A method for homology analysis of malicious code based on cross-process behavior monitoring
A technology of homology analysis and malicious code, which is applied in the field of homology analysis of malicious code based on cross-process behavior monitoring, can solve the problems of decreased detection accuracy, low code coverage, and undetectability, and achieve the goal of reducing the number of logs Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
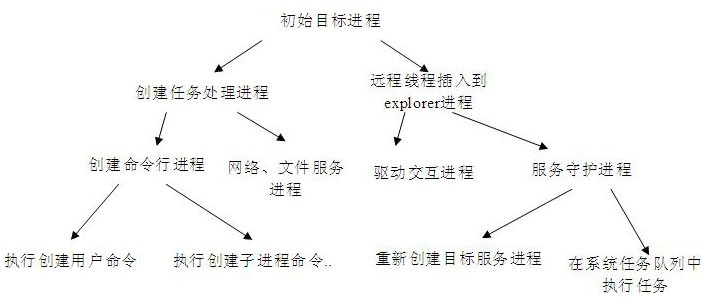
[0029] By adopting the technical solution proposed by the present invention, an efficient, low-memory, method for homology analysis of malicious codes based on cross-process behavior monitoring can be realized. The present invention proposes a method for homology analysis of malicious code based on cross-process behavior monitoring. Figure 1-4 Describe in detail.
[0030] Such as figure 1 As shown, create a target process relationship tree, the target process relationship tree includes the target process and the child process of the target process, the association relationship of the grandson process, the target process, the child process, the grandson process Perform relationship tree monitoring. figure 1 It is a tree structure composed of the target process and its children and grandchildren processes created during the execution of an attack code. Wherein, the process relationship tree further includes an association relationship of the processes that execute code behav...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More