A Physical Layer Security Method Based on Artificial Noise Power Allocation
A physical layer security and artificial noise technology, applied in power management, communication interference, confidential communication, etc., can solve the problems of poor confidentiality and high probability of confidentiality interruption, achieve enhanced security features, small probability of confidentiality interruption, and improve confidentiality Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
specific Embodiment approach 1
[0029] Specific implementation mode one: the specific process of a physical layer security method based on artificial noise power allocation in this implementation mode is as follows:
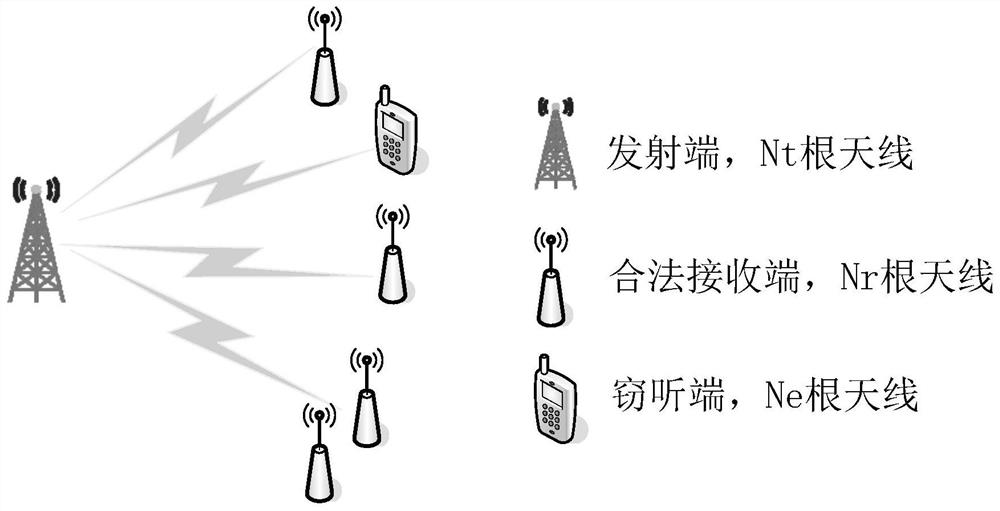
[0030] Step 1. Assume that there is a legal transmitter Alice, K legal receivers (Bob1, Bob2, ... BobK), and an eavesdropper Eve; the schematic diagram of the wireless broadcast communication system model is as follows figure 1 shown.
[0031] The number of antennas of Alice at the transmitting end is N t , the number of antennas for each legal receiver is N r , the number of antennas of the eavesdropper is N e ;
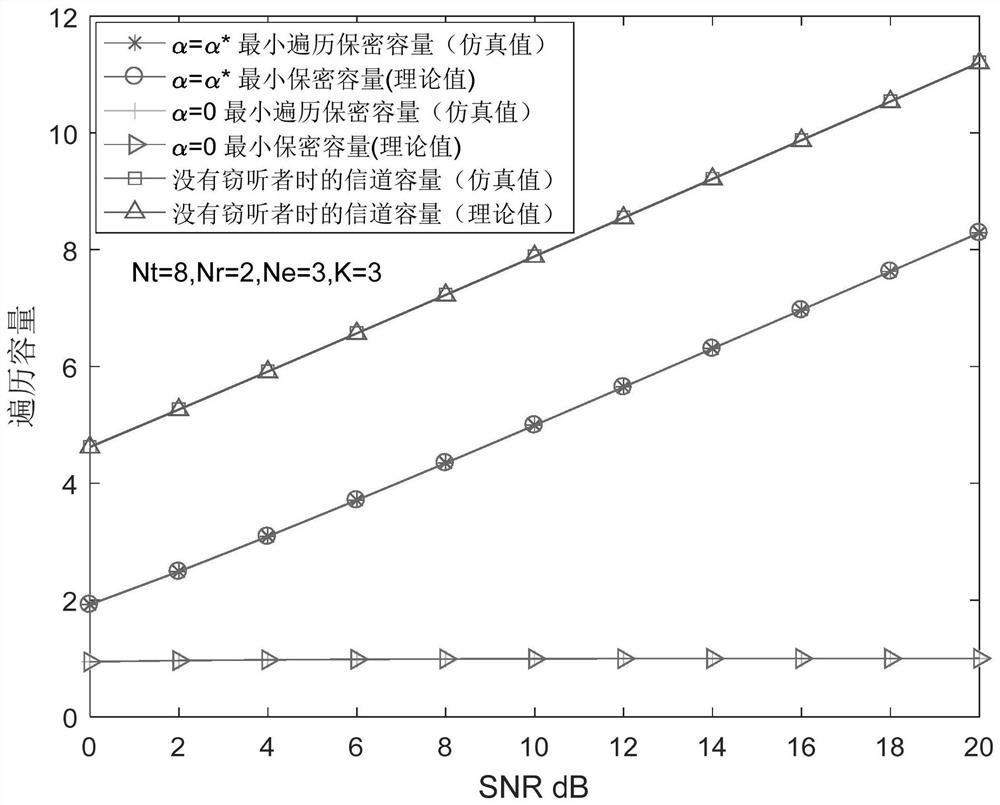
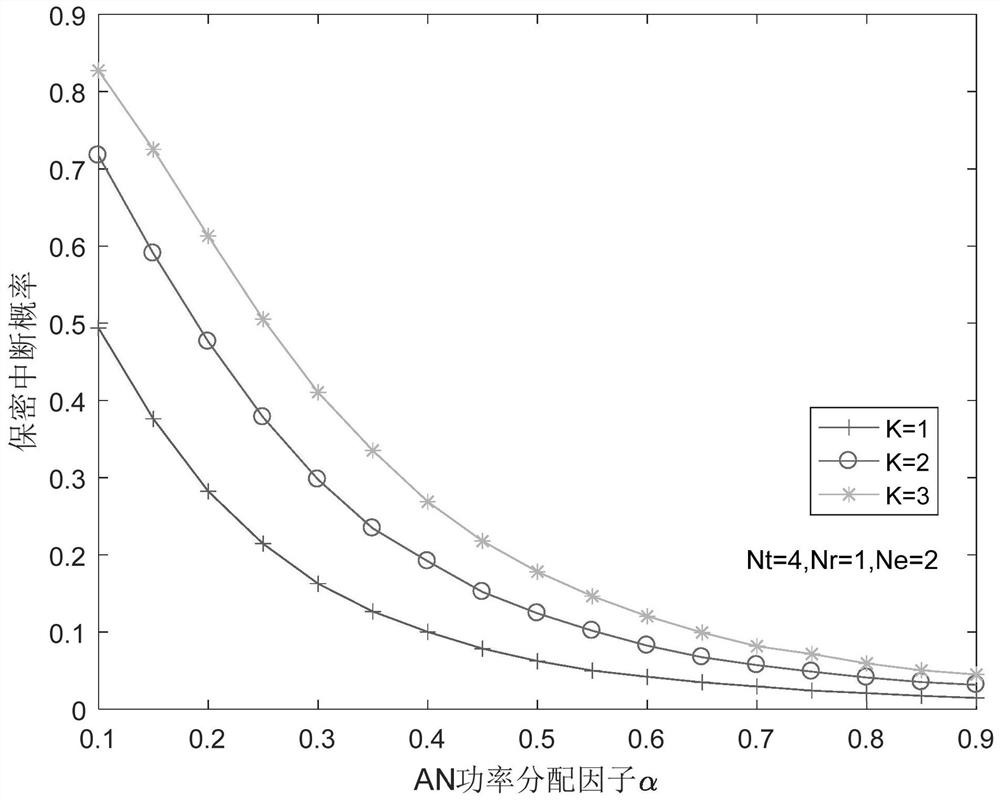
[0032] Assuming that the total transmit power constraint of the transmitter Alice is limited to P, where the power of the artificial noise signal transmitted by the transmitter Alice is αP, and the power of the useful signal is (1-α)P, then the transmitter Alice (the source with multiple antennas ) The transmitted signal x is expressed as
[0033]
[0034] where x s is a us...
specific Embodiment approach 2
[0040] Specific embodiment 2: The difference between this embodiment and specific embodiment 1 is that in the step 2, it is assumed that the receiving antenna gain of the eavesdropping end Eve and each legal receiver Bob are the same, and the calculation signal x passes through the wireless broadcast between Alice and Bob Legal channel transmission, the received signal reaching the kth legitimate receiver Bob, and the signal x is transmitted through the wiretapping channel between Alice and Eve, and the received signal reaches the eavesdropper Eve; the specific process is:
[0041] The signal x is transmitted through the wireless broadcast legal channel between Alice and Bob, and the received signal reaching the kth legal receiver Bob is expressed as:
[0042]
[0043] The signal x is transmitted through the eavesdropping channel between Alice and Eve, and the received signal reaching the eavesdropper Eve is expressed as:
[0044]
[0045] in, Represents the channel ma...
specific Embodiment approach 3
[0048] Specific embodiment three: the difference between this embodiment and specific embodiment one or two is that the H b,k and H e Each element in represents the channel complex gain when the signal is transmitted, H b,k Each element in satisfies the mean value of 0 and the variance of cyclic complex Gaussian distribution; H e Each element in satisfies the mean value of 0 and the variance of cyclic complex Gaussian distribution; n b,k Each element in has a mean of 0 and a variance of complex Gaussian vector of n e Each element in has a mean of 0 and a variance of complex Gaussian vector;
[0049] variance It is the system measurement value, indicating the variance of the Gaussian noise in the environment. If it is a simulation, this value is defined by itself. The variance It is the system measurement value, indicating the variance of the Gaussian noise in the environment. If it is a simulation, this value is defined by itself;
[0050] Assuming that the leg...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More