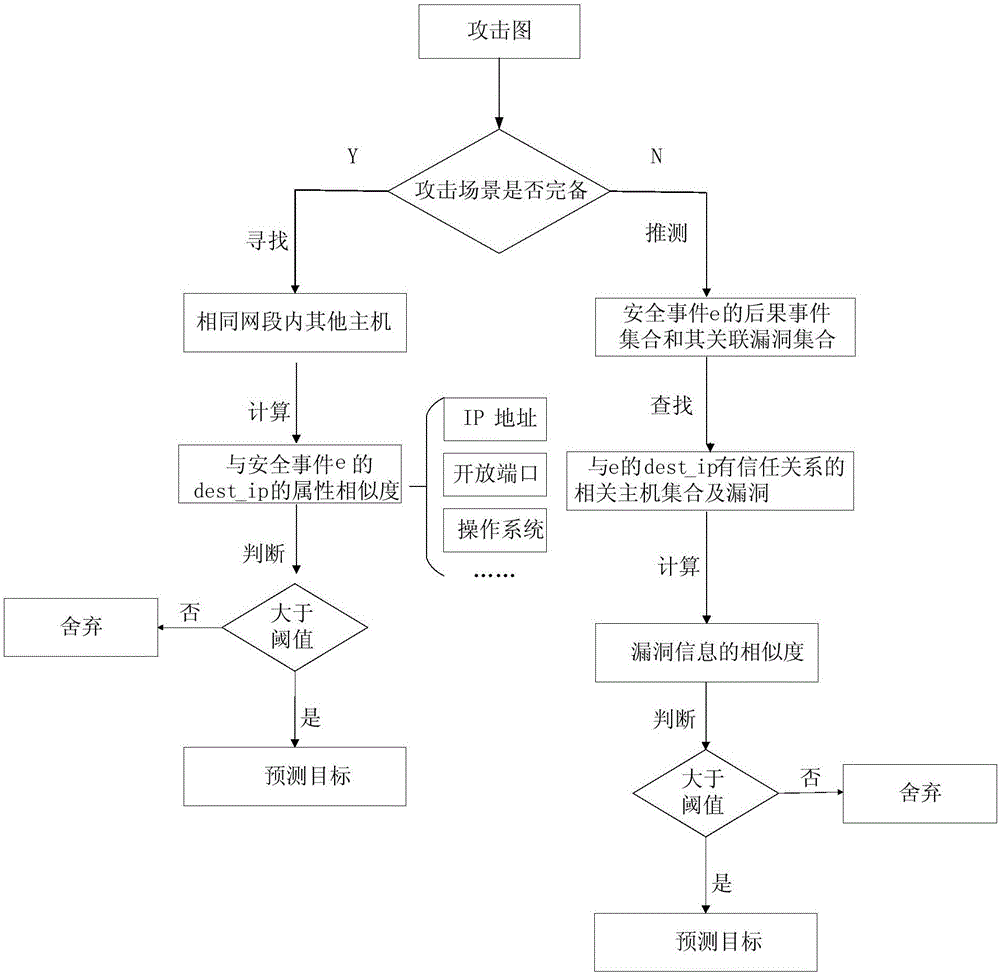
AI Technical Summary
Problems solved by technology
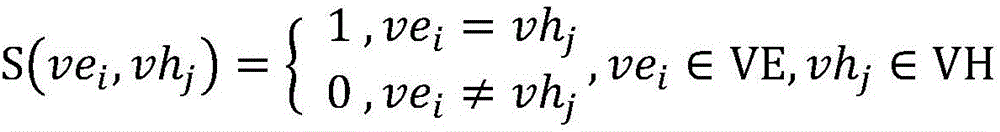
Method used
Image
Examples
Embodiment Construction
[0032] The technical solution of the present invention will be described in further detail below in conjunction with the examples. The following examples are implemented on the premise of the technical solutions of the present invention, and detailed implementation methods and processes are given, but the protection scope of the present invention is not limited to the following examples.
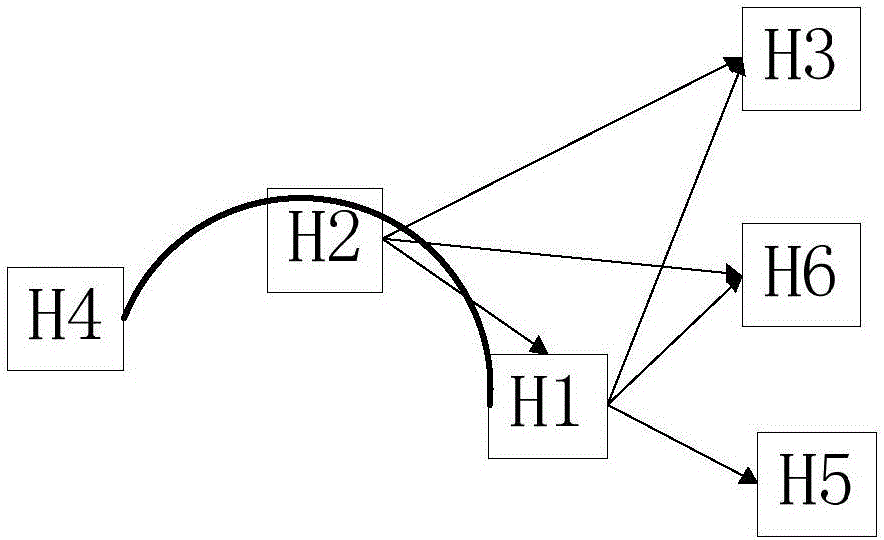
[0033]In order to better understand the method proposed in this embodiment, five hosts H1, H2, H3, H4, H5, and H6 under a network installed with an intrusion detection device are selected. Among them, H1 has a trust relationship with H3, H5, and H6, and H2 has a trust relationship with H1, H3, and H6, as shown in the table below. H4, H2, and H1 are the three hosts involved in a complete attack, and their connection relationship diagram is shown in the host relationship diagram ( figure 2 ) shown.
[0034] attack path H4->H2->H1 trust relationship H2->H1,H3,H6 trust...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More