Backward Computational Fuzzy Extractor and Method for Authentication
A device authentication and processor technology, applied in the field of cryptography, can solve problems such as insufficient security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0011] For the purpose of promoting an understanding of the principles of the present disclosure, reference will now be made to the embodiments illustrated in the drawings and described in the following written specification. It will be understood that no limitation of the scope of the present disclosure is thereby intended. It is further to be understood that this disclosure includes any alterations and modifications to the illustrated embodiments and includes further applications of the principles of this disclosure as would commonly occur to one skilled in the art to which this disclosure pertains.
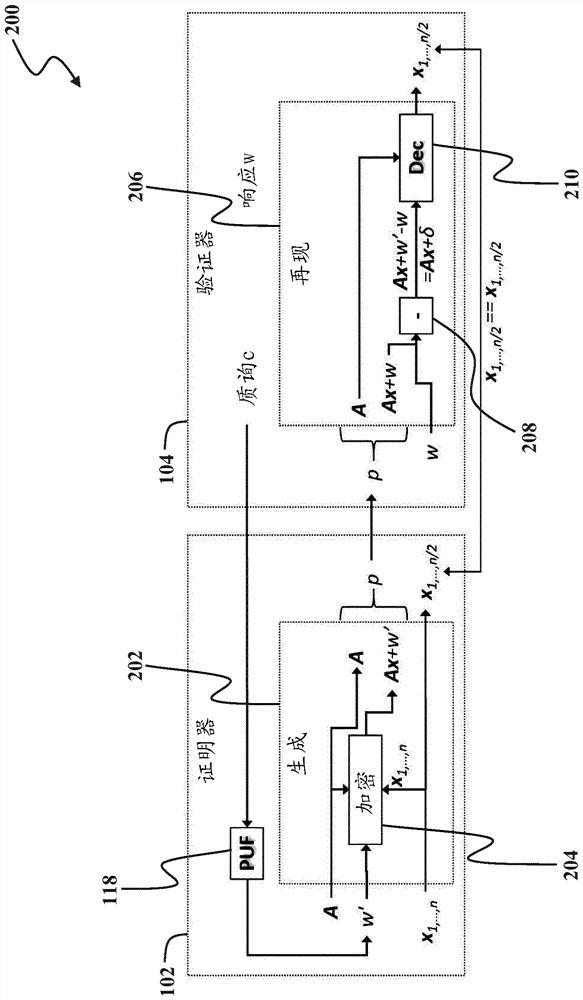
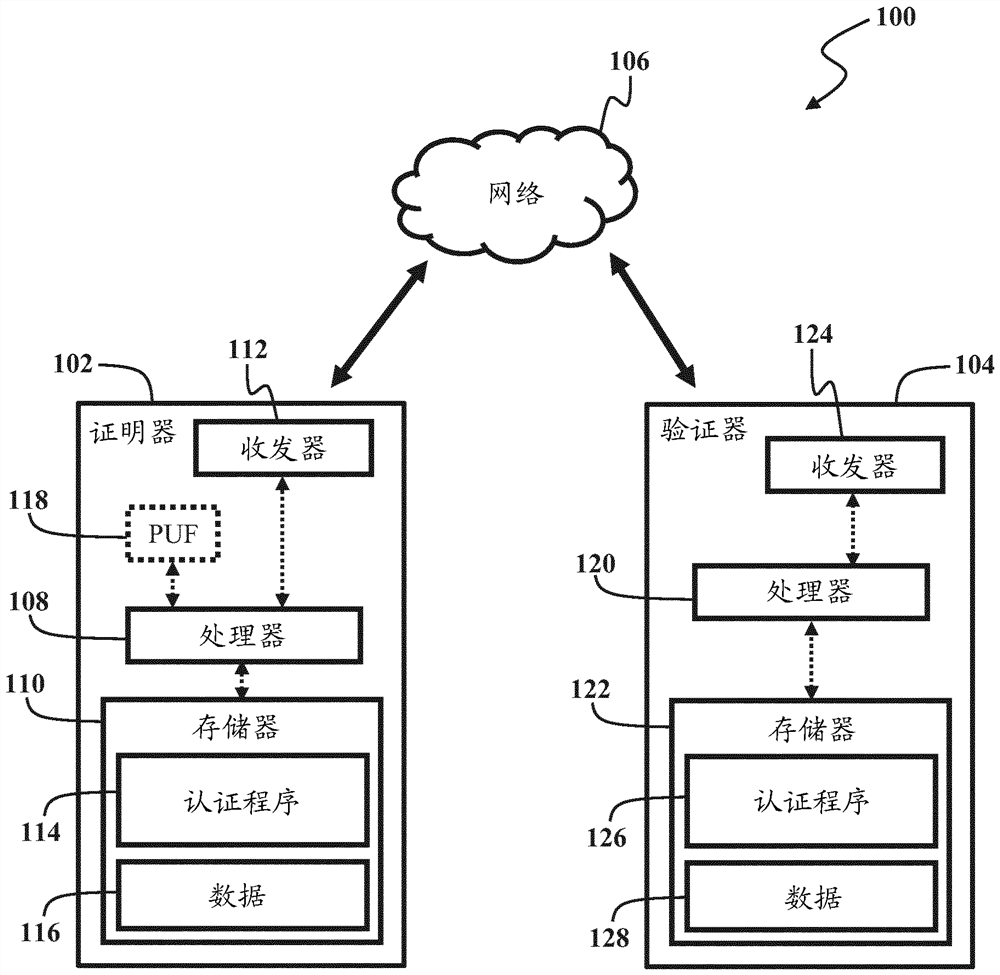
[0012] figure 1 A system 100 is shown that includes a proving device 102 (also referred to herein as a "certifier") and a verification device 104 (also referred to herein as a "verifier"). Attestation device 102 and verification device 104 via insecure communication channels such as network 106 (eg, the Internet, wireless local area network, or wireless mesh network) or direct...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More