Container isolation enhancement system based on ARM TrustZone
A technology that enhances the system and isolation, applied in the field of virtualization, can solve the problem of no description or report found, no data collected, etc., to achieve the effect of protecting user privacy
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
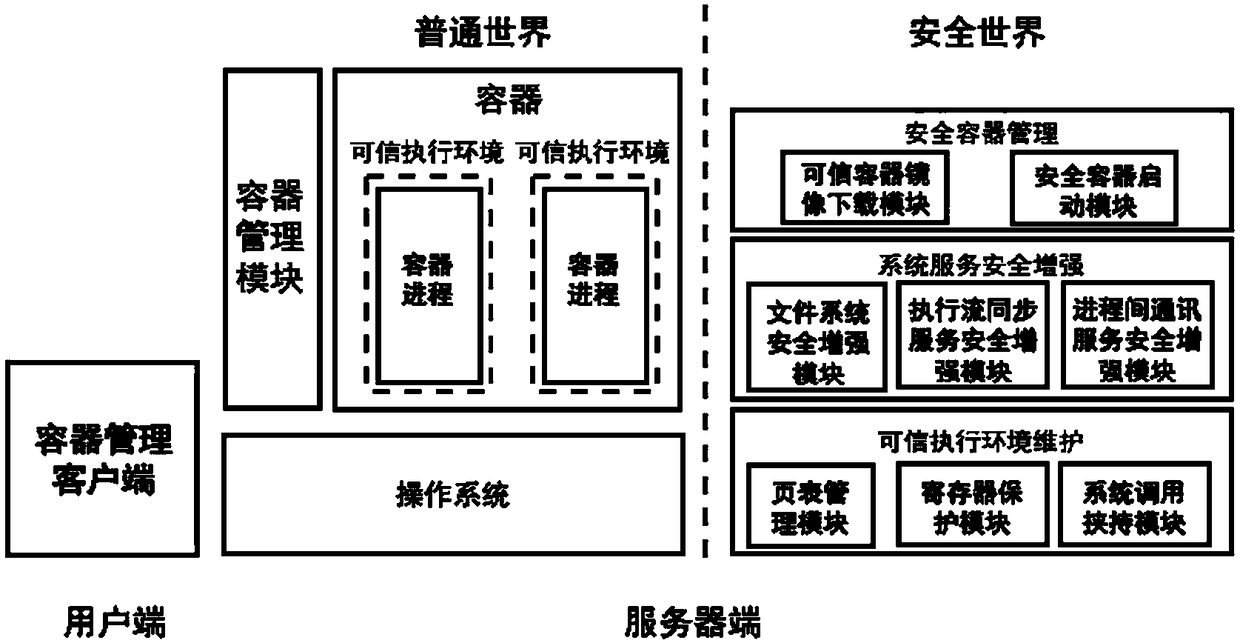
[0072] This embodiment provides a container isolation enhancement system based on ARM TrustZone, which can effectively solve the problems encountered in the prior art, including:
[0073] How to use the characteristics of the ARM platform's own architecture to maintain any number of trusted execution environments for containers? ARM's TrustZone hardware technology only provides a single trusted execution environment called "secure world". However, simply running different container applications in a "secure world" cannot improve the security between containers. Therefore, how to take advantage of the "secure world" and provide each container process with an exclusive trusted execution environment is very important.
[0074] How to prevent container applications from being attacked while relying on untrusted operating systems to provide services? Applications (including applications in containers) rely on system calls provided by the operating system to complete many function...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More