Electronic contract data encryption storage method and signing client
An electronic contract and data encryption technology, applied in the Internet field, can solve problems such as insecurity, unfavorable contract data information security, easy to be leaked, etc., to achieve the effect of eliminating security risks, protecting information security, and ensuring uniqueness
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0042] The present invention will be described in detail below in conjunction with the accompanying drawings and embodiments.
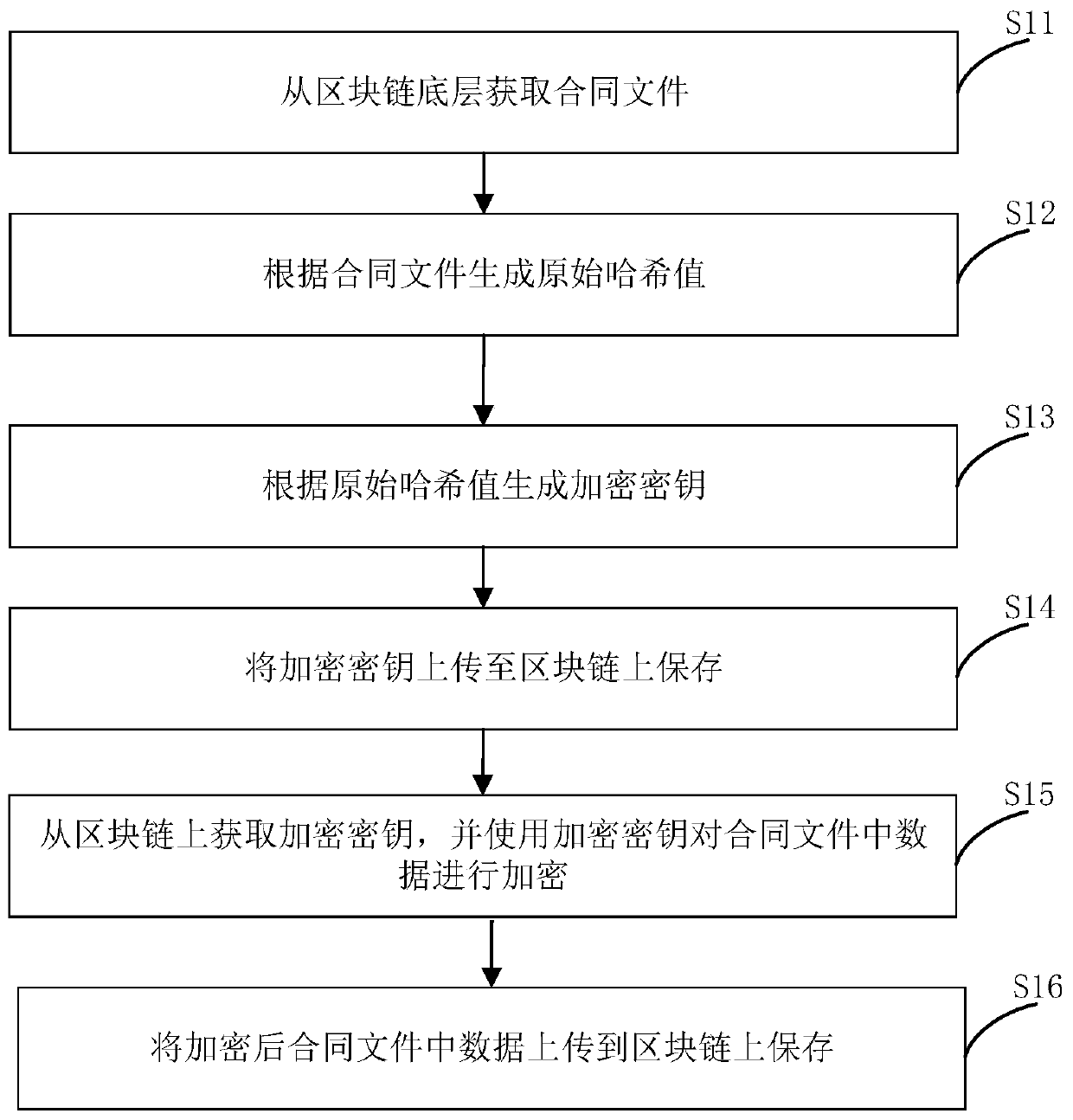
[0043] figure 1 It is a flow chart of an electronic contract data encryption storage method provided by an embodiment of the present application.
[0044] Such as figure 1 As shown, the method of the present embodiment includes:
[0045] S11: Obtain contract documents from the bottom layer of the blockchain;
[0046] S12: Generate the original hash value according to the contract file;
[0047] The original hash value is generated according to the contract content in the contract file, because the content of each contract file is different, so each original hash value will also be different.
[0048] As an optional implementation of the present invention, the generating the original hash value according to the contract file includes: encrypting the contract file using the SHA-512 algorithm to generate the original hash value.
[0049] SHA (Secure...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More