A network attack identification method and system
A network attack and identification method technology, which is applied in the field of network attack identification methods and systems, can solve the problem of high operation and maintenance processing costs, and achieve the effect of improving operation and maintenance efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
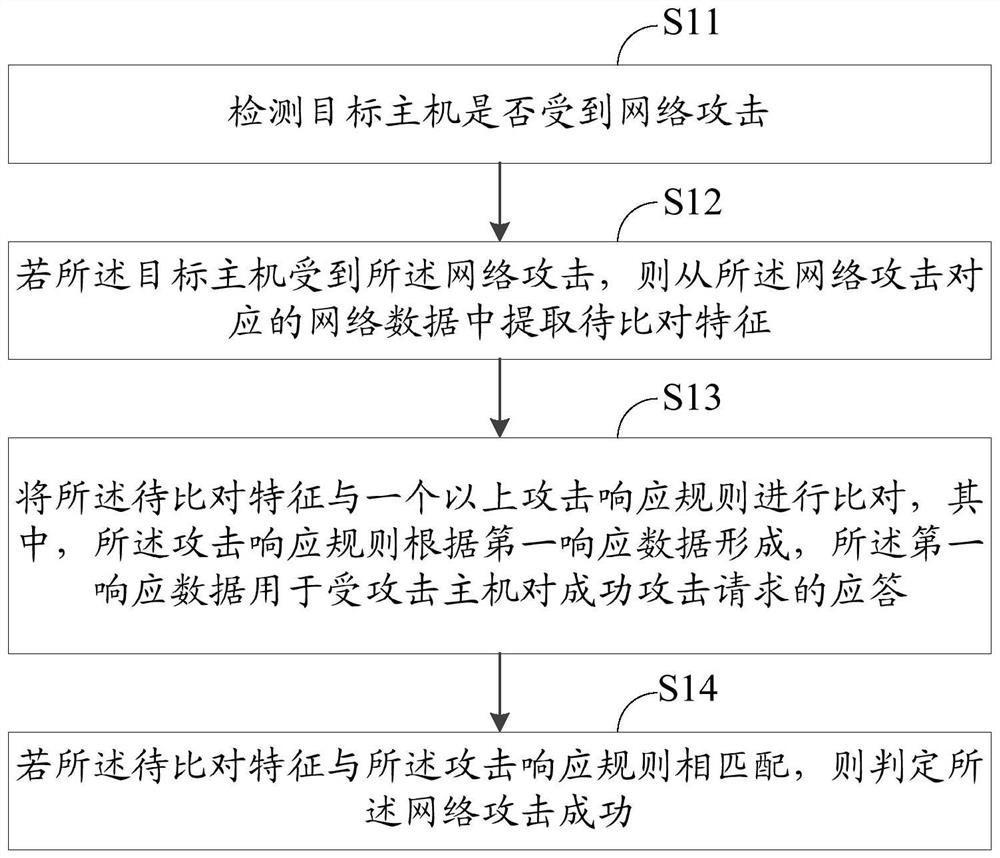
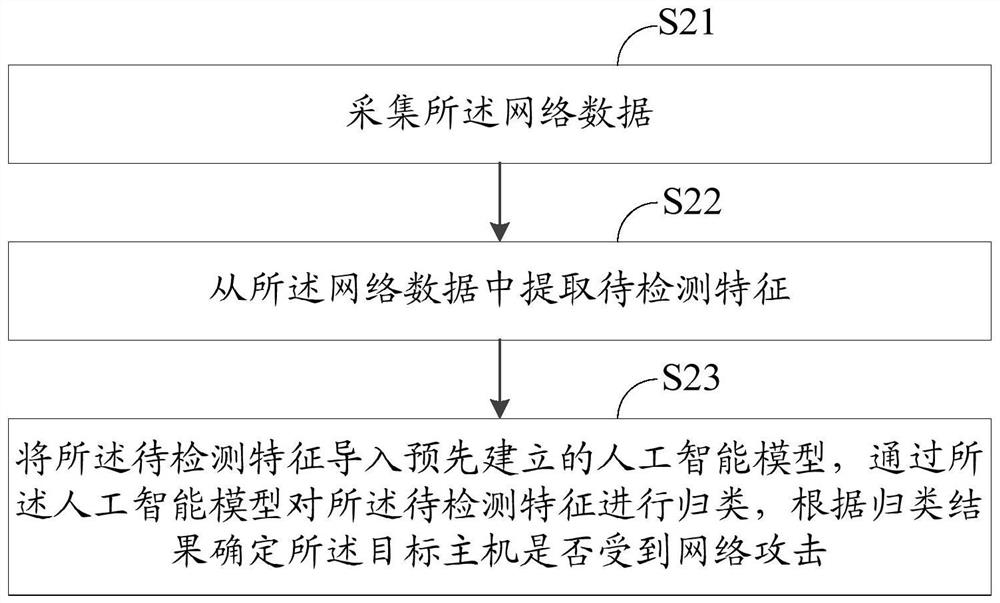
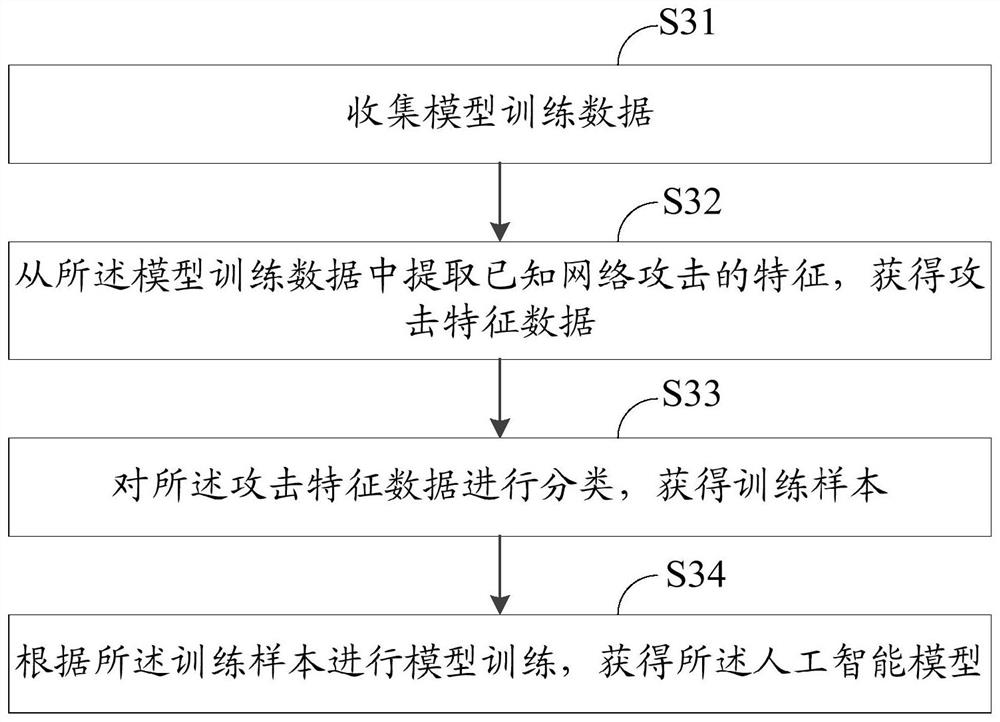
[0147] This embodiment provides a network attack identification method, figure 1 is a schematic flowchart of the network attack identification method, and the network attack identification method includes:
[0148] Step S11, detecting whether the target host is under network attack;
[0149] Step S12, if the target host is subjected to the network attack, extracting features to be compared from the network data corresponding to the network attack;
[0150] Step S13, comparing the feature to be compared with more than one attack response rule, wherein the attack response rule is formed according to the first response data, and the first response data is used for the attacked host to successfully attack the request answer;
[0151] Step S14, if the feature to be compared matches the attack response rule, it is determined that the network attack is successful.
[0152] The target host may be a server providing various services, a personal computer capable of realizing specific...
Embodiment 2
[0191] This embodiment provides another method for identifying a network attack. Compared with the method for identifying a network attack provided in Embodiment 1, after comparing the features to be compared with more than one attack response rule, an alarm message may also be generated, Wherein, the alarm information includes the attack type of the network attack, whether the network attack is successful, and the attack action of the successful network attack. For example, when the target host is attacked by SQL injection but the attack is unsuccessful, the alarm information can be "under SQL injection attack, the attack is invalid"; when the target host is attacked by SQL injection and the attack is successful, the specific attack action It uses the floor() function to report an error injection, and the alarm information can be "under SQL injection attack, the attack is successful, and the floor() function reports an error injection".
[0192]Further, after the alarm inform...
Embodiment 3
[0195] Embodiment 2 adopts a warning method in which one network attack corresponds to one warning message, that is, a corresponding warning message is generated when a network attack is detected. However, isolated alarm information cannot accurately reflect the security status of the target host, and this kind of attack display cannot grasp the attack process as a whole. Therefore, this embodiment provides another network attack identification method. Compared with the network attack identification method provided in Embodiment 2, after the alarm information is generated, this embodiment further includes:
[0196] Add a corresponding attack chain label to the alarm information according to the alarm content of the alarm information, where the attack chain label is used to represent the attack stage of the network attack in the attack chain;
[0197] Count each attack chain label of the same attack event, and obtain the total number of network attacks, the number of successfu...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More