Uplink and downlink decoupling single access method in heterogeneous network based on contract theory
A heterogeneous network, single-access technology, applied in access restriction, advanced technology, electrical components, etc., can solve the problem of lack of channel state information in base stations, achieve efficient user access and resource allocation, and meet the effect of feasibility
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0052] The present invention will be further described below in conjunction with the accompanying drawings.
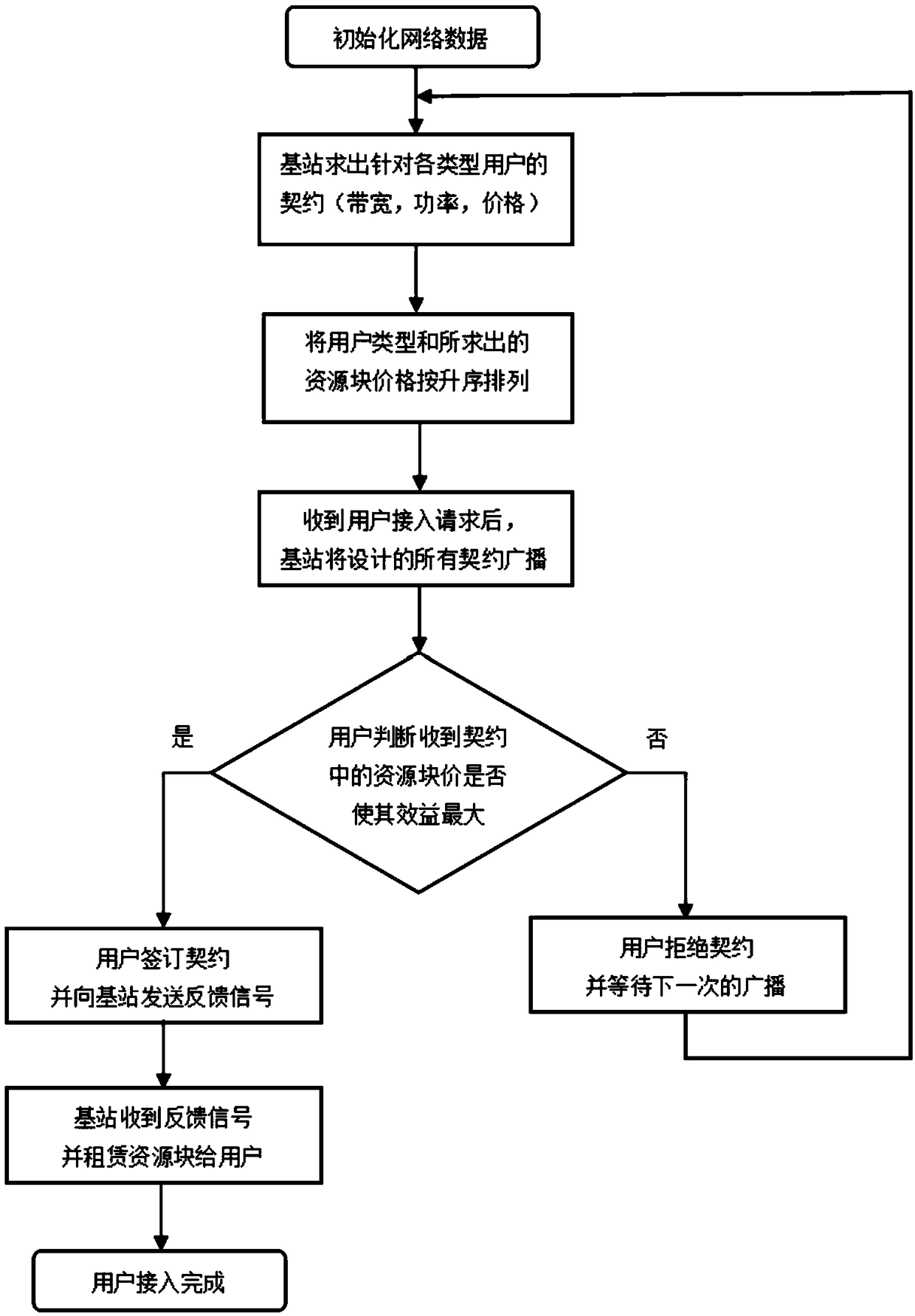
[0053] figure 1 It is a flowchart of the present invention, and the present invention mainly comprises the following parts:
[0054] 1) Contract design. In the heterogeneous network considered, the base station calculates the uplink and downlink node interference and user types according to the initialized network data, and proposes the optimization problem of the contract in a targeted manner. Under the constraints of individual rationality and incentive compatibility, the optimal resource pricing.
[0055] 2) Contract broadcast. The base station arranges the users in ascending order according to the user type information it has acquired. At the same time, arrange the designed contracts in ascending order of resource prices, and then broadcast them.
[0056] 3) The contract is signed. After the user receives the contract, according to the resource block price an...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More