Method and device for verifying verification code
A verification method and a verification device technology, which are applied in the field of Internet security, can solve problems such as low security, and achieve the effect of improving security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
[0061] The execution subject of a verification code verification method provided in the embodiment of this application may be a server, for example, a server of an e-mail website, a server of a forum website, a cloud storage server, etc.; or, the execution subject of this method may also be a terminal device, For example, a smart phone, a tablet computer, a notebook computer or a desktop computer, etc.; in addition, the execution subject of the method may also be an application program or the like. The executive body described does not constitute a limitation to this application.
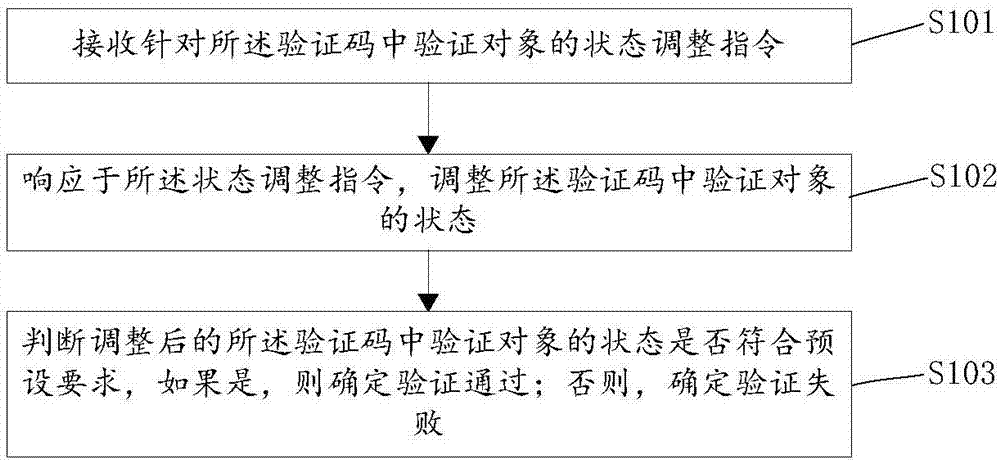
[0062] Please refer to figure 1 , figure 1 It shows a schematic flowchart of the implementation of a verification code verification method provided in Embodiment 1 of the present application. The method can include:
[0063] S101. Receive a state adjustment instruction for the verification object in the verification code;
[0064] The verification code can be generated by the server or the termi...
Embodiment 2
[0103] Based on the aforementioned embodiment 1, the inventive concept of the present application has been described in detail. In order to facilitate a better understanding of the technical features, means and effects of the present application, the verification code verification method of the present application will be further described below, thus forming another of the present application. Example.
[0104] The verification code verification process in Embodiment 2 of this application is similar to the verification code verification process described in Embodiment 1. For other steps not introduced in Embodiment 2, please refer to the relevant description in Embodiment 1, which will not be repeated here repeat.
[0105] Please refer to figure 2 , figure 2 A schematic flow chart showing the implementation of a verification code verification method provided in Embodiment 2 of the present application is shown. In this embodiment, the displayed verification code includes ...
Embodiment 3
[0128] Based on the aforementioned embodiment 1 and embodiment 2, the inventive concept of the present application is described in detail. In order to facilitate a better understanding of the technical features, means and effects of the present application, the verification code verification method of the present application will be further explained below, thus forming Yet another embodiment of the present application.
[0129] The verification code verification process in Embodiment 3 of the present application is similar to the verification code verification process described in Embodiment 1 and Embodiment 2. For other steps not introduced in Embodiment 3, please refer to Embodiment 1 and Embodiment 2. The related descriptions will not be repeated here.
[0130] Please refer to Figure 5 , Figure 5It shows a schematic flowchart of an implementation of a verification code verification method provided in Embodiment 3 of the present application. In this embodiment, the ver...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More