Method and system for protecting safety of dual-system shared memory data
A shared memory and data security technology, applied in the field of data interaction, can solve problems such as data leakage and lack of data security, and achieve the effect of protecting security and preventing data leakage
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
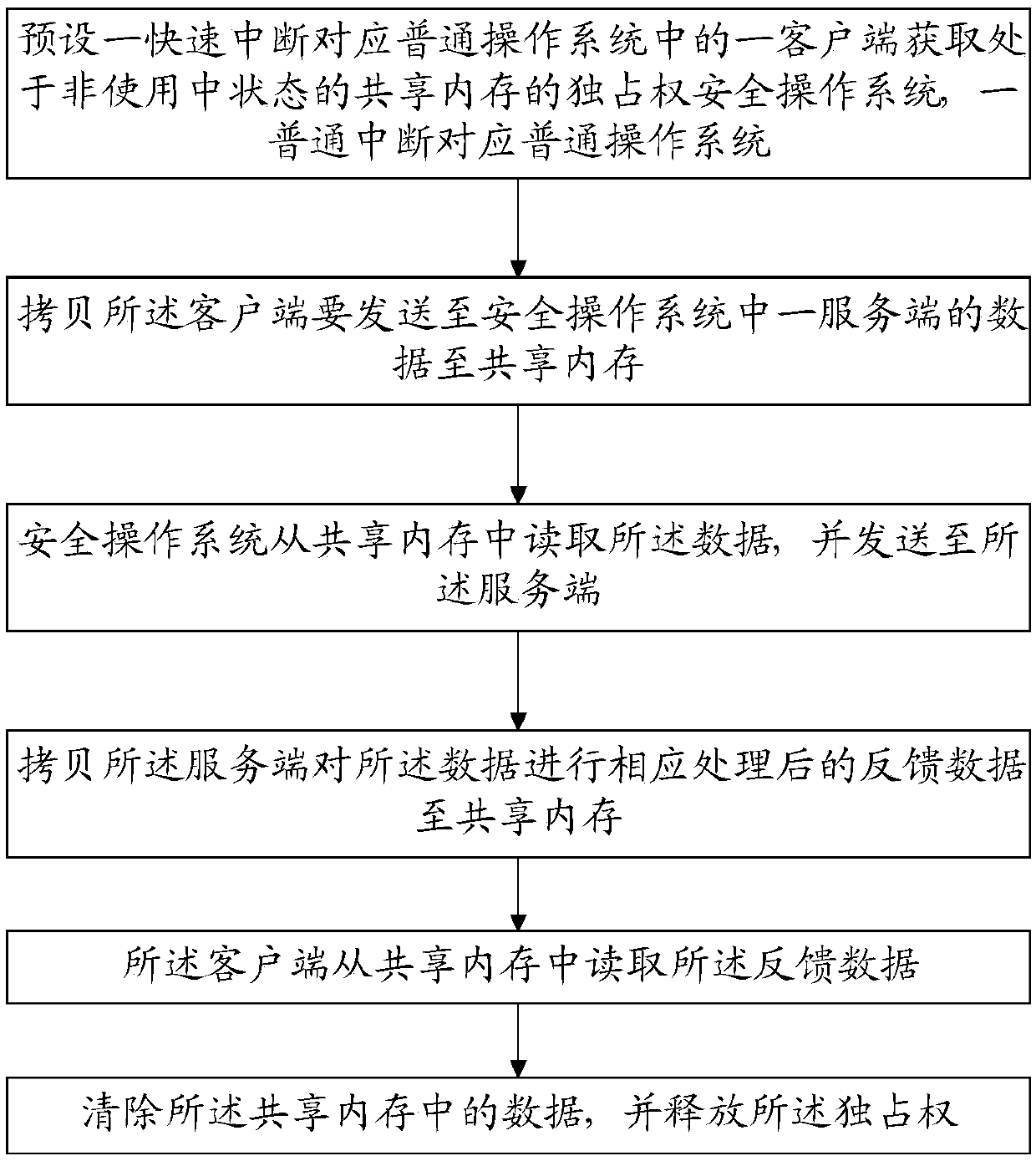
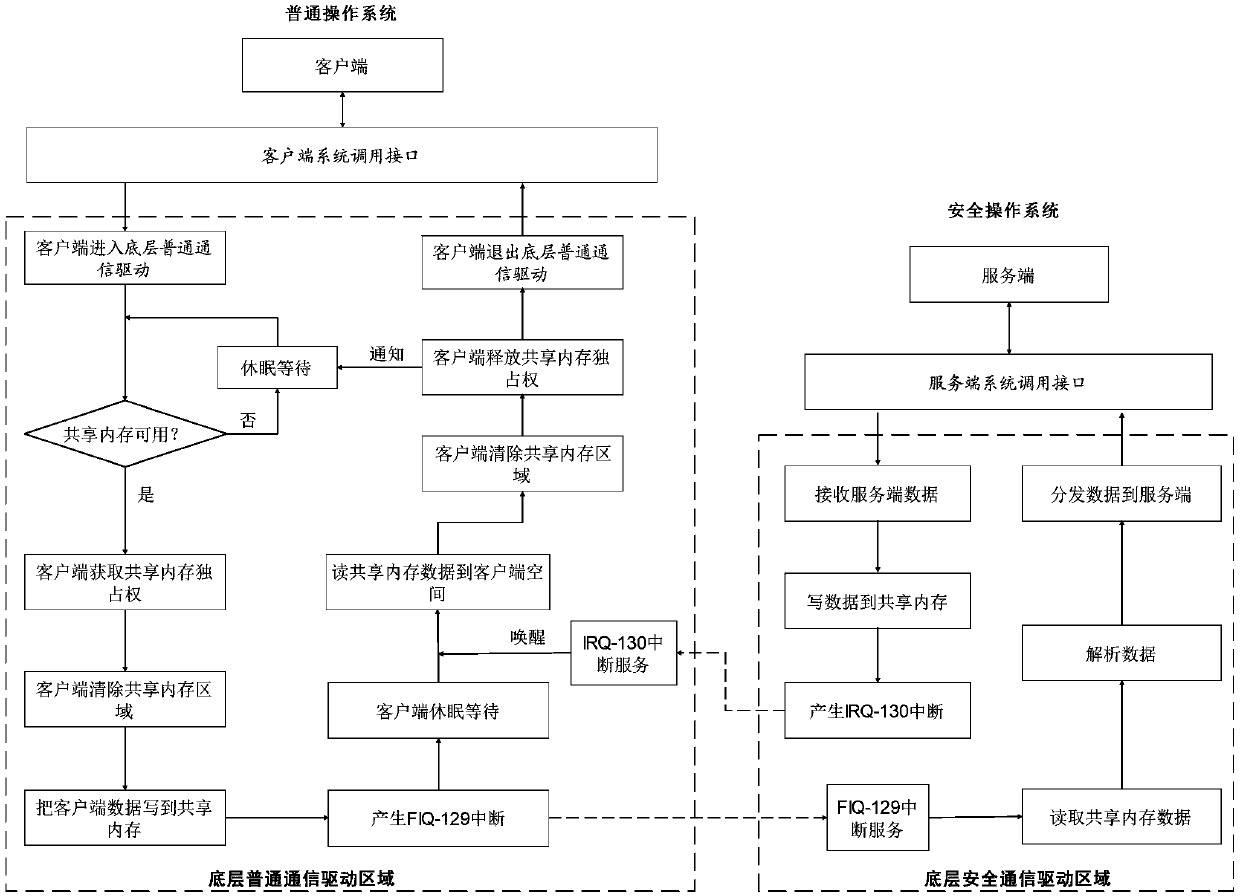
[0088] Please refer to figure 2 and image 3 , this embodiment provides a method for protecting the data security of the shared memory of dual systems, which can effectively prevent other client programs from reading the data in the shared memory, thereby ensuring the security of the data in the shared memory during the communication process.
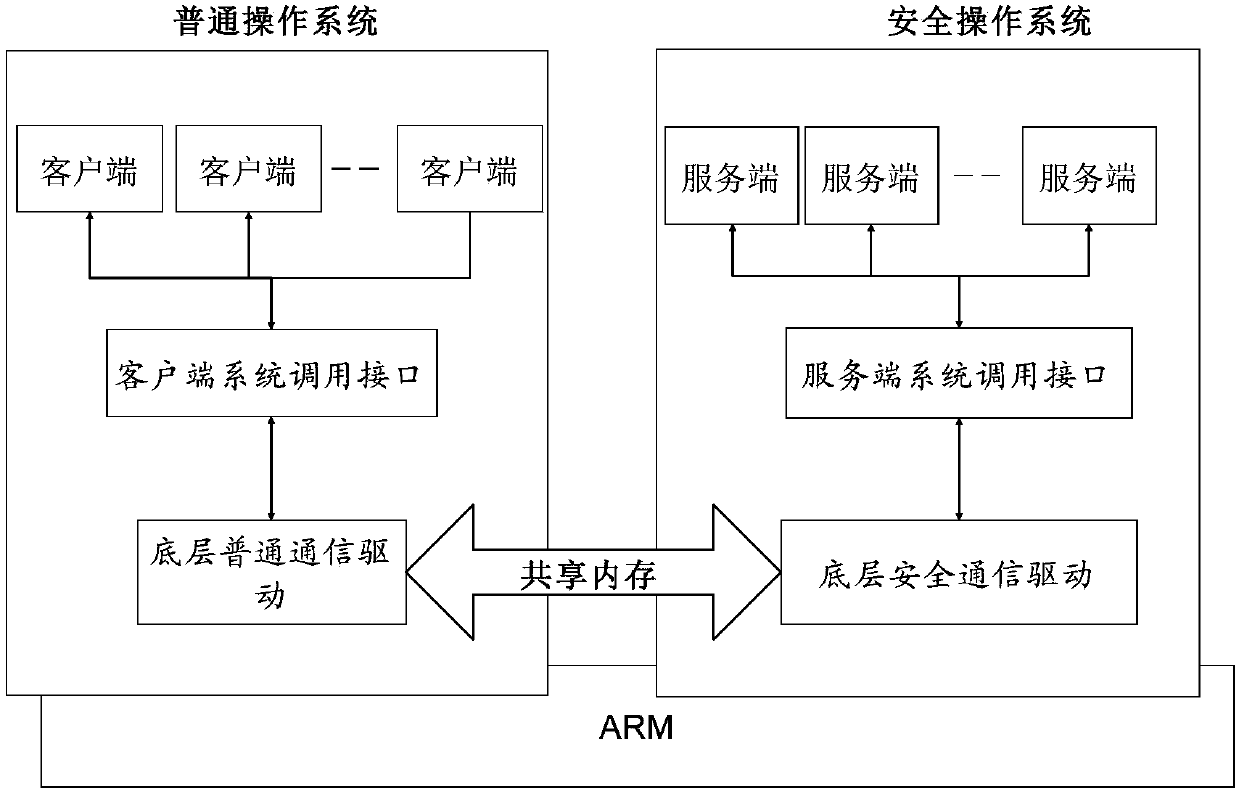
[0089] This embodiment is based on figure 2 The data communication model of the two systems shown is realized. Call the server system call interface (GPTEE Internal API) through the server program of the security operating system, call the client system call interface (GPTEE Client API) through the client program of the ordinary operating system, and pass the underlying ordinary communication driver of the ordinary operating system ( doscom-driver) and the underlying security communication driver (tee-driver) of the security operating system to communicate data.
[0090] The shared memory in this embodiment physically reflects a co...
Embodiment 2
[0115] This embodiment provides a specific application scenario based on the first embodiment. The application scenario is that the client A requests the server A to encrypt data.
[0116] Specifically, the following steps may be included:
[0117] 1. Client A enters the doscom-driver area through the GPTEE Client API interface (assuming that the shared memory is idle at this time);
[0118] 2. Client A obtains the exclusive right to shared memory;
[0119] 3. Client A clears the shared memory data;
[0120] 4. Client A encapsulates the data that needs to be sent to server A, and copies the encapsulated data to the shared memory area;
[0121] 5. The processor switches to the safe operating system to run, and the client enters dormancy and waits;
[0122] 6. The security operating system notifies the tee-driver to read the shared memory data;
[0123] 7. tee-driver reads shared memory data and parses the data;
[0124] 8. tee-driver sends the parsed data to server A;
[...
Embodiment 3
[0133] This embodiment is further expanded on the basis of the first embodiment, and provides a data interaction method based on the shared memory of the dual systems to solve the problem of how to coordinate the dual systems and protect data in the shared memory by using the shared memory for communication between the two systems. This embodiment can not only effectively prevent other client programs from reading data in the shared memory, but also coordinate multiple clients and two operating systems to perform orderly operations on shared memory processes.
[0134] This embodiment is also based on figure 2 The data communication model of the two systems shown is realized.
[0135] Simultaneously combine image 3 , the specific data interaction process is as follows:
[0136] S1: preset a fast interrupt and its corresponding fast interrupt processing program, a normal interrupt and its corresponding normal interrupt processing program, the fast interrupt processing progra...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More