Patents
Literature
5129results about "Coding/ciphering apparatus" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
Electronic content delivery system
InactiveUS6226618B1Key distribution for secure communicationDigital data processing detailsDelivery systemSystem safety
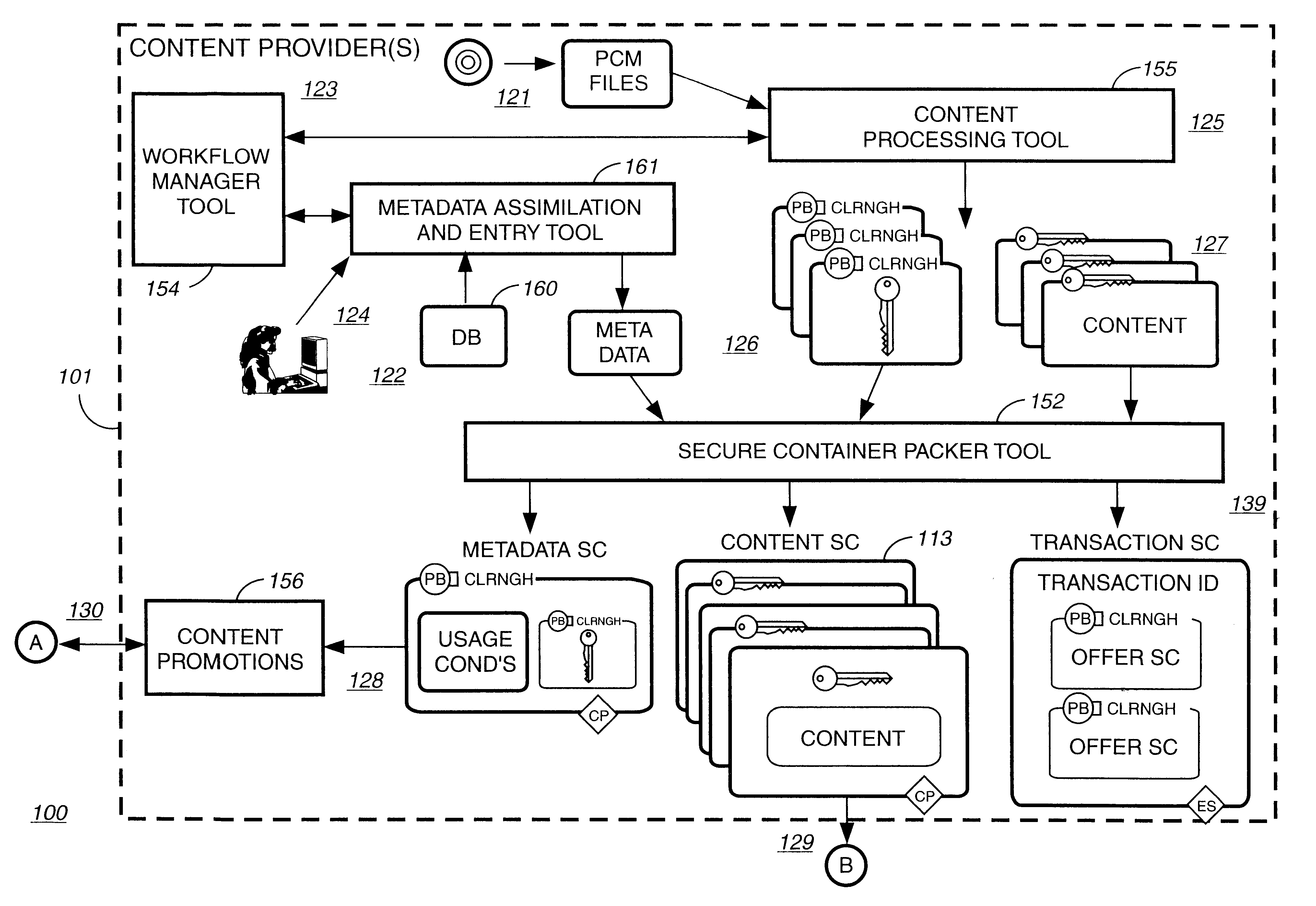
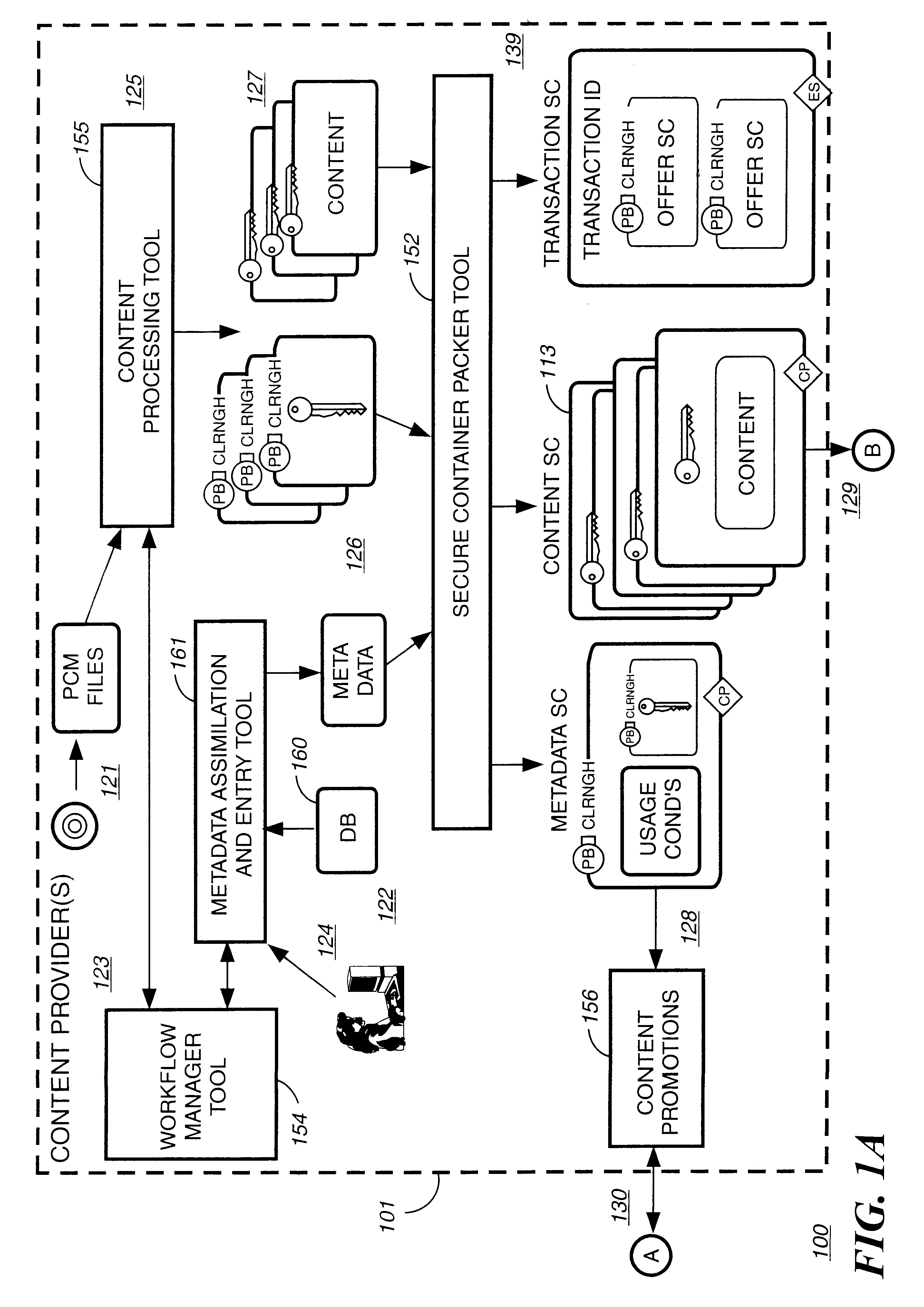
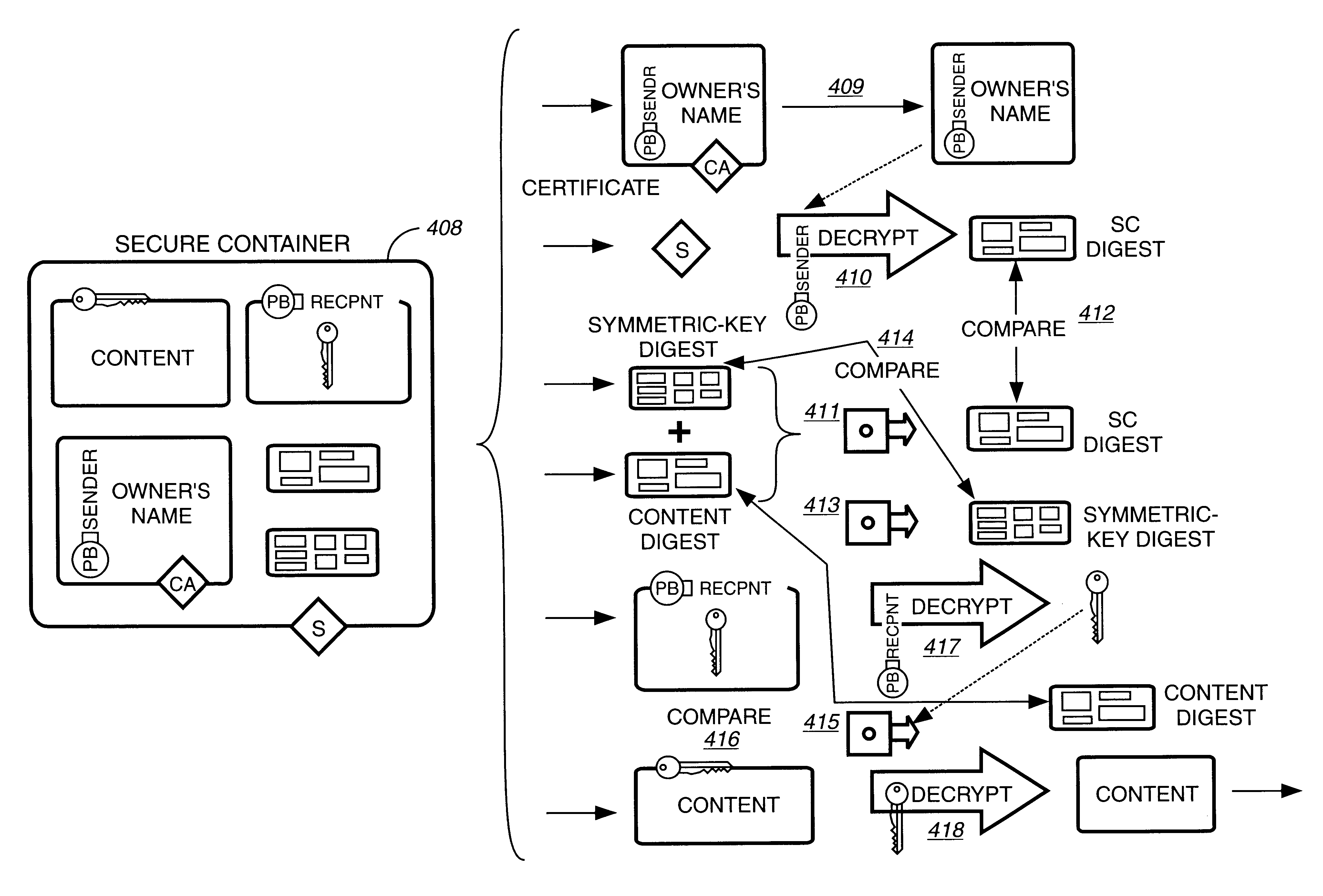
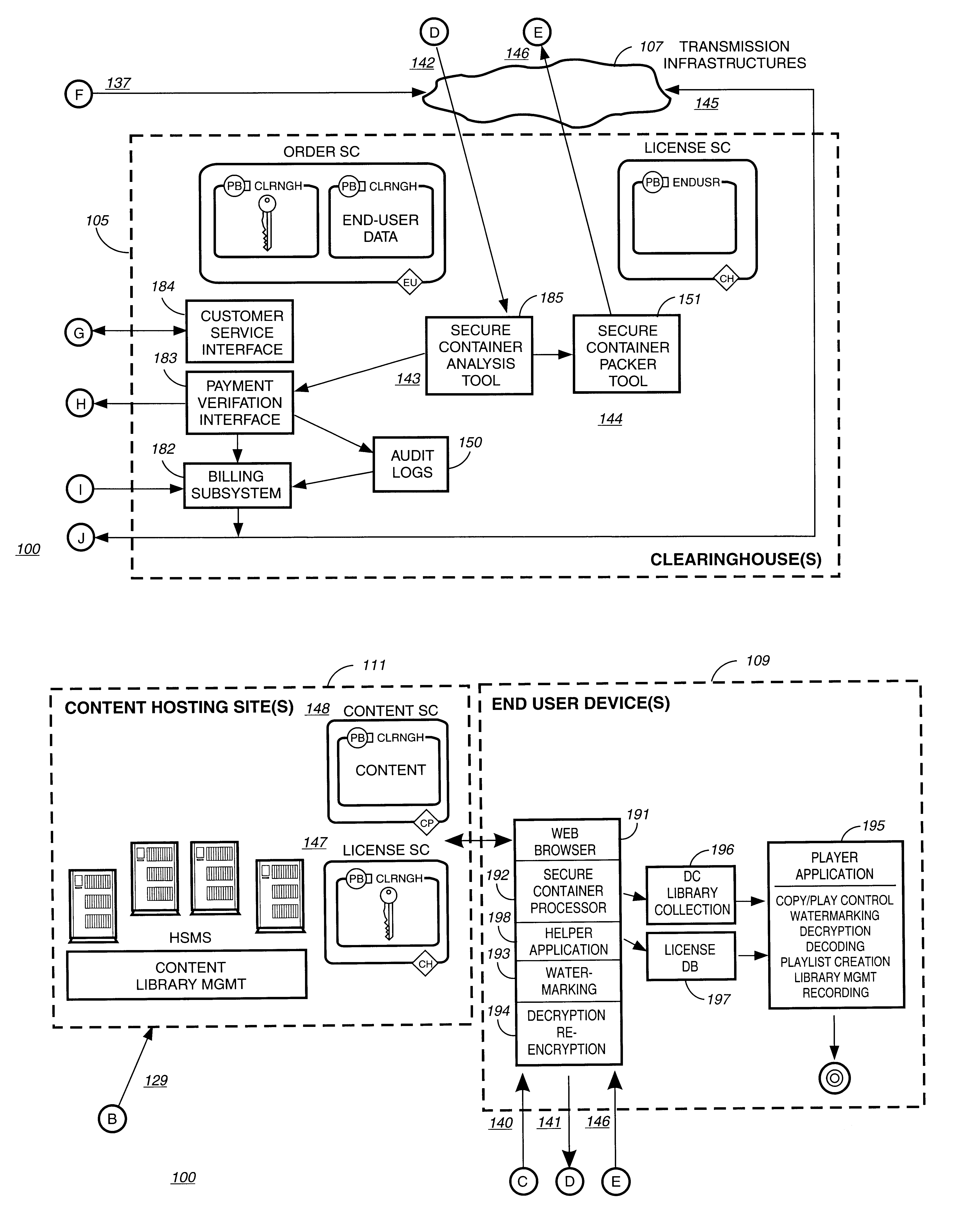
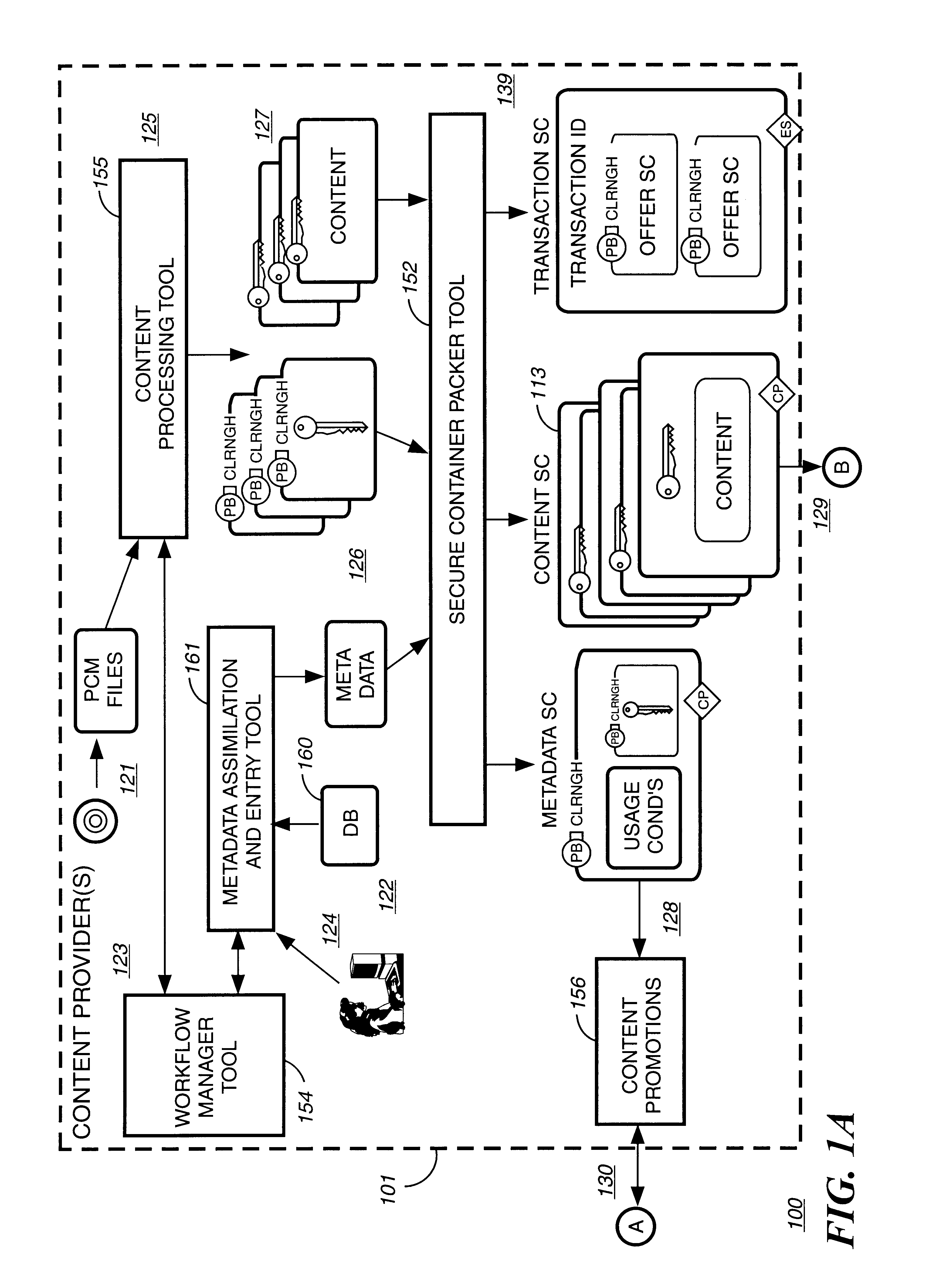
Disclosed is a method and apparatus of securely providing data to a user's system. The data is encrypted so as to only be decryptable by a data decrypting key, the data decrypting key being encrypted using a first public key, and the encrypted data being accessible to the user's system, the method comprising the steps of: transferring the encrypted data decrypting key to a clearing house that possesses a first private key, which corresponds to the first public key; decrypting the data decrypting key using the first private key; re-encrypting the data decrypting key using a second public key; transferring the re-encrypted data decrypting key to the user's system, the user's system possessing a second private key, which corresponds to the second public key; and decrypting the re-encrypted data decrypting key using the second private key.
Owner:LEVEL 3 COMM LLC
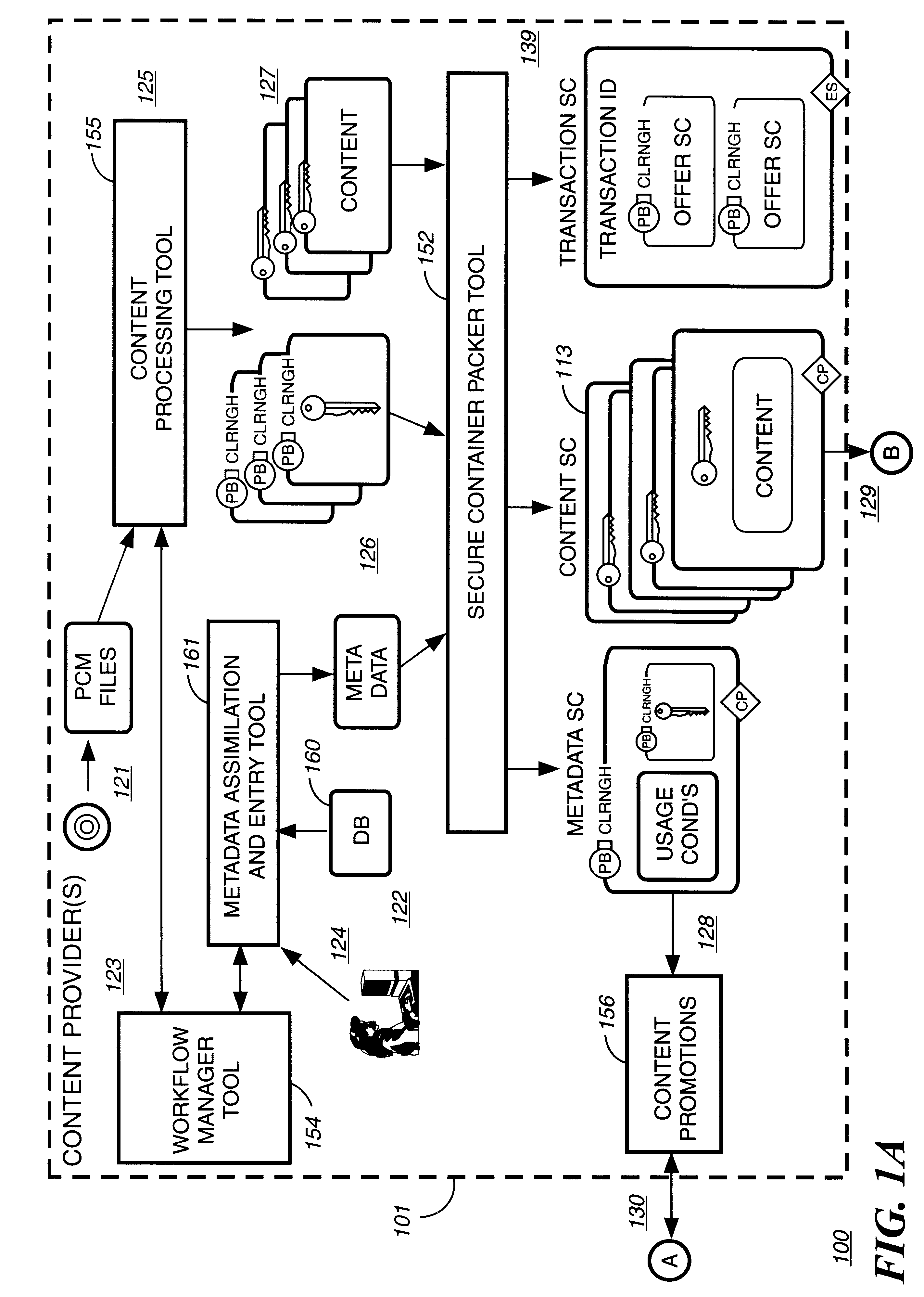
Automated method and apparatus to package digital content for electronic distribution using the identity of the source content
InactiveUS6345256B1Key distribution for secure communicationDigital data processing detailsDigital contentNumber content
A method to automatically retrieve data associated with content. An identifier is read that is stored on electronic readable medium storing content. The identifier is used to search a database for data associated with the content. Data that is associated with the content is retrieved as guided by the database. And the data retrieved is used to create a version of the content for electronic distribution. In accordance with another aspect of the invention, a computer readable medium is described to carry out the above method.
Owner:INT BUSINESS MASCH CORP
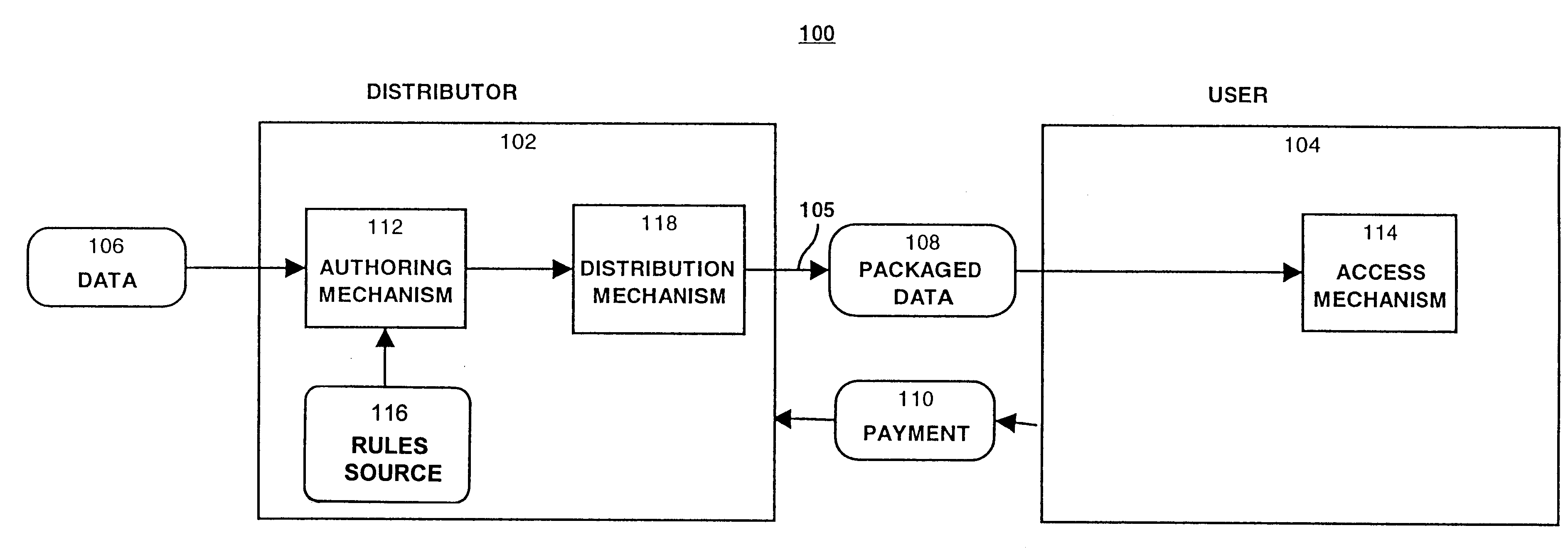
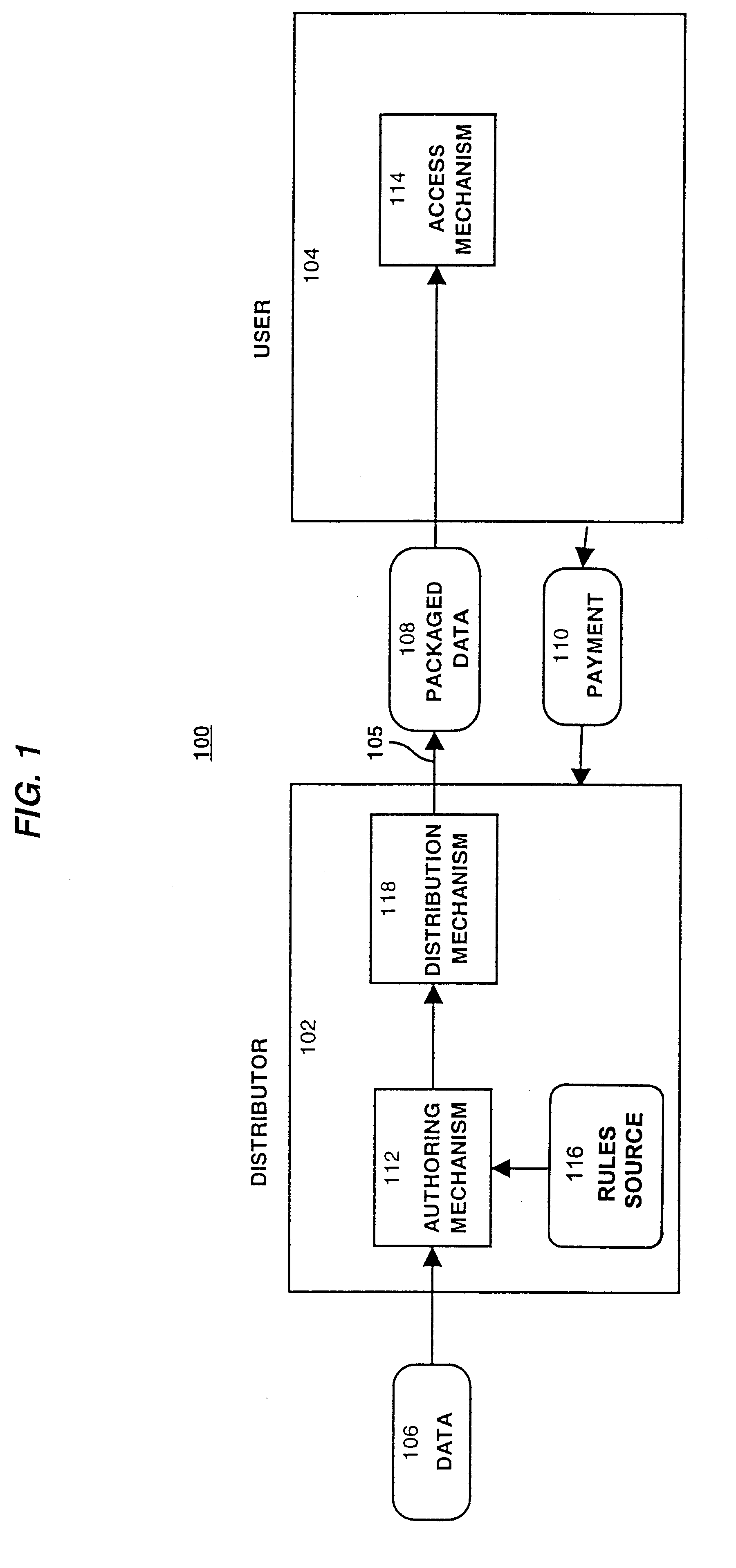
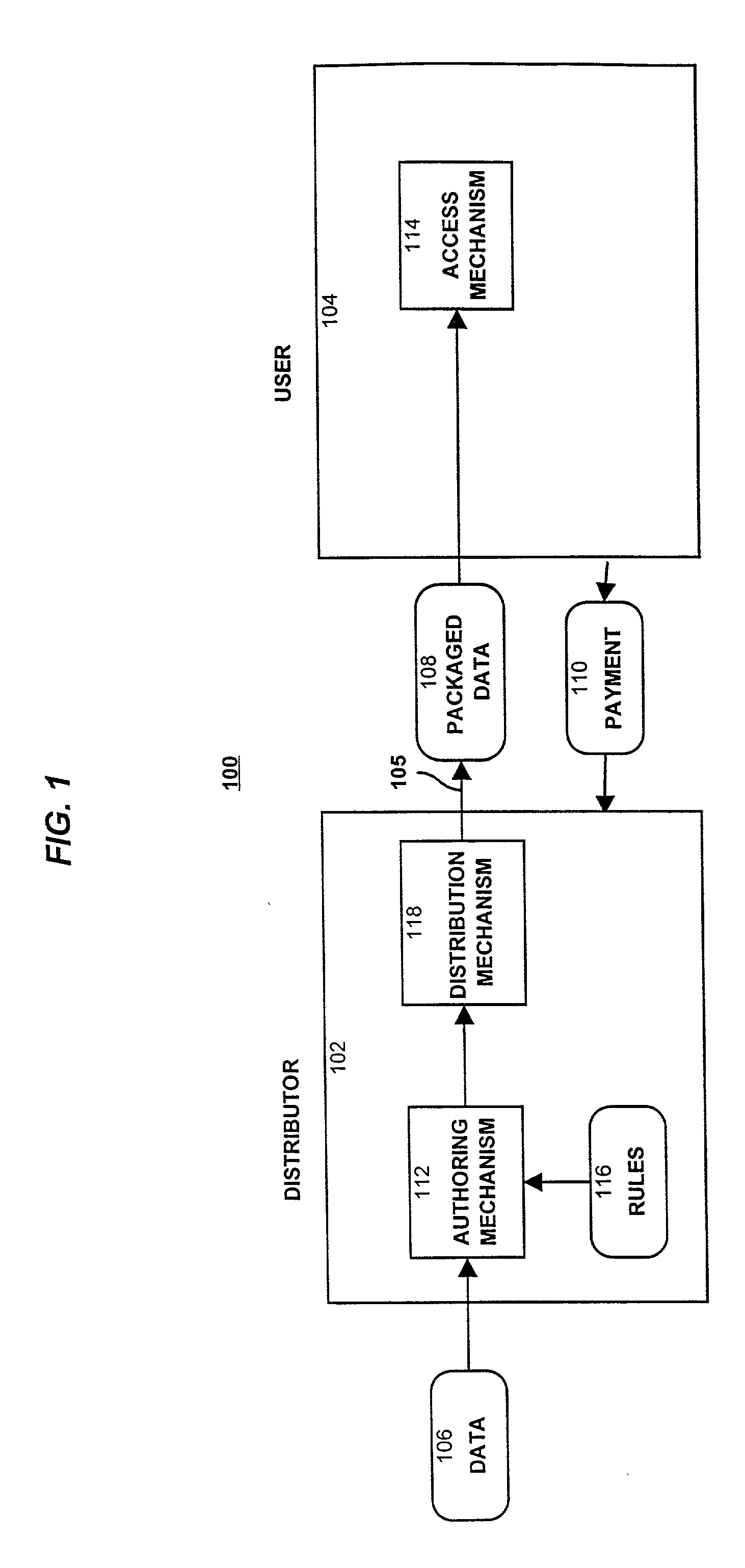
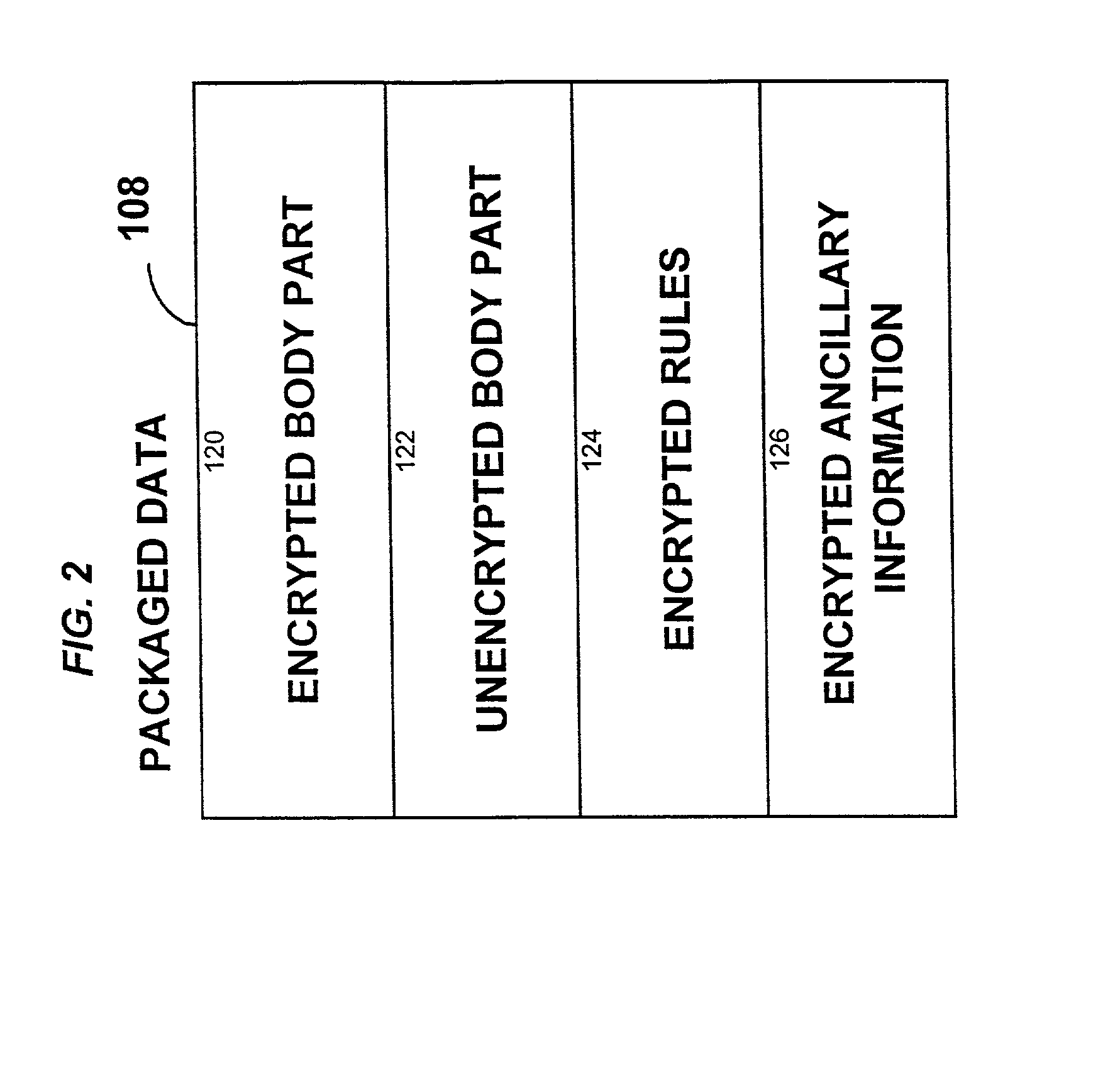
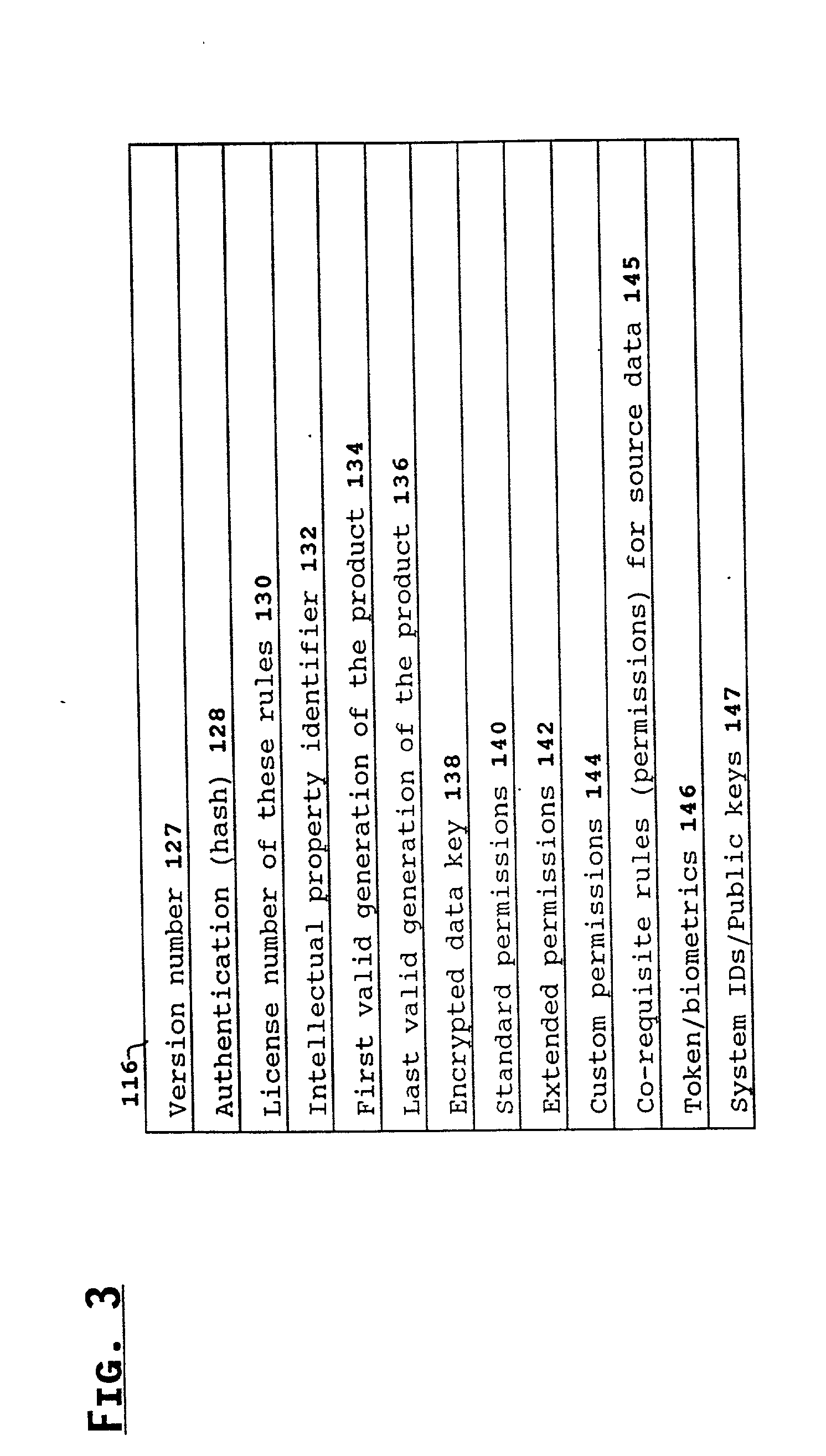
System for controlling access and distribution of digital property
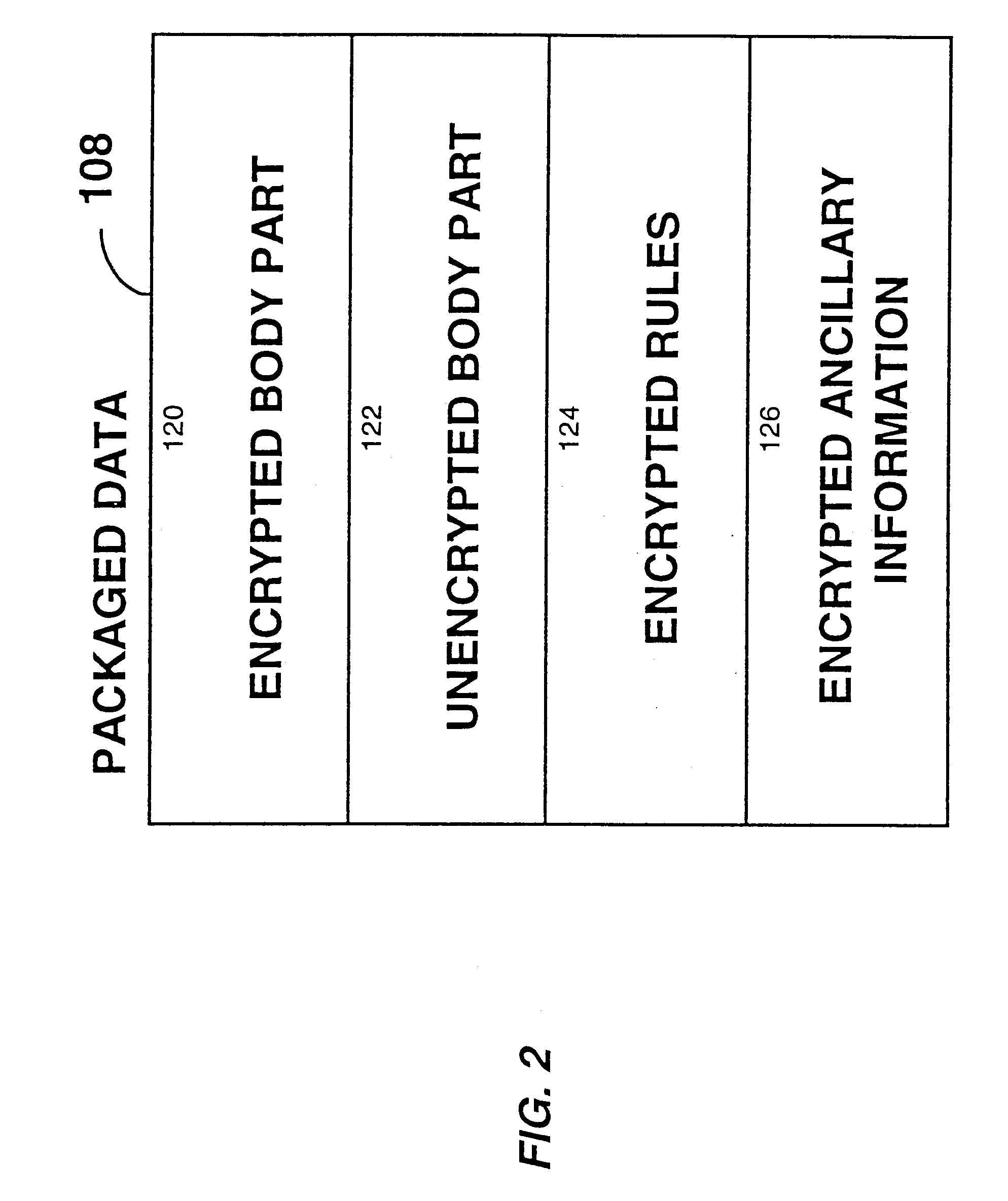
InactiveUS6314409B2Key distribution for secure communicationMultiple keys/algorithms usageTamper resistanceData access
A method and device are provided for controlling access to data. Portions of the data are protected and rules concerning access rights to the data are determined. Access to the protected portions of the data is prevented, other than in a non-useable form; and users are provided access to the data only in accordance with the rules as enforced by a mechanism protected by tamper detection. A method is also provided for distributing data for subsequent controlled use of those data. The method includes protecting portions of the data; preventing access to the protected portions of the data other than in a non-useable form; determining rules concerning access rights to the data; protecting the rules; and providing a package including: the protected portions of the data and the protected rules. A user is provided controlled access to the distributed data only in accordance with the rules as enforced by a mechanism protected by tamper protection. A device is provided for controlling access to data having protected data portions and rules concerning access rights to the data. The device includes means for storing the rules; and means for accessing the protected data portions only in accordance with the rules, whereby user access to the protected data portions is permitted only if the rules indicate that the user is allowed to access the portions of the data.
Owner:HANGER SOLUTIONS LLC
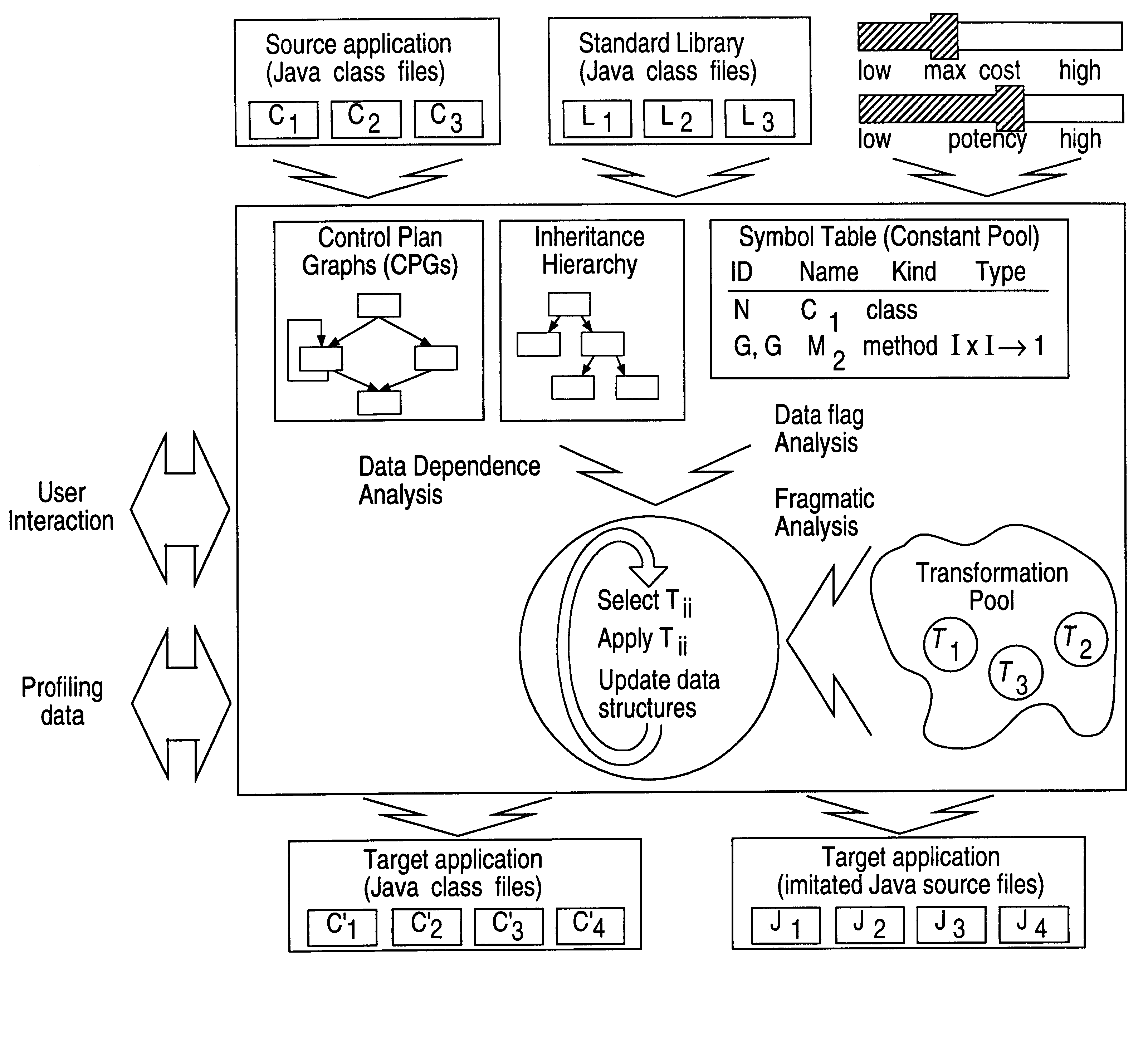
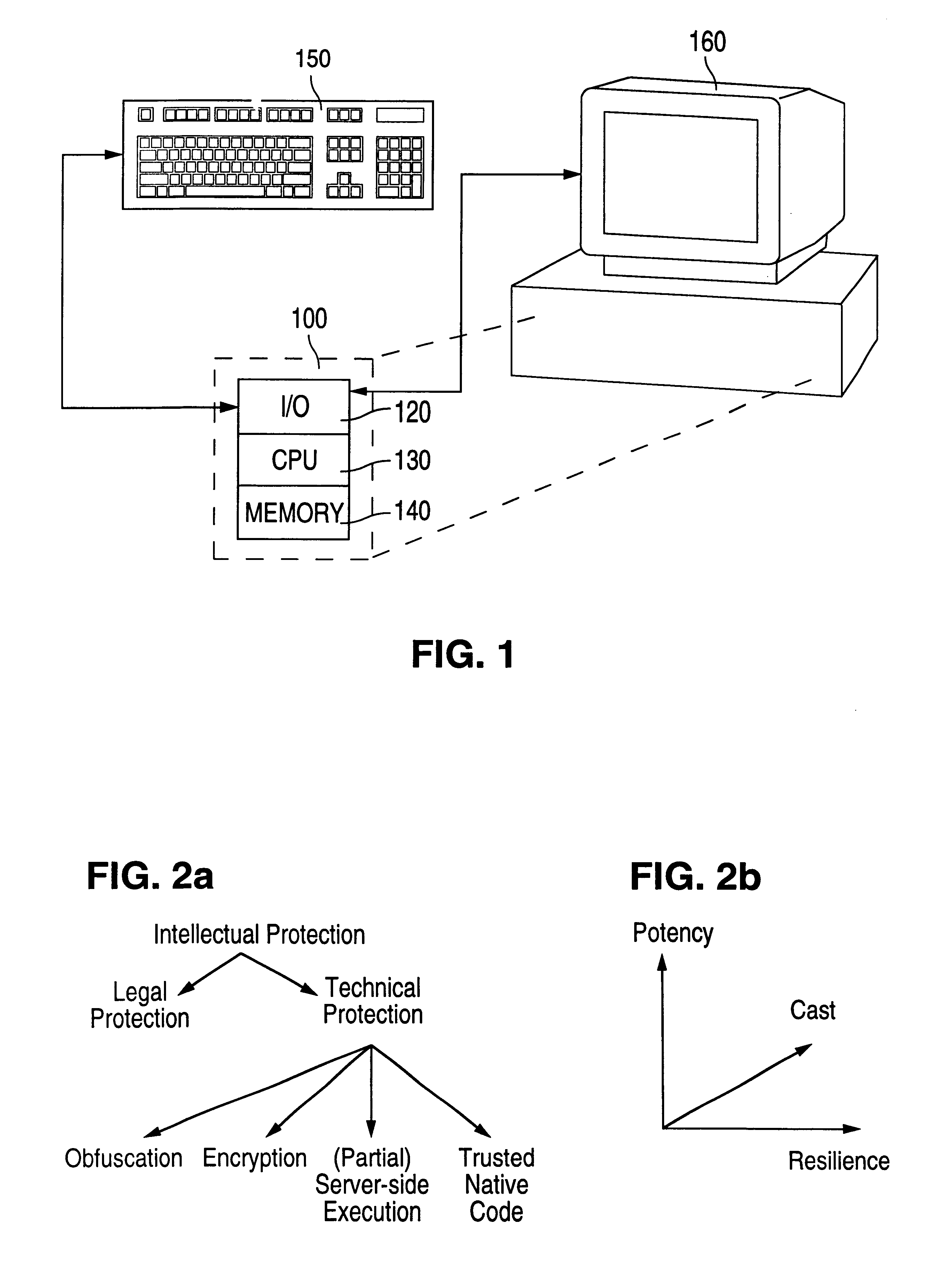
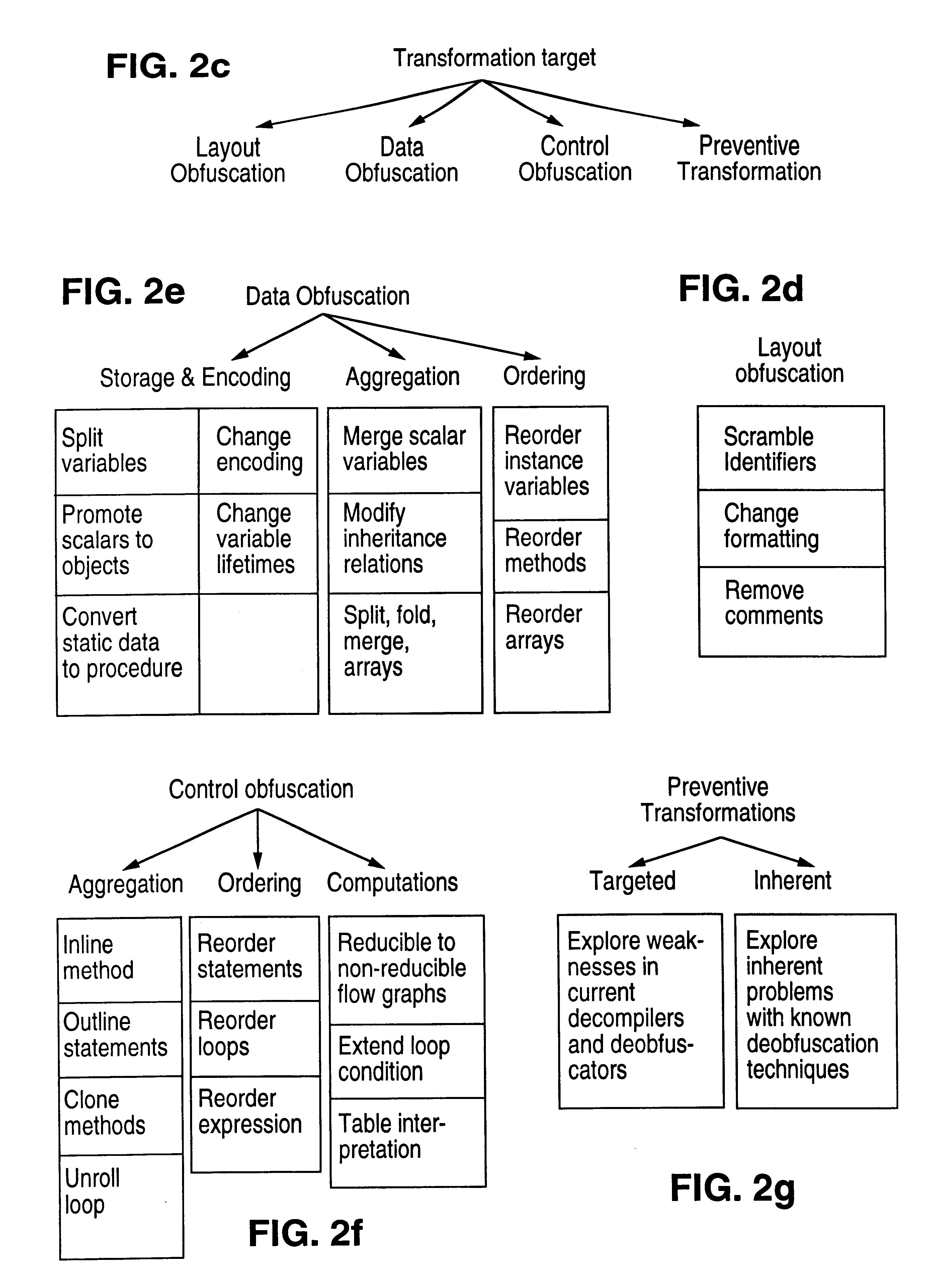
Obfuscation techniques for enhancing software security
InactiveUS6668325B1Guaranteed maximum utilizationDigital data processing detailsUnauthorized memory use protectionObfuscationTheoretical computer science
The present invention provides obfuscation techniques for enhancing software security. In one embodiment, a method for obfuscation techniques for enhancing software security includes selecting a subset of code (e.g., compiled source code of an application) to obfuscate, and obfuscating the selected subset of the code. The obfuscating includes applying an obfuscating transformation to the selected subset of the code. The transformed code can be weakly equivalent to the untransformed code. The applied transformation can be selected based on a desired level of security (e.g., resistance to reverse engineering). The applied transformation can include a control transformation that can be creating using opaque constructs, which can be constructed using aliasing and concurrency techniques. Accordingly, the code can be obfuscated for enhanced software security based on a desired level of obfuscation (e.g., based on a desired potency, resilience, and cost).
Owner:INTERTRUST TECH CORP
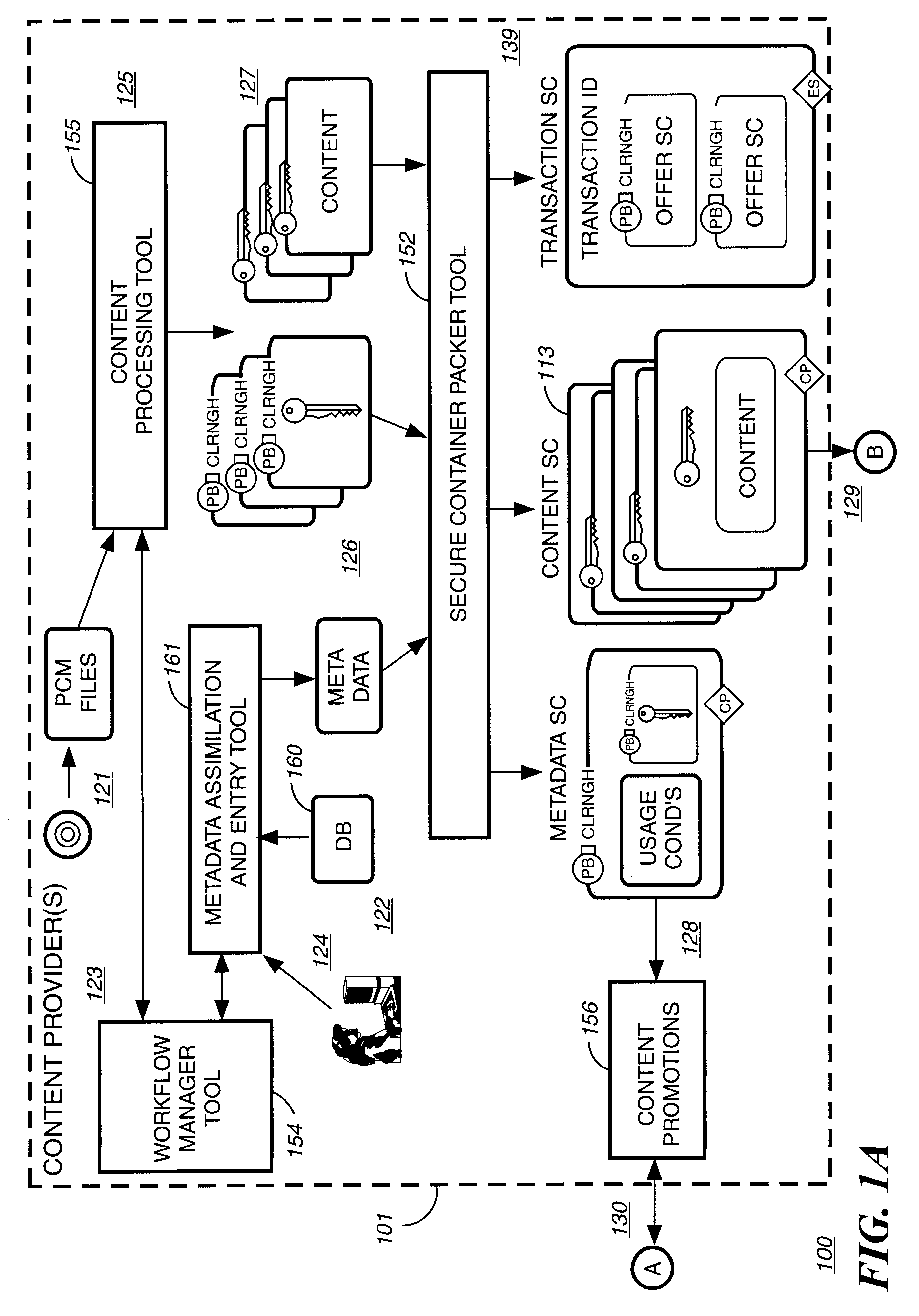
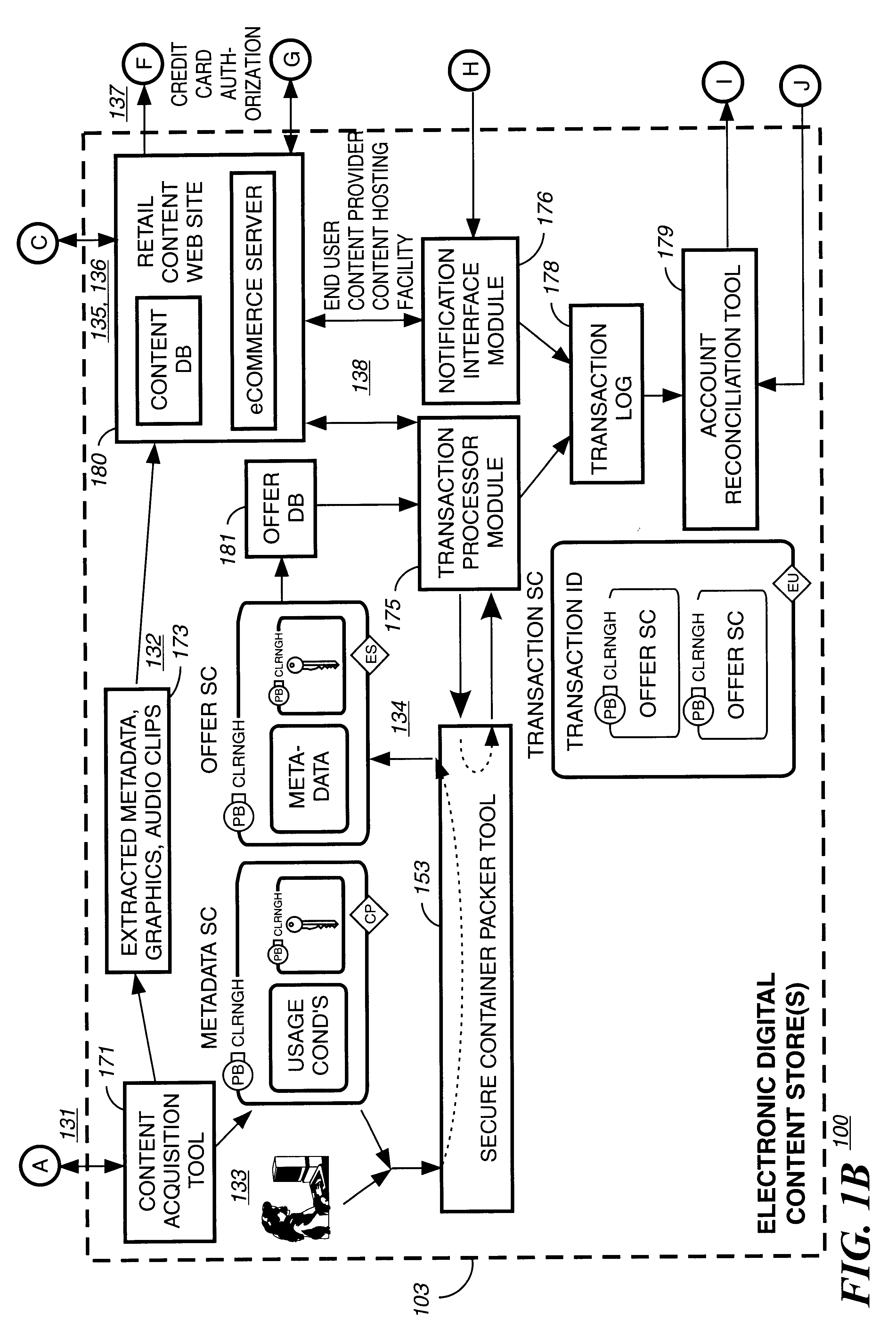
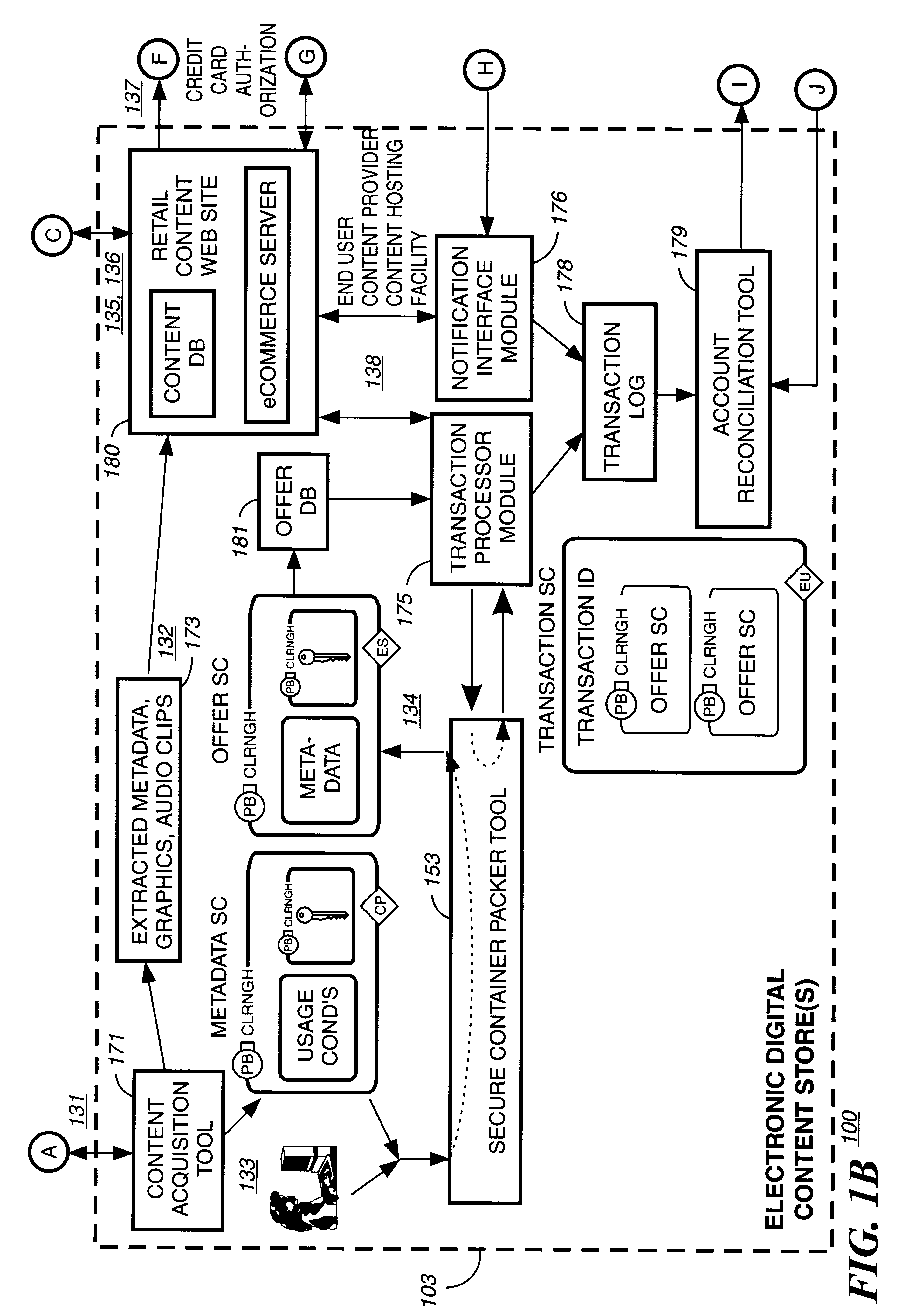
Secure electronic content distribution on CDS and DVDs
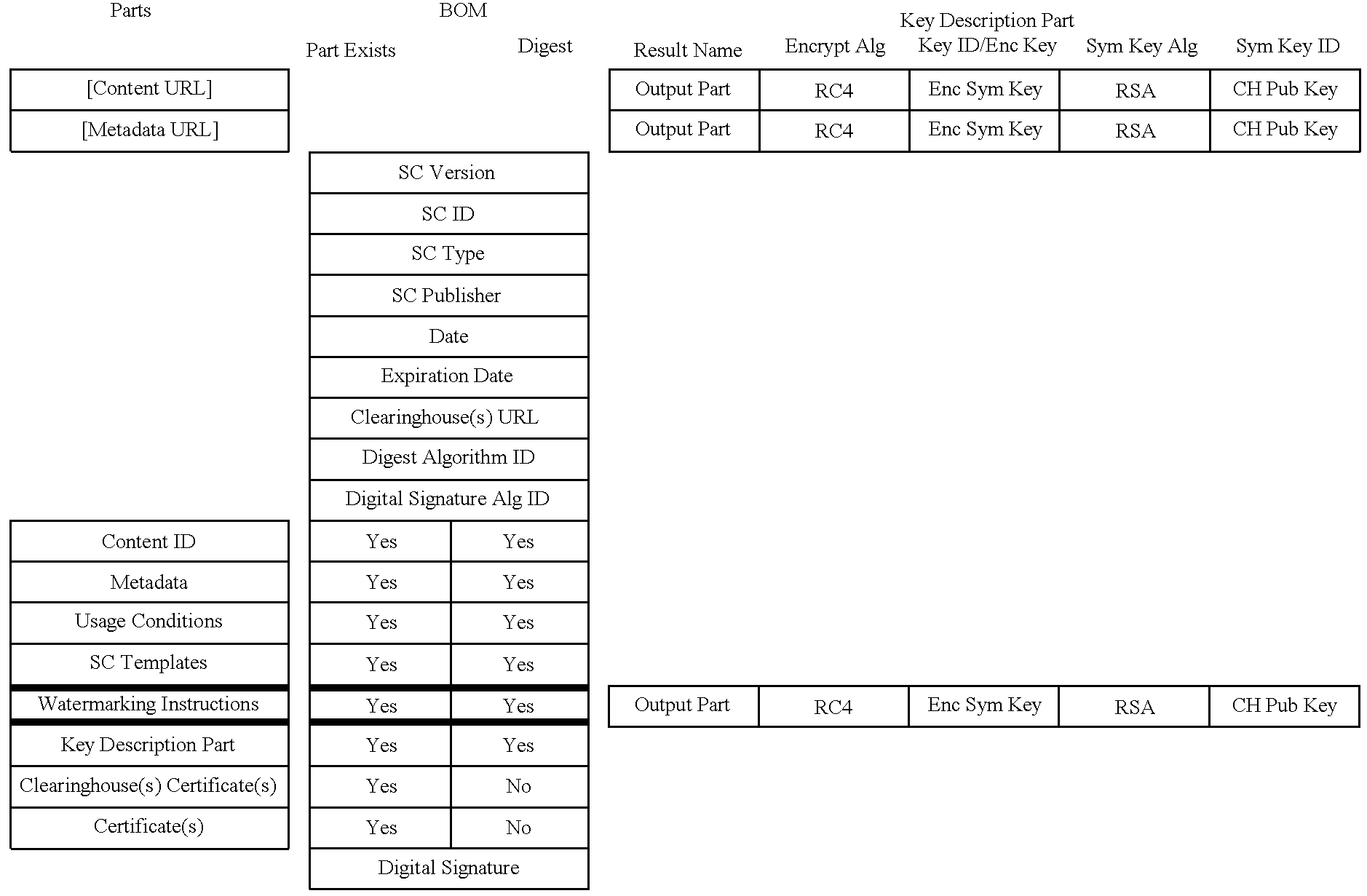
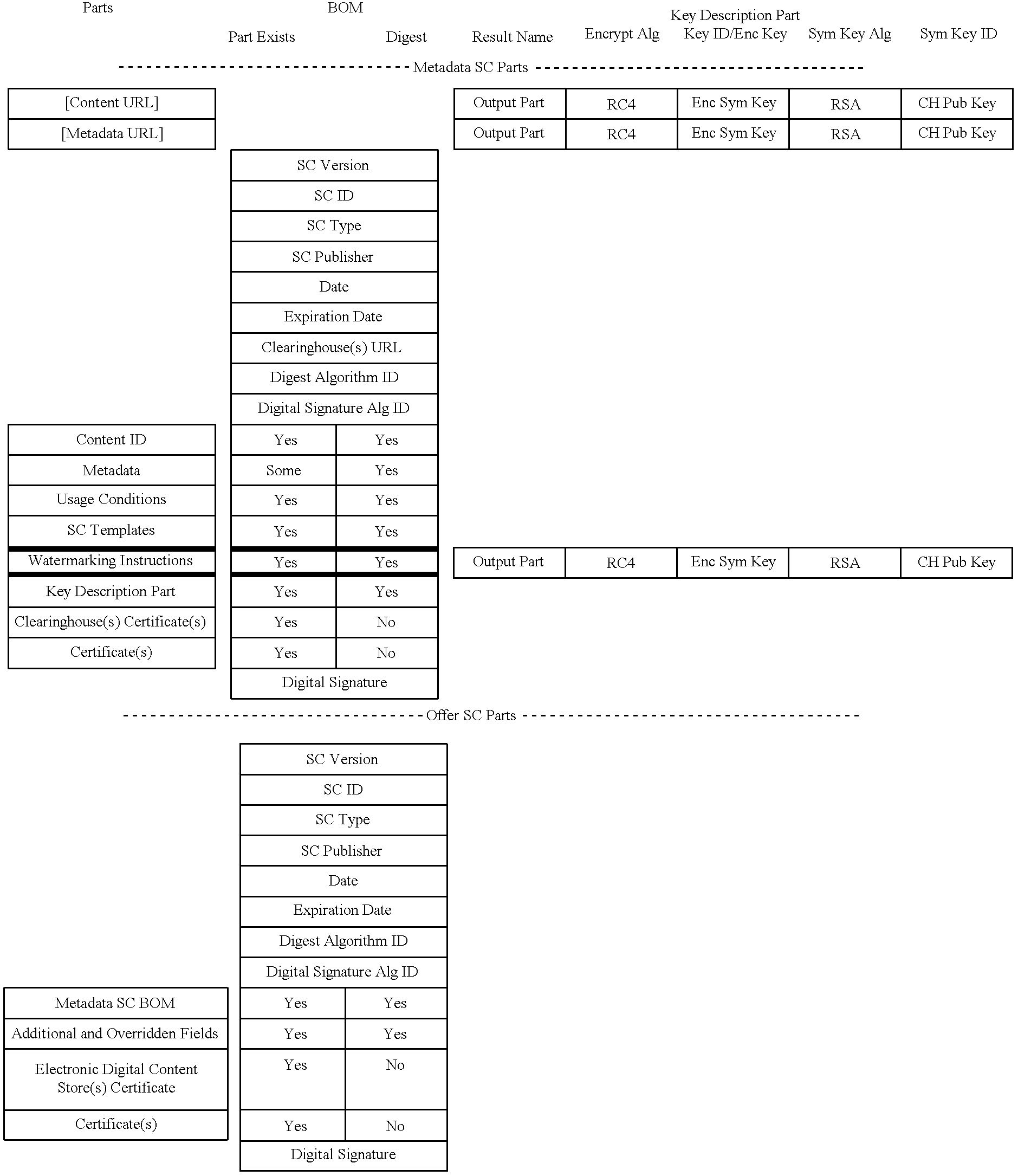
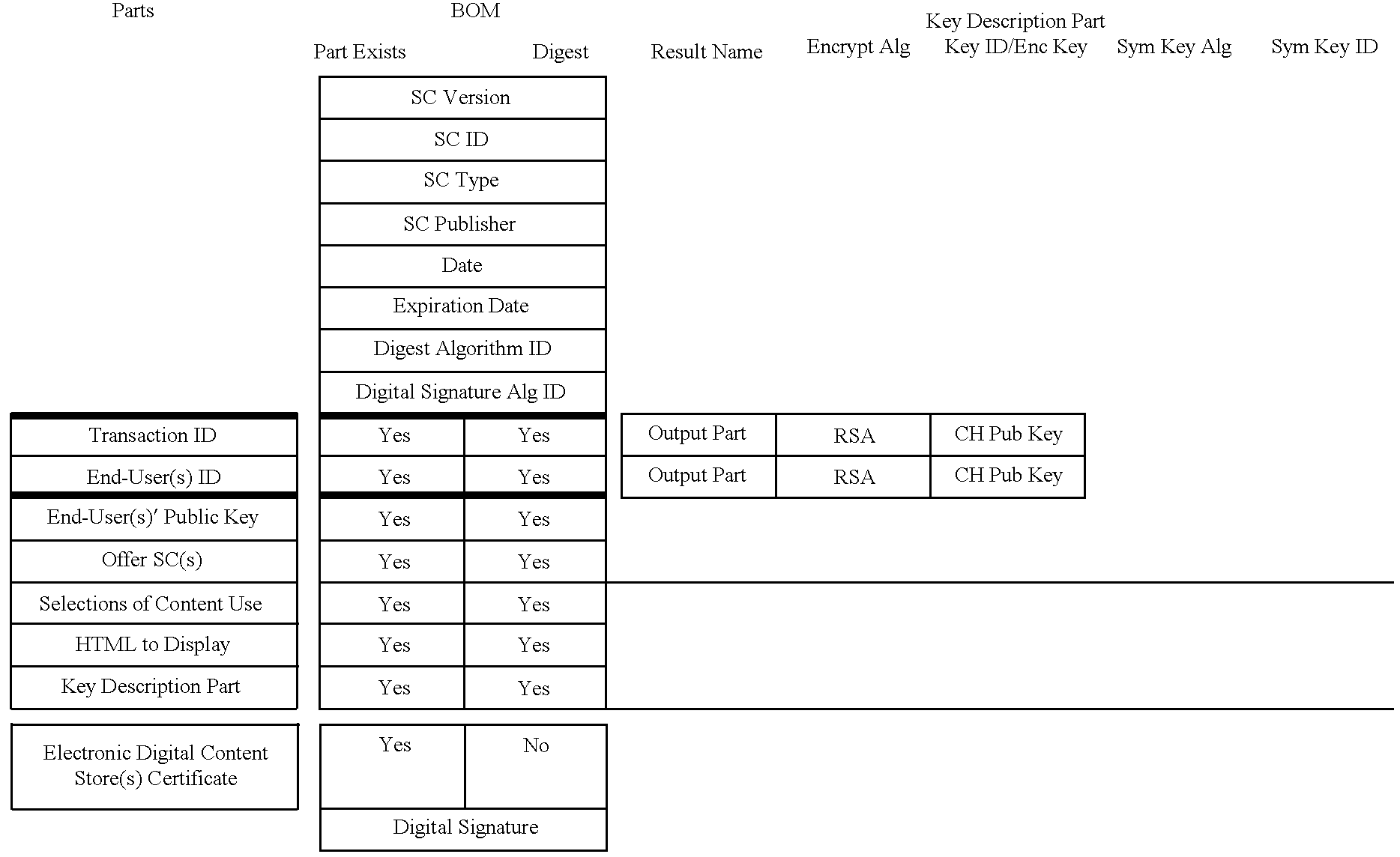
InactiveUS6611812B2Key distribution for secure communicationDigital data processing detailsDigital contentComputer terminal
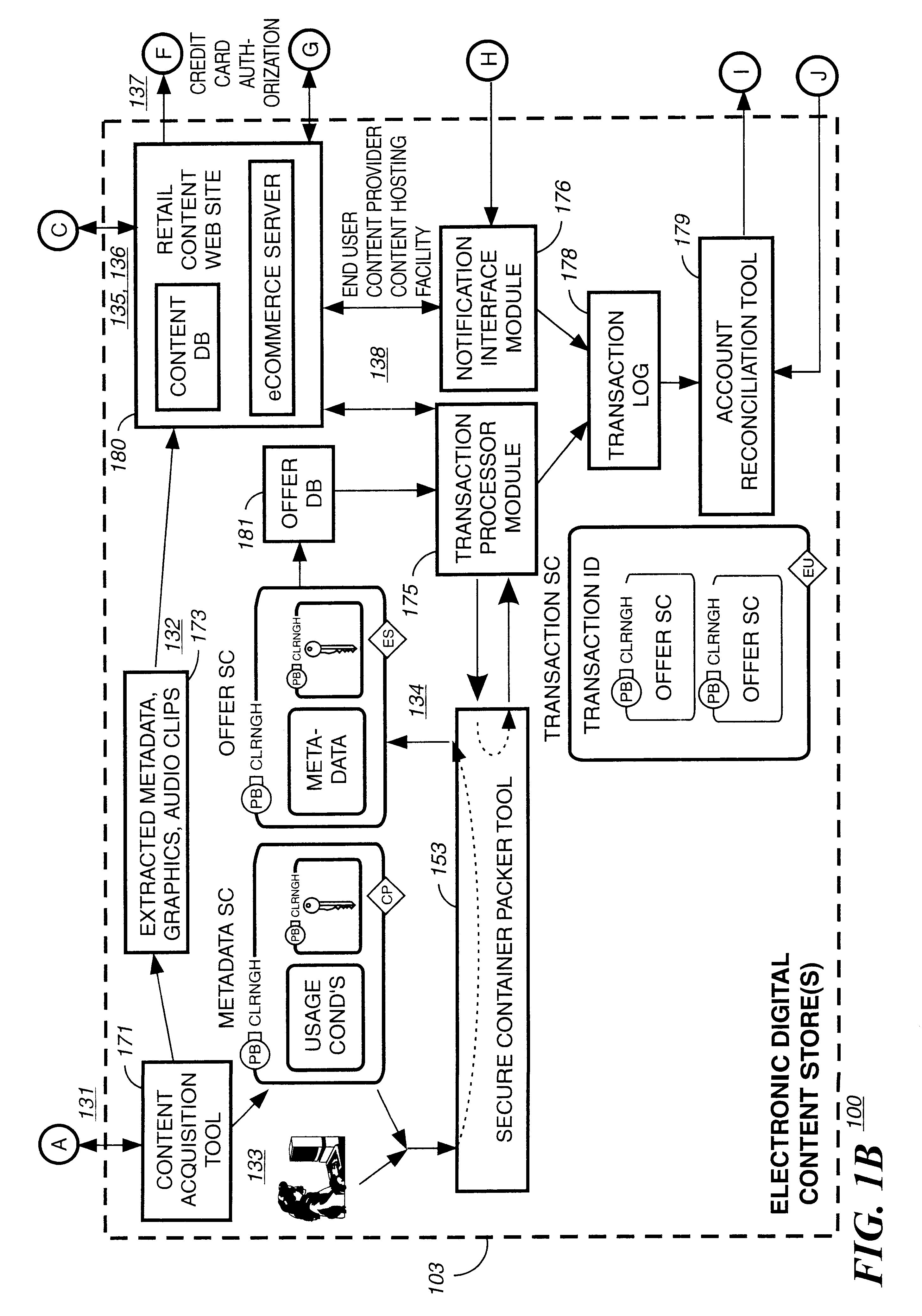
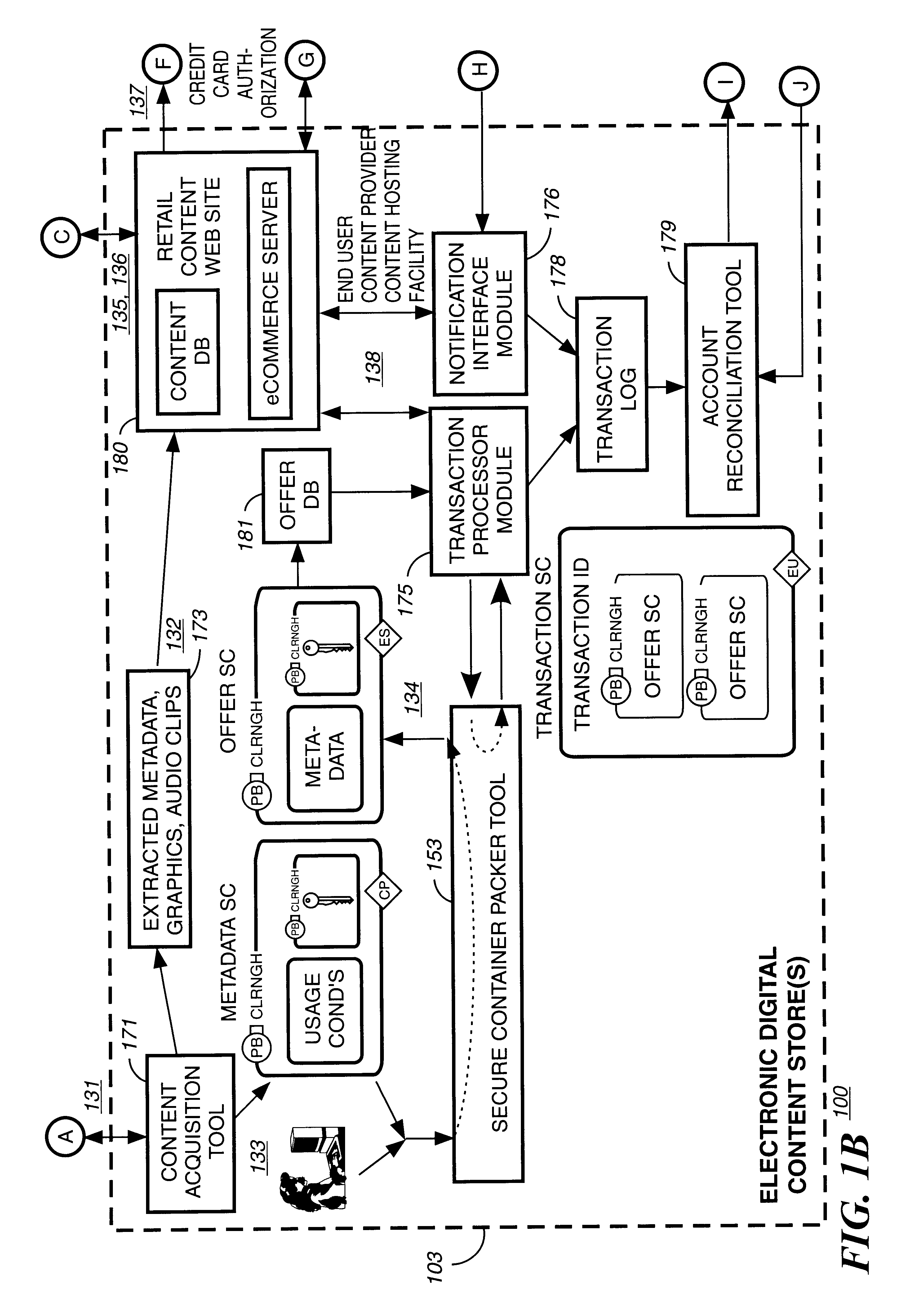
A method to delivery encrypted digital content to a end user system for playing the content comprising the steps of: reading from a computer readable medium metadata which has previously associated with the content. A user selects from the metadata associated content to decrypt and the end user system establishes a secure connection with an authorization authority for decrypting the content. The end user system receives a secure container containing the decrypting key for decrypting at least part of the previously encrypted content as permitted. The system creates a secure container using the encrypting key from a clearing house, wherein the secure container has an encrypting key therein from the end user system; transferring the secure container to the clearing house for authentication of permission to decrypt the content. The system receives from the clearing house, a secure container encrypted using the encrypting key of the end user system containing the decrypting key for decrypting at least part of the previously encrypted content stored on the computer readable medium as permitted; and playing at least part of the previously encrypted content by decrypting the secure container using the encrypting key of the end user system to access the decrypting key for decrypting at least part of the encrypted content.
Owner:WISTRON CORP
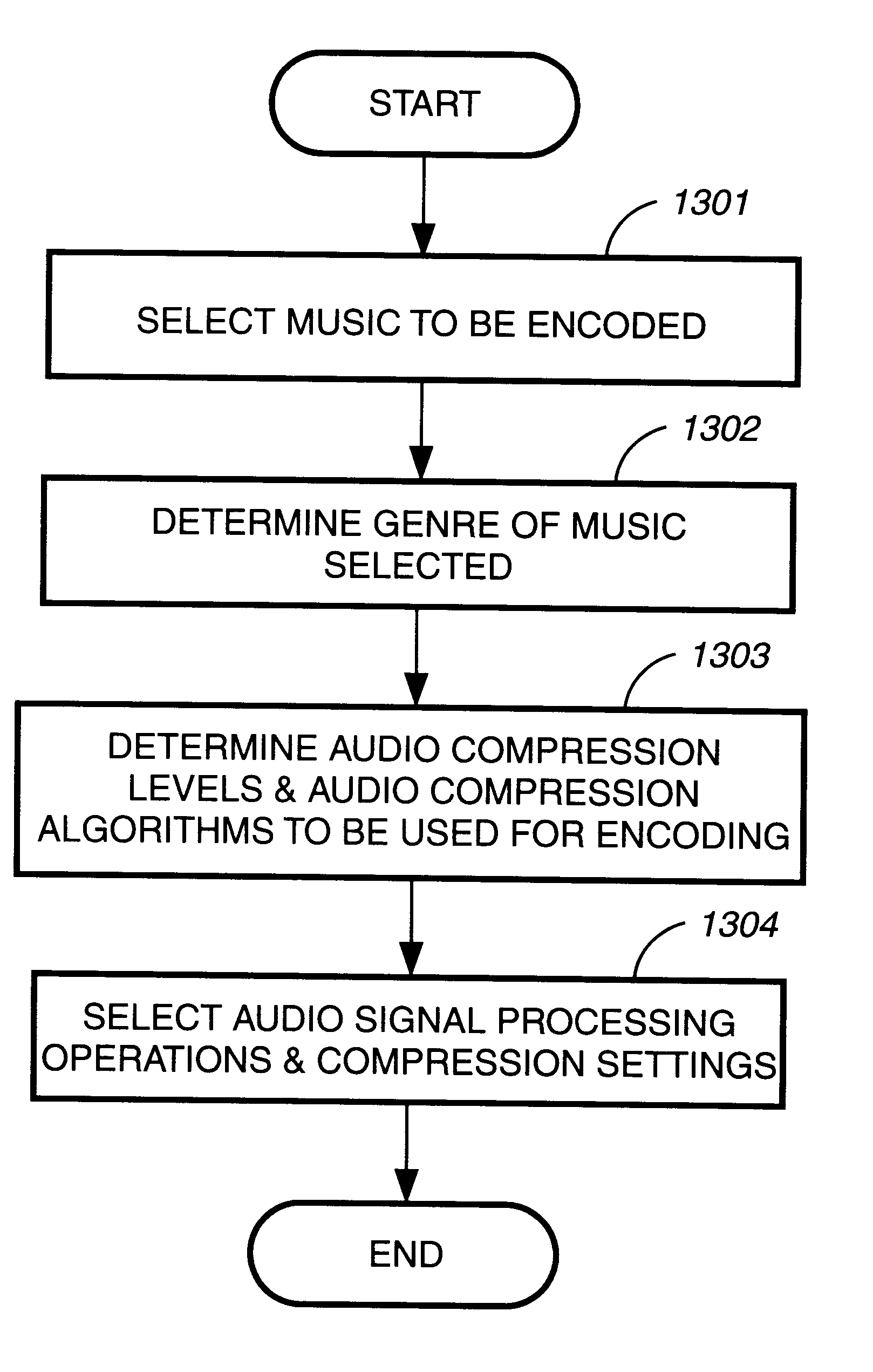
Method and apparatus to create encoded digital content
InactiveUS6263313B1Electrophonic musical instrumentsKey distribution for secure communicationDigital contentNumber content
Owner:LEVEL 3 COMM LLC
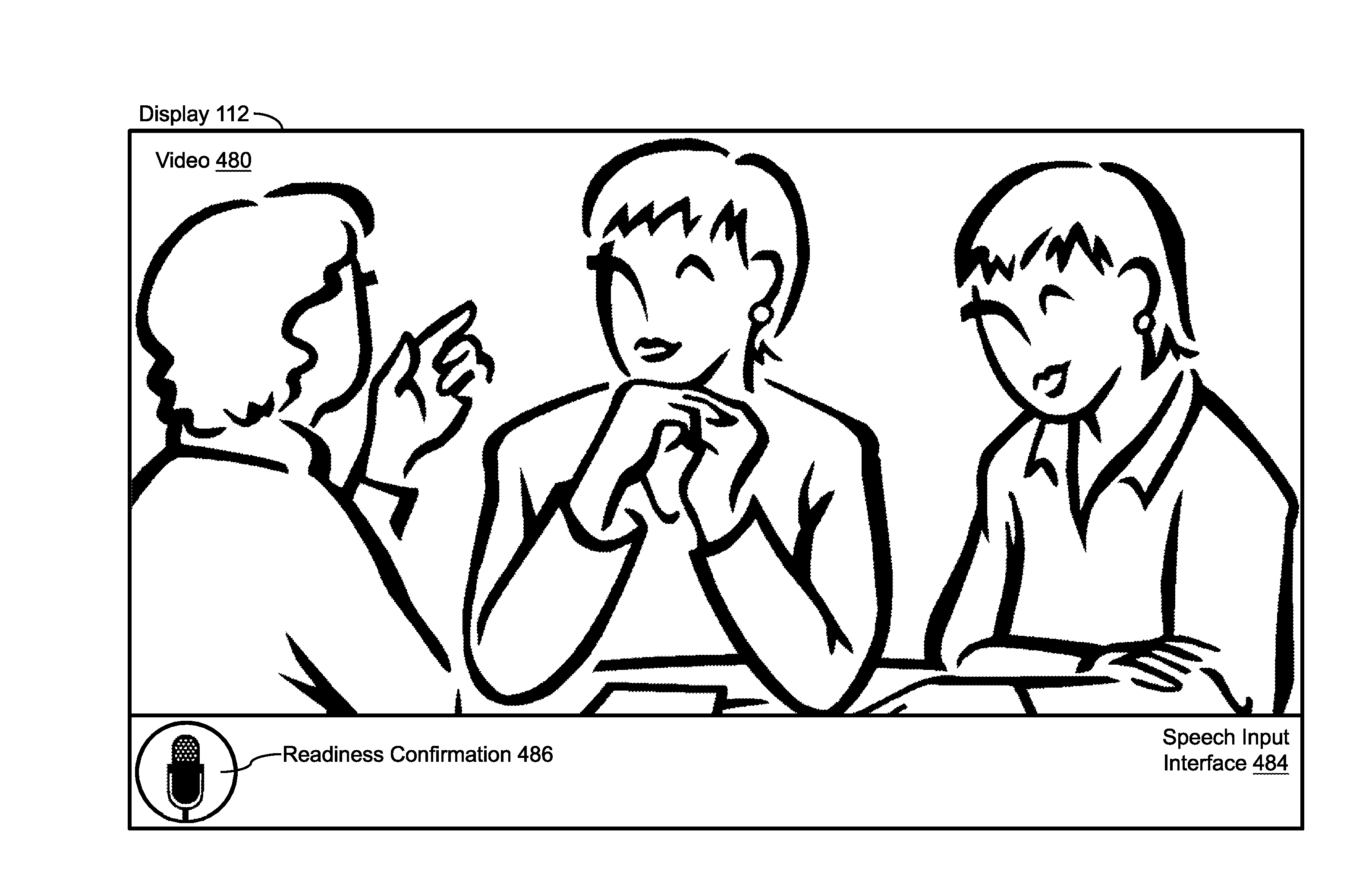
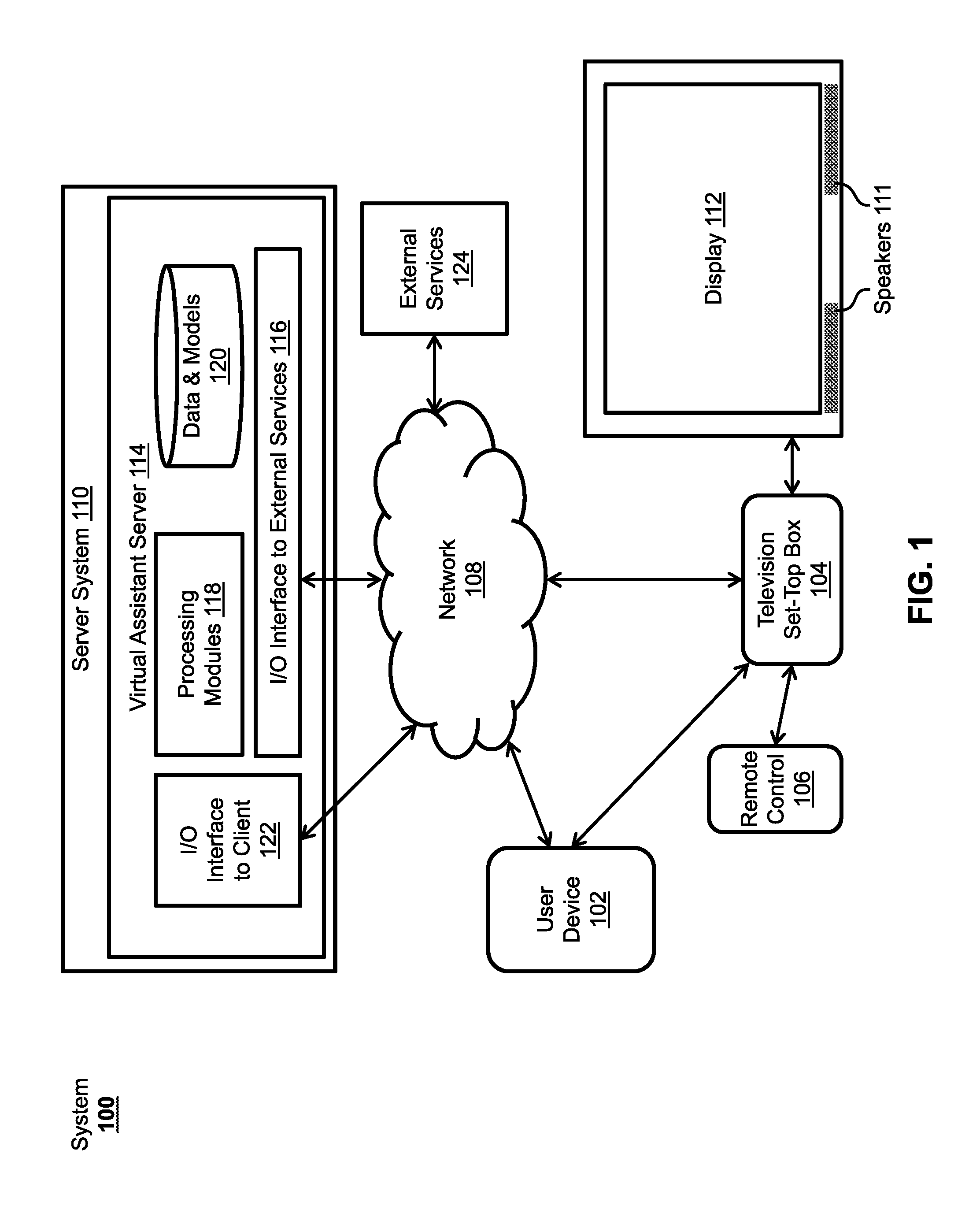
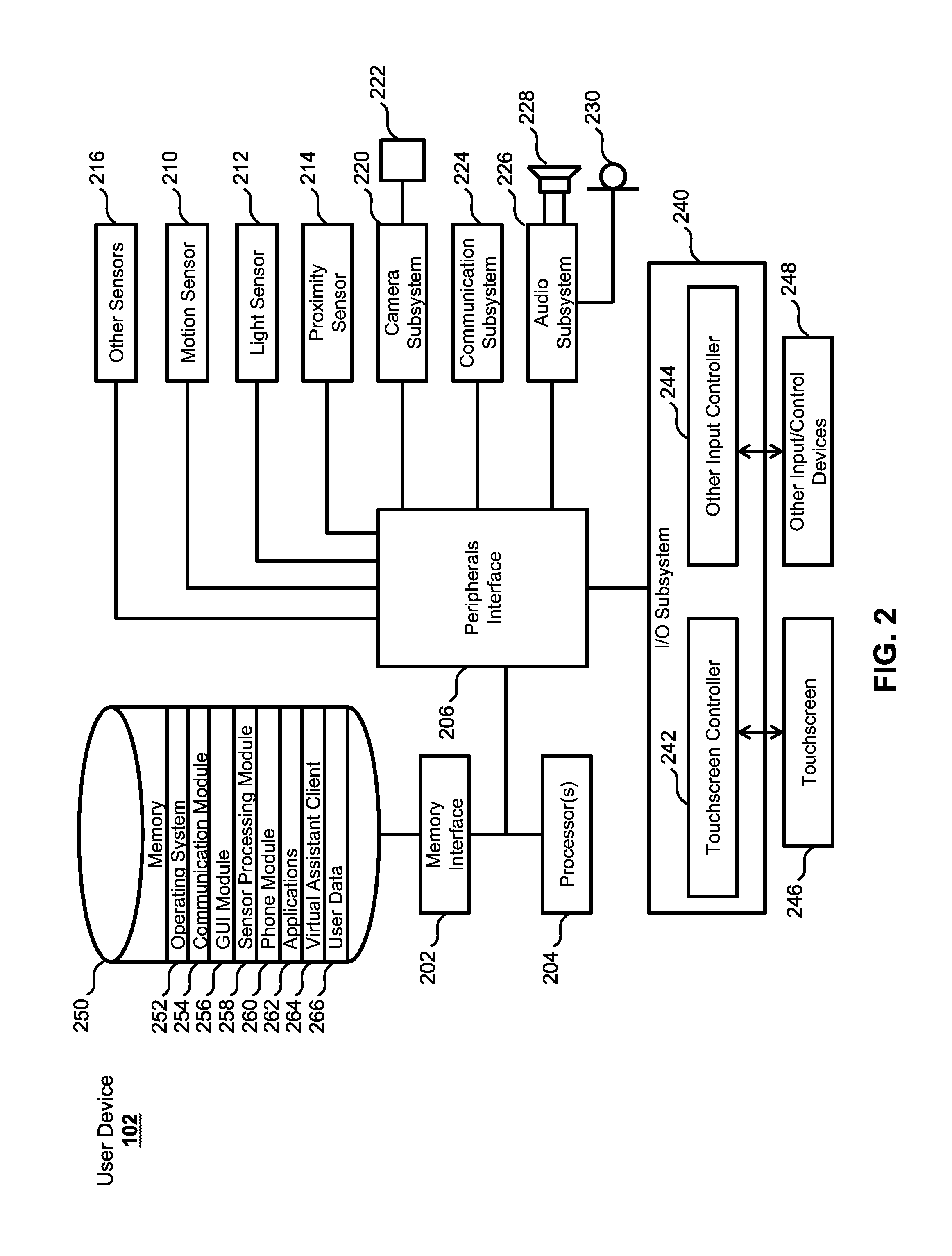
Intelligent automated assistant for TV user interactions
Systems and processes are disclosed for controlling television user interactions using a virtual assistant. A virtual assistant can interact with a television set-top box to control content shown on a television. Speech input for the virtual assistant can be received from a device with a microphone. User intent can be determined from the speech input, and the virtual assistant can execute tasks according to the user's intent, including causing playback of media on the television. Virtual assistant interactions can be shown on the television in interfaces that expand or contract to occupy a minimal amount of space while conveying desired information. Multiple devices associated with multiple displays can be used to determine user intent from speech input as well as to convey information to users. In some examples, virtual assistant query suggestions can be provided to the user based on media content shown on a display.
Owner:APPLE INC
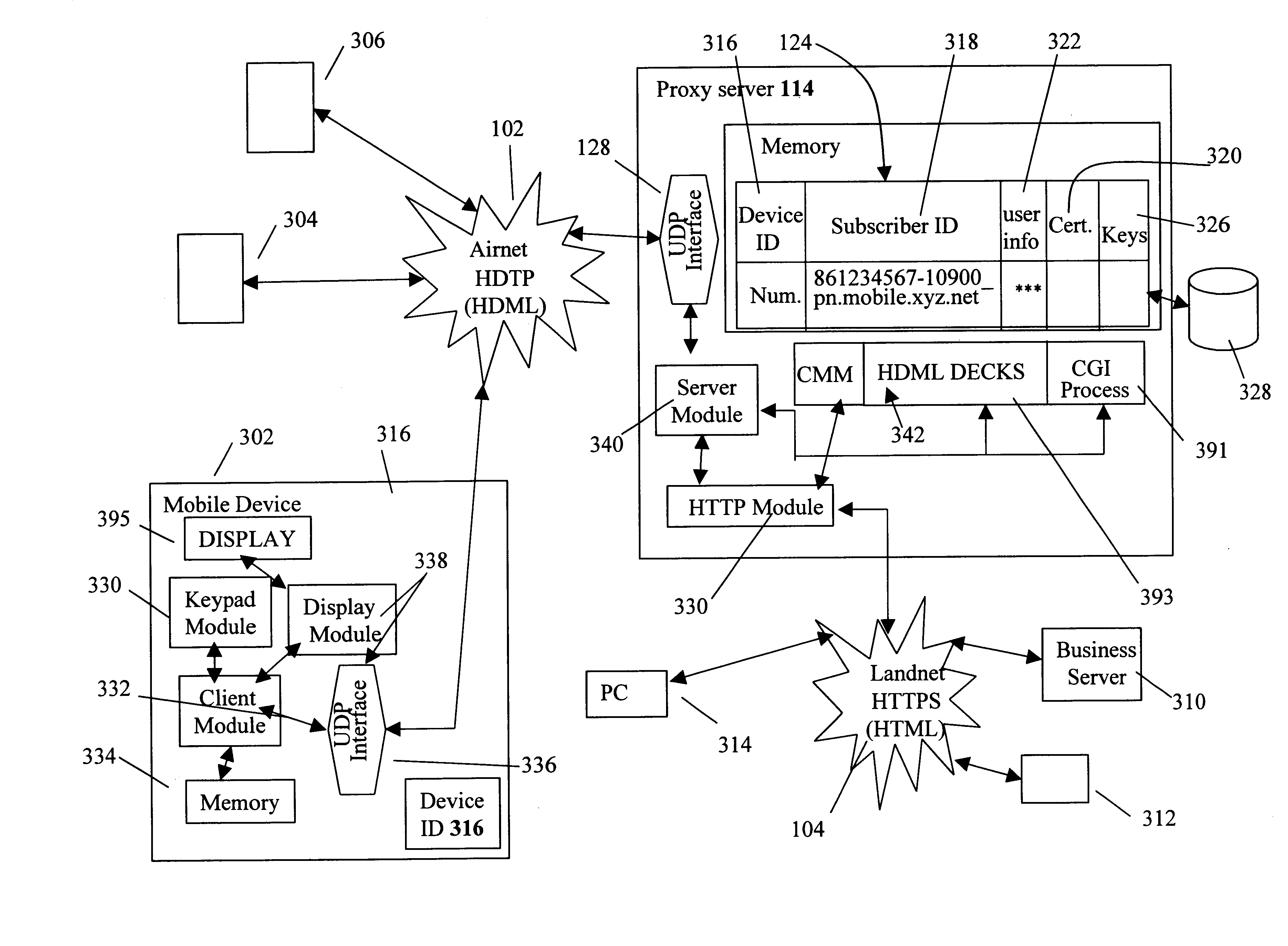
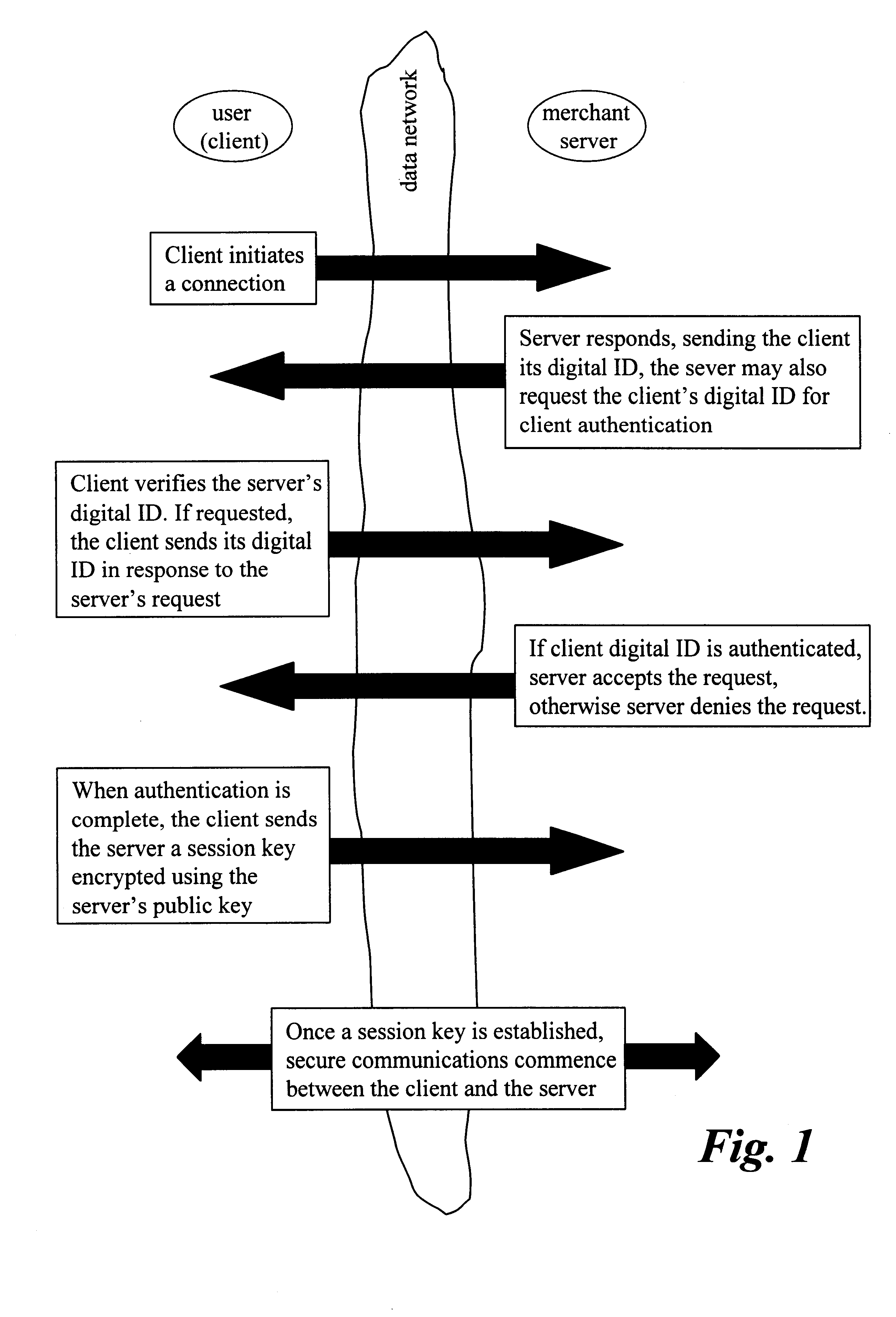
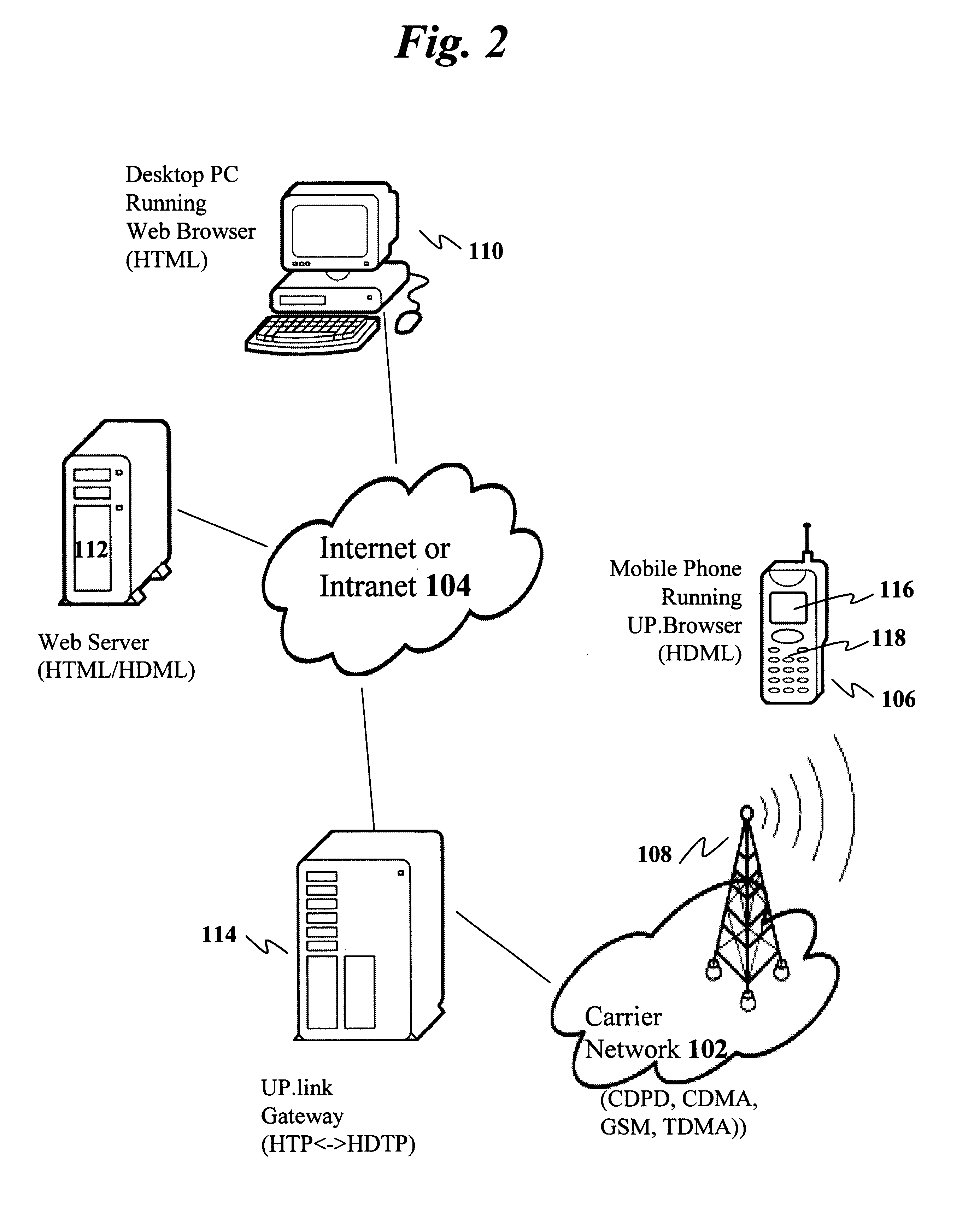
Centralized certificate management system for two-way interactive communication devices in data networks
InactiveUS6233577B1Key distribution for secure communicationData processing applicationsServer applianceCommunication device
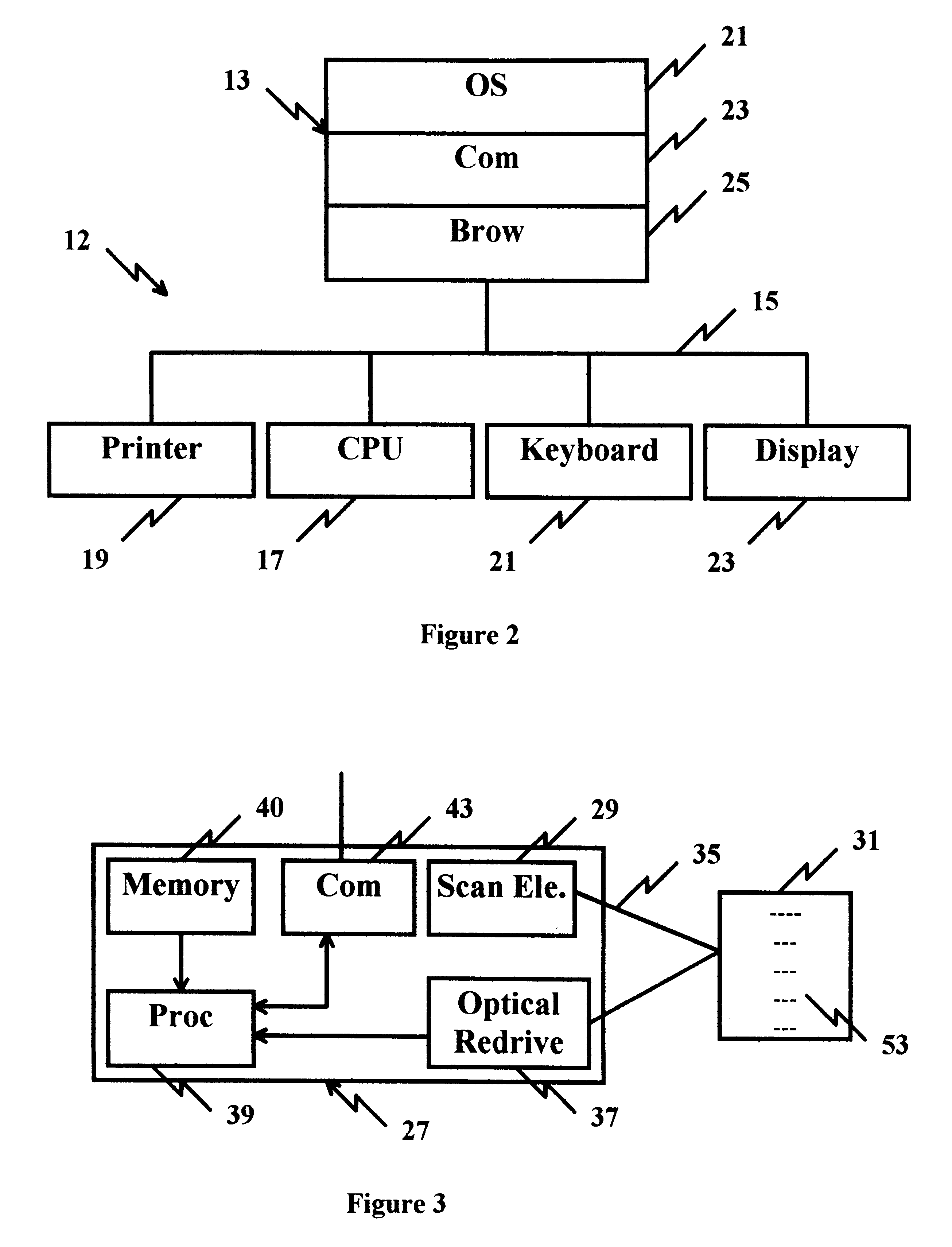
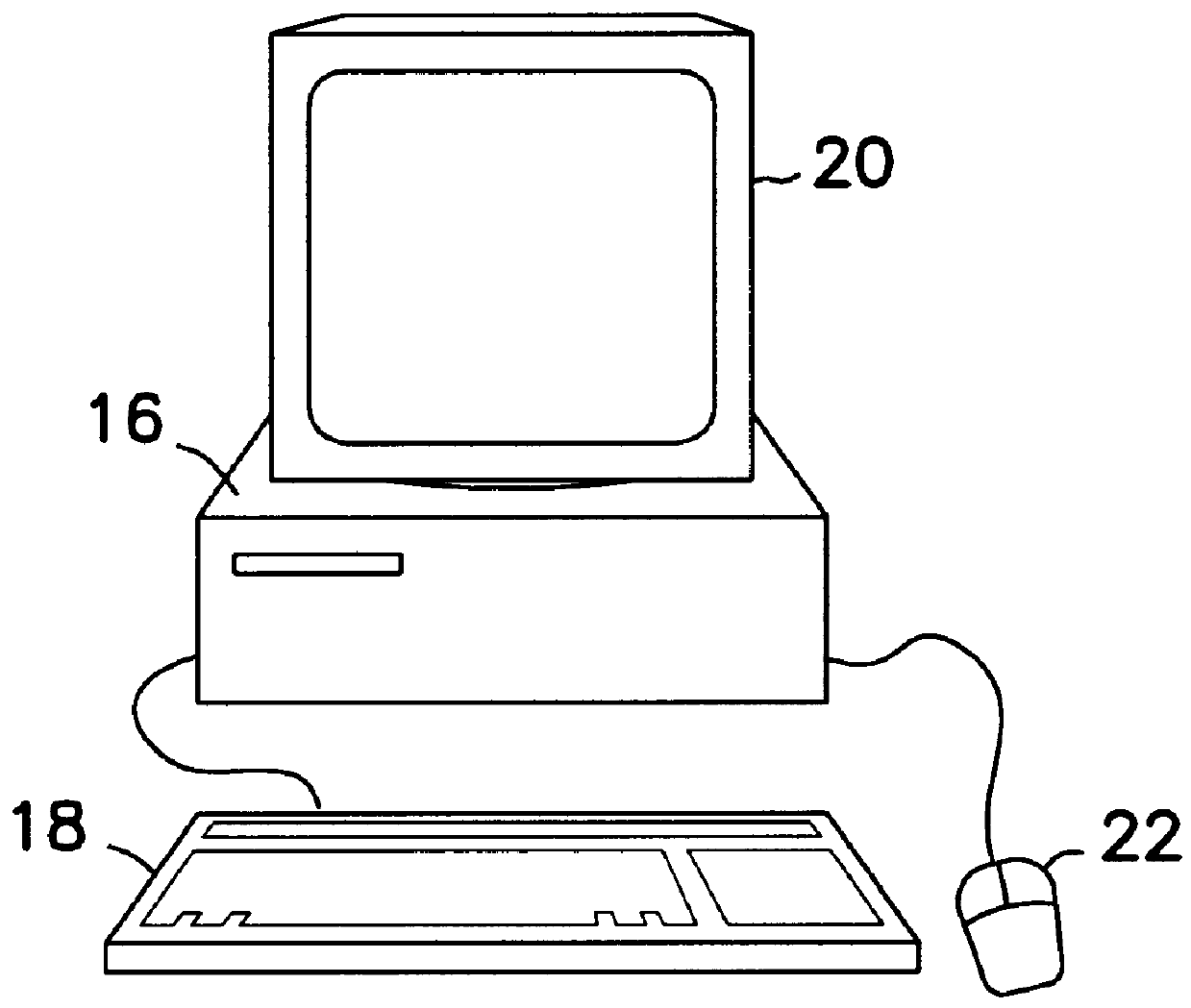
The present invention discloses a central certificate management system for thin client devices in data networks and has particular applications to systems having a large number of the thin clients serviced by a proxy server through which the thin clients communicate with a plurality of secure server computers over a data network. According to one aspect, the present invention provides a certificate management module that causes the server device to manage digital certificates for each of the thin client devices. To minimize the latency of obtaining certificates for each of the thin client devices, the certificate management module reserves a fixed number of free certificates signed by a certificate authority and their respective private keys in a certificate database and frequently updates the free certificate according to a certificate updating message. Whenever a user account is created for a thin client device, the certificate management module fetches one or more free certificates from the certificate database and associate the fetched certificates to the created account and meanwhile the certificate management module creates new free certificates with the certificate authority to fill in the certificate database. Apart from the tradition of obtaining certificates locally in client devices that normally have sufficient computing power, the present invention uses the computing resources in a server device to carry out the task of obtaining and maintaining certificates asynchronously in the proxy server and further. These and other features in the present invention dramatically minimize the demands for computing power and memory in thin client devices like mobile devices, cellular phones, landline telephones or Internet appliance controllers.
Owner:UNWIRED PLANET
Method and apparatus for uniquely identifying a customer purchase in an electronic distribution system
InactiveUS6389403B1Key distribution for secure communicationDigital data processing detailsContent IdentifierUser device
A system for tracking usage of digital content on user devices. Content sites for distributing digital content over a computer readable medium to users. The content sites associate unique content identifier with the content associated. Electronic stores coupled to a network sell licenses to play digital content data to users. The licenses contain a unique transaction identifier for uniquely identifying the transaction, and the licenses contain a unique item identifier for uniquely identifying at least one item in the transaction. Content players, which receive from the network the licensed content data, are used to play the licensed content data. The content players produce a purchase identifier based upon the mathematical combination of the content identifier, the transaction identifier and the item identifier.
Owner:WISTRON CORP
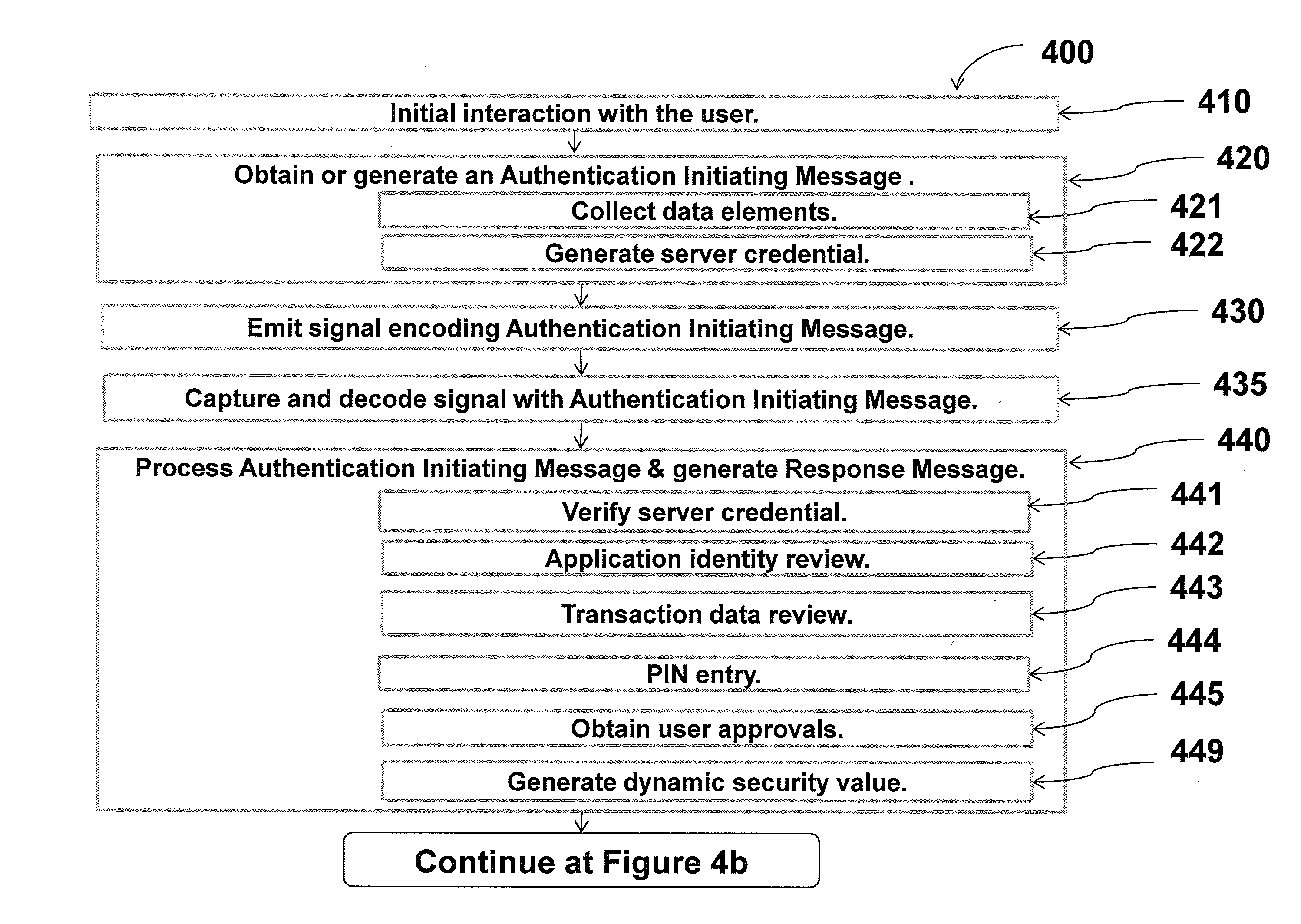
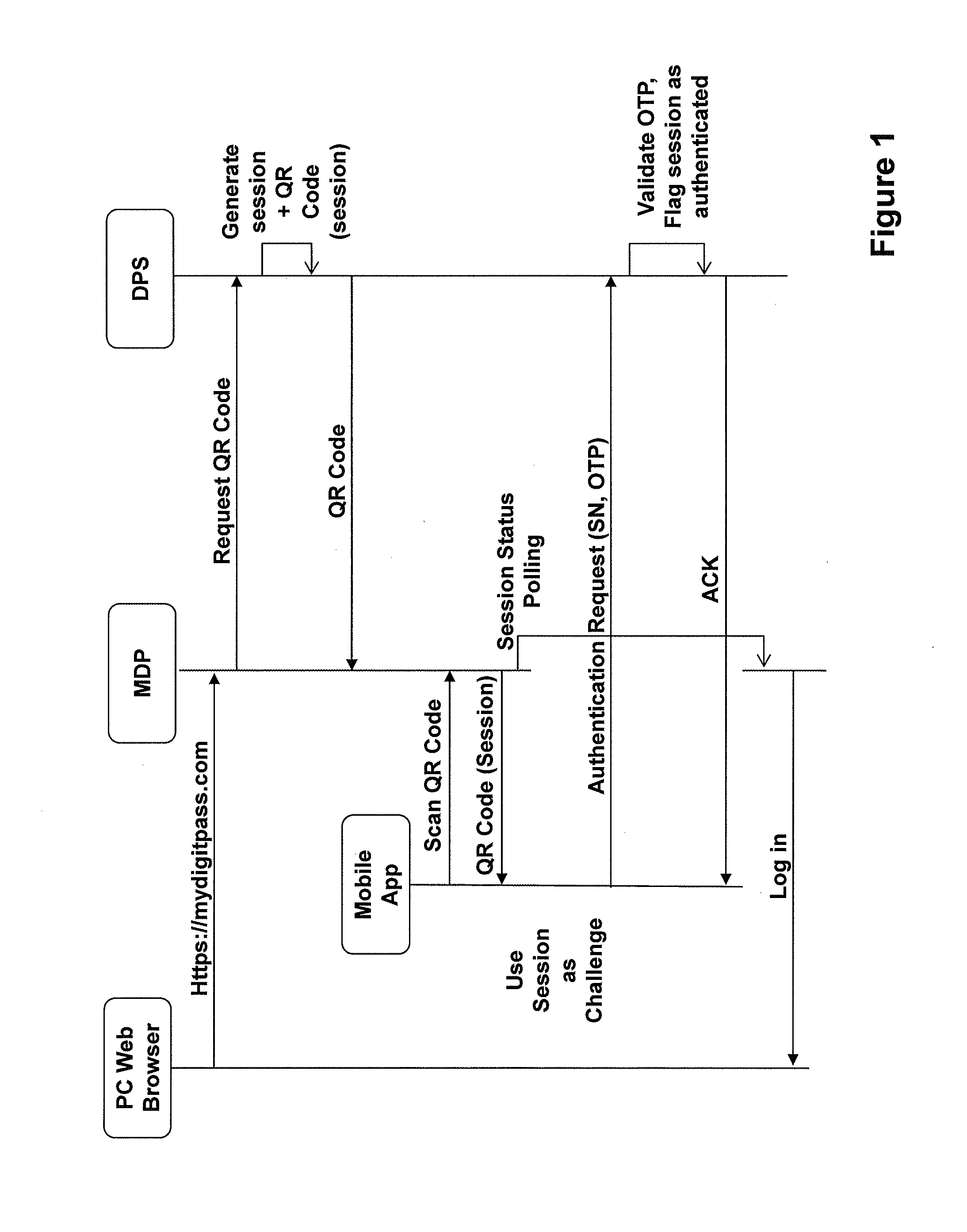
User-convenient authentication method and apparatus using a mobile authentication application
ActiveUS20140040628A1Authentication process can be made convenientCost-effectiveDigital data authenticationCoding/ciphering apparatusUser authenticationApplication software
Methods, apparatus, and systems for securing application interactions are disclosed. Application interactions may be secured by, at a user authentication device, capturing a signal emitted by an access device encoded with an authentication initiating message including an application identifier, decoding the signal and obtaining the authentication initiating message, retrieving the application identifier, presenting a human interpretable representation of the application identity to the user, obtaining user approval to generate a response message available to a verification server, generating a dynamic security value using a cryptographic algorithm that is cryptographically linked to the application identity, and generating a response message including the generated dynamic security value; making the response message available to a verification server; and, at the verification server, receiving the response message, verifying the response message including verifying the validity of the dynamic security value, and communicating the result of the verification of the response message to the application.
Owner:ONESPAN NORTH AMERICA INC
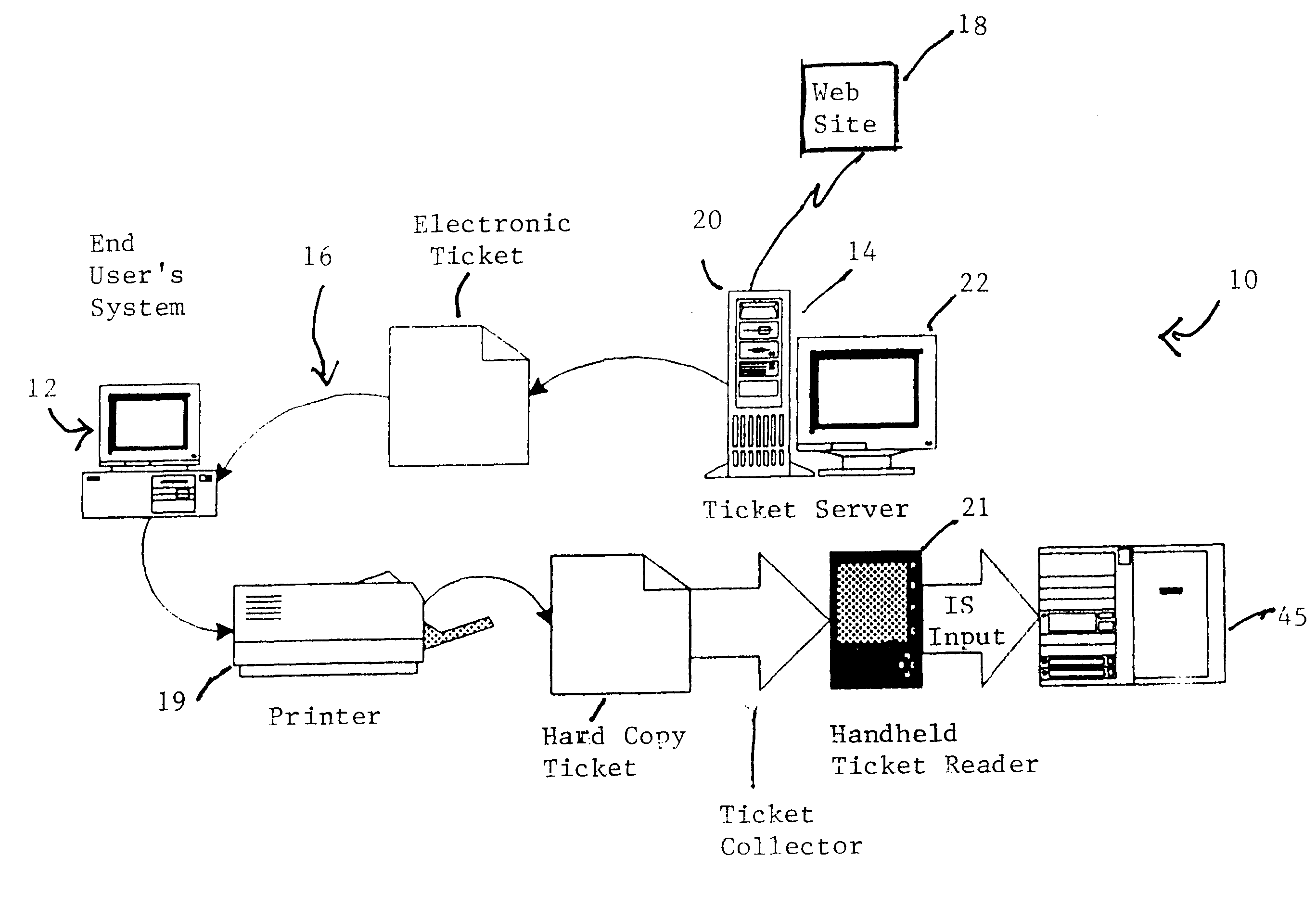
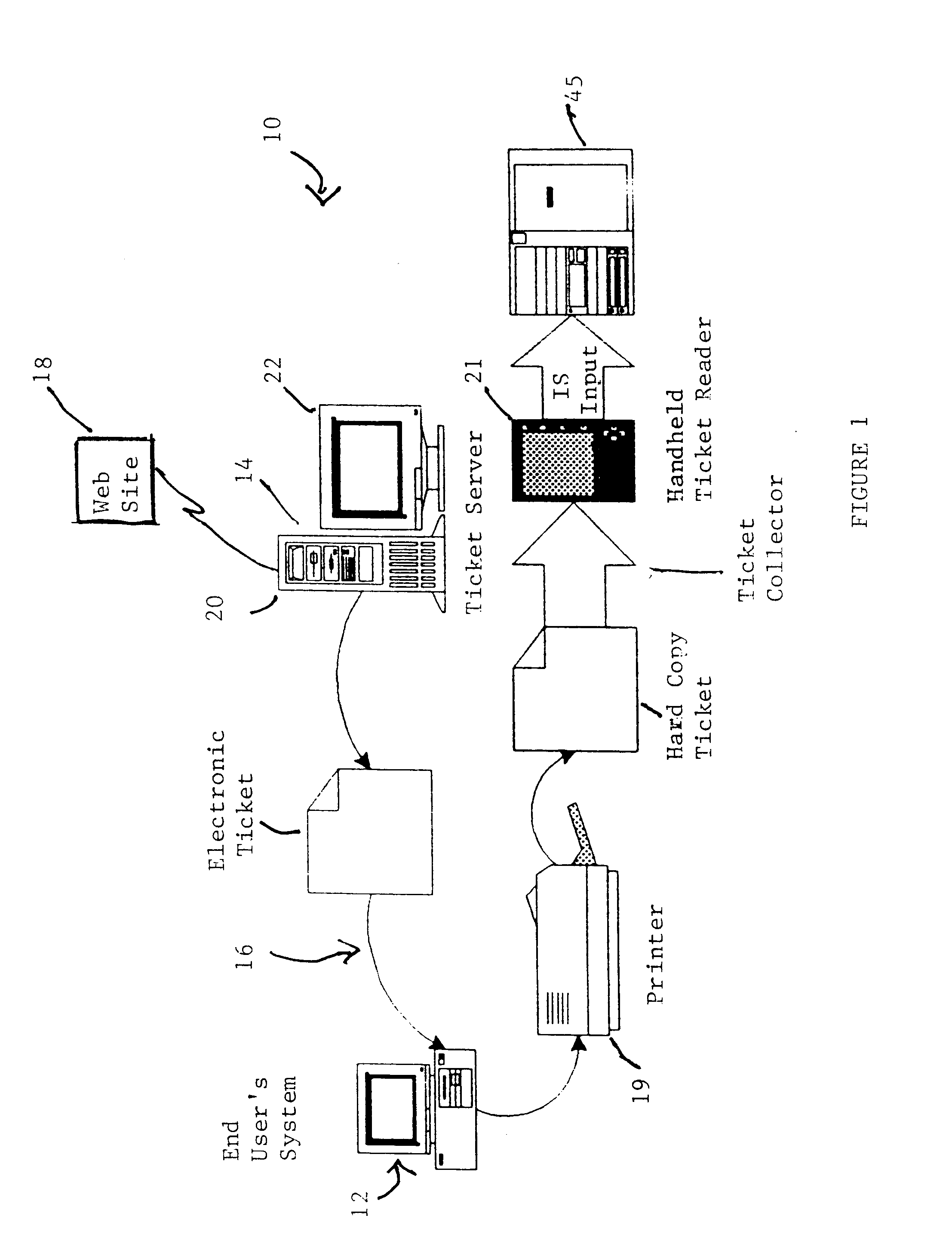
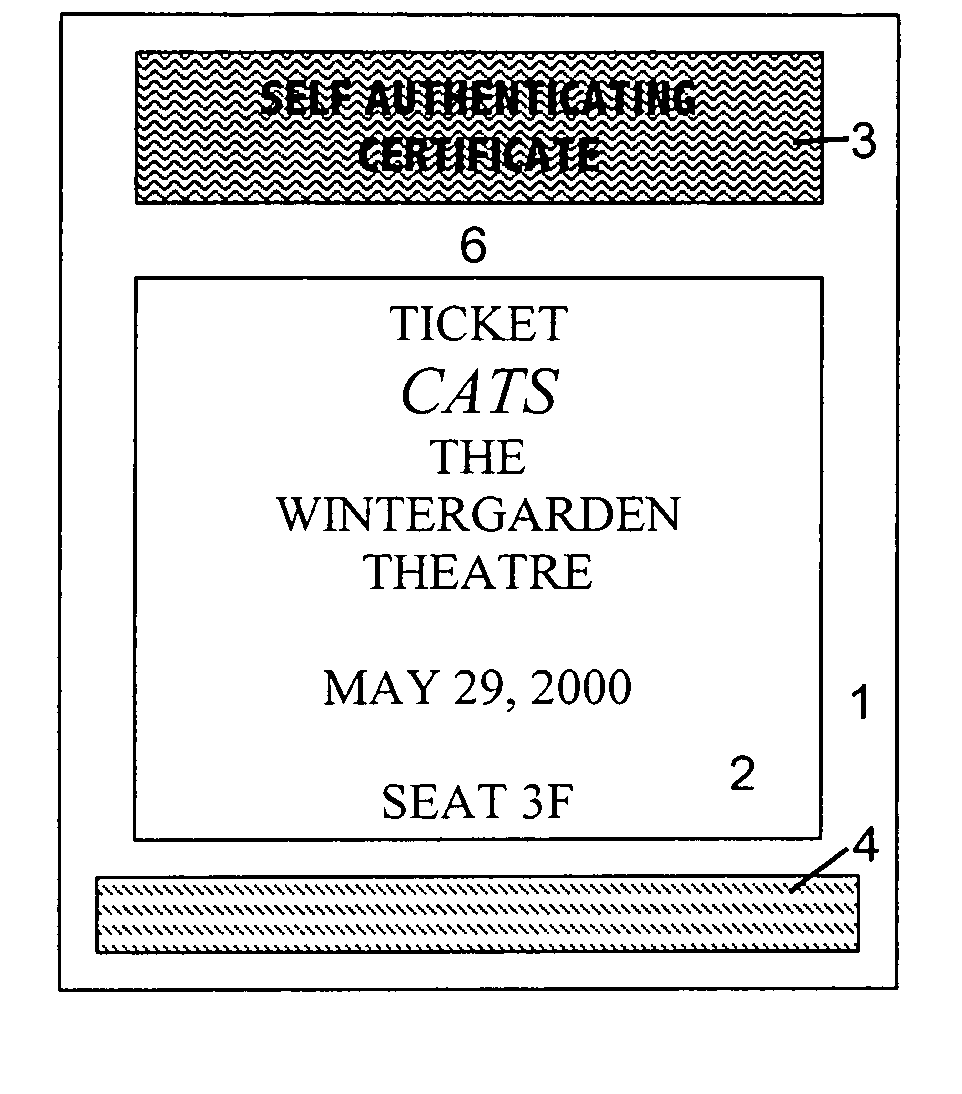
Cryptographic encoded ticket issuing and collection system for remote purchasers
InactiveUS6223166B1Prevent ticket fraudTicket-issuing apparatusElectrical apparatusCollection systemInformation networks
A cryptographic encoded, ticket issuing and collection system for real-time purchase of tickets by purchasers at remote user stations in an information network that includes a plurality of remote user stations coupled to a server in an information network, e.g., the Internet, for purchase of services, products, or tickets to an event. An operator of the remote user station selects a ticket for purchase to an event using standard protocols of information network. An electronic ticket is transmitted to the operator and includes a cypher code created using a public key cryptography system. The operator displays the electronic ticket for verification purposes and proceeds to print out the ticket at the station. The ticket is presented to a ticket collector whereupon the ticket is scanned by a portable terminal for decoding the cypher code using a public key reloaded into the terminal by the producers of the event. The decoded cypher code is compared against the event description stored in the portable terminal and if equal, the ticket is accepted for admission to the event. The ticket information is stored in the portable terminal and subsequently uploaded to the information system to check for duplicate tickets.
Owner:IBM CORP
Method and apparatus for embedding data, including watermarks, in human perceptible images
InactiveUS6031914AGood autocorrelationPromote generationElectric signal transmission systemsCharacter and pattern recognitionPattern recognitionFrequency spectrum
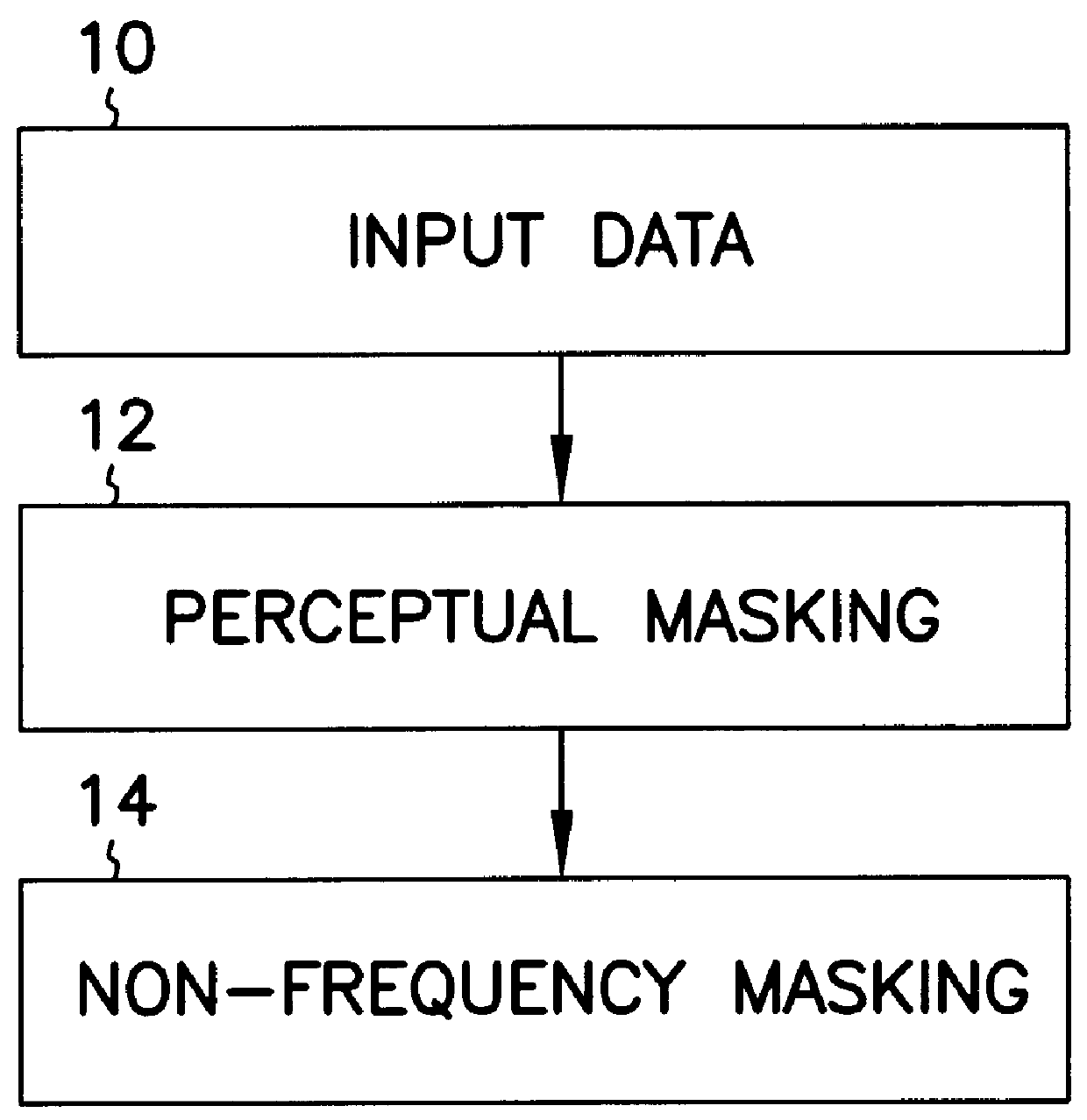
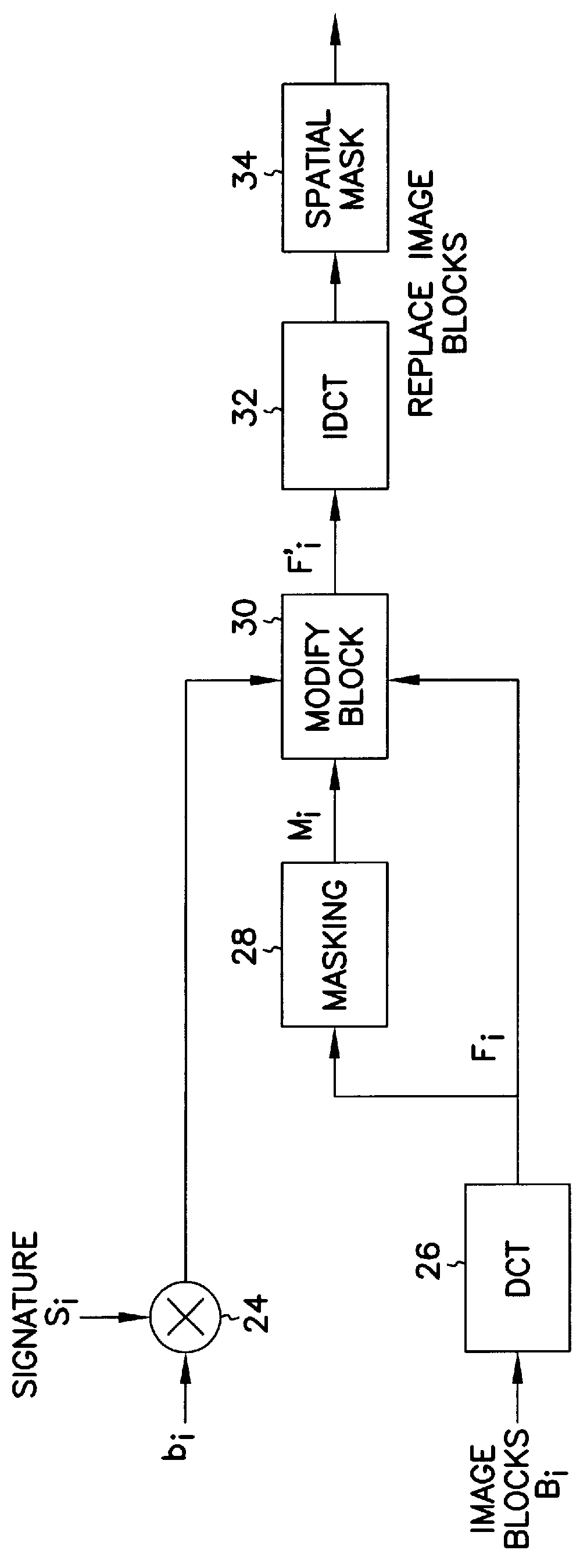
A technique for hiding of data, including watermarks, in human-perceptible images, that is, image host data, is disclosed. In one embodiment a method comprises three steps. In the first step, data to be embedded is inputted. In the case of a watermark, this data is a unique signature, and may be a pseudo-noise (PN) code. In the case of hidden data to be embedded in the host data, this data is the hidden data itself, or the hidden data as spread against the frequency spectrum by a pseudo-noise (PN) code. In the second step, the inputted data is embedded within the host data, in accordance with a perceptual mask of the host data. The perceptual mask determines the optimal locations within the host data to insert the inputted data. In the case of images, these optimal locations are determined by reference to the human visual system. In the third step, the host data, with the embedded data, is further masked by a non-frequency mask. In the case of image data, the non-frequency mask is a spatial mask.
Owner:MINNESOTA RGT UNIV OF A CORP OF MN
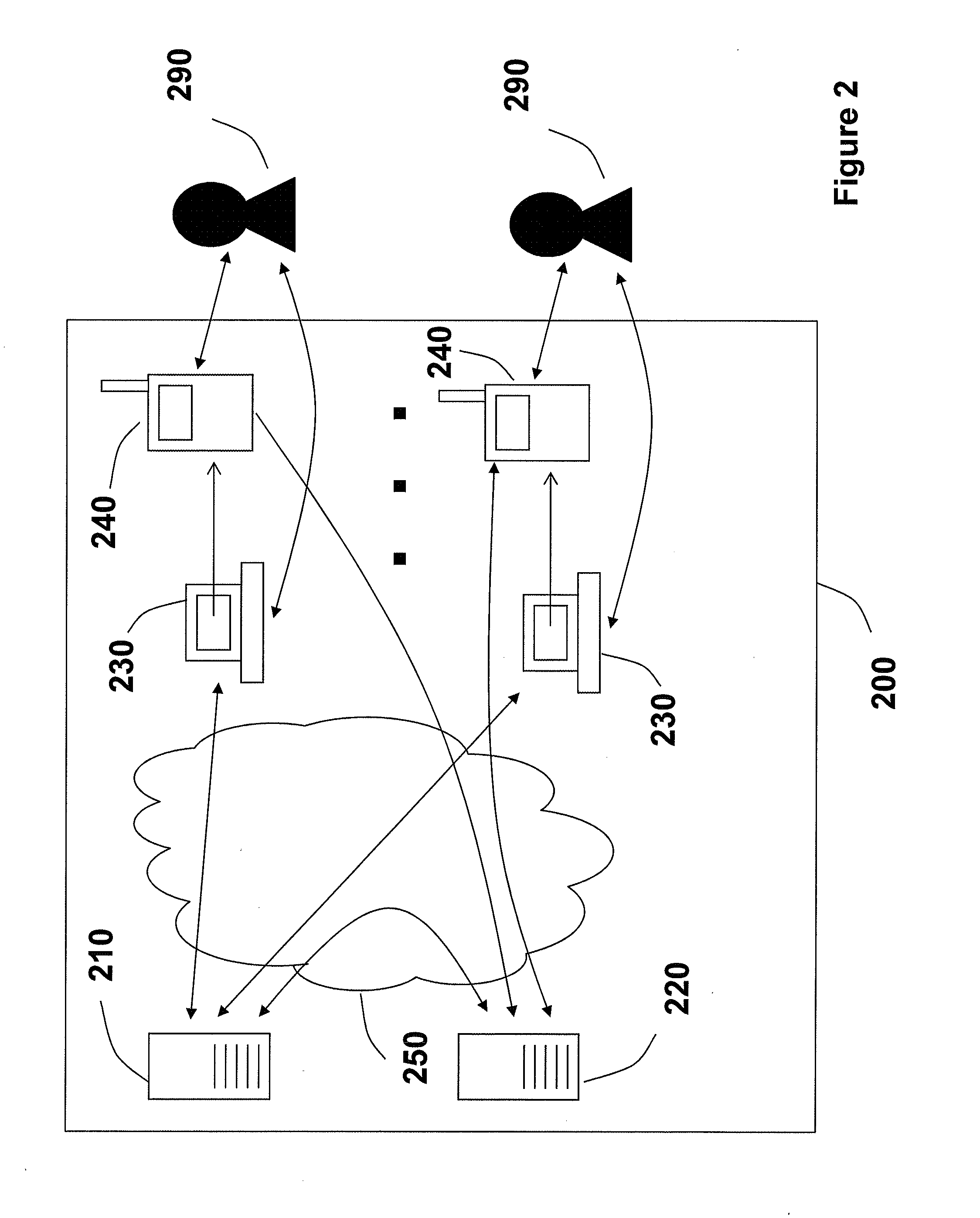
Method and system of program transmission optimization using a redundant transmission sequence
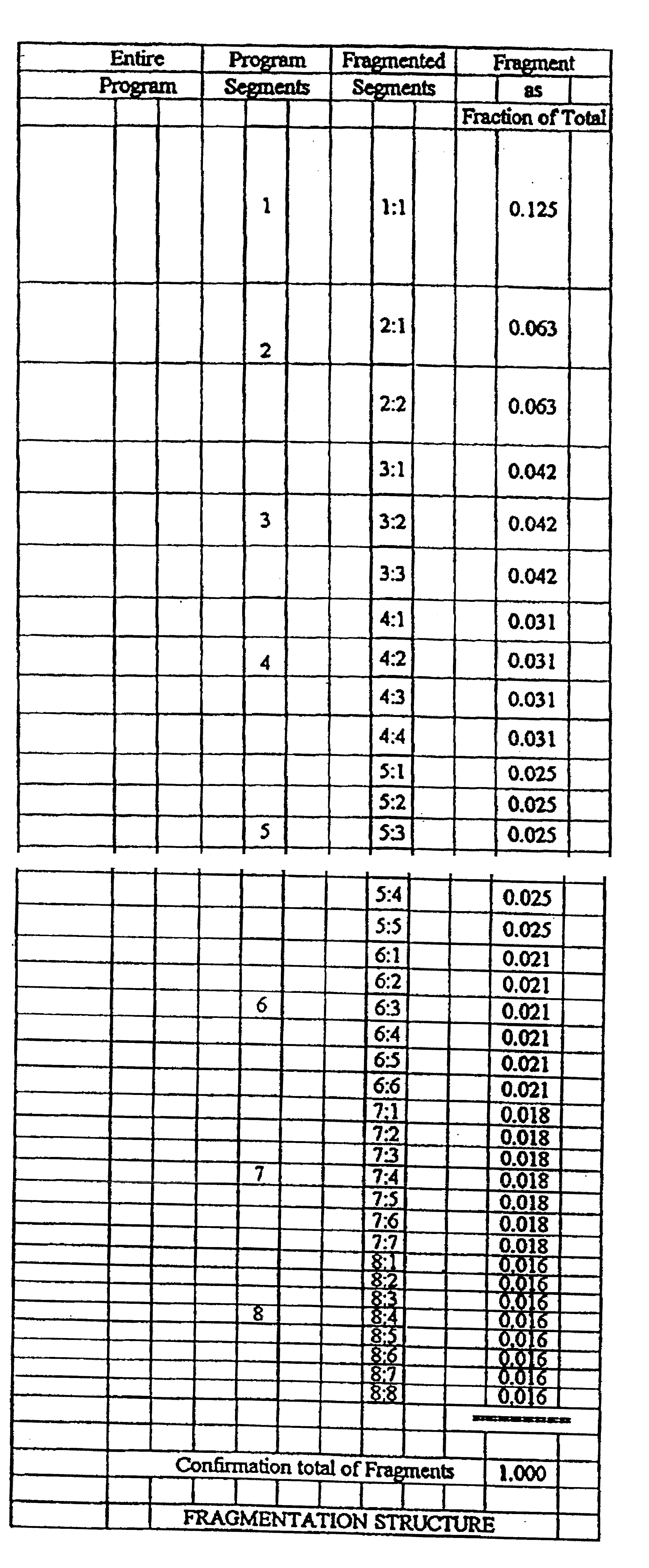
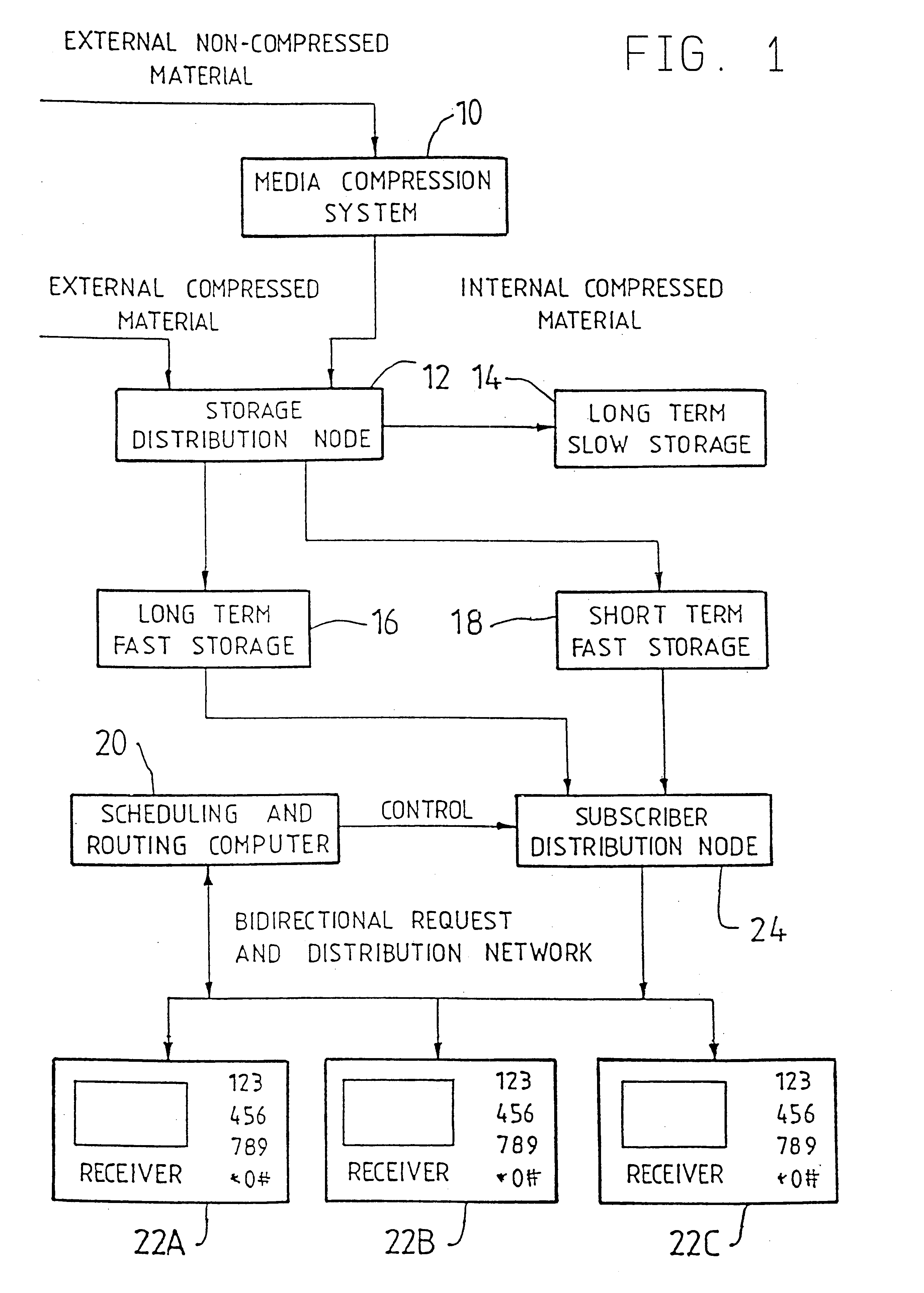
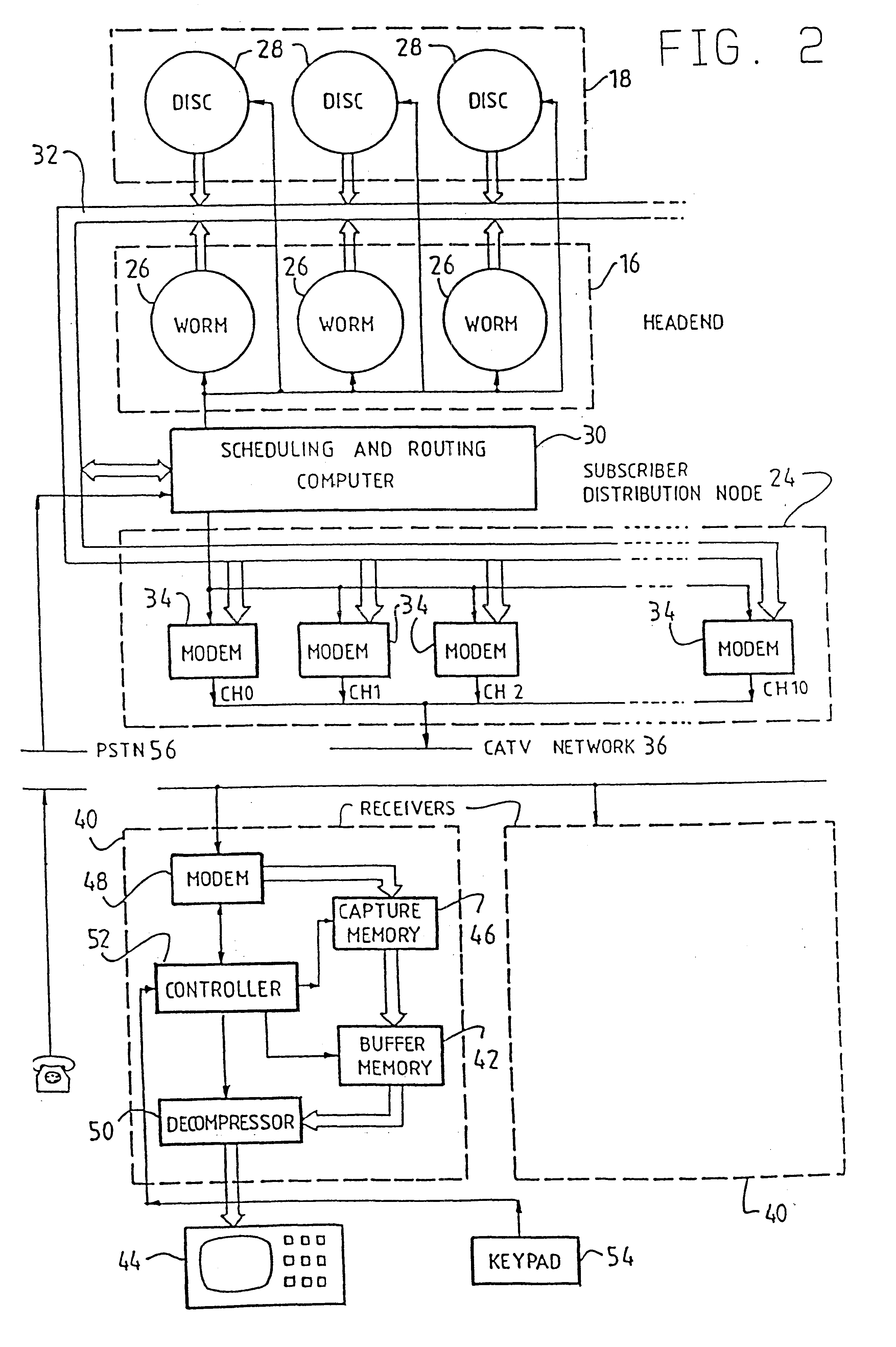
A system and method of optimizing transmission of a program to multiple users over a distribution system, with particular application to video-on-demand for a CATV network. The system includes, at a head end of the CATV network a scheduling and routing computer for dividing the video program stored in long term fast storage or short term fast storage into a plurality of program segments, and a subscriber distribution node for transmitting the program segments in a redundant sequence in accordance with a scheduling algorithm. At a receiver of the CATV network there is provided a buffer memory for storing the transmitted video program segments for subsequent playback whereby, in use, the scheduling algorithm can ensure that a user's receiver will receive all of the program segments in a manner that will enable continuous playback in real time of the program. Under the control of controller the receiver distinguishes received program segments by a segment identifier so that redundant segments captured in capture memory are then stored in buffer memory from which the segments can be retrieved and decompressed in data compressor for immediate or subsequent viewing. In one embodiment, the method of this invention includes dividing at least some segments into fragments, and transmitting one fragment of each segment during a playback interval of a duration, for example, equal to a playback time of a segment.
Owner:DETA TECH DEV
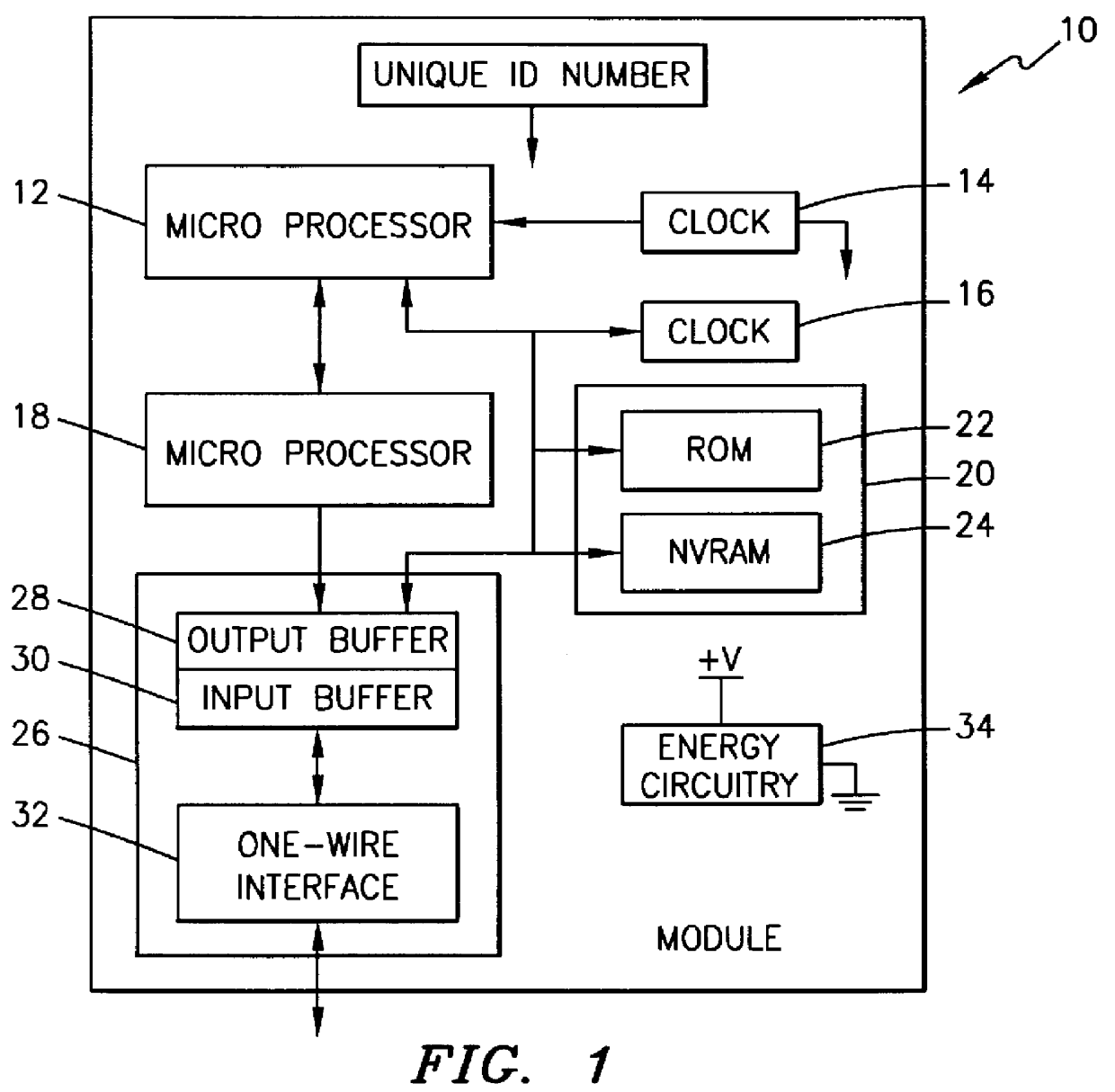
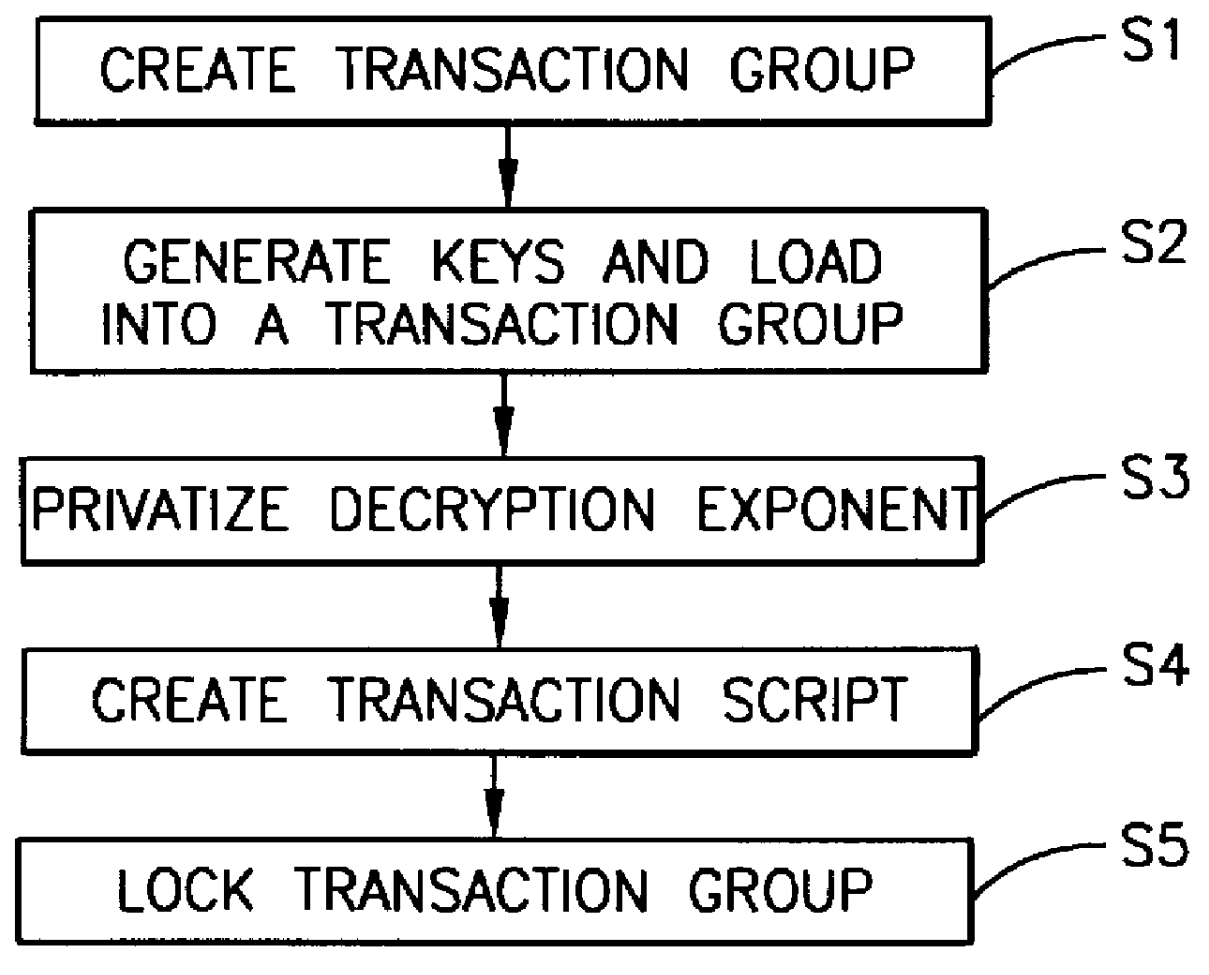
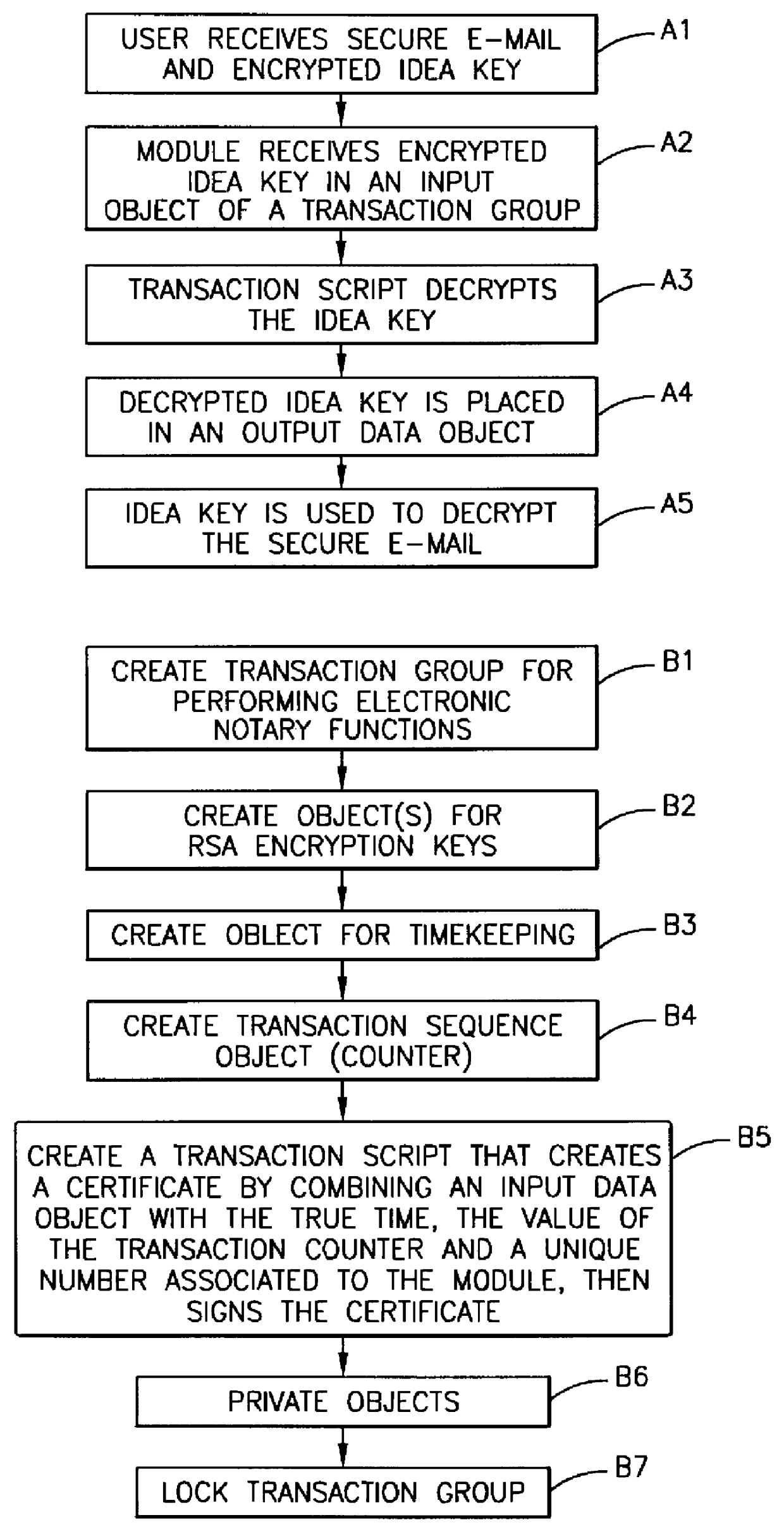
Method, apparatus, system and firmware for secure transactions
The present invention relates to an electronic module used for secure transactions. More specifically, the electronic module is capable of passing information back and forth between a service provider's equipment via a secure, encrypted technique so that money and other valuable data can be securely passed electronically. The module is capable of being programmed, keeping track of real time, recording transactions for later review, and creating encryption key pairs.
Owner:MAXIM INTEGRATED PROD INC
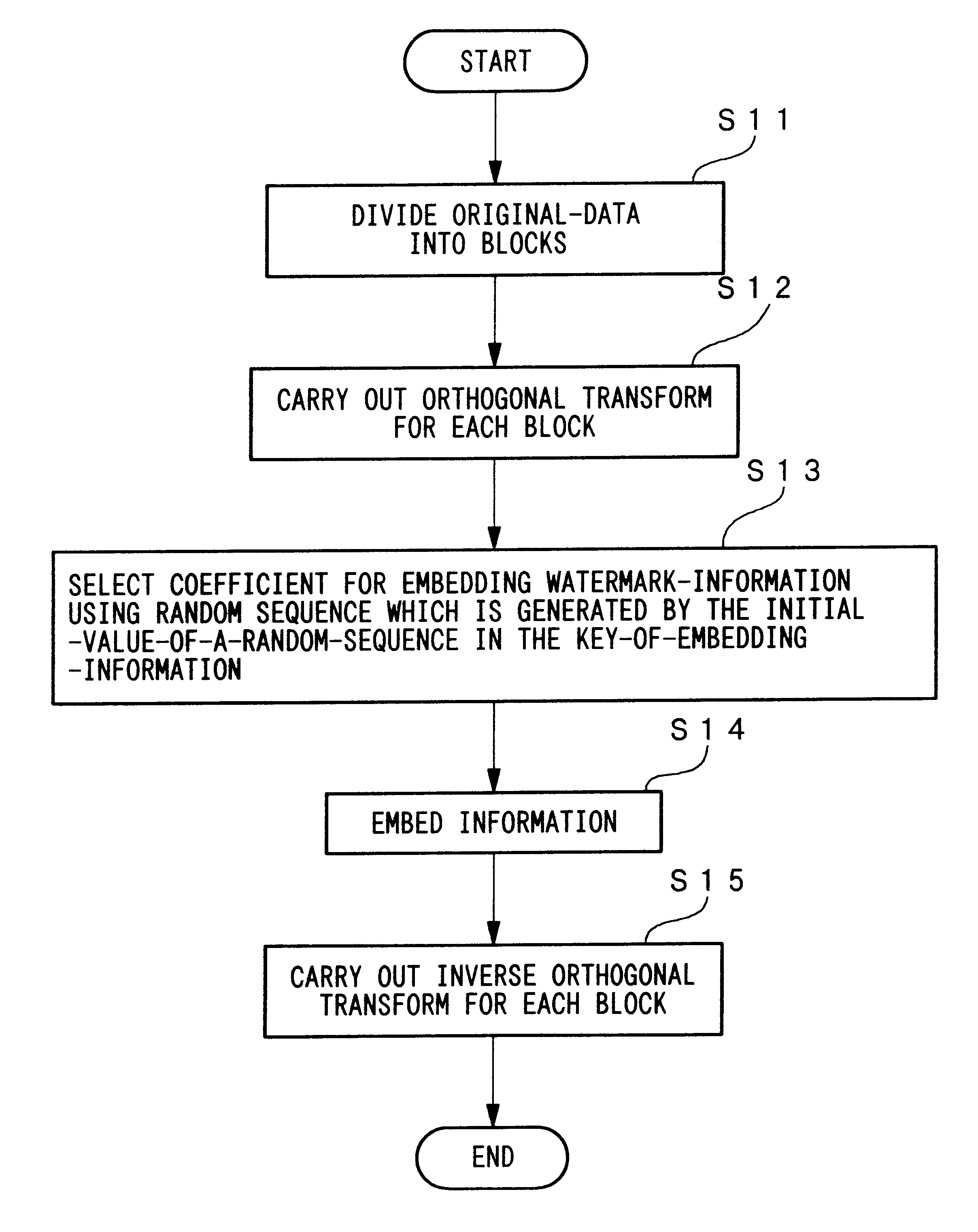
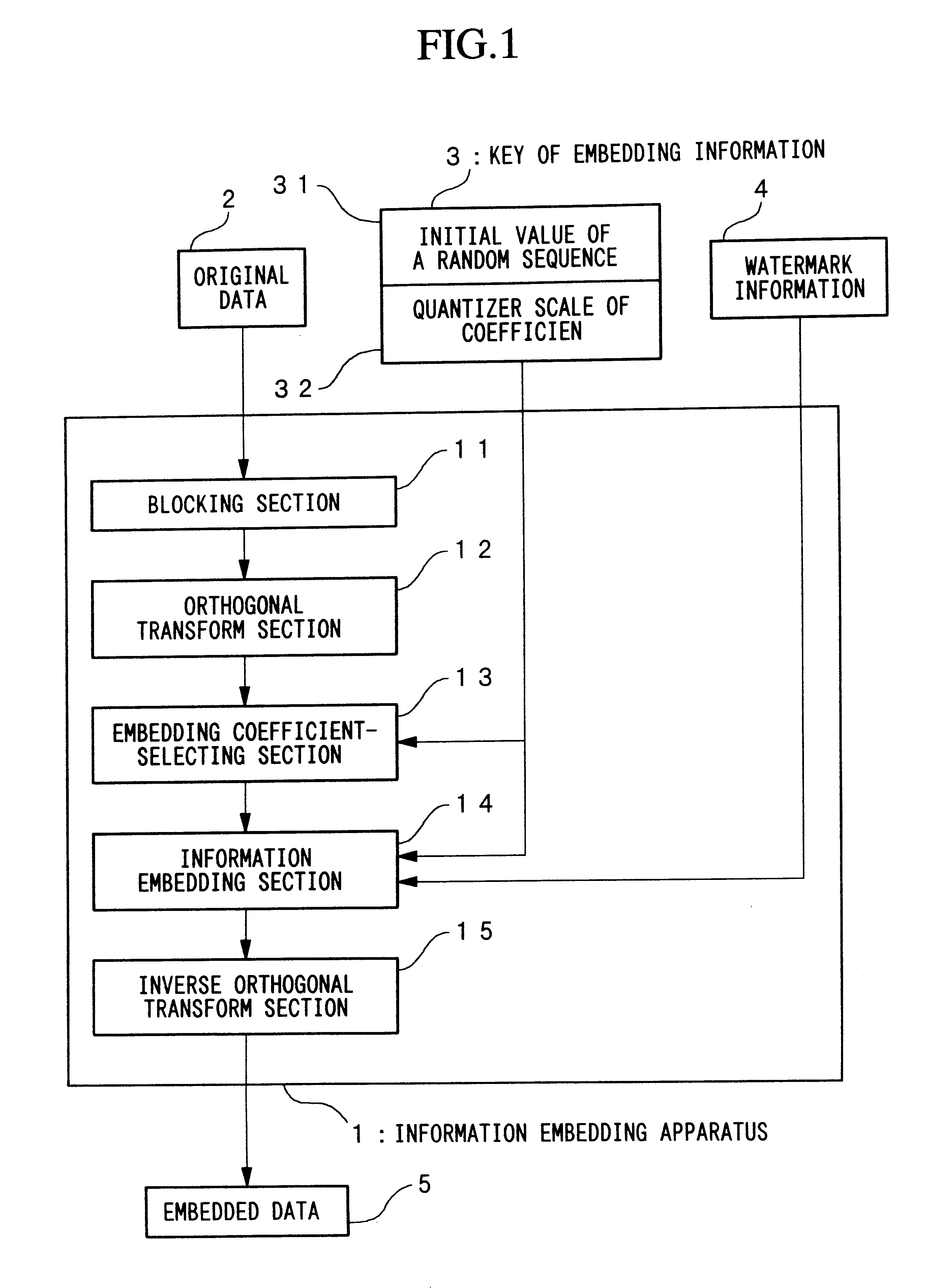
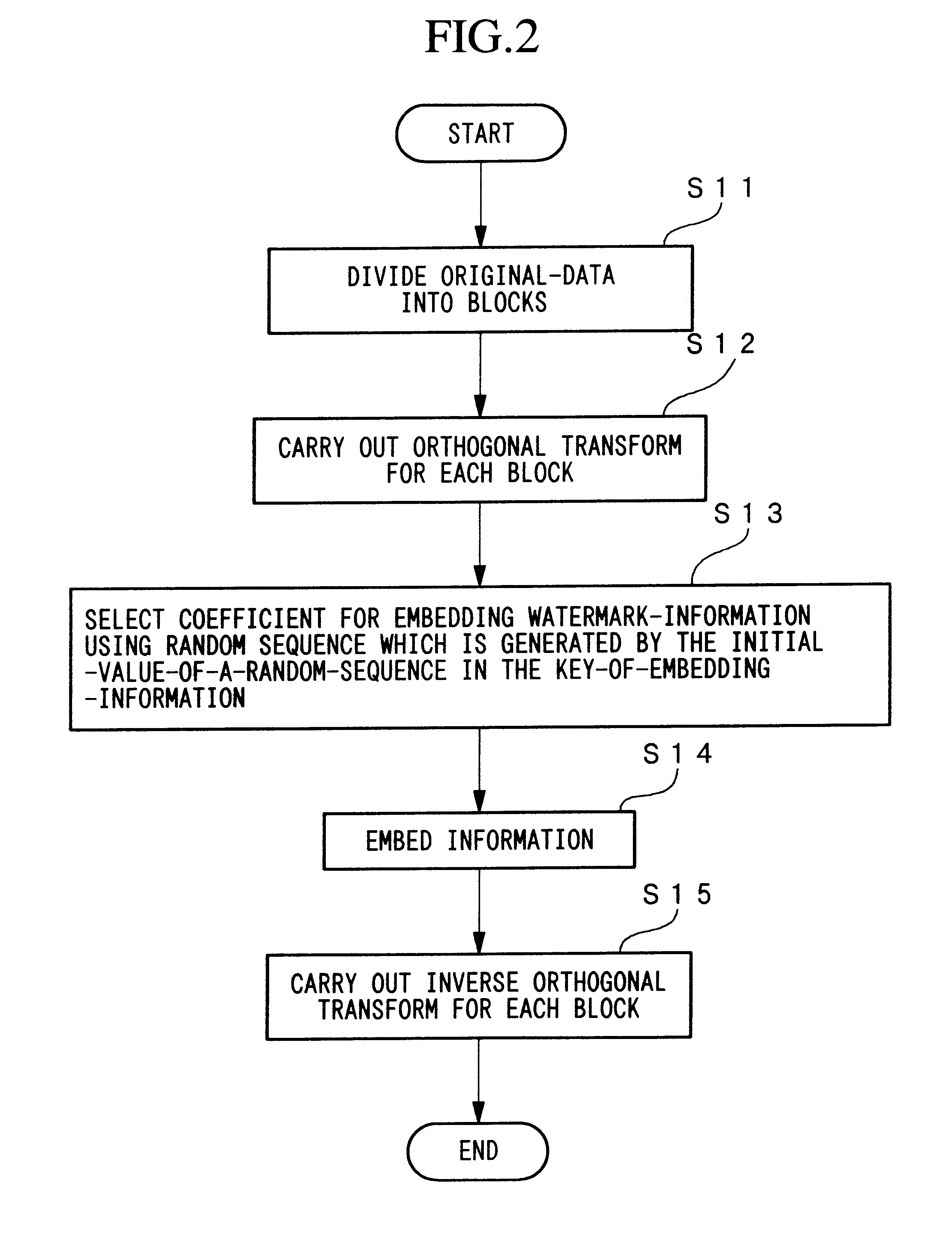
Method for embedding and reading watermark-information in digital form, and apparatus thereof
InactiveUS6185312B1Information can be droppedOther printing matterCharacter and pattern recognitionInformation embeddingOrthogonal transformation
An apparatus for embedding information comprises: a blocking step for dividing data to be processed into blocks; an orthogonal transform step for obtaining coefficients by carrying out orthogonal transformation for each block; an embedding coefficient selecting step for determining coefficients in which the watermark-information will be embedded by using a random sequence which is generated by initial value; an information embedding step for sequentially embedding the watermark-information, which has arbitrary length of bits, by quantizing value of said coefficients using a predetermined value for quantization; and an inverse orthogonal transform step for carrying out inverse orthogonal transformation for modified coefficients to form block in which the watermark-information is embedded, as well as combining the divided blocks and reconstructing the original form.
Owner:NIPPON TELEGRAPH & TELEPHONE CORP
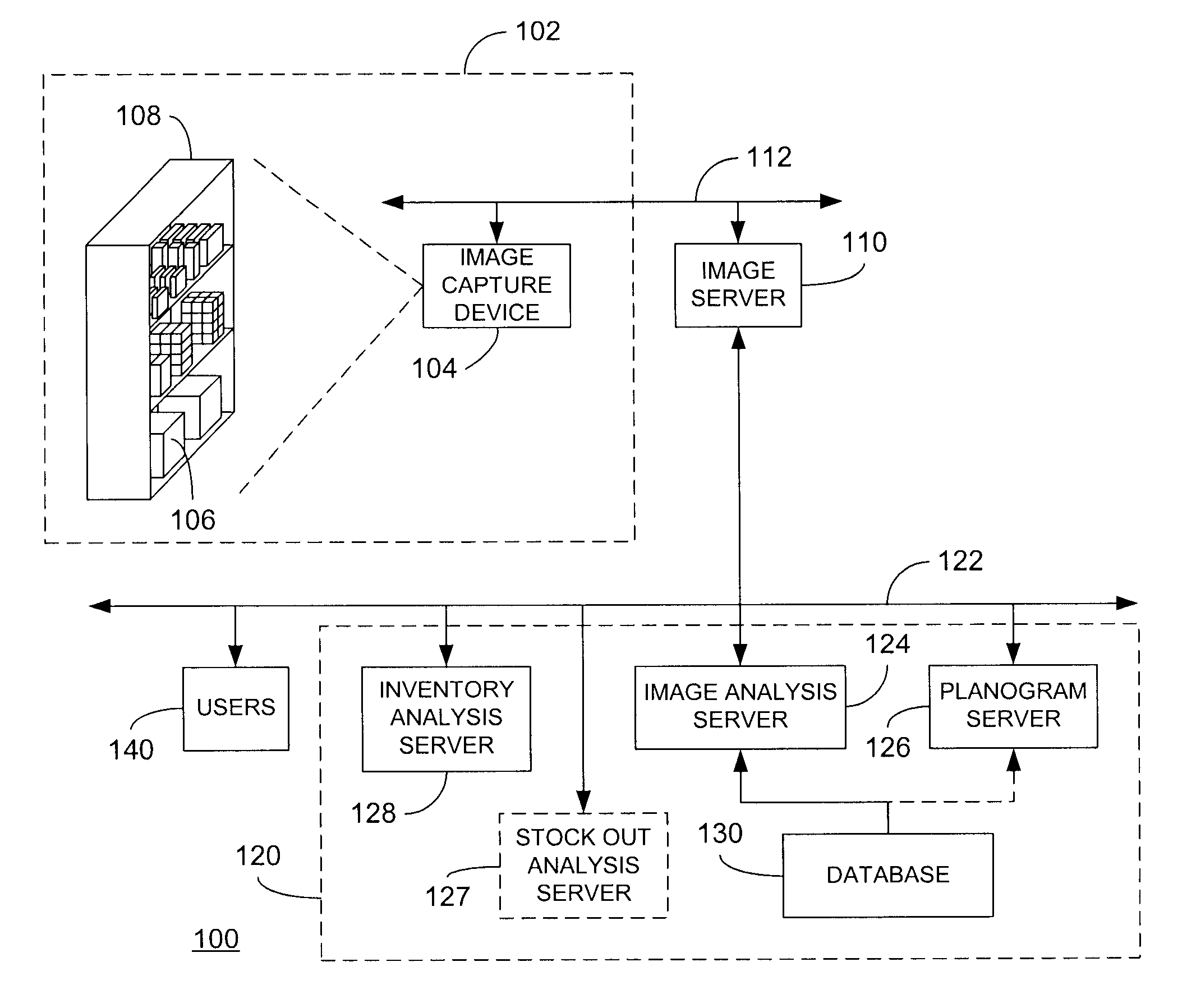
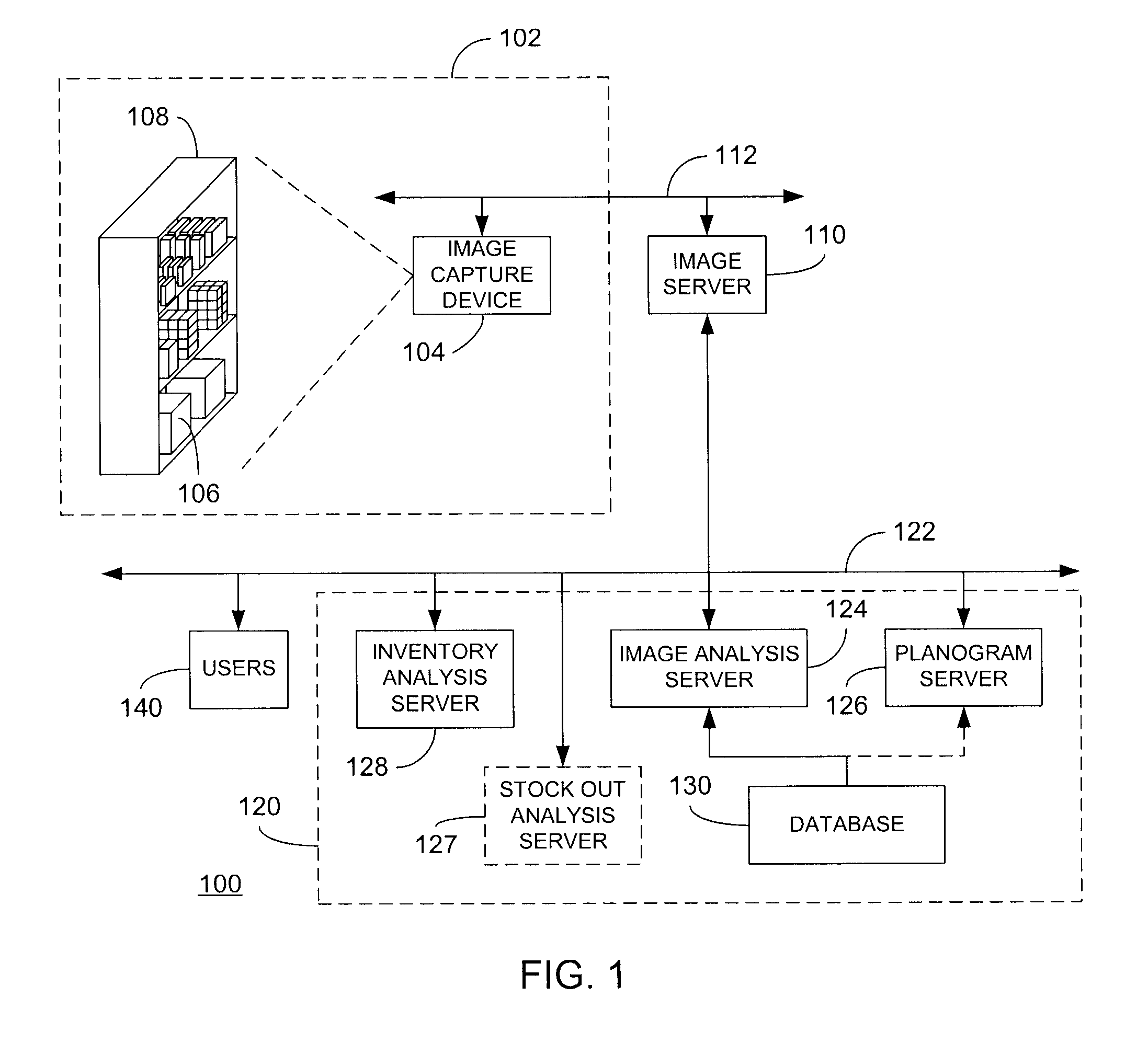
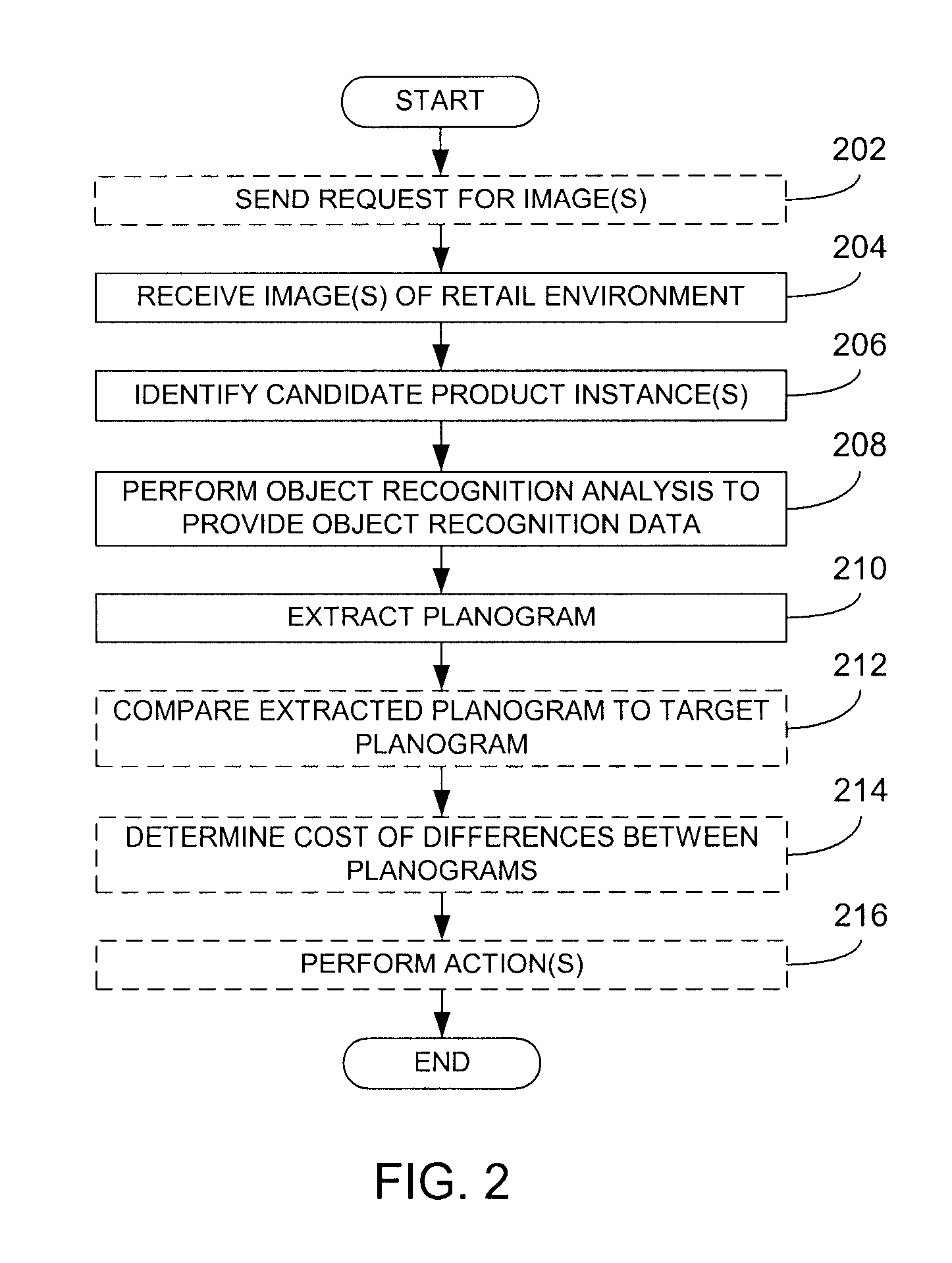
Detection of stock out conditions based on image processing
ActiveUS8630924B2Enhancing efficiency and effectivenessQuick checkElectric signal transmission systemsHand manipulated computer devicesPattern recognitionObject based
Owner:ACCENTURE GLOBAL SERVICES LTD
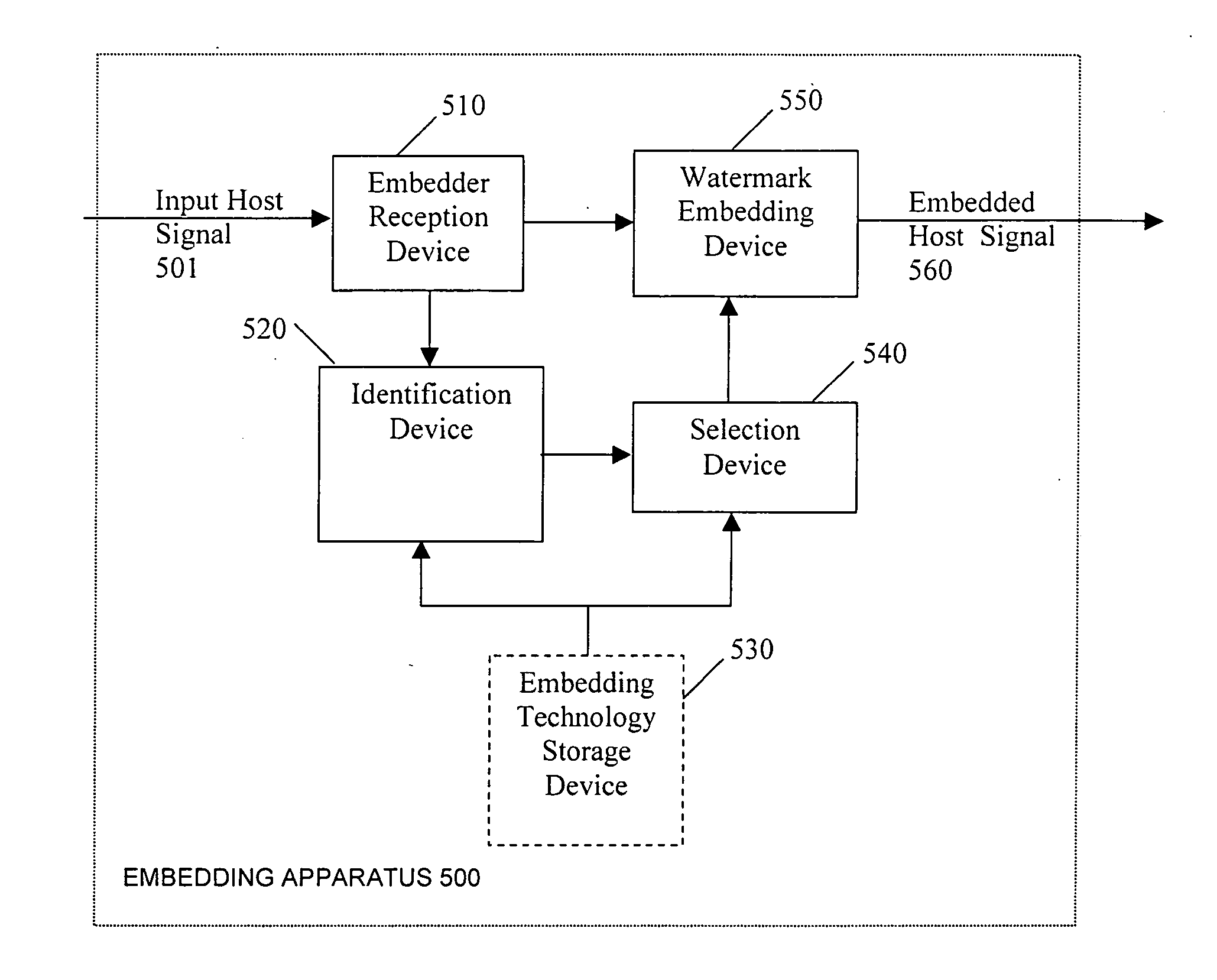
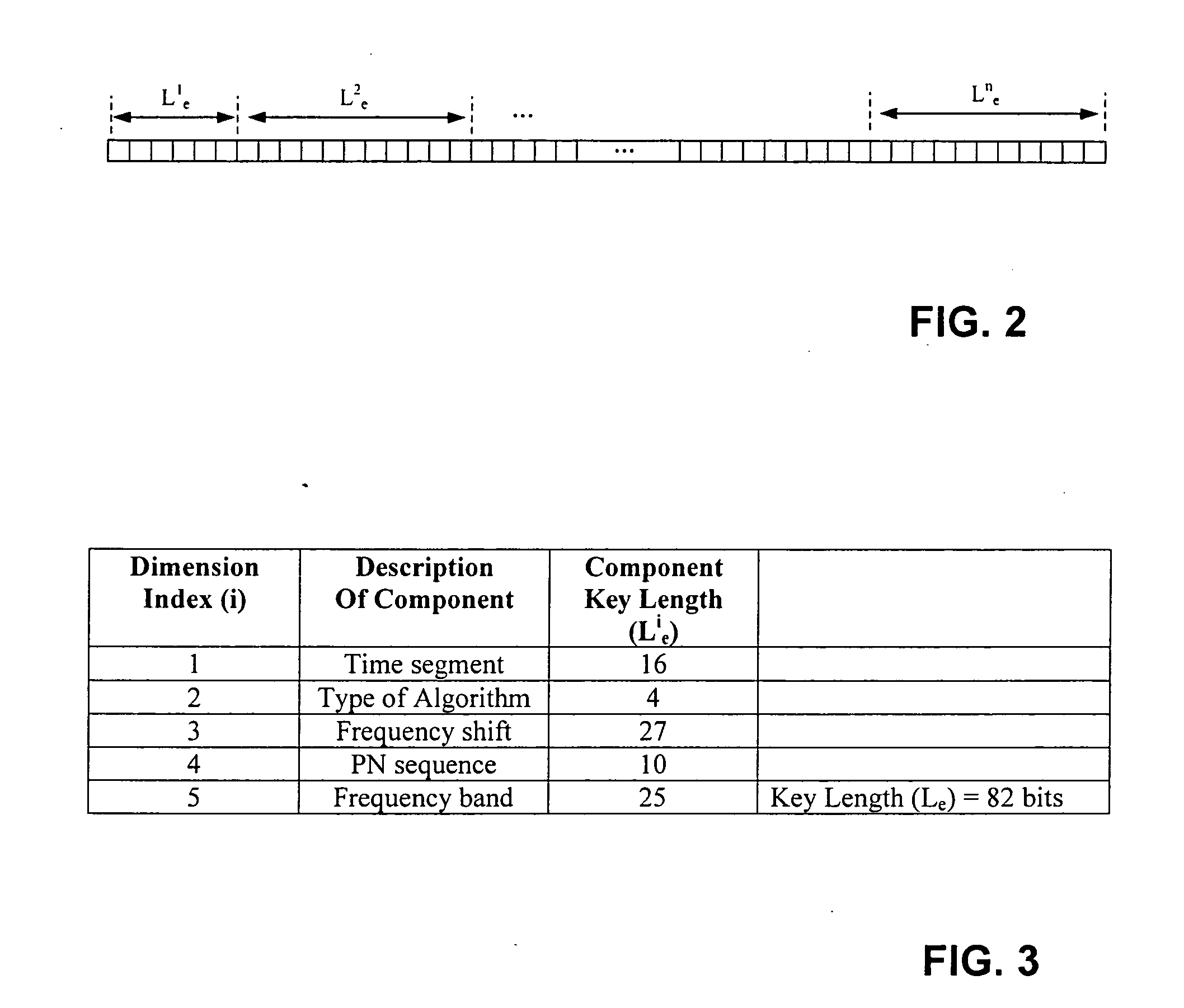
Security enhancements of digital watermarks for multi-media content
InactiveUS20060239501A1Reliable methodLow costUser identity/authority verificationSpeech analysisTheoretical computer scienceSecurity enhancement
Methods and apparatus for embedding digital watermarks into a digital host content are provided. A digital host content is received, e.g., at a receiver or other device incorporating a receiver. One or more watermark embedding technologies is selected. Multiple embedding opportunities are identified within the host content. A subset of the identified embedding opportunities is selected. A multiplicity of digital watermarks are then embedded into the host content in accordance with the selected subset of embedding opportunities utilizing the one or more selected watermark embedding technologies. The selecting of the subset of embedding opportunities may be adapted to provide a desired tradeoff between levels of robustness, security, and transparency of the watermark. A plurality of watermarking embedding technologies may be selected and used in the embedding step.
Owner:VERANCE
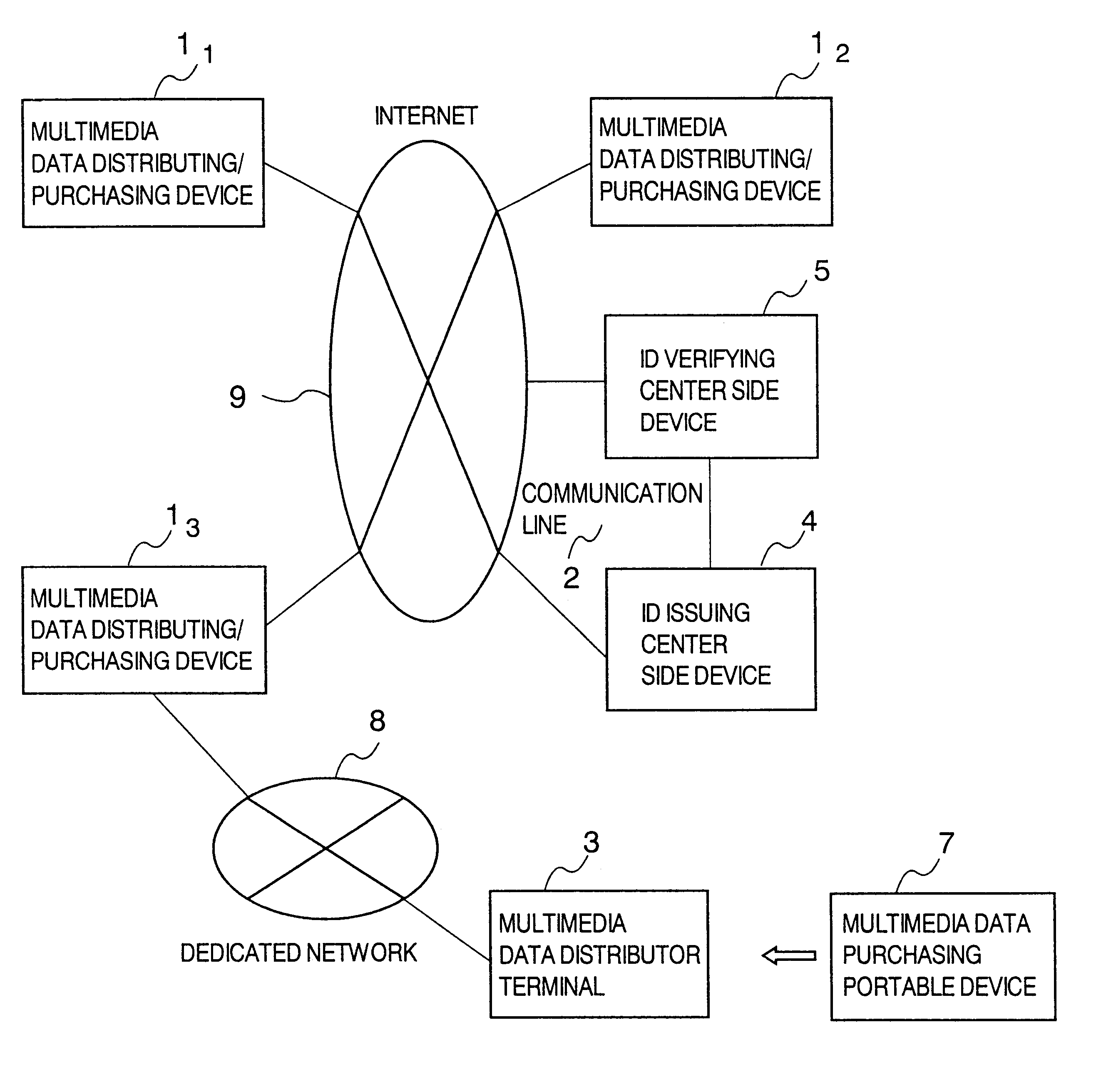
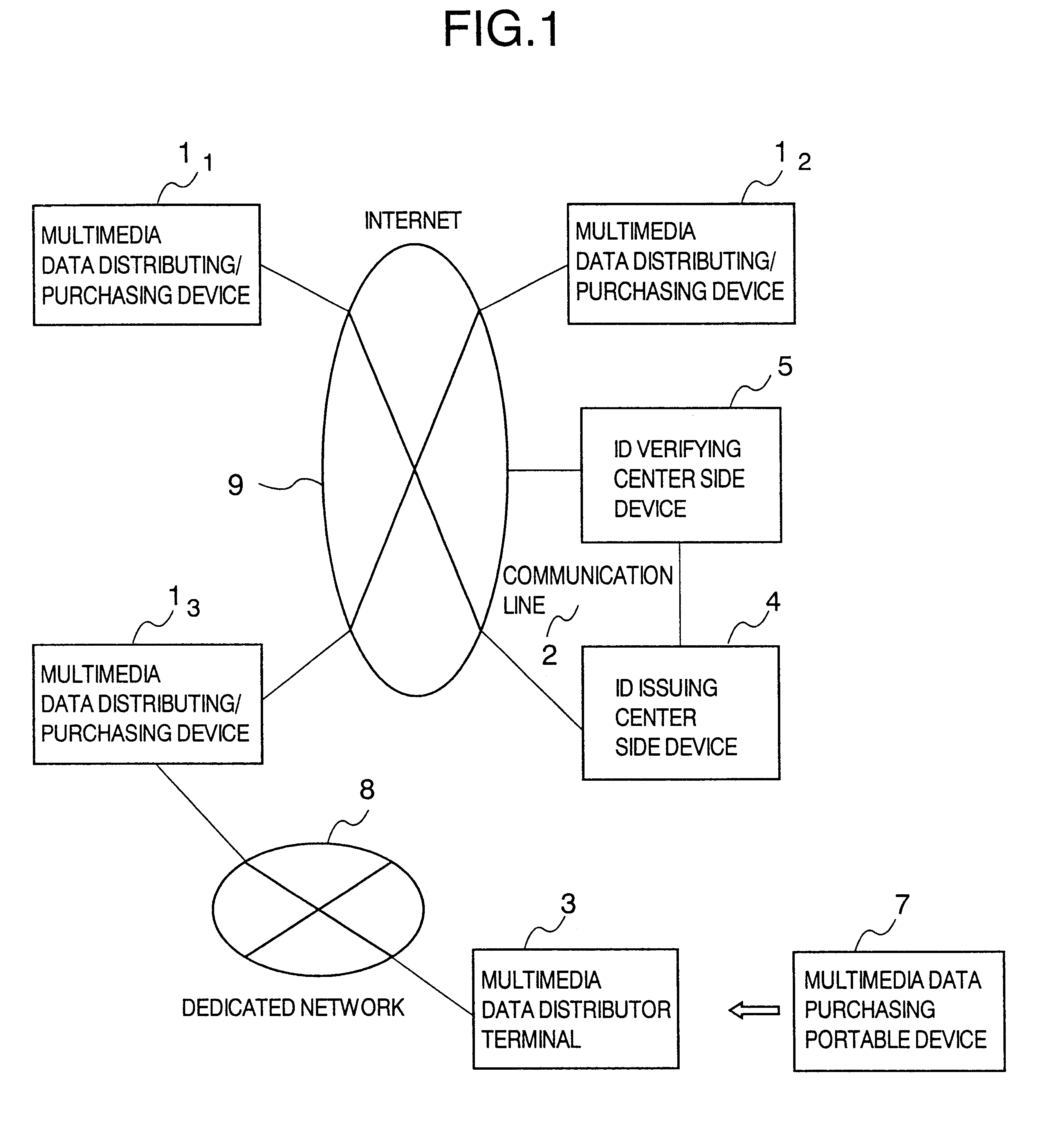
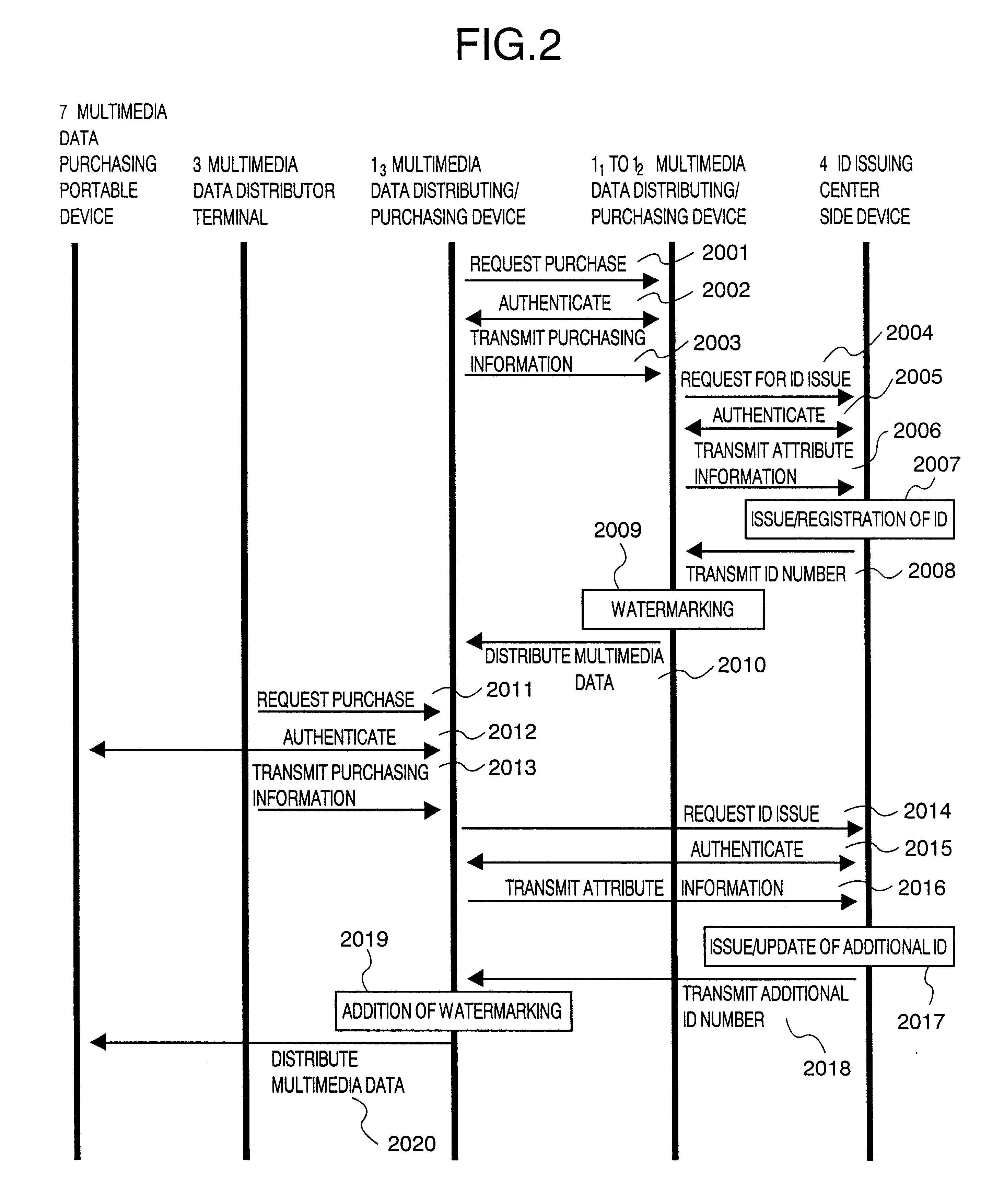
Method and system for distributing multimedia data with management information
InactiveUS6889211B1Data processing applicationsDigital data protectionInformation embeddingManagement information systems
A multimedia data distributing system comprising an ID issuing center side device and a multimedia data distributor side device for distributing multimedia data as electronic data to a purchaser of the multimedia data. The multimedia data distributor device includes: an attribute information transmitting unit that transmits attribute information of the electronic data indicating the multimedia data to be distributed, to the ID issuing center side device; a watermark information embedding unit that embeds information specifying the ID number transmitted from the ID issuing center side device in response to the attribute information transmitted to the attribute information transmitting unit, as an watermark information in the electronic data indicating the multimedia data to be distributed; and a distribution unit that distributes the electronic data indicating the multimedia data, in which the information specifying the ID number is embedded as the watermark information by the watermark information embedding unit, to the purchaser of the multimedia data. The ID issuing center side device includes: an ID number generating unit that generates a unique ID number and registering the generated ID number in a database in a manner to correspond to the attribute information transmitted by the distributor of the multimedia data; and an ID number transmitting unit that transmits the information specifying the generated ID number to the multimedia data distributor device.
Owner:HITACHI LTD
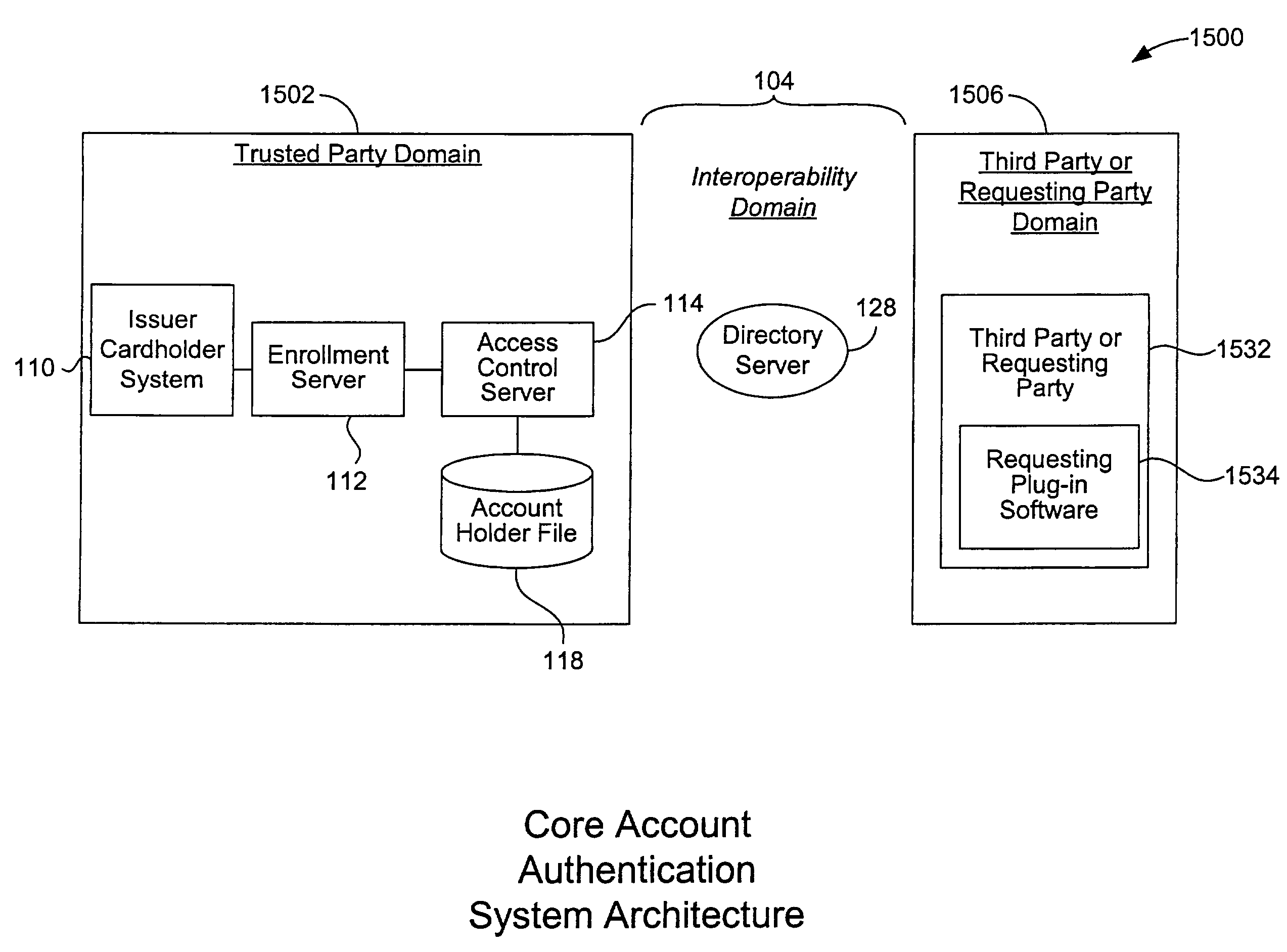
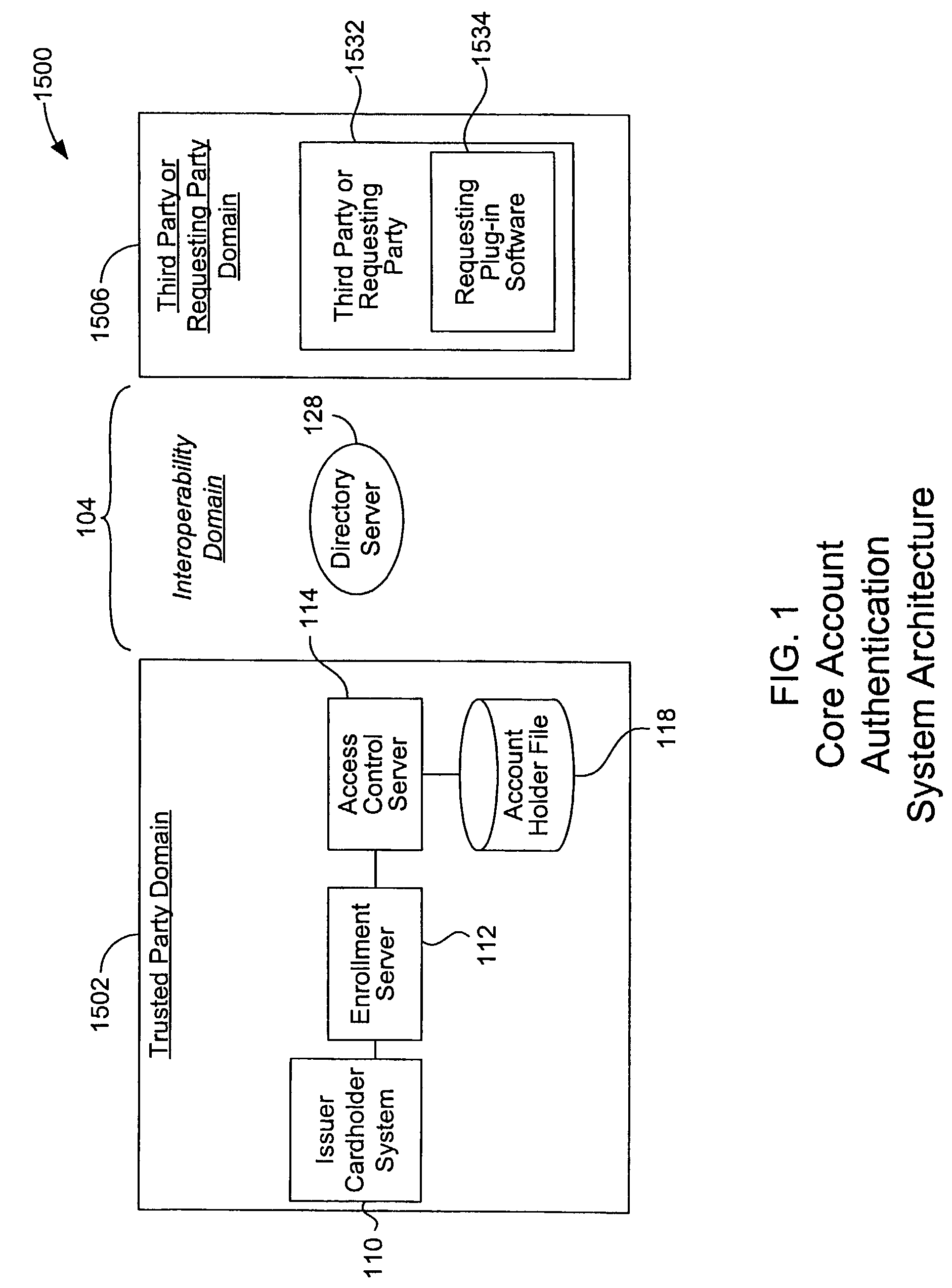
Mobile account authentication service
ActiveUS7707120B2Minimal investmentHigh level of interoperabilityComplete banking machinesFinanceInternet Authentication ServicePayment
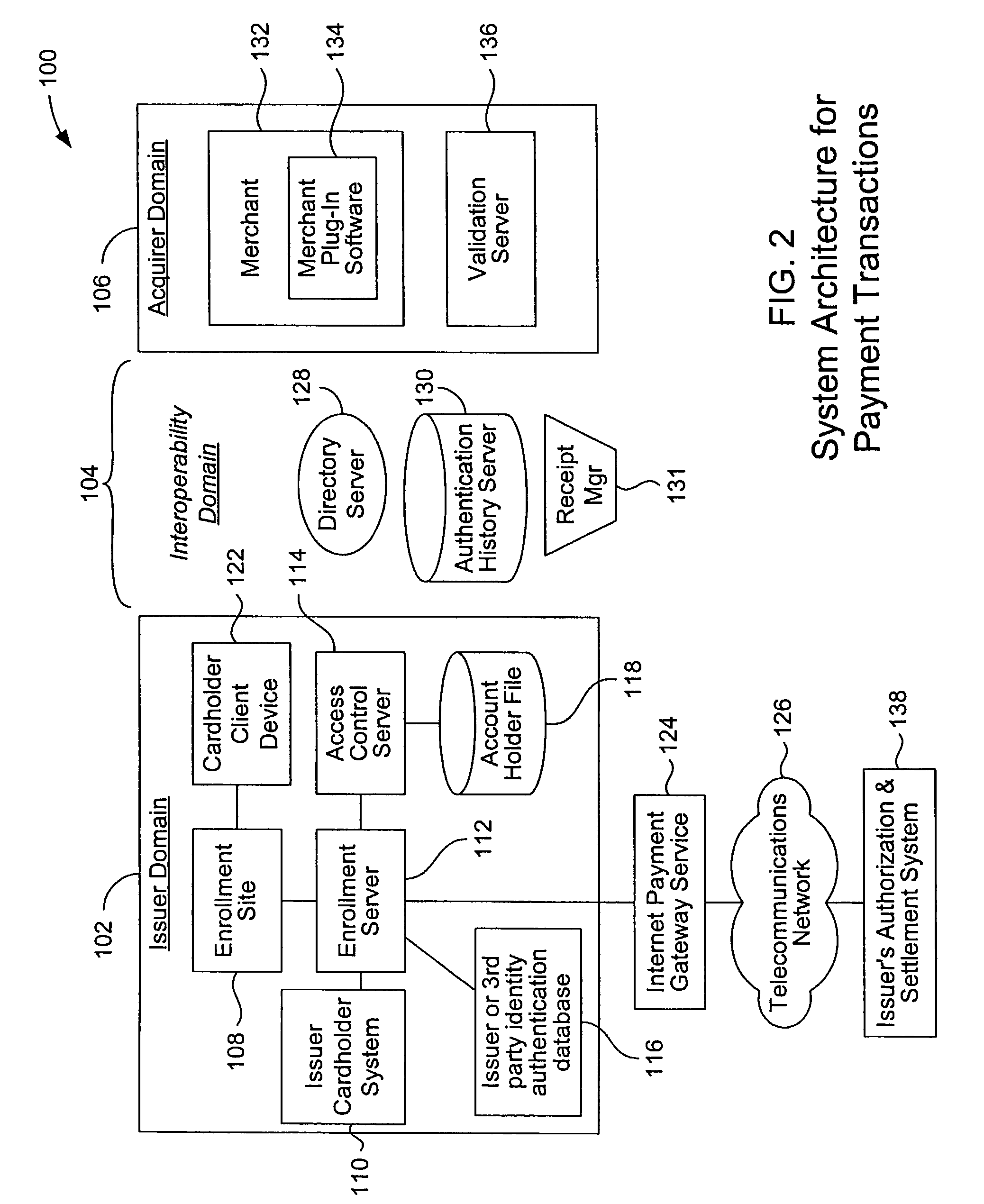
A payment authentication service authenticates the identity of a payer during online transactions. The authentication service allows a card issuer to verify a cardholder's identity using a variety of authentication methods, such as with the use of tokens. Authenticating the identity of a cardholder during an online transaction involves querying an access control server to determine if a cardholder is enrolled in the payment authentication service, requesting a password from the cardholder, verifying the password, and notifying a merchant whether the cardholder's authenticity has been verified. Systems for implementing the authentication service in which a cardholder uses a mobile device capable of transmitting messages via the Internet are described. Systems for implementing the authentication service in which a cardholder uses a mobile device capable of transmitting messages through voice and messaging channels is also described.
Owner:VISA INT SERVICE ASSOC
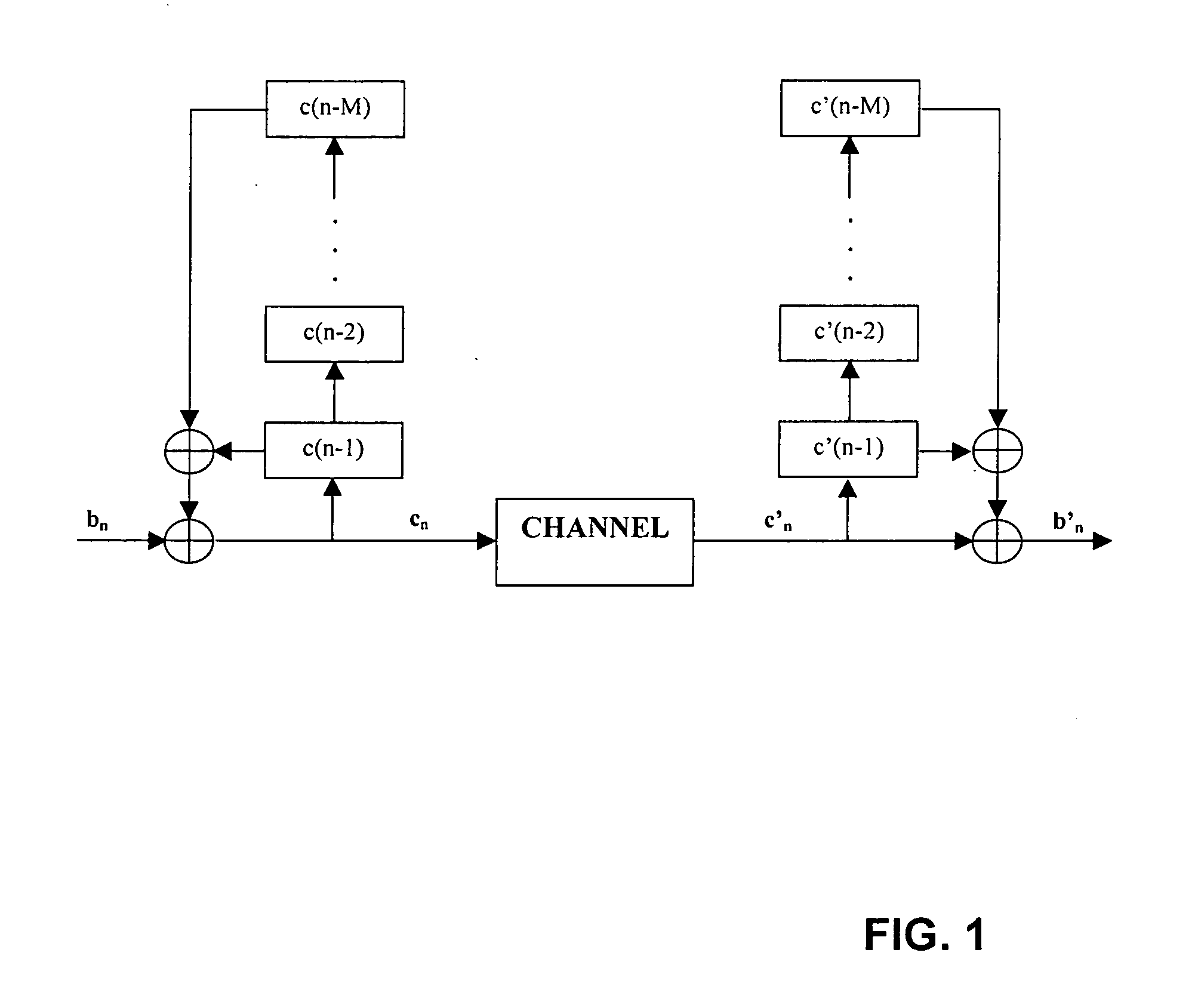
Generating and matching hashes of multimedia content
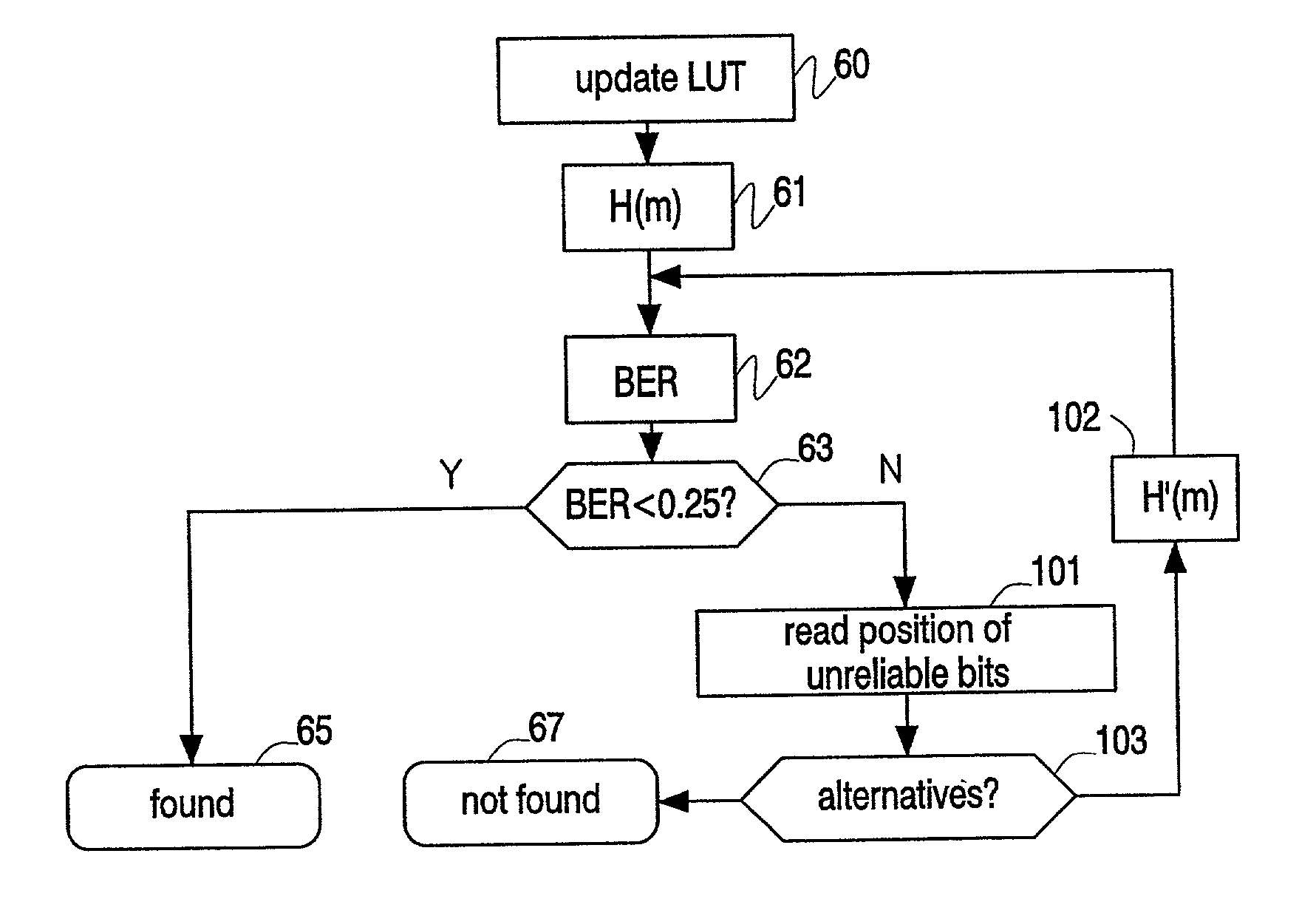
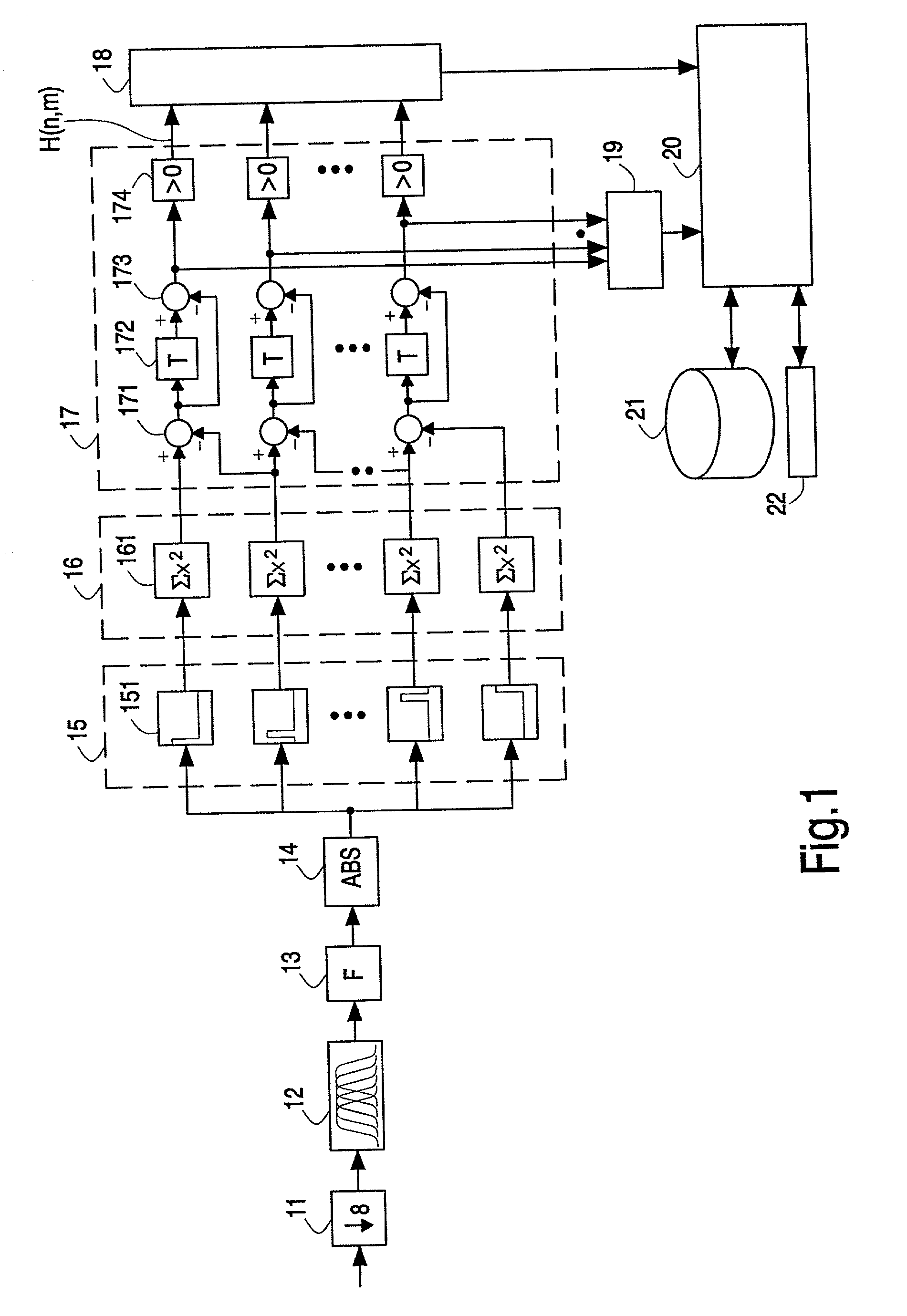
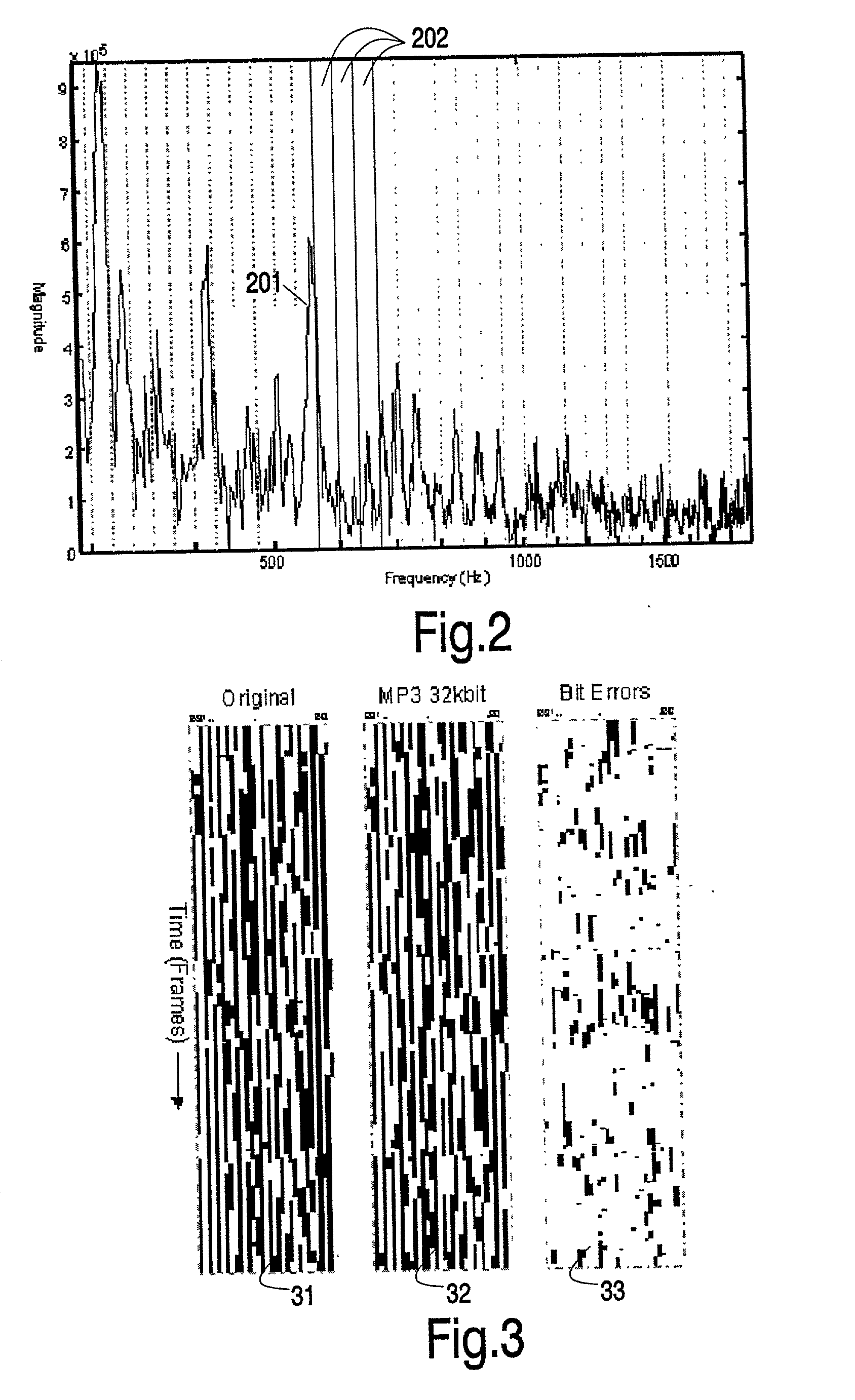
ActiveUS20020178410A1RobustRobust hashingElectrophonic musical instrumentsCode conversionFrequency spectrumAlgorithm
Hashes are short summaries or signatures of data files which can be used to identify the file. Hashing multimedia content (audio, video, images) is difficult because the hash of original content and processed (e.g. compressed) content may differ significantly. The disclosed method generates robust hashes for multimedia content, for example, audio clips. The audio clip is divided (12) into successive (preferably overlapping) frames. For each frame, the frequency spectrum is divided (15) into bands. A robust property of each band (e.g. energy) is computed (16) and represented (17) by a respective hash bit. An audio clip is thus represented by a concatenation of binary hash words, one for each frame. To identify a possibly compressed audio signal, a block of hash words derived therefrom is matched by a computer (20) with a large database (21). Such matching strategies are also disclosed. In an advantageous embodiment, the extraction process also provides information (19) as to which of the hash bits are the least reliable. Flipping these bits considerably improves the speed and performance of the matching process.
Owner:GRACENOTE
Apparatus and method for providing secure network communication
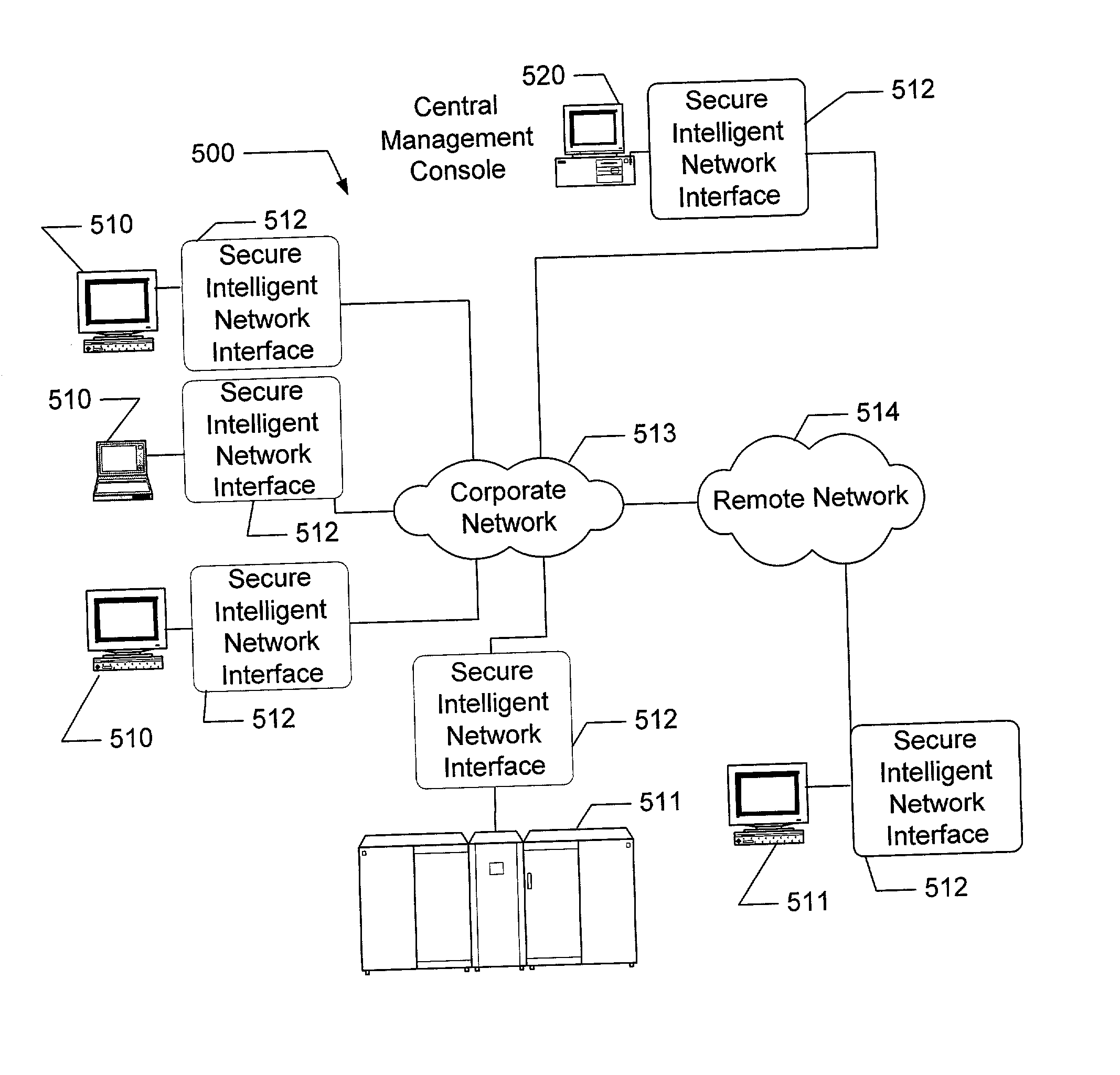
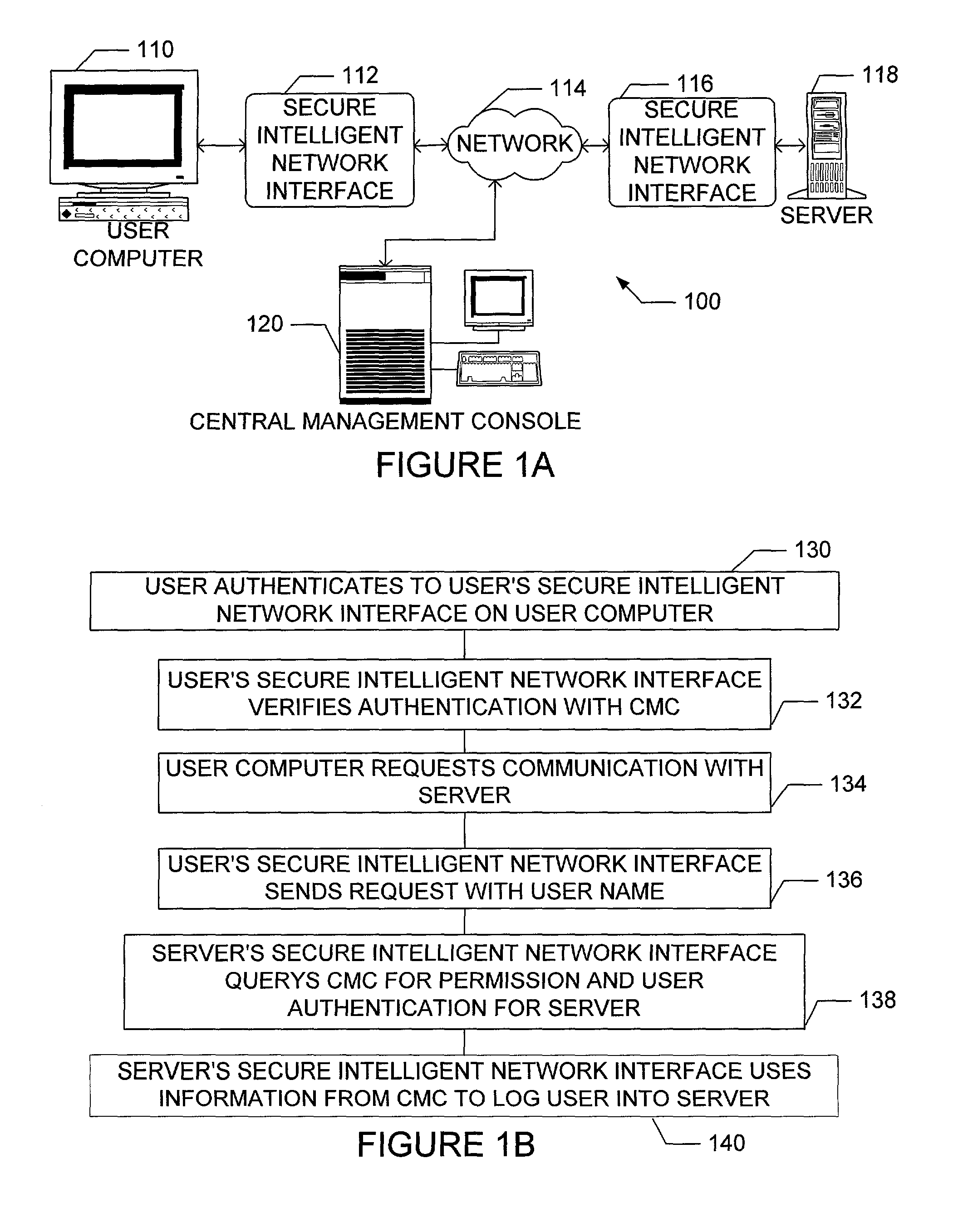
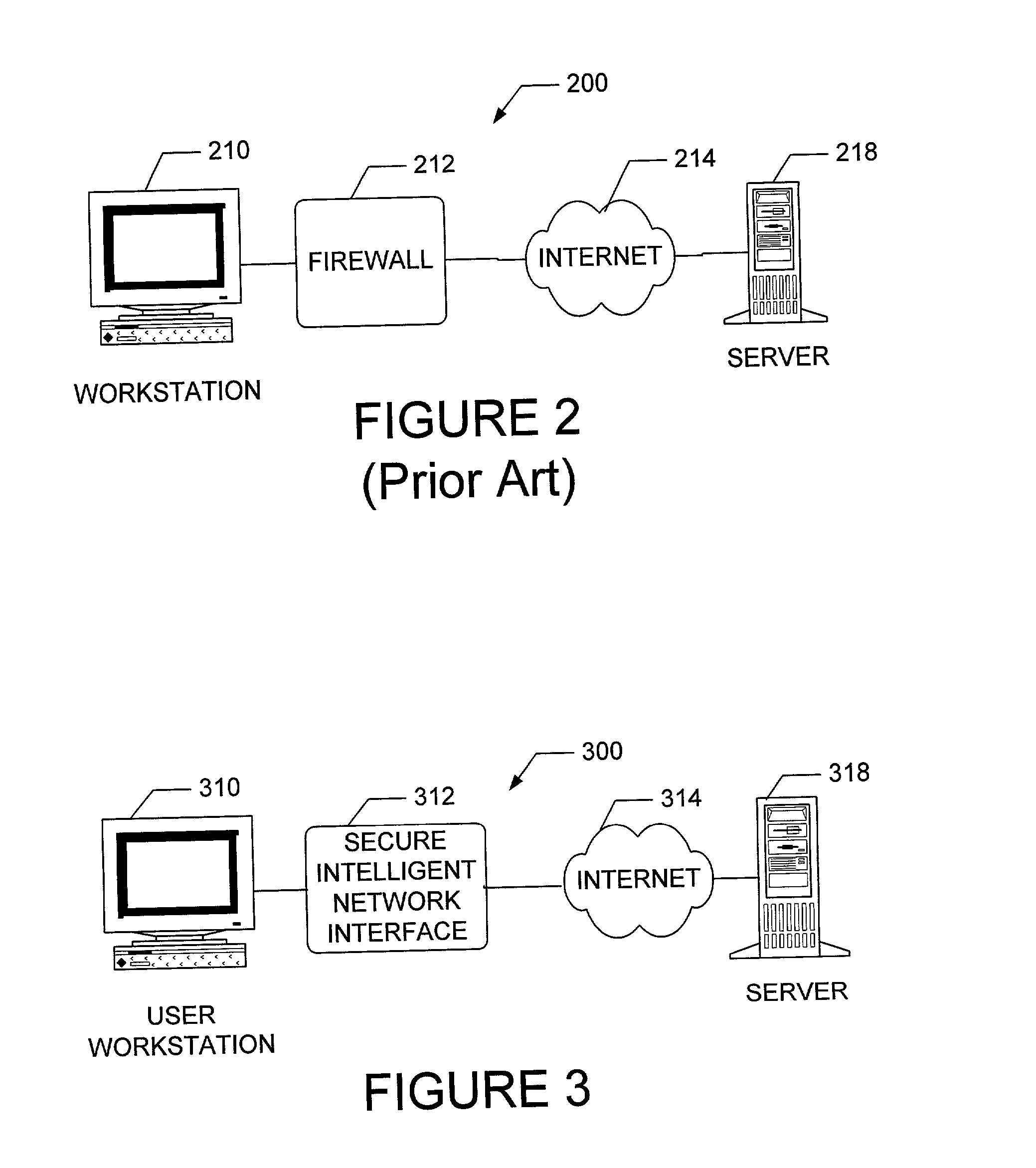
InactiveUS20020162026A1Eliminate attackEliminate needData taking preventionDigital data processing detailsFault toleranceIntelligent Network
The present invention is drawn to an apparatus and method for providing secure network communication. Each node or computer on the network has a secure, intelligent network interface with a coprocessor that handles all network communication. The intelligent network interface can be built into a network interface card (NIC) or be a separate box between each machine and the network. The intelligent network interface encrypts outgoing packets and decrypts incoming packets from the network based on a key and algorithm managed by a centralized management console (CMC) on the network. The intelligent network interface can also be configured by the CMC with dynamically distributed code to perform authentication functions, protocol translations, single sign-on functions, multi-level firewall functions, distinguished-name based firewall functions, centralized user management functions, machine diagnostics, proxy functions, fault tolerance functions, centralized patching functions, Web-filtering functions, virus-scanning functions, auditing functions, and gateway intrusion detection functions.
Owner:NEUMAN MICHAEL +1
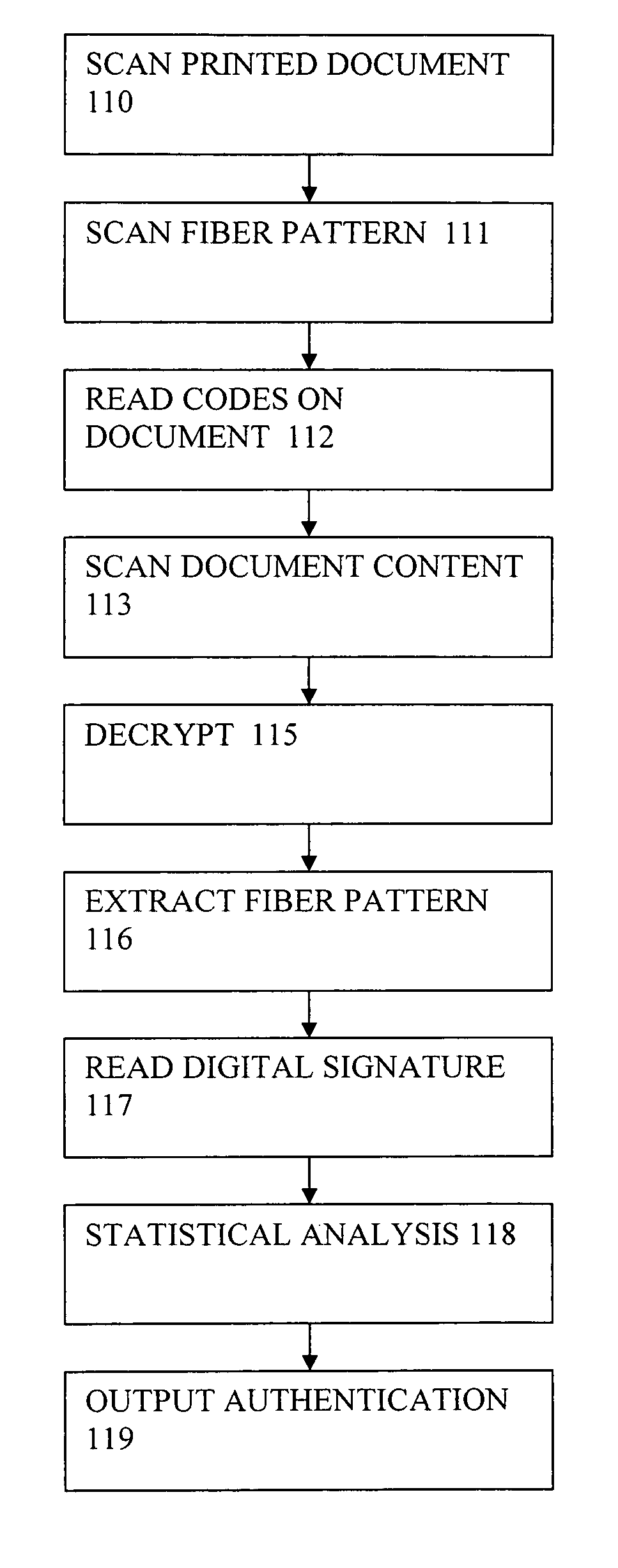
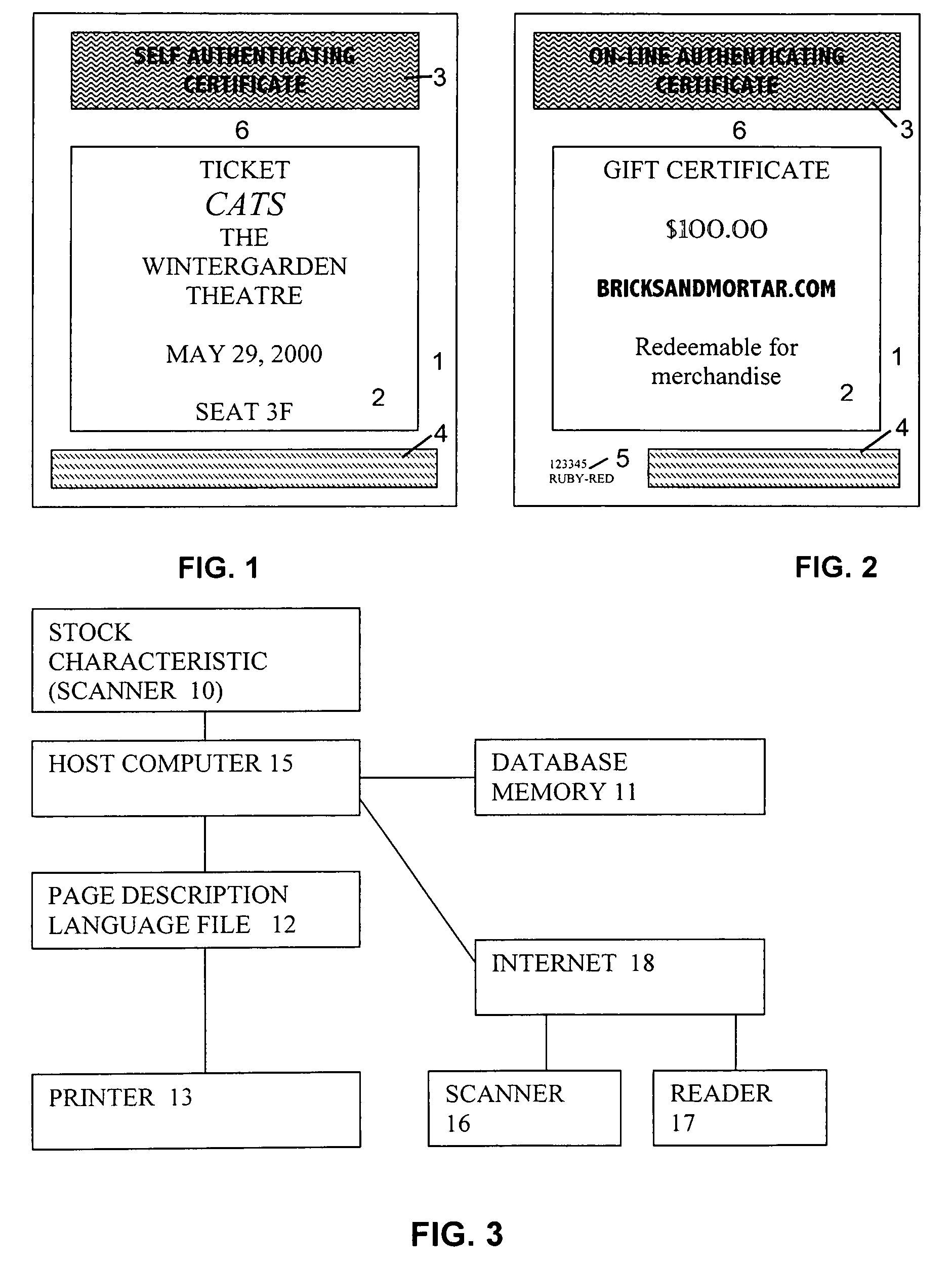
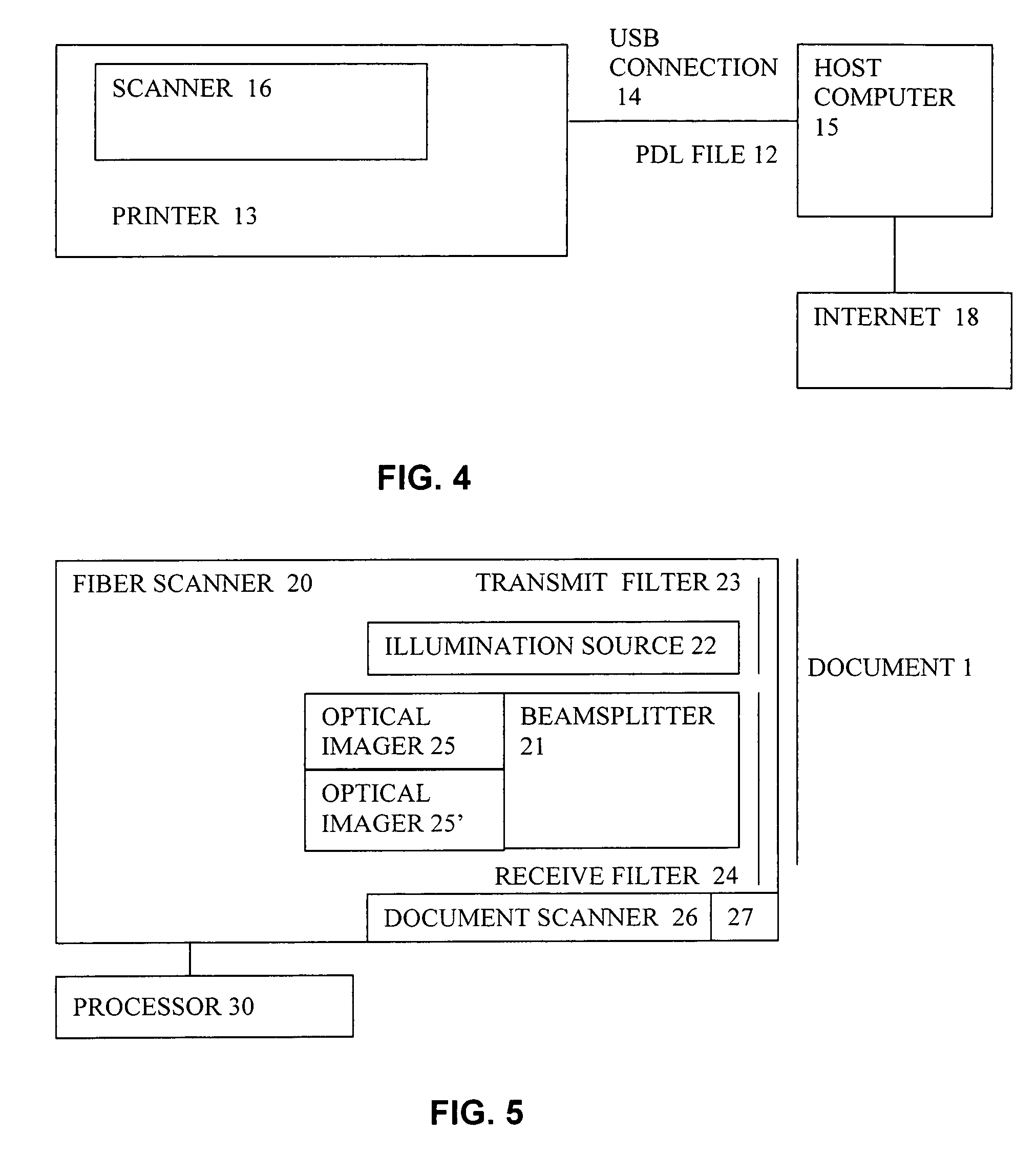
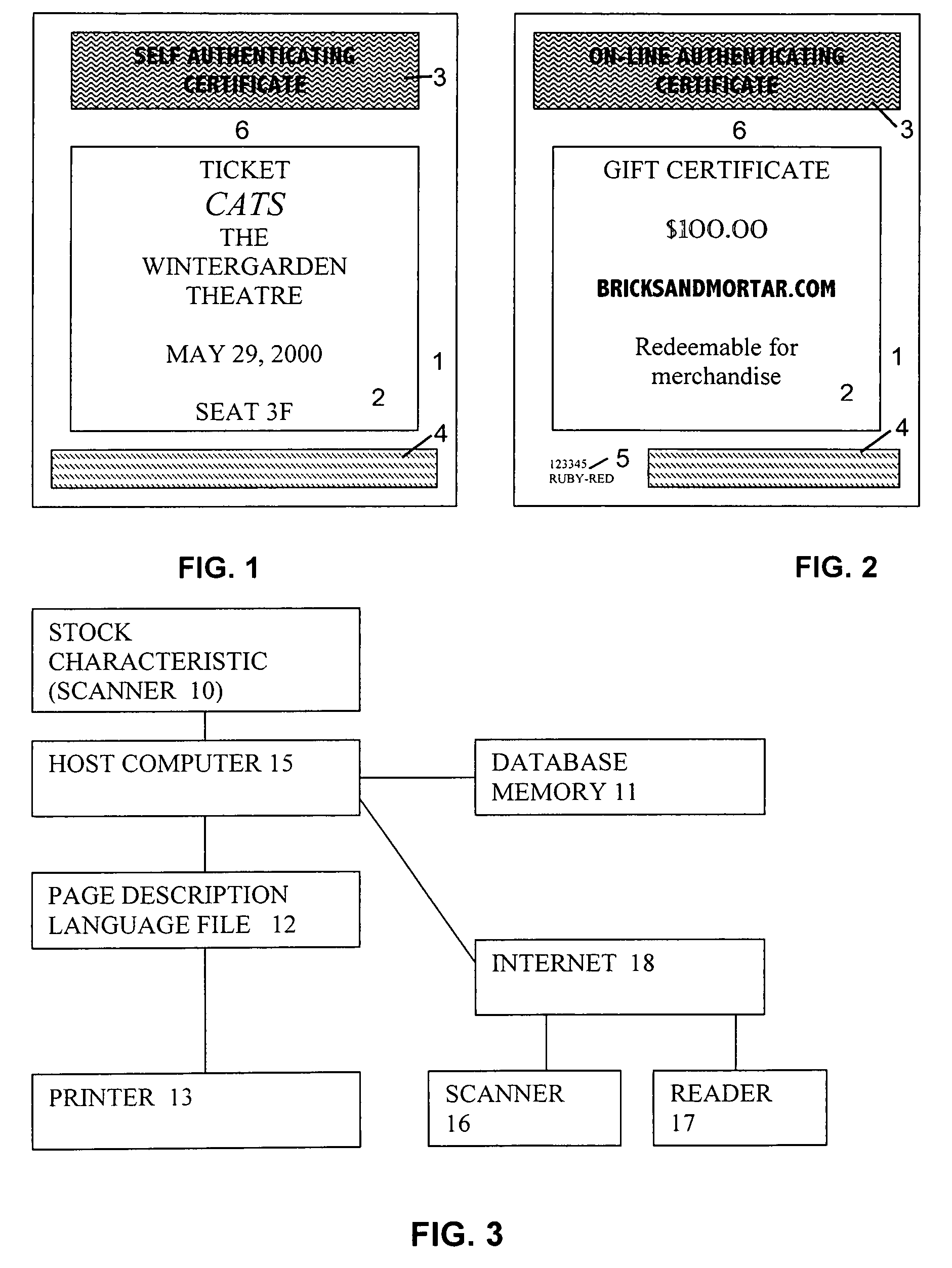
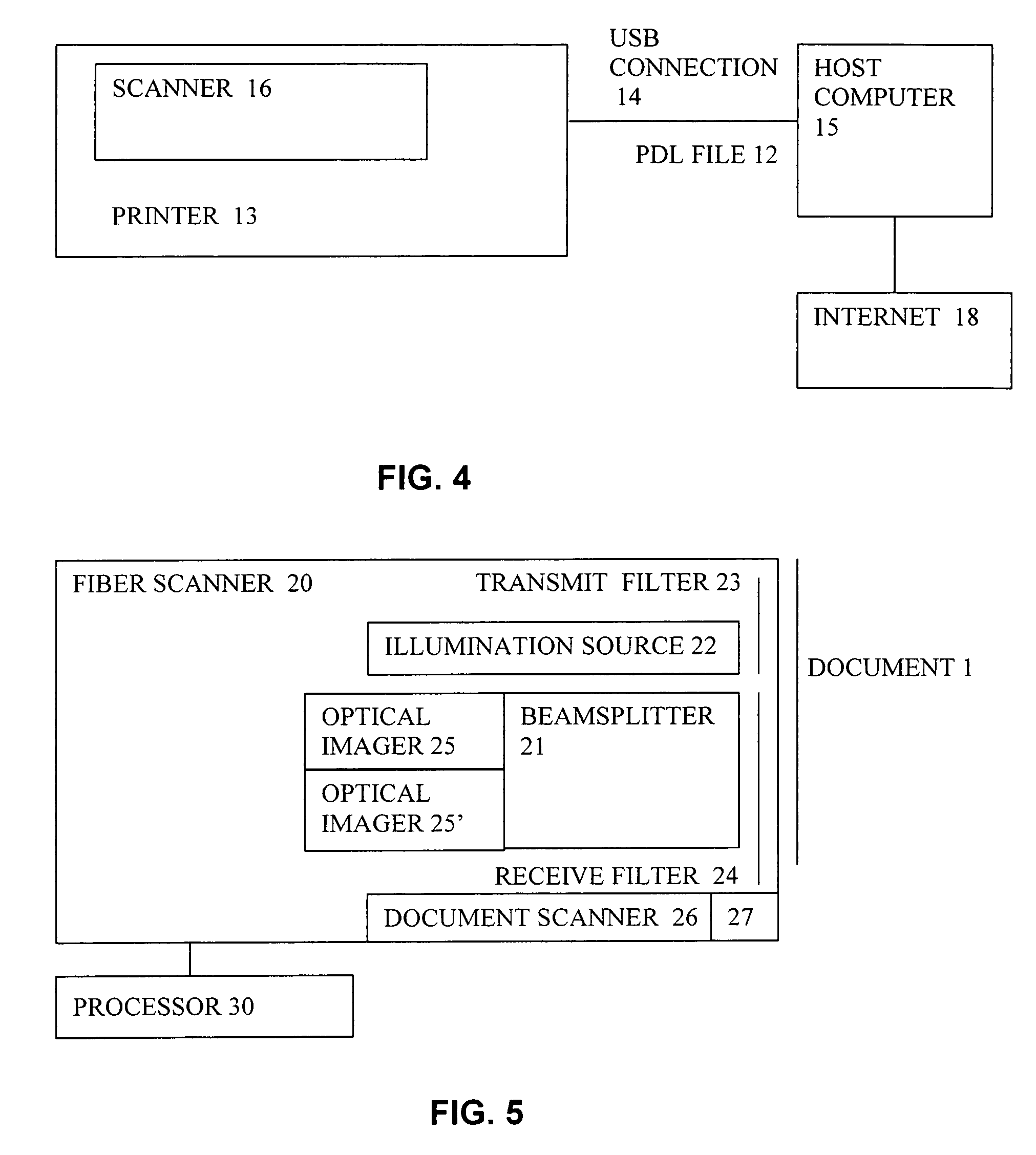
System and method for production and authentication of original documents
InactiveUS7080041B2Improve shielding effectImprove accuracyOther printing matterUser identity/authority verificationDocument IdentifierLogical security
A system and method for authenticating documents and content thereof. A counterfeit resistant document recording medium is provided, having thereon a predefined unique document identifier and at least one security feature. The recording medium is thereafter imprinted with document content, which typically varies between documents. The document content is stored in a database, indexed by an associated document identifier. The document may then be authenticated by checking the security feature and comparing the stored document content with a perceived document content. The system provides a number of opportunities for commercial exploitation, including sales of identified recording media, recording of information in a database, on-line authentication transactions, differential accounting for document validations and counterfeit identifications, imprinting devices, authentication devices, and the like. The system prevents counterfeiting of valuable documents through casual means by providing both physical and logical security.
Owner:ESECUREDOCS
System for controlling access and distribution of digital property
InactiveUS20010021926A1Key distribution for secure communicationMultiple keys/algorithms usageTamper resistanceData access
A method and device are provided for controlling access to data. Portions of the data are protected and rules concerning access rights to the data are determined. Access to the protected portions of the data is prevented, other than in a non-useable form; and users are provided access to the data only in accordance with the rules as enforced by a mechanism protected by tamper detection. A method is also provided for distributing data for subsequent controlled use of those data. The method includes protecting portions of the data; preventing access to the protected portions of the data other than in a non-useable form; determining rules concerning access rights to the data; protecting the rules; and providing a package including: the protected portions of the data and the protected rules. A user is provided controlled access to the distributed data only in accordance with the rules as enforced by a mechanism protected by tamper protection. A device is provided for controlling access to data having protected data portions and rules concerning access rights to the data. The device includes means for storing the rules; and means for accessing the protected data portions only in accordance with the rules, whereby user access to the protected data portions is permitted only if the rules indicate that the user is allowed to access the portions of the data.
Owner:HANGER SOLUTIONS LLC
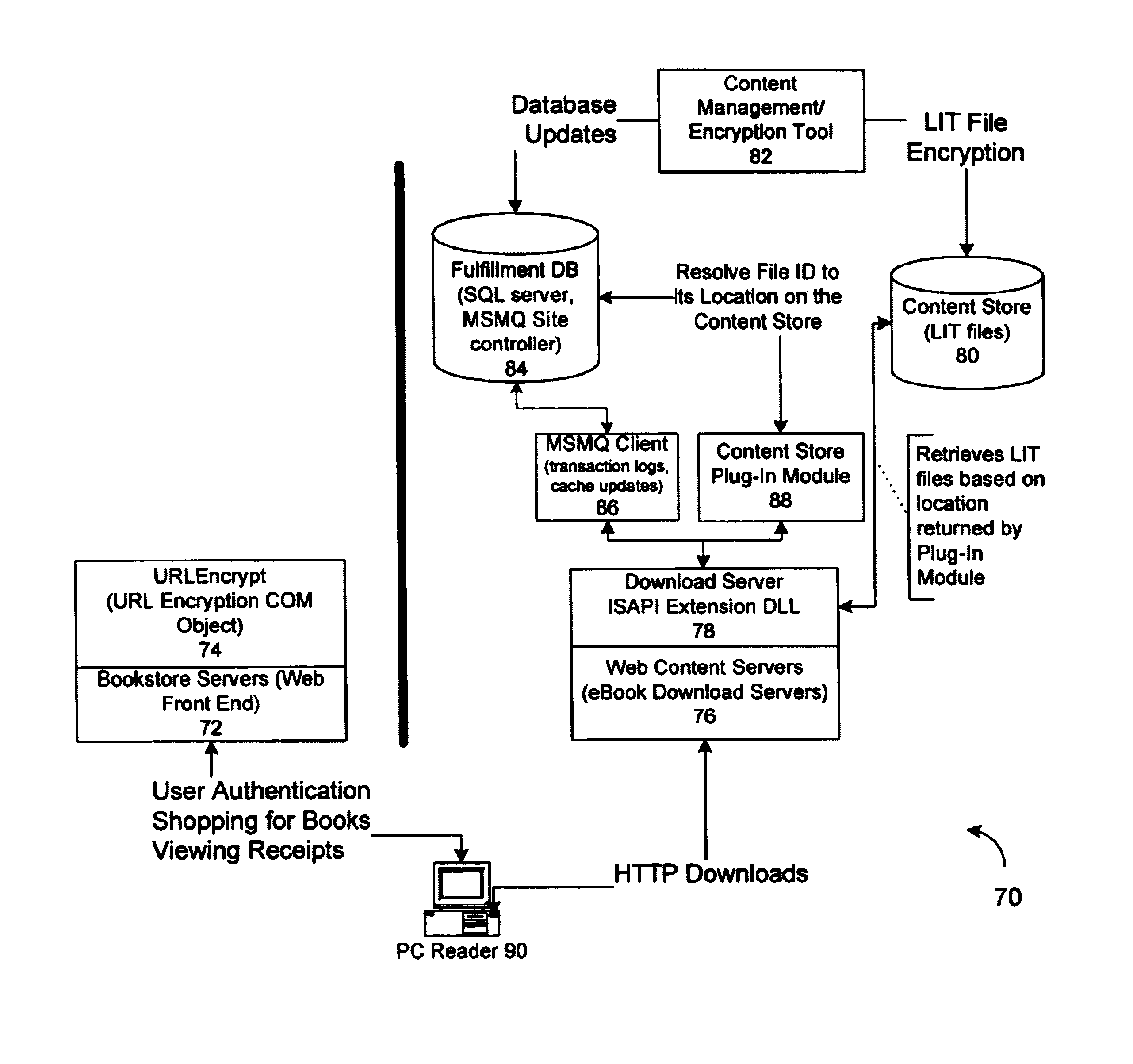
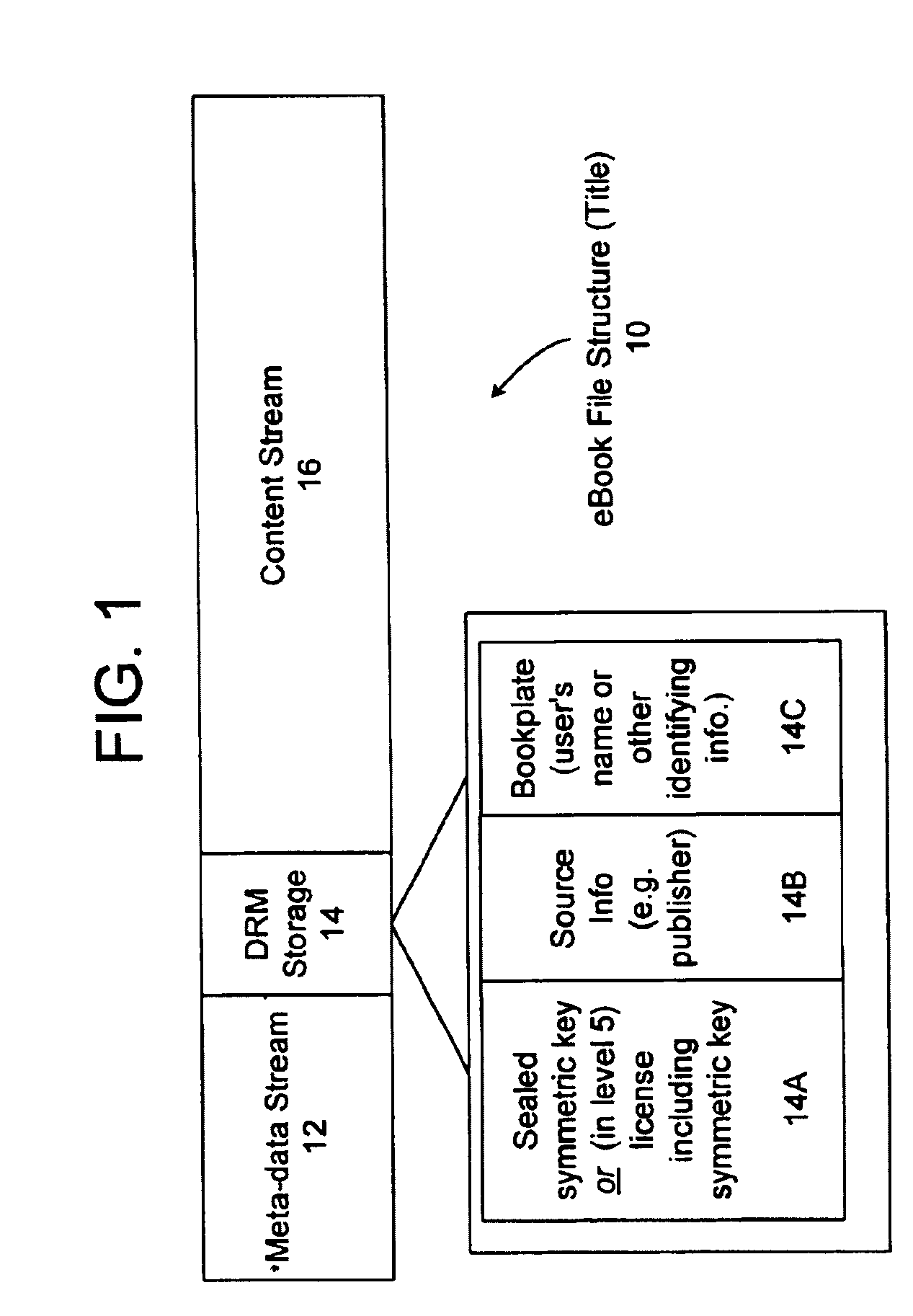
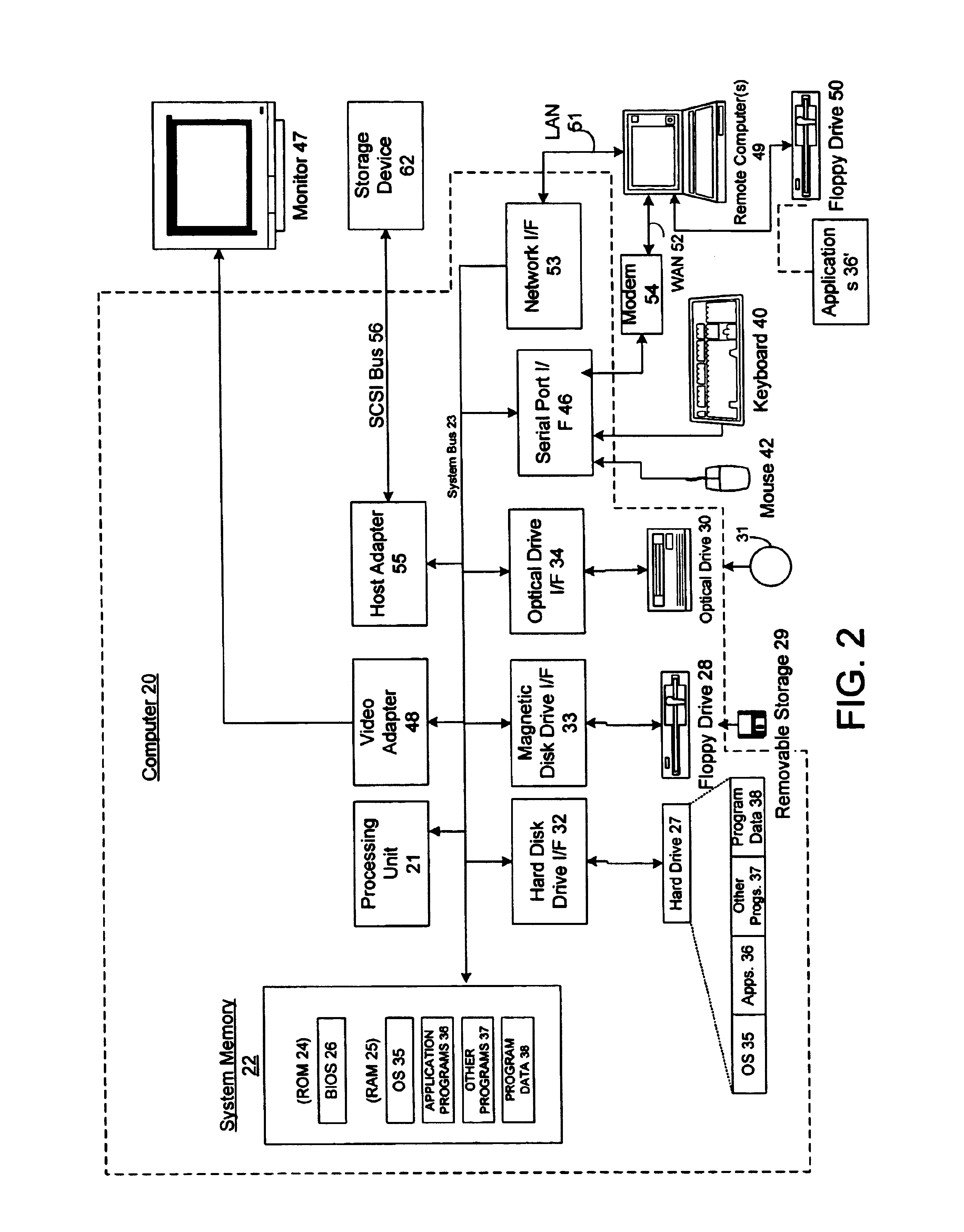
Server for an electronic distribution system and method of operating same
ActiveUS7047411B1Preventing unchecked proliferationKey distribution for secure communicationUser identity/authority verificationStore and forwardDigital rights management system
A server architecture for a digital rights management system that distributes and protects rights in content. The server architecture includes a retail site which sells content items to consumers, a fulfillment site which provides to consumers the content items sold by the retail site, and an activation site which enables consumer reading devices to use content items having an enhanced level of copy protection. Each retail site is equipped with a URL encryption object, which encrypts, according to a secret symmetric key shared between the retail site and the fulfillment site, information that is needed by the fulfillment site to process an order for content sold by the retail site. Upon selling a content items, the retail site transmits to the purchase a web page having a link to a URL comprising the address of the fulfillment site and a parameter having the encrypted information. Upon the following the link, the fulfillment site downloads the ordered content to the consumer preparing the content if necessary in accordance with the type of security to be carried with the content. The fulfillment site includes an asynchronous fulfillment pipeline which logs information about processed transactions using a store-and-forward messaging service. The fulfillment site may be implemented as several server devices, each having a cache which stores frequently downloaded content items, in which case the asynchronous fulfillment pipeline may also be used to invalidate the cache if a change is made at one server that affects the cached content items. An activation site provides an activation certificate and a secure repository executable to consumer content-rendering devices which enable those content rendering devices to render content having an enhanced level of copy-resistance. The activation site “activates” client-reading devices in a way that binds them to a persona, and limits the number of devices that may be activated for a particular persona, or the rate at which such devices may be activated for a particular persona.
Owner:MICROSOFT TECH LICENSING LLC
Method and apparatus for making secure electronic payments
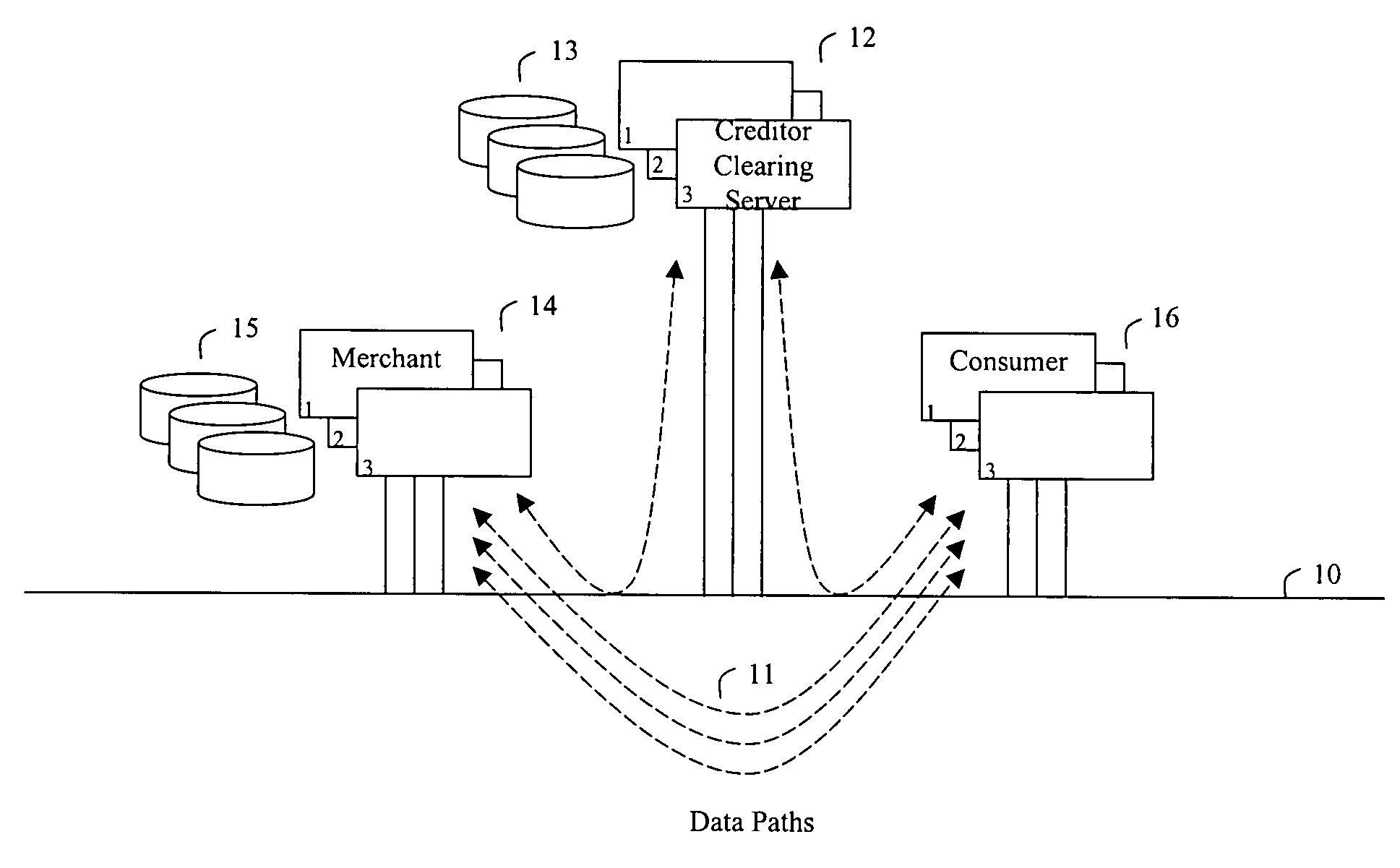
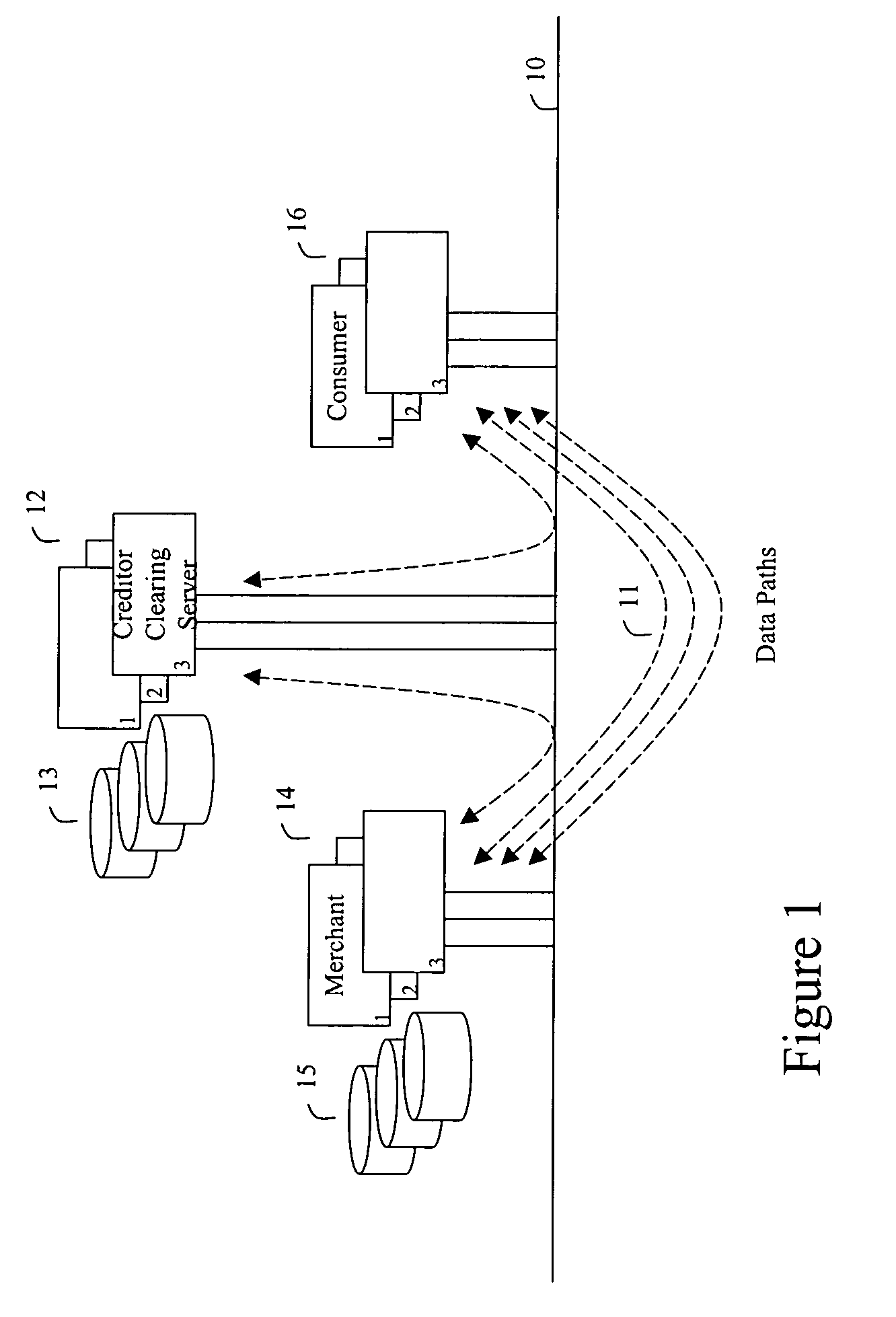
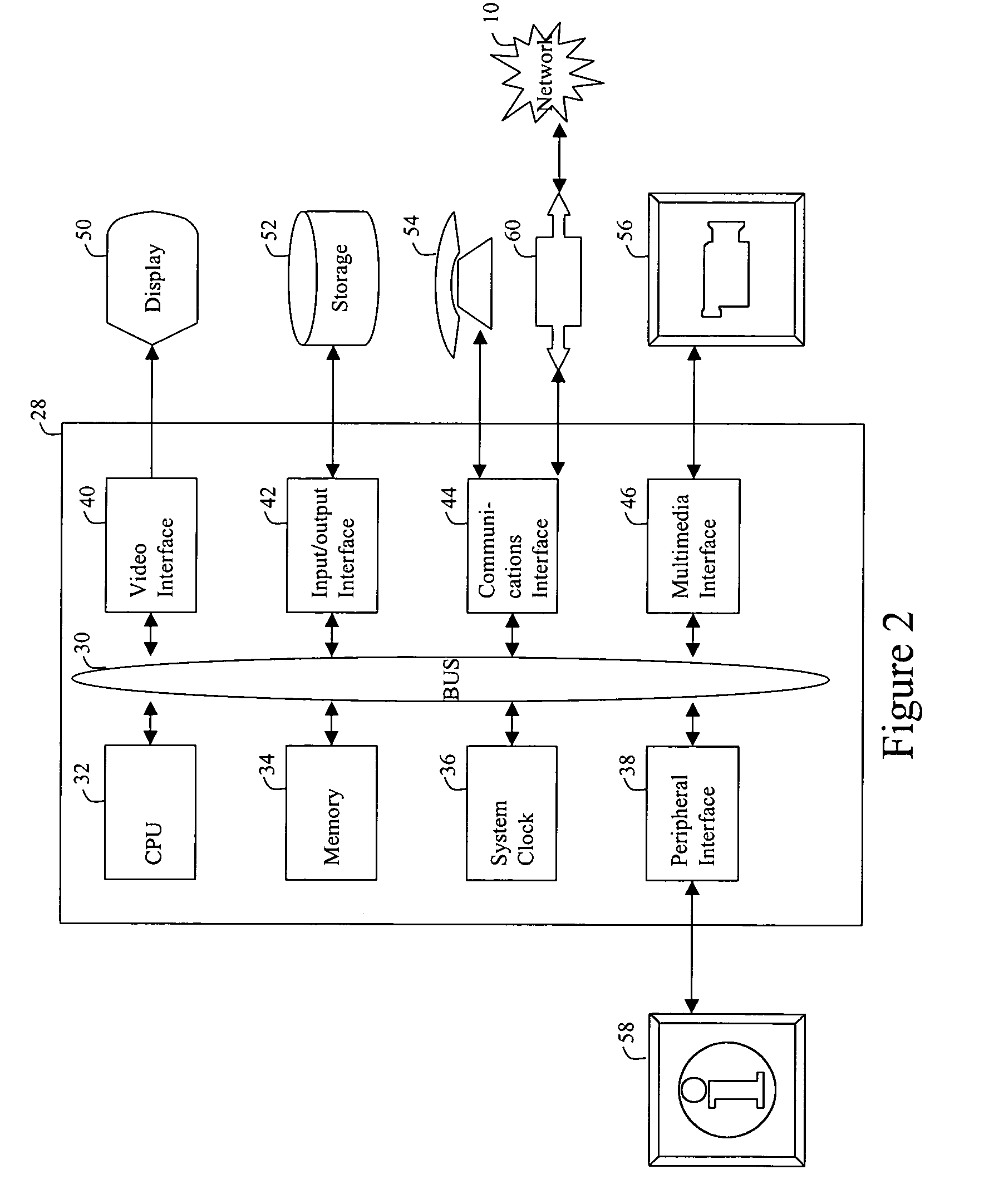
In accordance with the present invention, consumers and merchants use computing devices connected to a network, such as the Internet, through wired and wireless means, wherein the consumer connects to a clearing server device to purchase or retrieve previously purchased token, the consumer then connects to the merchant's computer or website to attain price quotes of goods and services, selects the goods and / or services to be purchased, and then communicates a request for purchase to the merchant. The merchant then communicates a request for an update key to the clearing server. The update key is used as an authorization to modify the value of the token. To debit the customer the decrement key is requested and to credit the customer an increment key is asked for. An overwrite key is another type of update key. Together with the overwrite key a replacement token is provided to the merchant who in turn forwards the new token to the customer. As an aspect of the invention, if the token was not previously used, the clearing server simply issues the update key. If, however, it is determined that the token was used, the amount paid by the consumer to a previous merchant is determined the token adjusted and the overwrite key together with the new token is returned to the merchant. The merchant then forwards the purchased merchandise, the update key, and possibly a new token to the consumer.
Owner:AMPACASH CORP
System and method for production and authentication of original documents
InactiveUS20050038756A1Improve shielding effectImprove accuracyOther printing matterUser identity/authority verificationDocument IdentifierPaper document
A system and method for authenticating documents and content thereof. A counterfeit resistant document recording medium is provided, having thereon a predefined unique document identifier and at least one security feature. The recording medium is thereafter imprinted with document content, which typically varies between documents. The document content is stored in a database, indexed by an associated document identifier. The document may then be authenticated by checking the security feature and comparing the stored document content with a perceived document content. The system provides a number of opportunities for commercial exploitation, including sales of identified recording media, recording of information in a database, on-line authentication transactions, differential accounting for document validations and counterfeit identifications, imprinting devices, authentication devices, and the like. The system prevents counterfeiting of valuable documents through casual means by providing both physical and logical security.
Owner:ESECUREDOCS
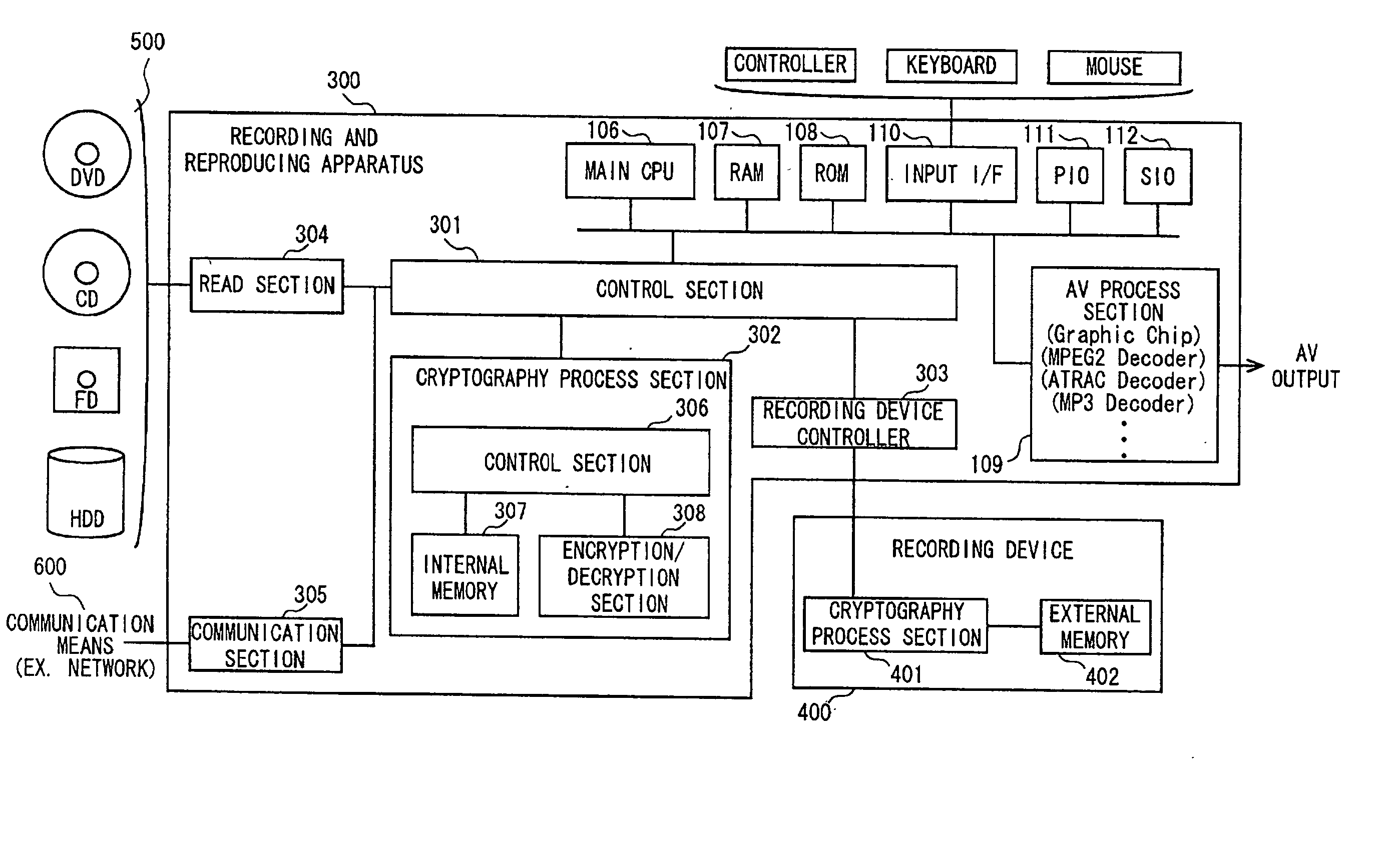
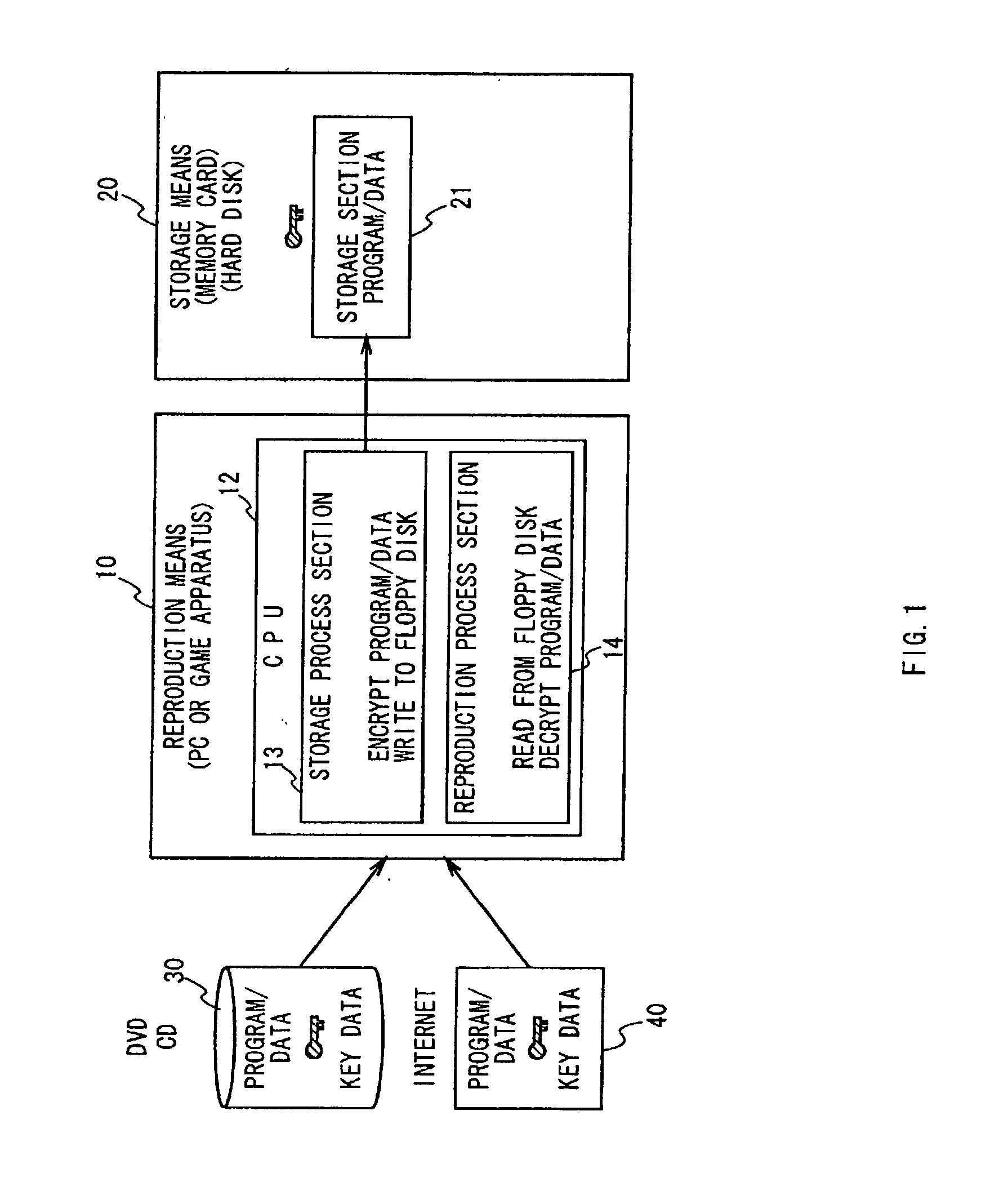
Data authentication system
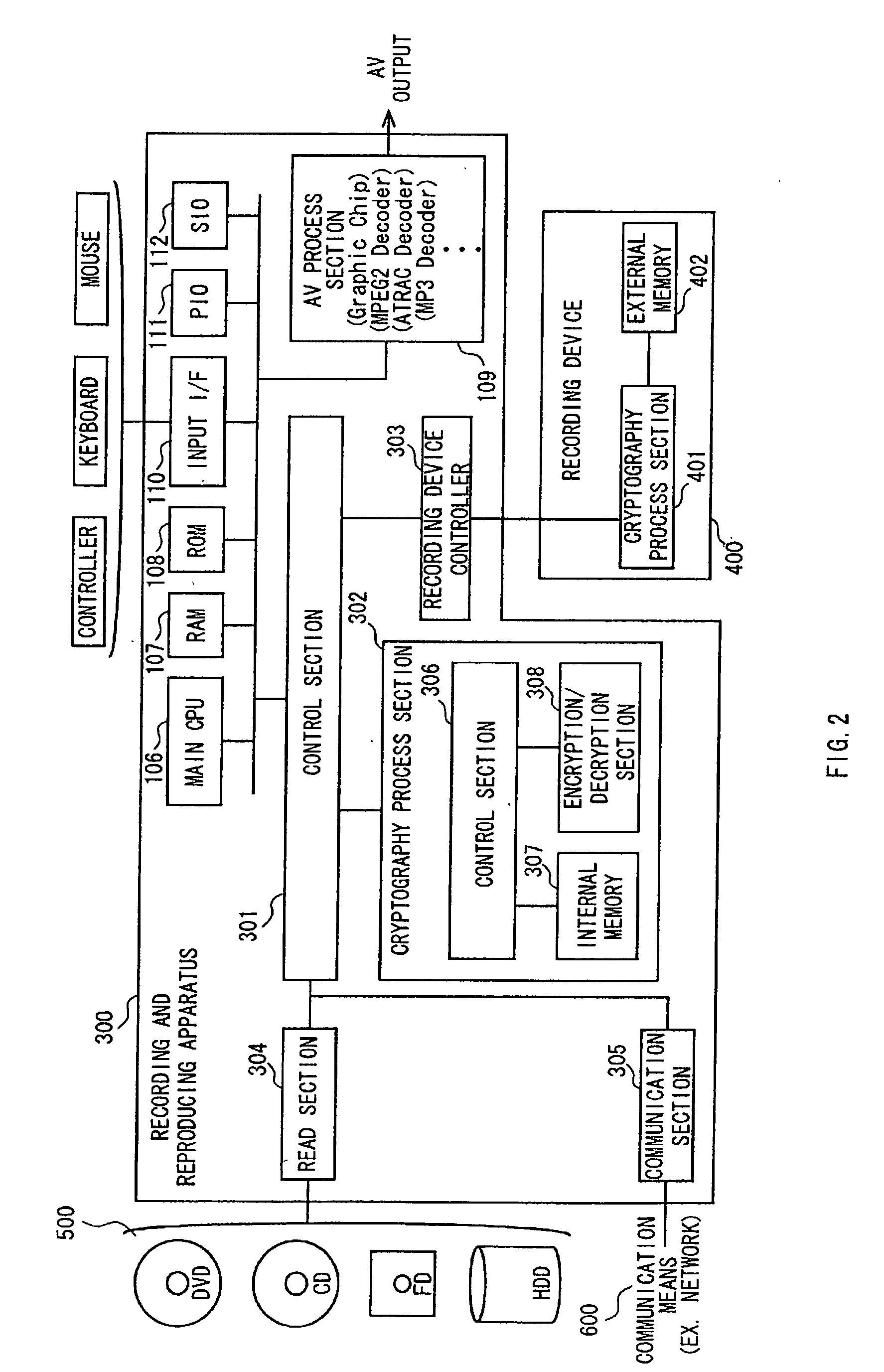
InactiveUS20020169971A1Efficient verificationPossibility of leakageTelevision system detailsMultiple keys/algorithms usageKey storageMaster key
A data processing apparatus a data processing method efficiently ascertain that data are valid, prevent encryption processing key data from leaking, eliminate illegal use of contents data, restrict contents utilization, apply a different plurality of data formats to contents and efficiently execute reproduction processing of compressed data. The verification process of partial data is executed by collating the integrity partial data as check values for a combination of partial data of a content, and the verification process of the entirety of the combination of partial data is executed by collating partial-integrity-check-value-verifying integrity check values that verify the combination of the partial integrity check values. Master keys to generate individual keys necessary for a process of such as data encryption are stored in the storage section and keys are generated as required. An illegal device list is stored in the header information of a content and referred to when data is used. Keys specific to a data processing apparatus and common keys are stored and the keys are selectively used according to the content use restriction. Plural content blocks are coupled, and at least a part of the content blocks is applied to an encryption process by an encryption key Kcon, then encryption key data that is the encryption key Kcon encrypted by an encryption key Kdis is stored in the header section. A content data is made of compression data and an expansion processing program or a combination of types of compression programs and the reproducing apparatus can determine an expansion program applicable to a compressed content.
Owner:SONY CORP
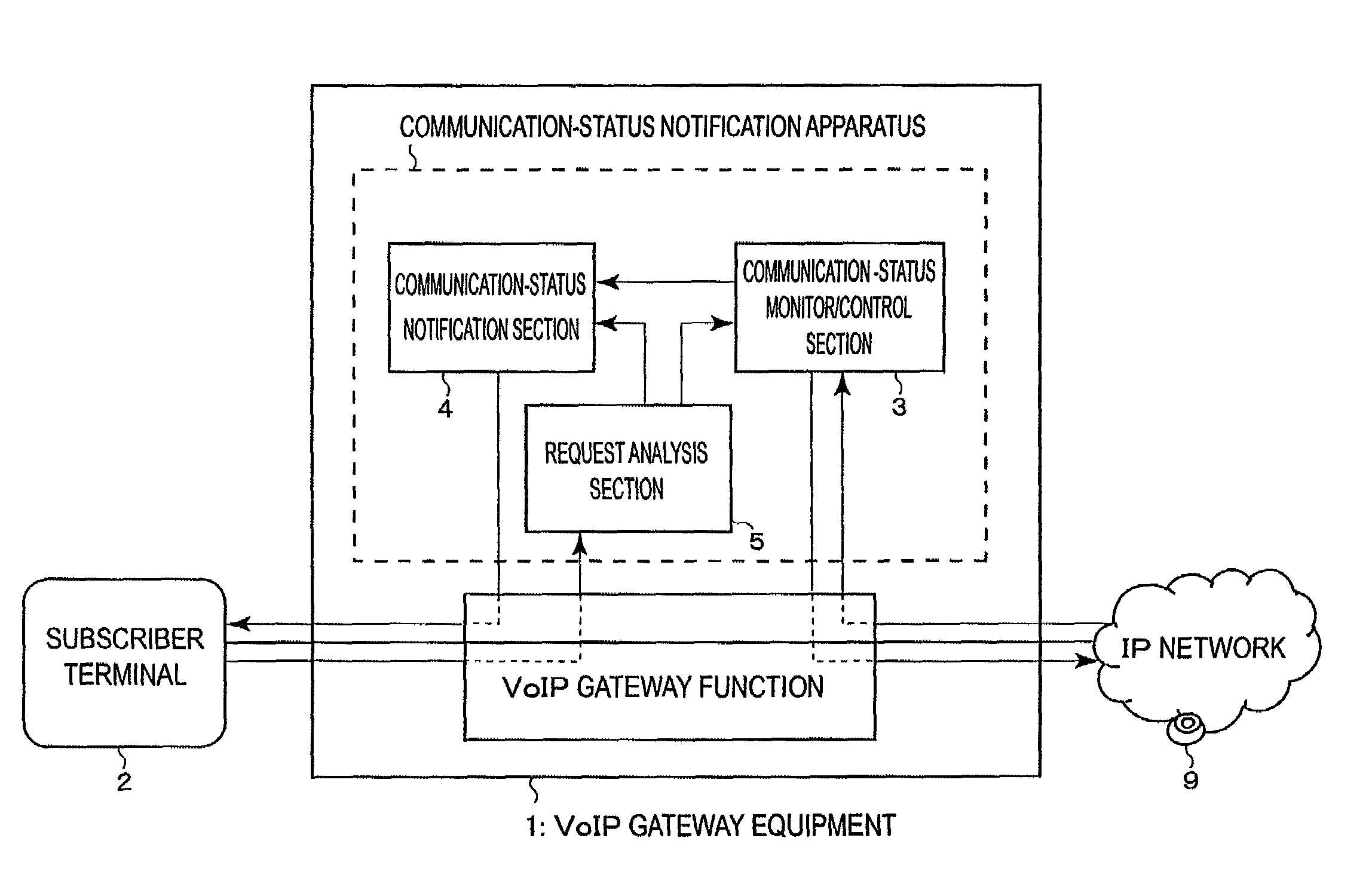
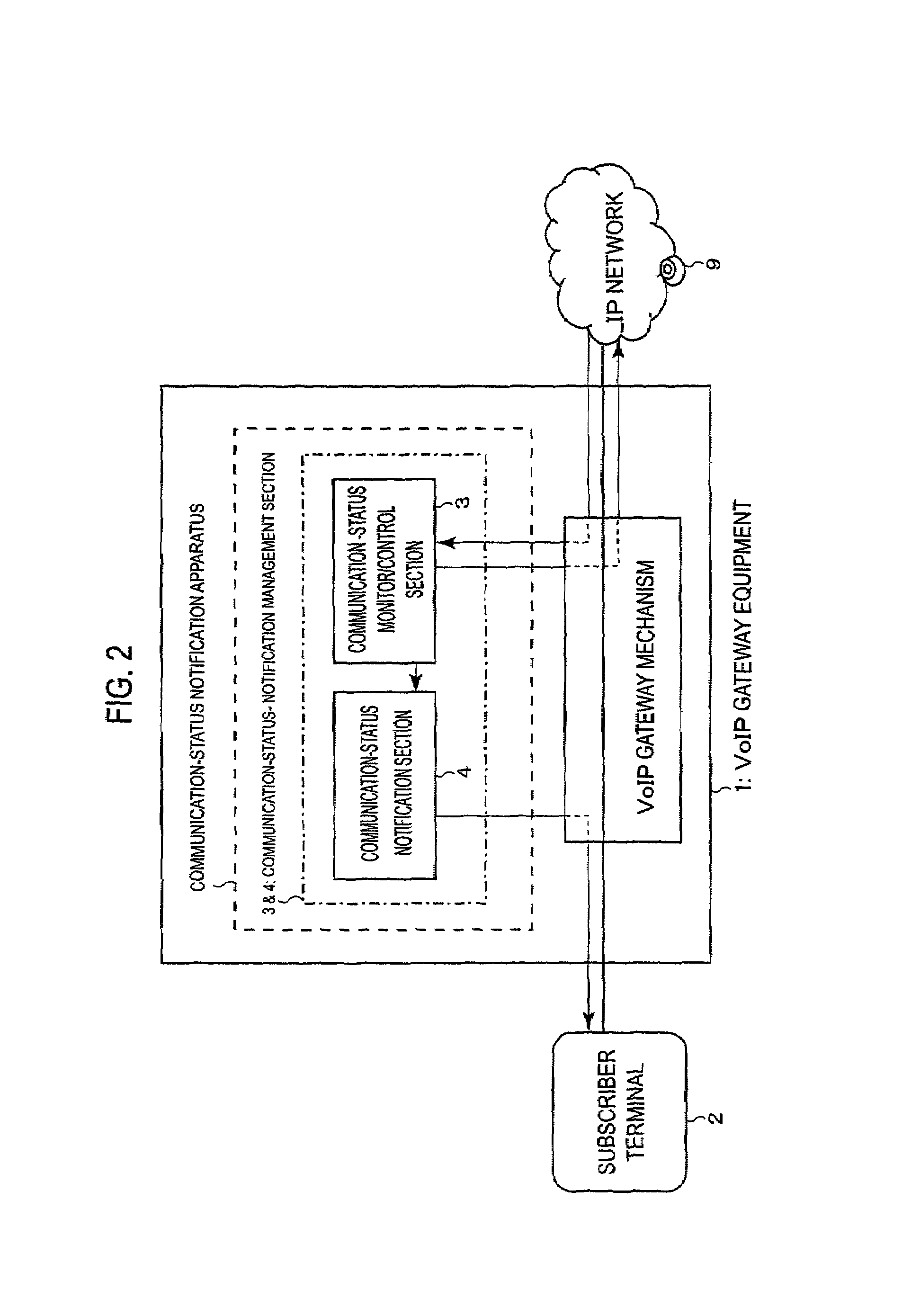
Communication-status notification apparatus for communication system, communication-status display apparatus, communication-status notification method, medium in which communication-status notification program is recorded and communication apparatus
InactiveUS6967958B2Easily via a subscriber terminalEasy to observeInterconnection arrangementsMultiple keys/algorithms usageControl communicationsSpeech sound
Owner:FUJITSU LTD
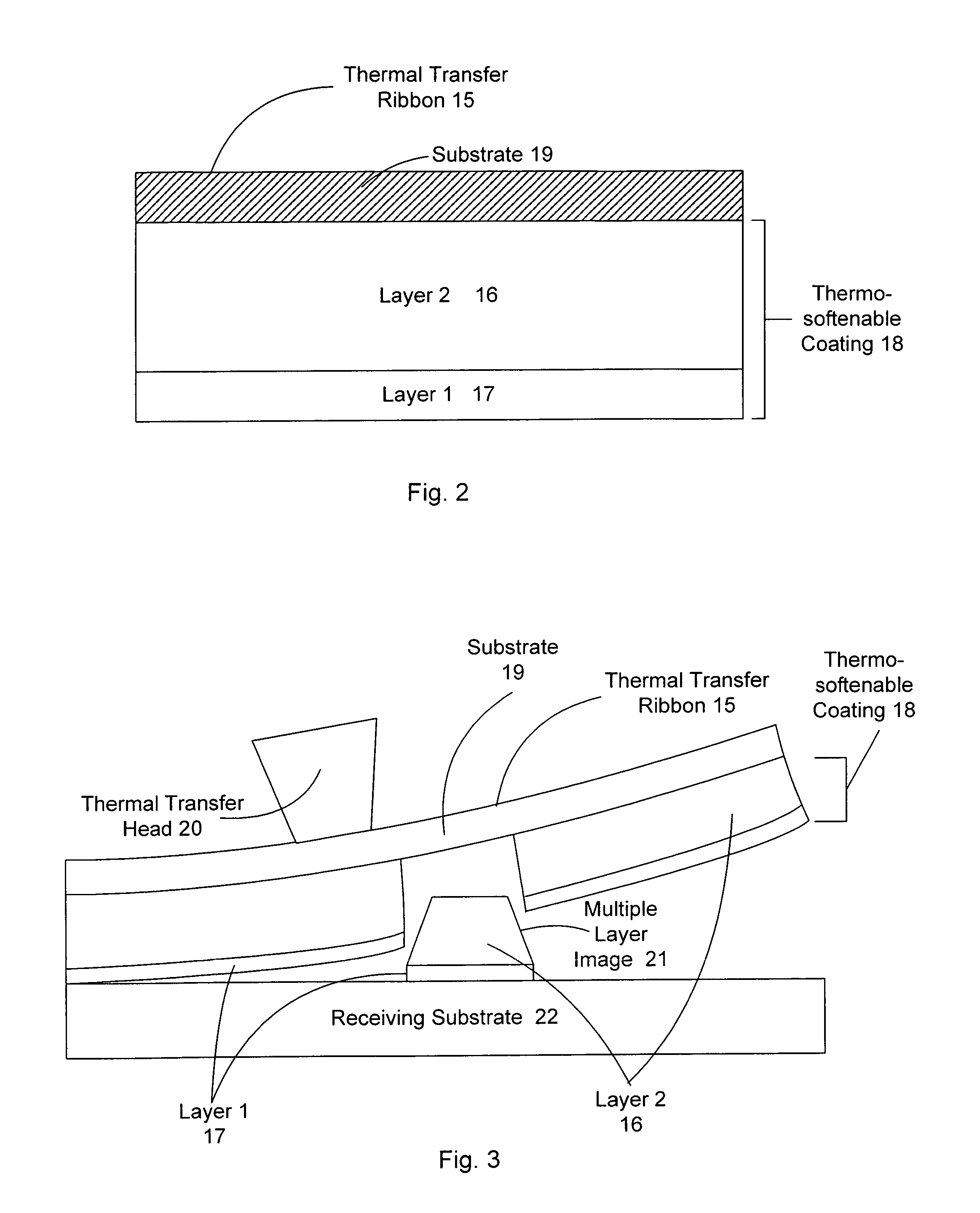
Authentication method and system
InactiveUS7089420B1Great difficultyEfficient codingOther printing matterUser identity/authority verificationComputer hardwareOptical property
The present invention provides a method and apparatus for the production and labeling of objects in a manner suitable for the prevention and detection of counterfeiting. Thus, the system incorporates a variety of features that make unauthorized reproduction difficult. In addition, the present invention provides an efficient means for the production of labels and verification of authenticity, whereby a recording apparatus which includes a recording medium, having anisotrophic optical domains, along with a means for transferring a portion of the recording medium to a carrier, wherein a bulk portion of the recording medium has macroscopically detectable anisotrophic optical properties and the detecting apparatus thereon.
Owner:COPILOT VENTURES FUND III
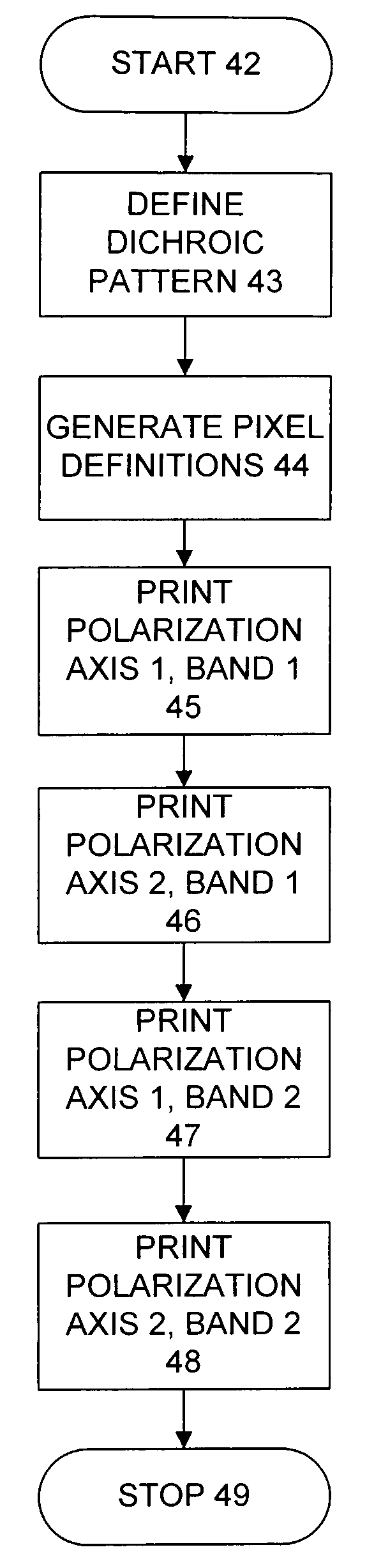
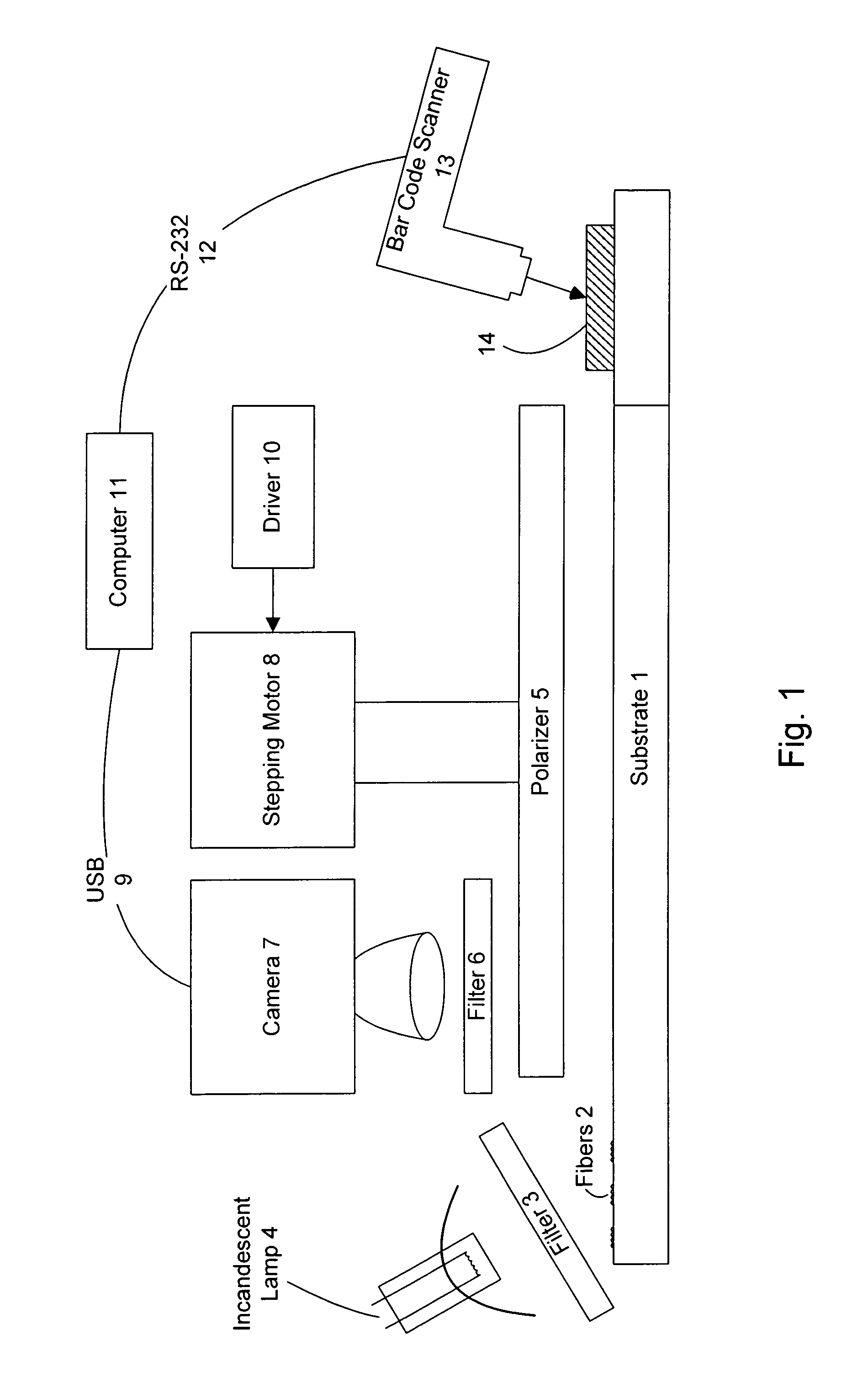
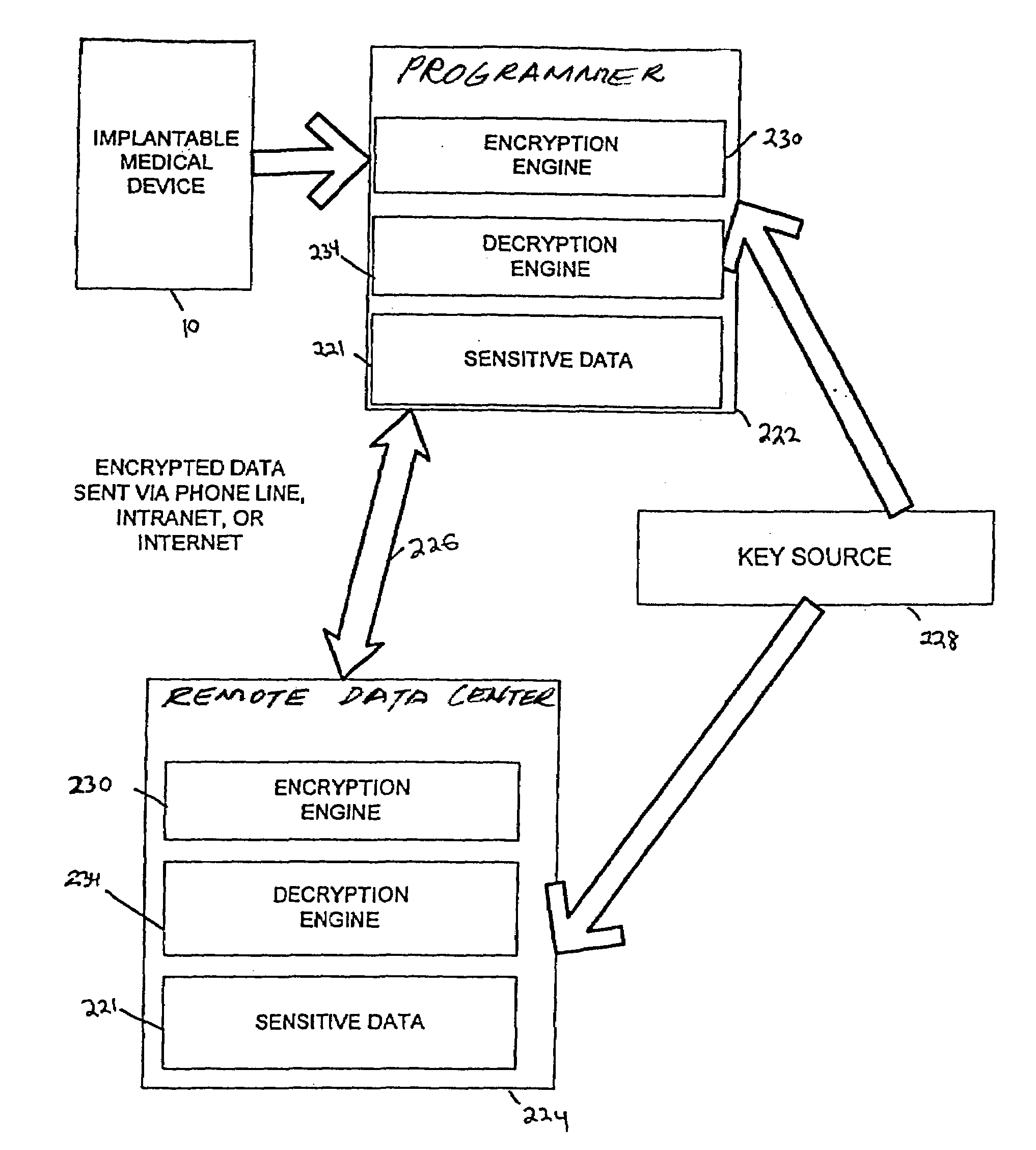
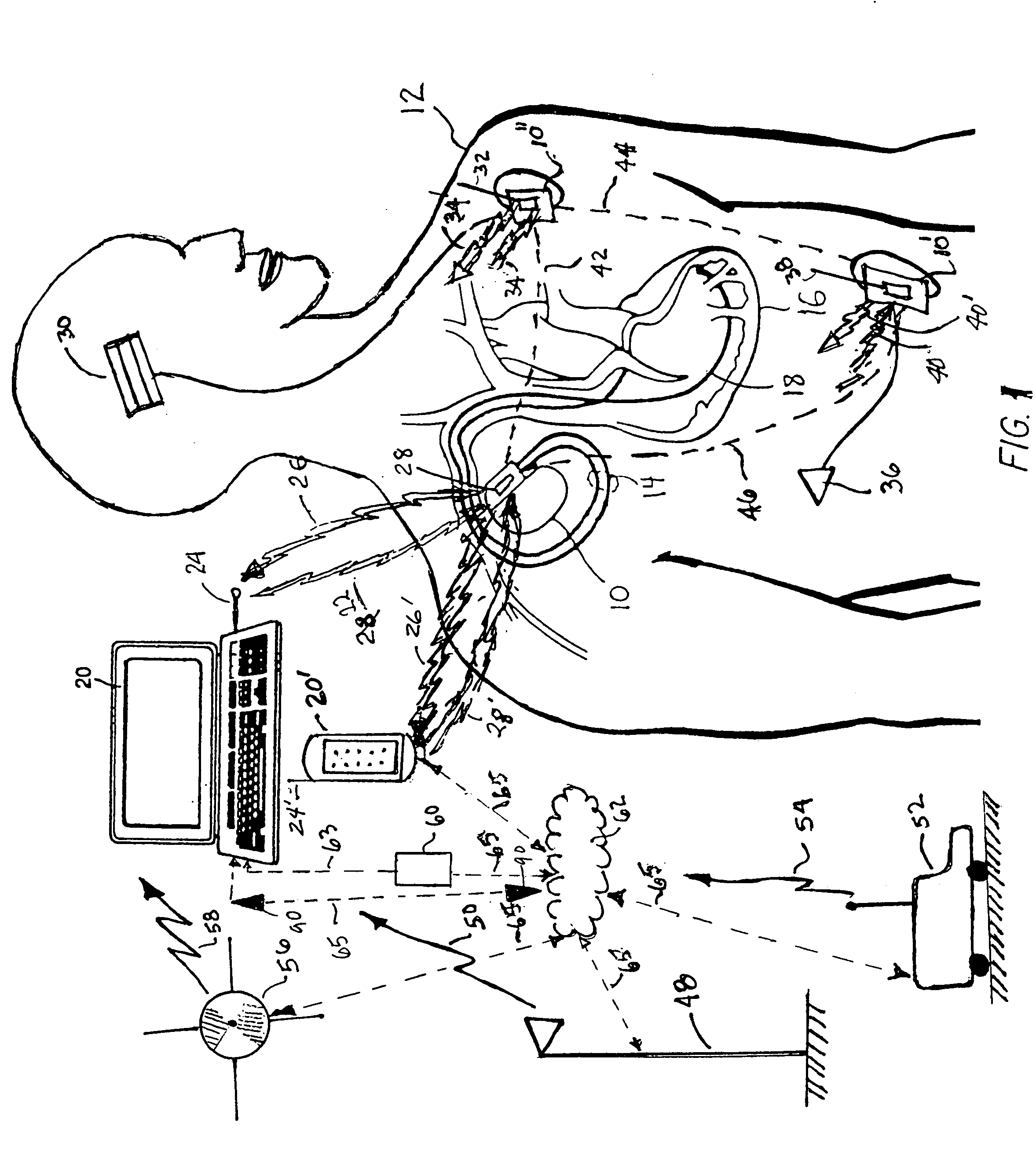
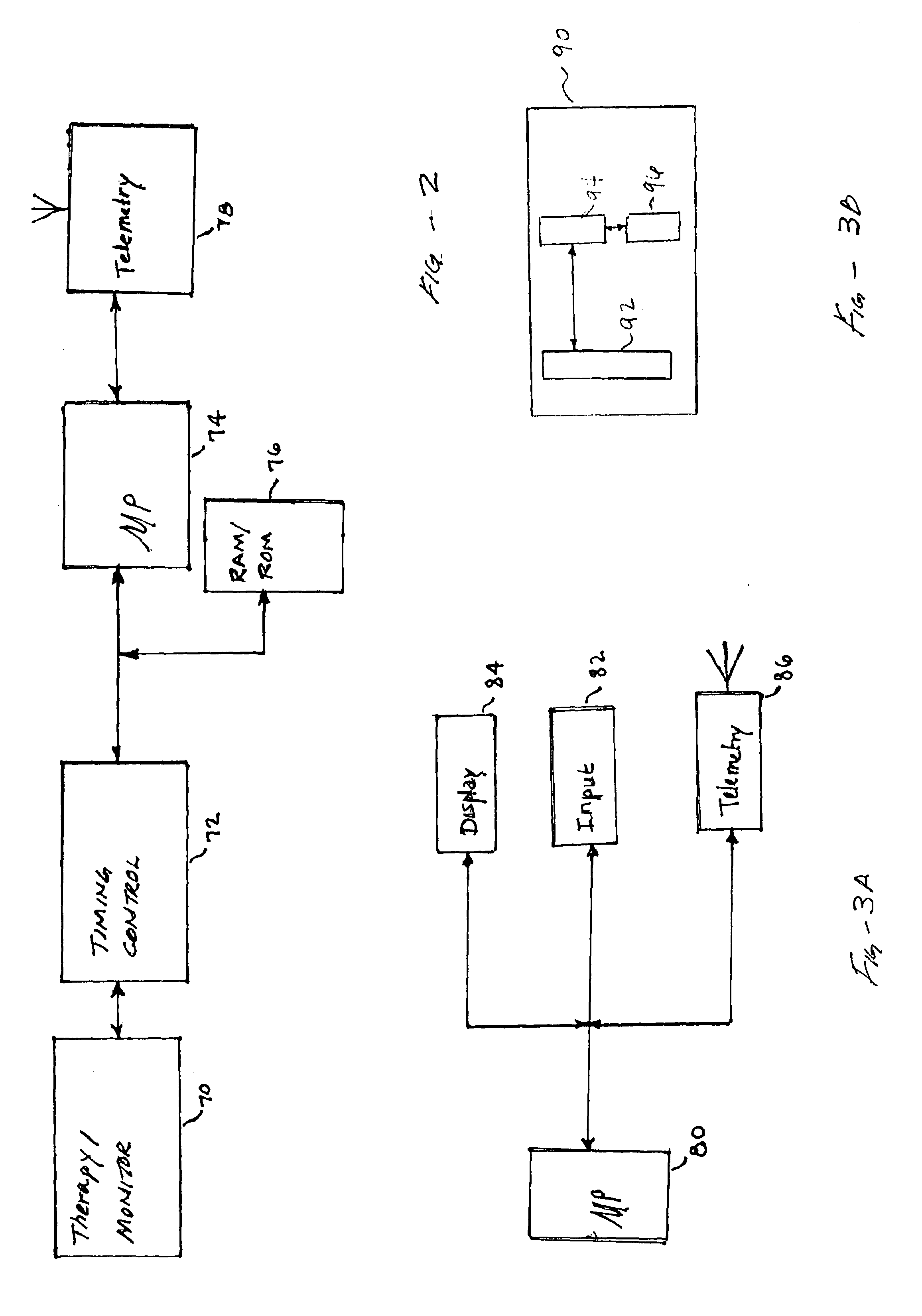
Method and apparatus to secure data transfer from medical device systems
InactiveUS7039810B1Key distribution for secure communicationElectrotherapyCommunications systemData center
Sensitive data such as patient records are securely transferred between a programmer and a data encryption. A database residing on the programmer contains patient information obtained by at least one implantable medical device. A key source provides the programmer with a first key and the remote expert data center with a second key to be used in the encryption / decryption process. An encryption engine residing within the programmer encrypts the sensitive patient information contained within the database, using the first key. The programmer transmits the encrypted patient information to the remote expert data center via a data communications system such as a public network. A decryption engine residing within the remote expert data center decrypts the encrypted sensitive patient information using the second key.
Owner:MEDTRONIC INC