Encryption system, homomorphic signature method, and homomorphic signature program
An encryption system and homomorphic technology, applied in transmission systems, digital transmission systems, homomorphic encryption communications, etc., can solve problems such as inability to edit messages
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment approach 1
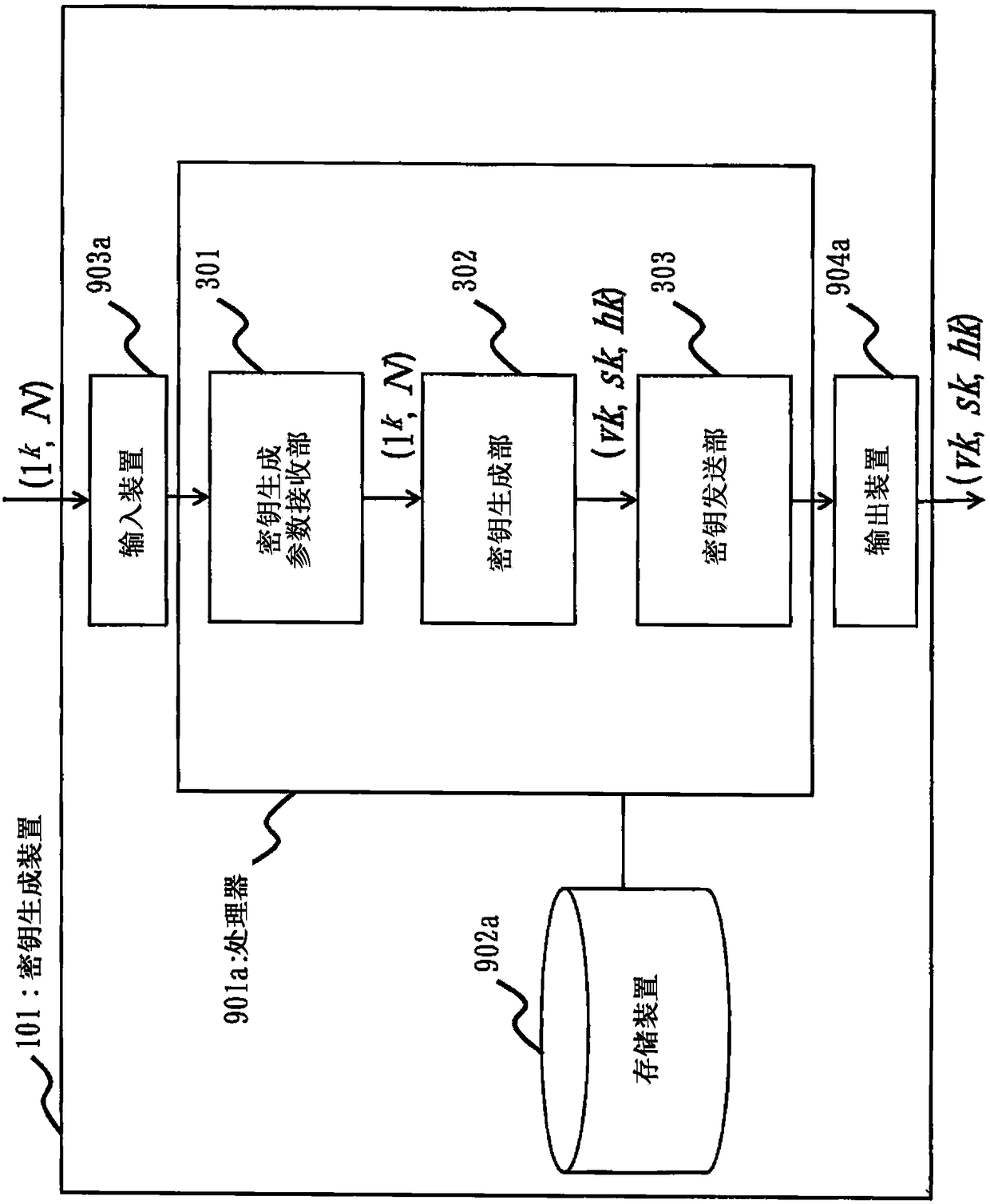
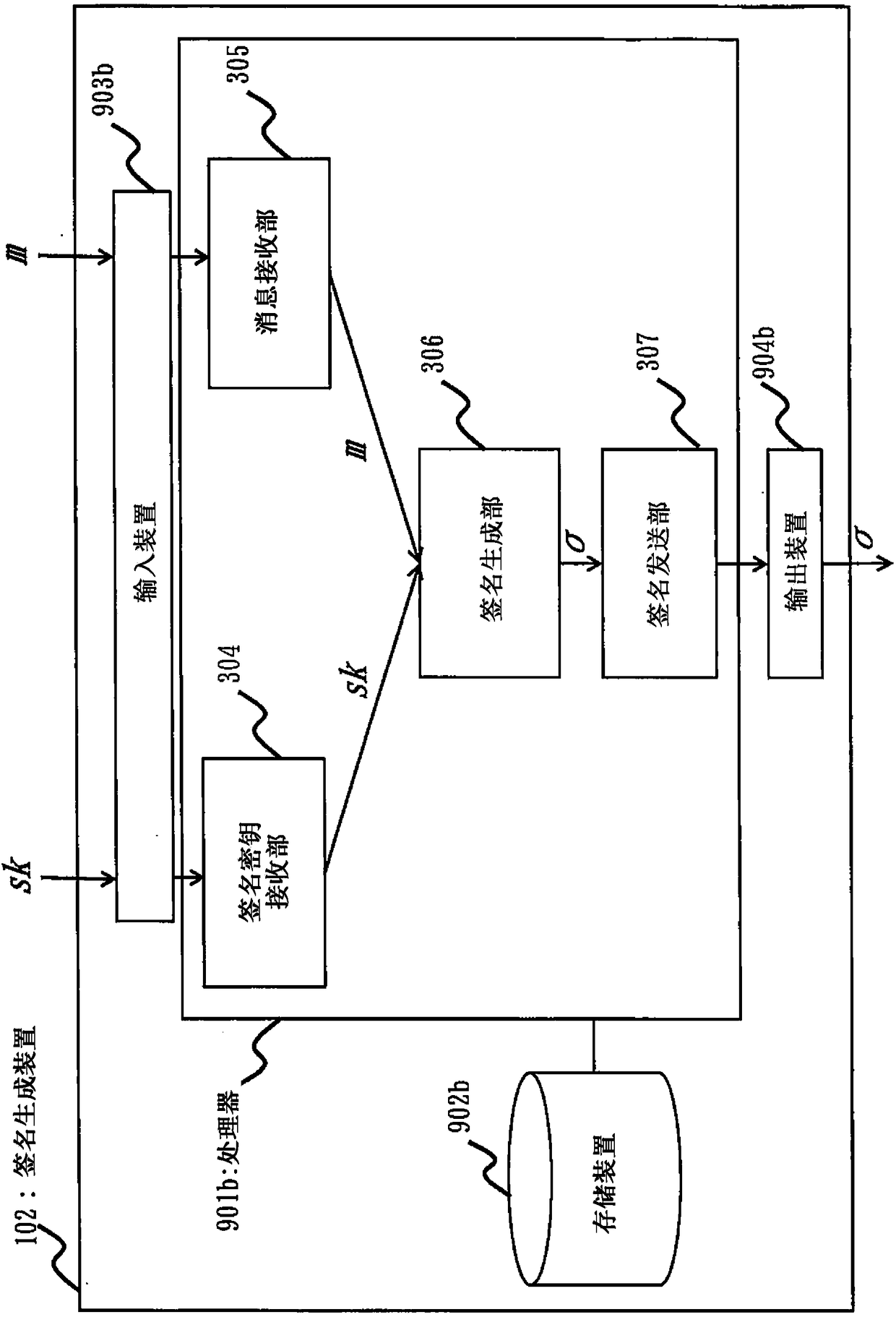
[0067] ***Description of structure***
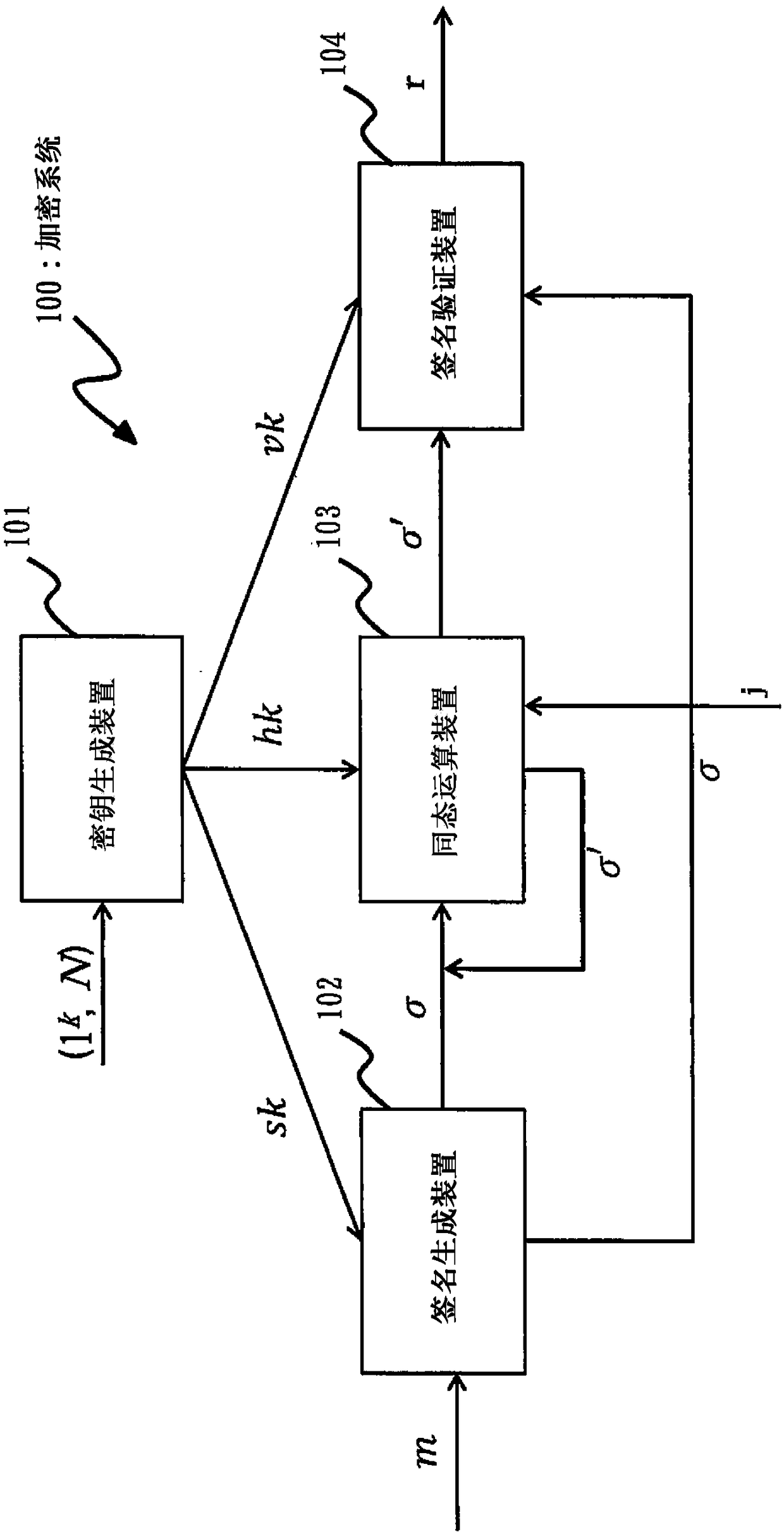
[0068] figure 1 It is a system configuration diagram of the encryption system 100 of this embodiment.
[0069] Such as figure 1 As shown, the encryption system 100 has a key generation device 101, a signature generation device 102, a homomorphic operation device 103, and a signature verification device 104.
[0070] First, use figure 1 The outline of the function of each device of the encryption system 100 will be described.
[0071] The key generation device 101 obtains key generation parameters (1 k , N), execute a key generation algorithm to generate a verification key vk, a signature key sk, and a homomorphic key hk.
[0072] Here, in order to ensure the security of the method in the encryption system 100, the signature key sk is only given to a user or device that is permitted to perform signature generation. In addition, the homomorphic key hk is only given to users or devices permitted to perform homomorphic operations. The signature key ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More