Information protection method and system of sensitive content data
A content data and information protection technology, applied in digital data protection, electronic digital data processing, instruments, etc., can solve the problem of low security, achieve high security, reduce the risk of cracking, and reduce the risk of leakage.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0039] The following will clearly and completely describe the technical solutions in the embodiments of the present invention in conjunction with the accompanying drawings in the embodiments of the present invention. It should be understood that the described embodiments are only some of the embodiments of the present invention, not all of them. Example. Based on the embodiments of the present invention, all other embodiments obtained by those skilled in the art without making creative efforts belong to the protection scope of the present invention.
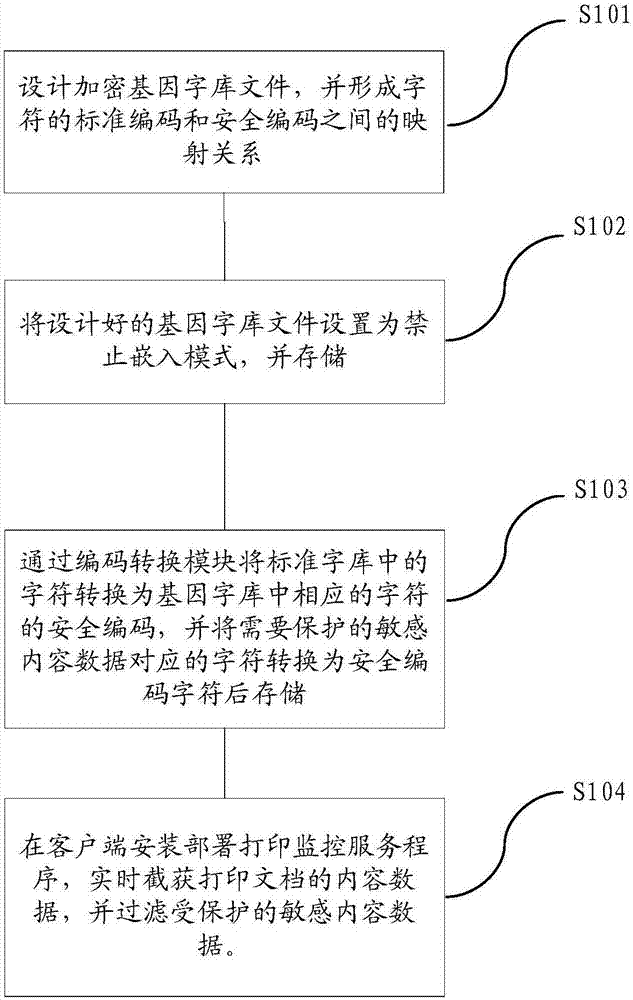
[0040] Such as figure 1 As shown, a file sensitive content data information protection method mainly includes the following steps:
[0041] S101: First, design the genetic font file, the genetic font includes characters and their security codes, the security code of each character in the genetic font and the standard code of the character in the standard font form a many-to-one Mapping relations.
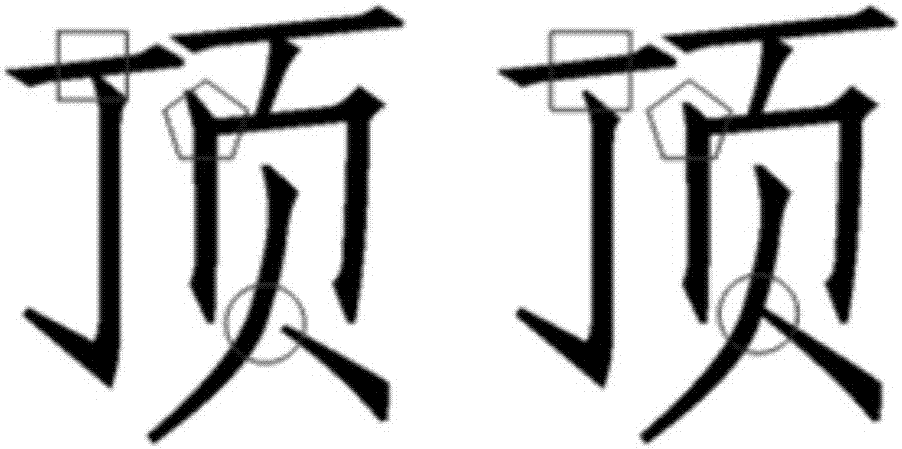
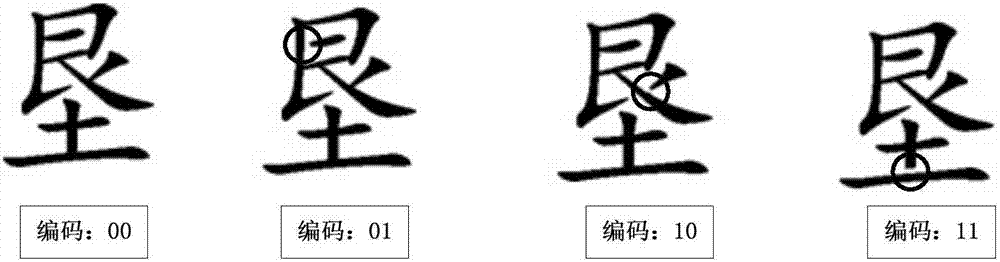
[0042] Preferably, in the ge...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More