Hybrid encryption method for instant messaging
A hybrid encryption and communication technology, applied in the usage of multiple keys/algorithms, digital transmission systems, electrical components, etc., can solve problems such as corporate and personal losses, business security threats, etc., to improve efficiency, flexibility, and improve safety effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
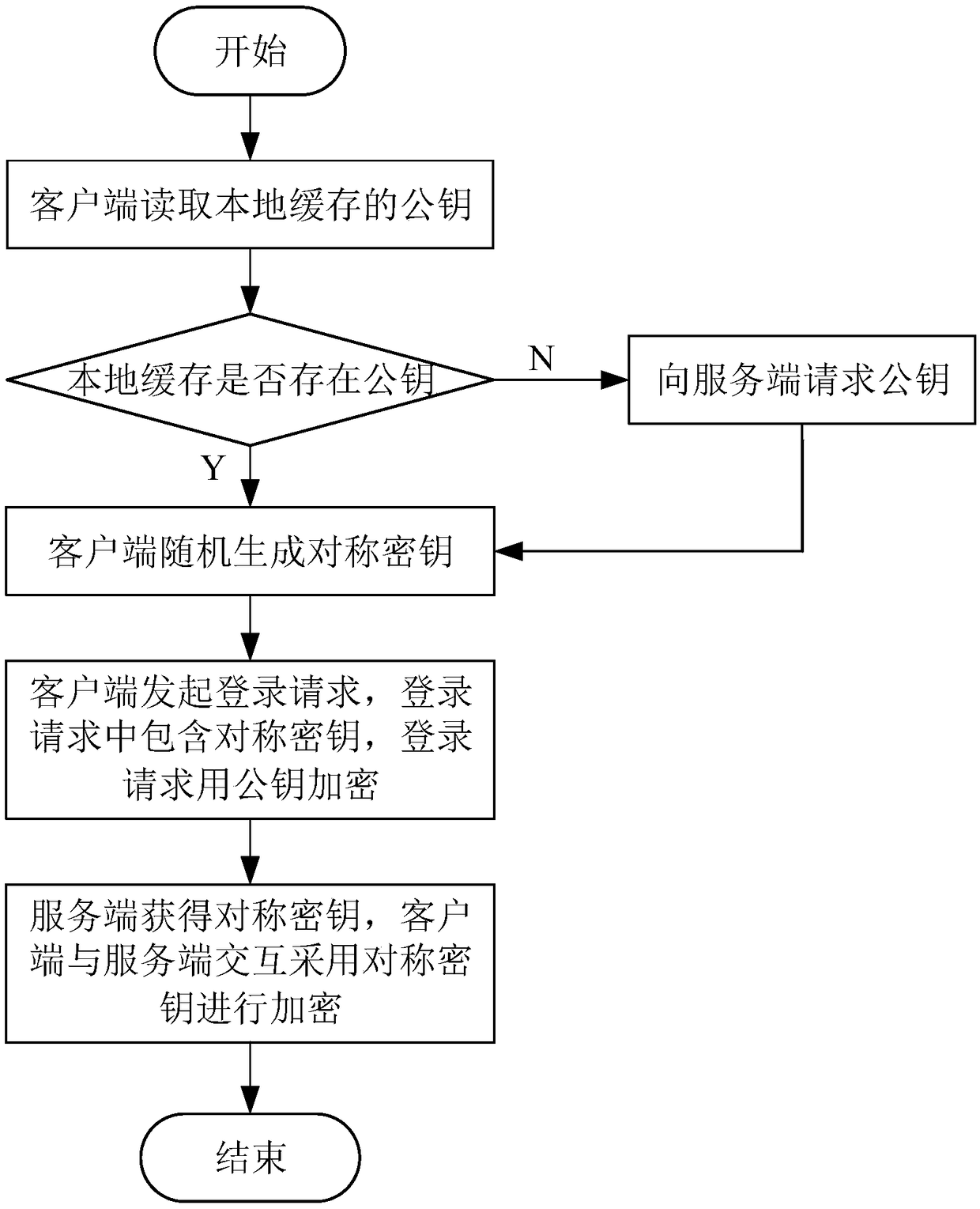
[0023] Such as figure 1 As shown, a hybrid encryption method for instant messaging, the method includes the following steps:
[0024] (1) The client obtains an asymmetric encryption public key and randomly generates a symmetric encryption key;
[0025] (2) The client sends a login request to the server, the login request includes a symmetric encryption key randomly generated by the client, and the login request is asymmetrically encrypted by an asymmetric encryption public key and then sent to the server;
[0026] (3) After the server accepts the login request and completes the login, it obtains the symmetric encryption key sent by the client;
[0027] (4) After the login is completed, all interaction requests between the client and the server are symmetrically encrypted using a symmetric encryption key.
[0028] In step (1), the asymmetric encryption key is obtained in the following way: the client reads the asymmetric encryption public key in the local cache. If the asymme...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More