A method for secure authentication of payment based on two-dimensional codes
An authentication method and payment security technology, applied in the field of network payment applications, can solve problems such as potential safety hazards, two-dimensional code payment theft, etc., and achieve the effect of improving security and facilitating use
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
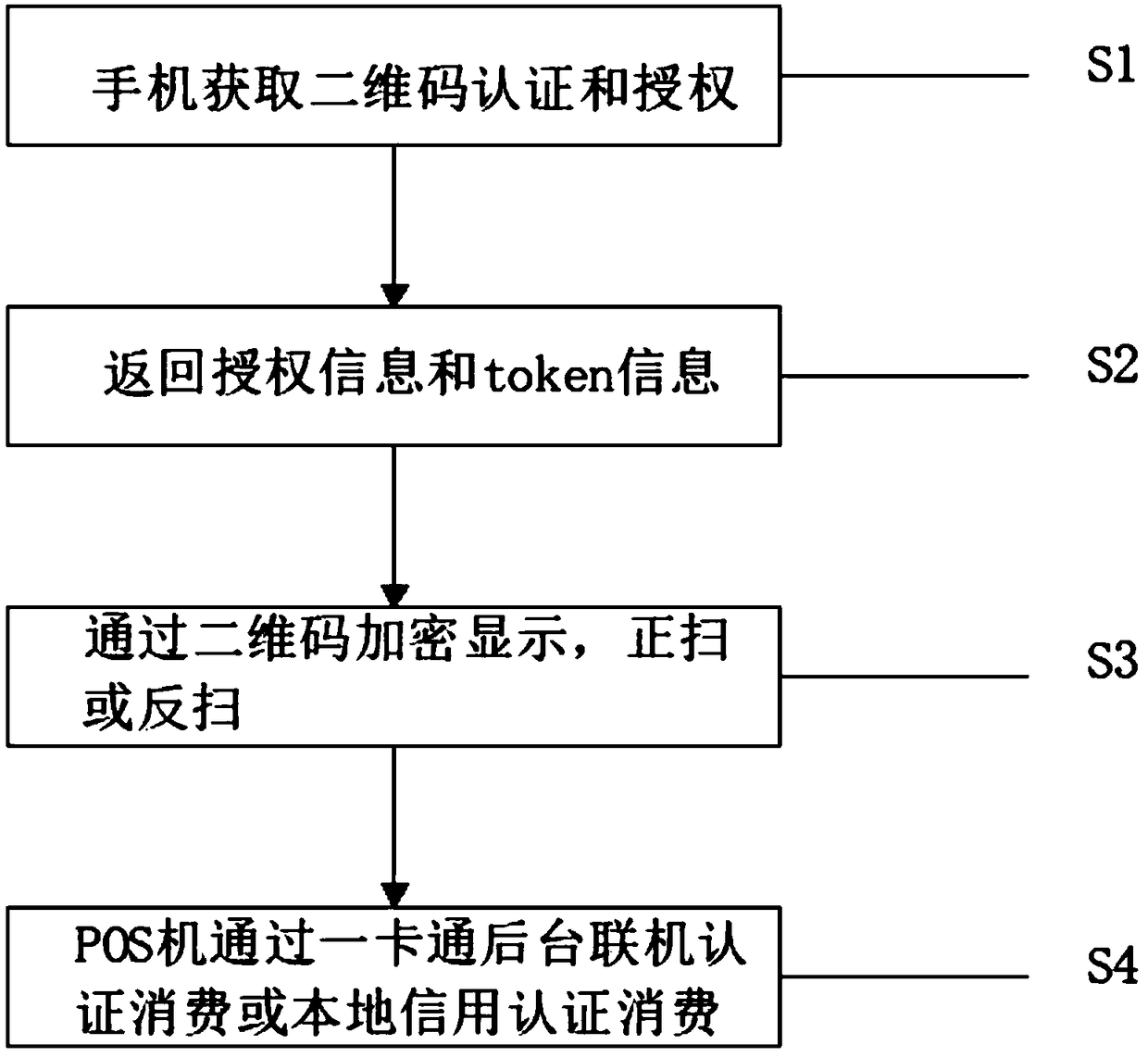
[0018] A payment security authentication method based on a two-dimensional code, comprising the following steps:
[0019] S1. Mobile phone QR code authentication and authorization;
[0020] S2. Return authorization information and token information;
[0021] S3. Encrypted display through the QR code, scan forward or reverse;
[0022] S4. The POS machine authenticates consumption or local credit through the backstage of the one-card.
[0023] In S1, the mobile phone QR code authentication and authorization is based on the mobile phone cloud receiving the QR code information sent by the mobile phone, and comparing and checking the QR code cloud to determine the accuracy of the QR code.
[0024] In S2, the authorization information is returned after checking the QR code information on the mobile phone cloud, and the token information is after the authorization information.
[0025] In S3, the two-dimensional code encryption display is based on the symmetric algorithm and the a...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com