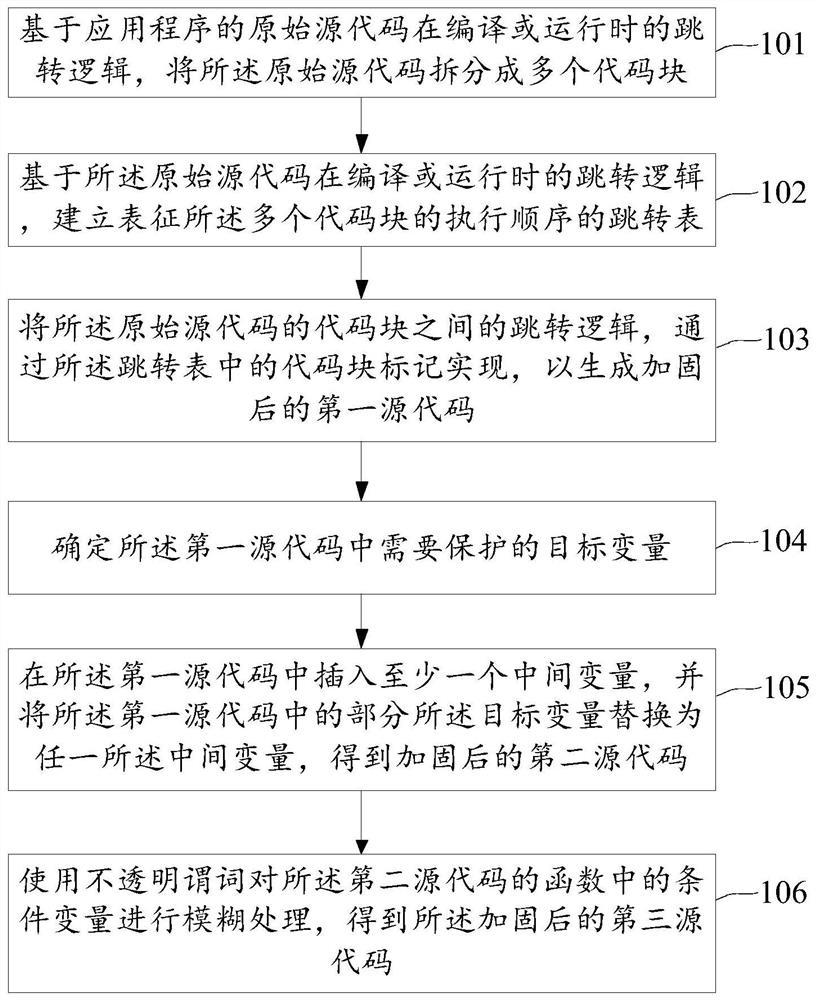
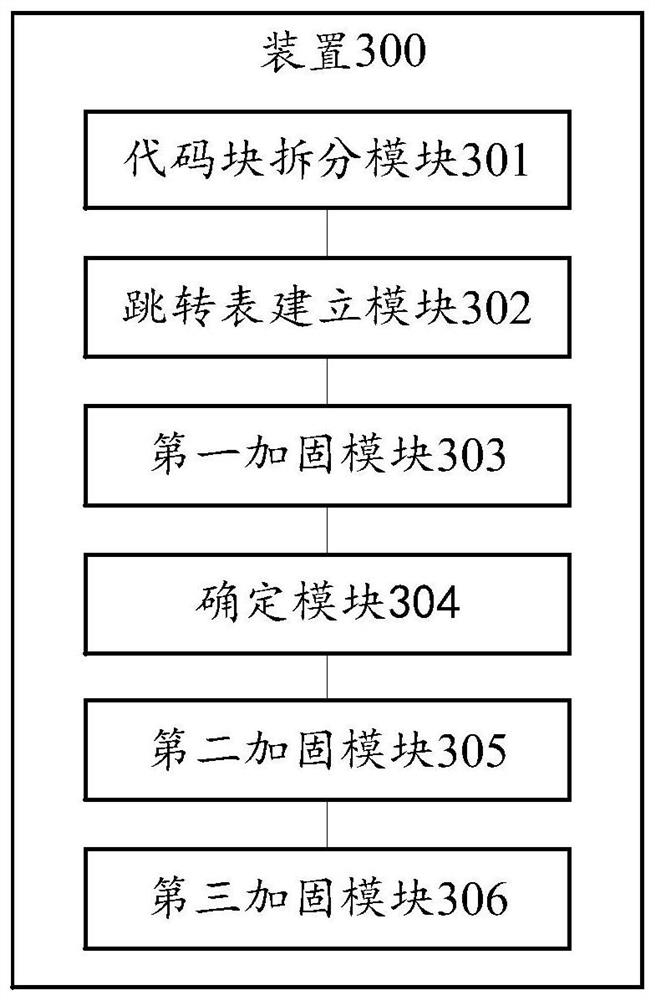
Source code hardening method and device based on sequence, symbolic execution and single-point logic
A symbolic execution and source code technology, applied in the direction of program/content distribution protection, etc., can solve the problem that the anti-reverse analysis ability of source code needs to be improved, and achieve the effect of improving the anti-reverse analysis ability and increasing the difficulty of cracking.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0029] In order to make the purpose, technical solution and advantages of the present application clearer, the technical solution of the present application will be clearly and completely described below in conjunction with specific embodiments of the present application and corresponding drawings. Apparently, the described embodiments are only some of the embodiments of the present application, rather than all the embodiments. Based on the embodiments in this application, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the scope of protection of this application.
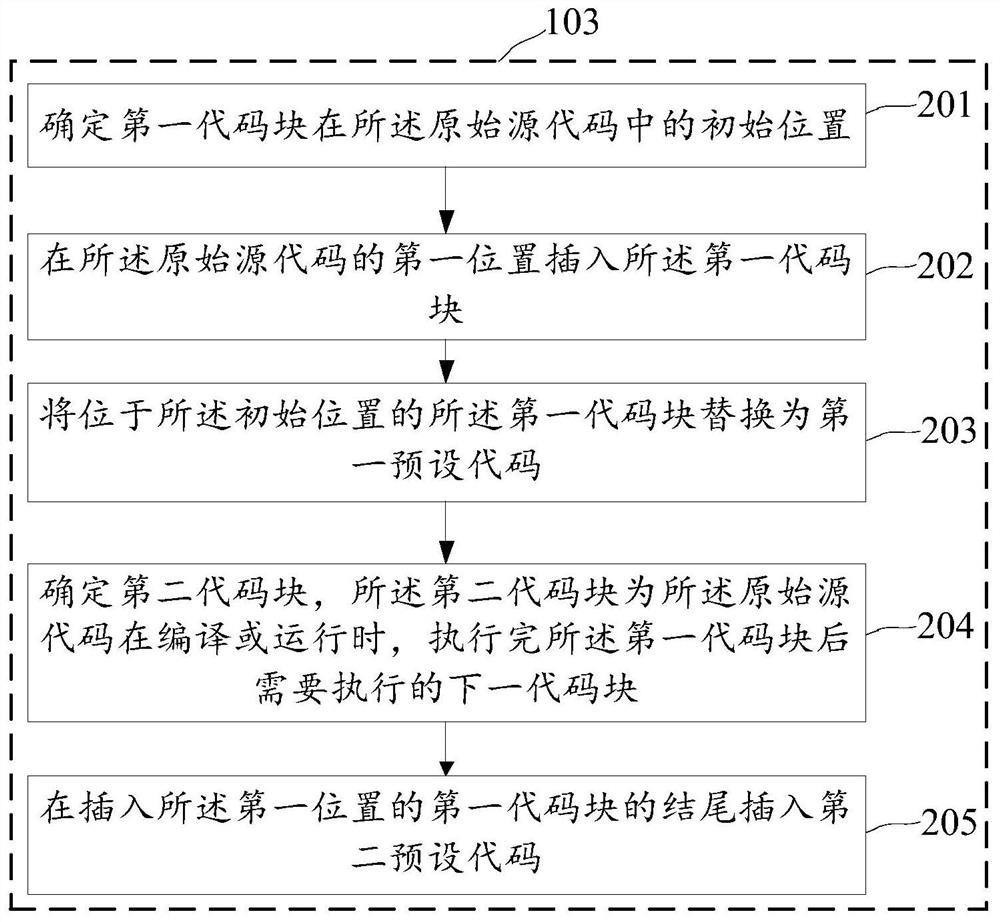
[0030] In order to improve the anti-reverse analysis capability of the source code, the embodiment of the present application provides a source code hardening method and device based on sequence, symbolic execution and single-point logic, which will be described respectively below.
[0031] It should be noted that the execution subject for implementin...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More