Third-party-based verified information non-leakage data integrity and source verification method
A technology of data integrity and verification method, applied in user identity/authority verification, digital transmission system, secure communication device, etc., can solve problems such as difficulties, and achieve the effect of ensuring security and safe data transmission
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
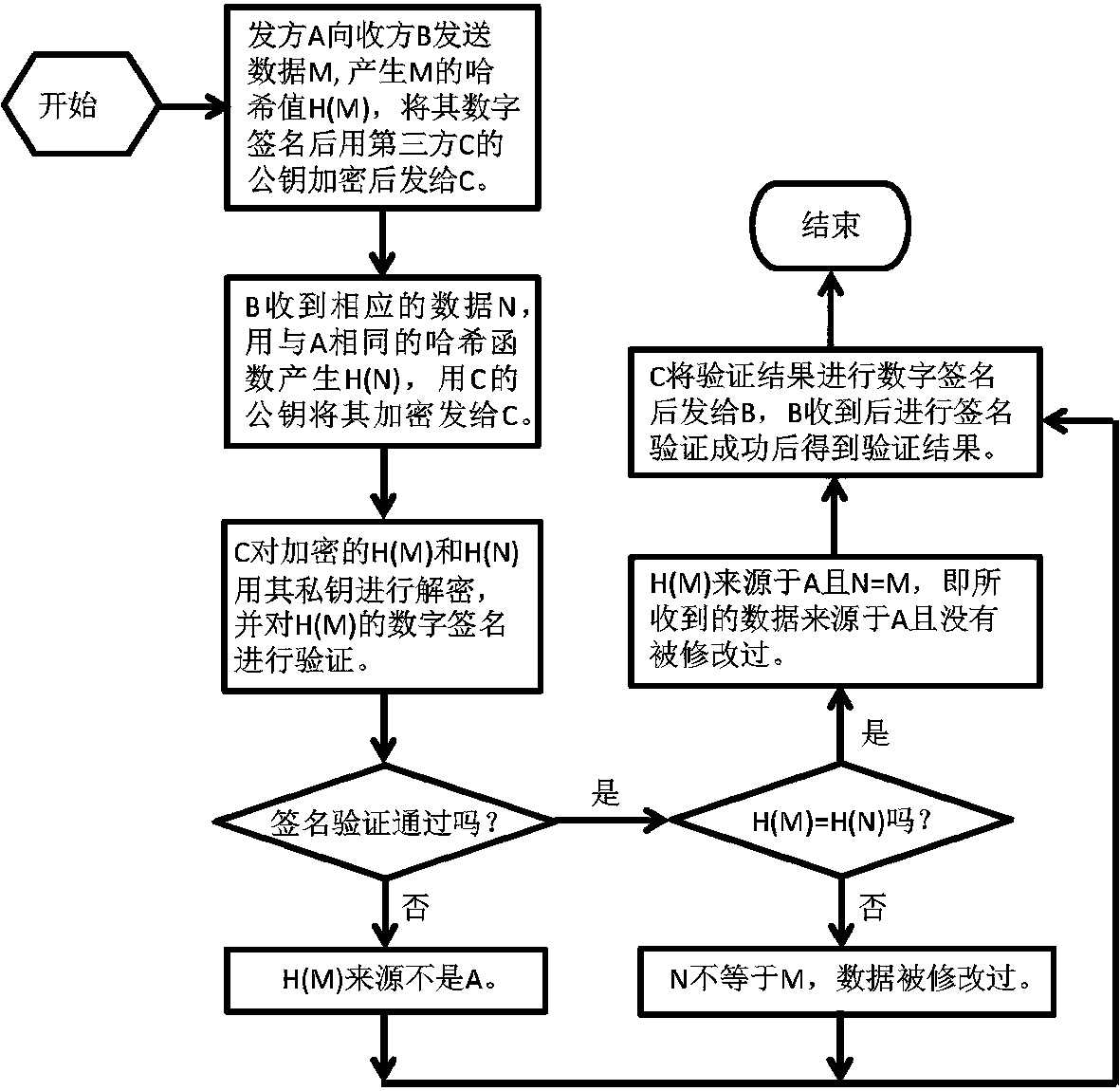
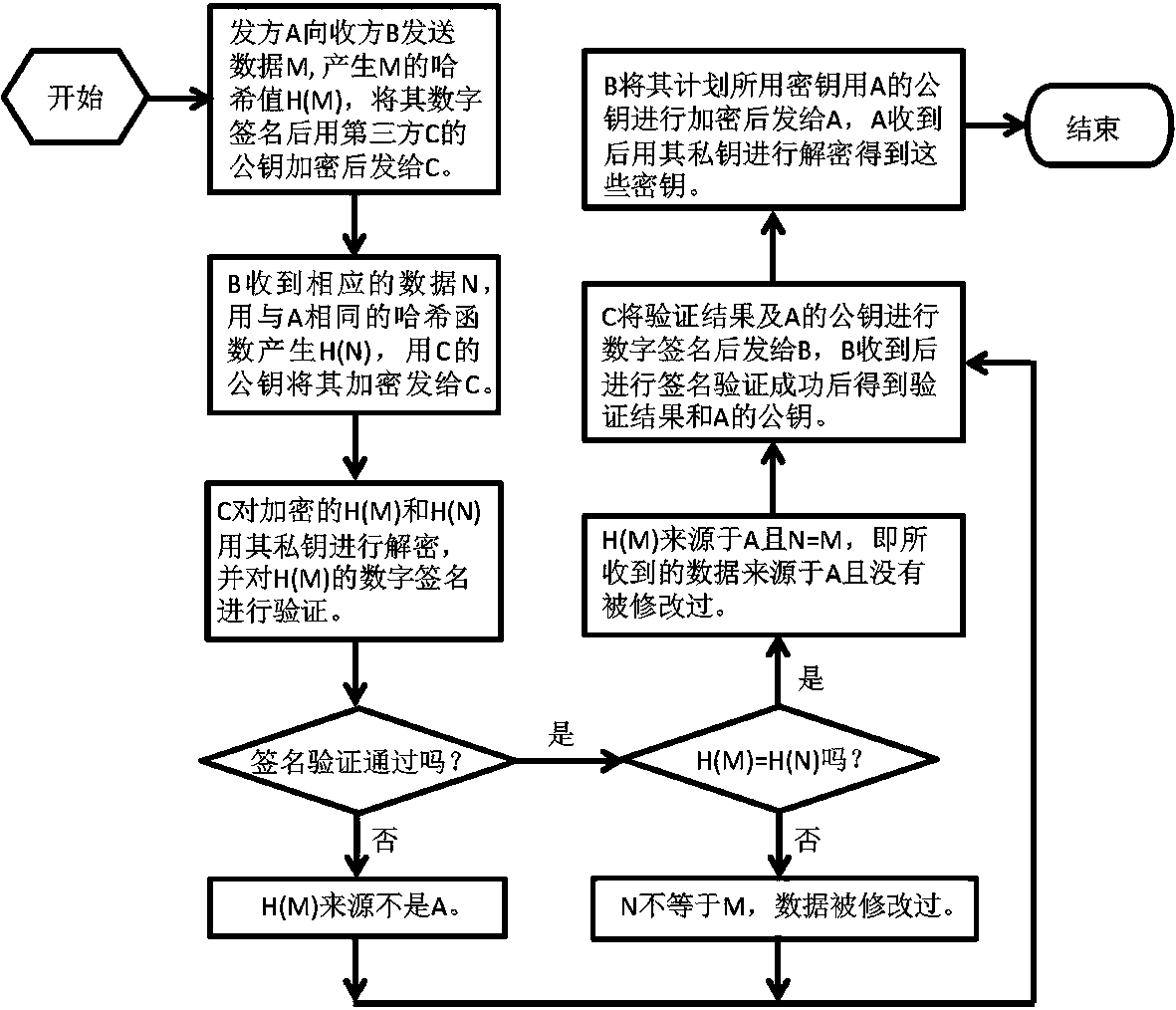
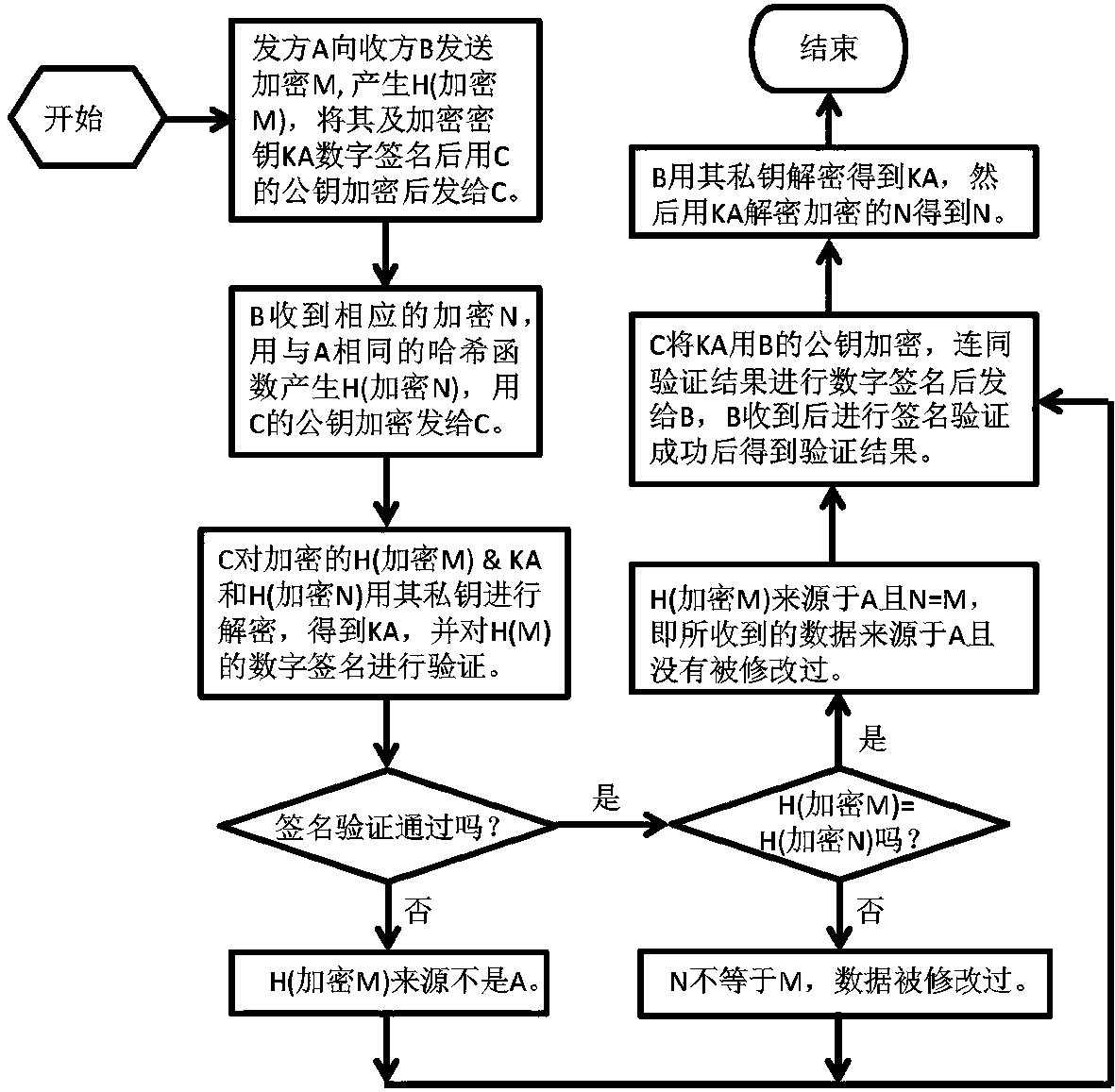
[0017] Use below Figure 1-3 , the present invention will be described in detail in conjunction with specific embodiments. The following examples will help those skilled in the art to further understand the present invention, but do not limit the present invention in any form. It should be noted that those skilled in the art can make several modifications and improvements without departing from the concept of the present invention. These all belong to the protection scope of the present invention.
[0018] The verification method of the present invention based on the fact that the third party does not disclose the integrity and source of the verified information data includes:
[0019] Based on the verification method that the third party does not disclose the data integrity of the verified information and the source of the simple mode, the data used for verification and transmission is in plain text, and the sender does not encrypt it, and the receiver does not need to decr...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More