Unix white-list control method based on hook technology
A control method and whitelist technology, which are applied in the fields of instruments, electrical digital data processing, platform integrity maintenance, etc., and can solve the problem that the computing environment is no longer safe.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0017] In order to make the technical problems, technical solutions and beneficial effects to be solved by the present invention clearer, the present invention will be described in detail below in conjunction with the accompanying drawings and embodiments. It should be noted that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
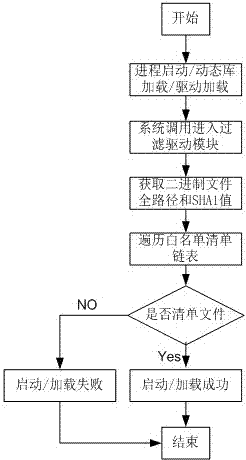
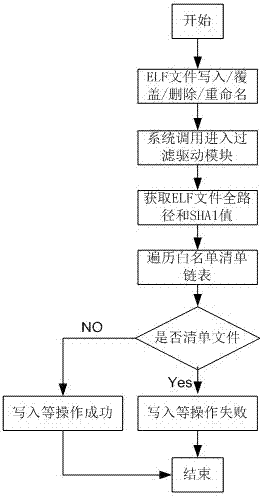
[0018] The Unix whitelist control method based on hook technology adds a filter driver module on the Unix system, and the filter driver module is implemented in a kernel-driven manner, and is installed and started by the whitelist main service process; the filter driver module is used throughout On the operating system, control the startup of processes in the non-white list, control the loading of dynamic libraries in the non-white list, control the loading of drivers in the non-white list, control the addition of binary files, and control the writing, overwriting, and replaceme...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More