Security protection method and device and access network equipment
A technology for access network equipment and security protection, which is applied in the field of communication and can solve problems such as on-demand activation that cannot achieve user plane security protection
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
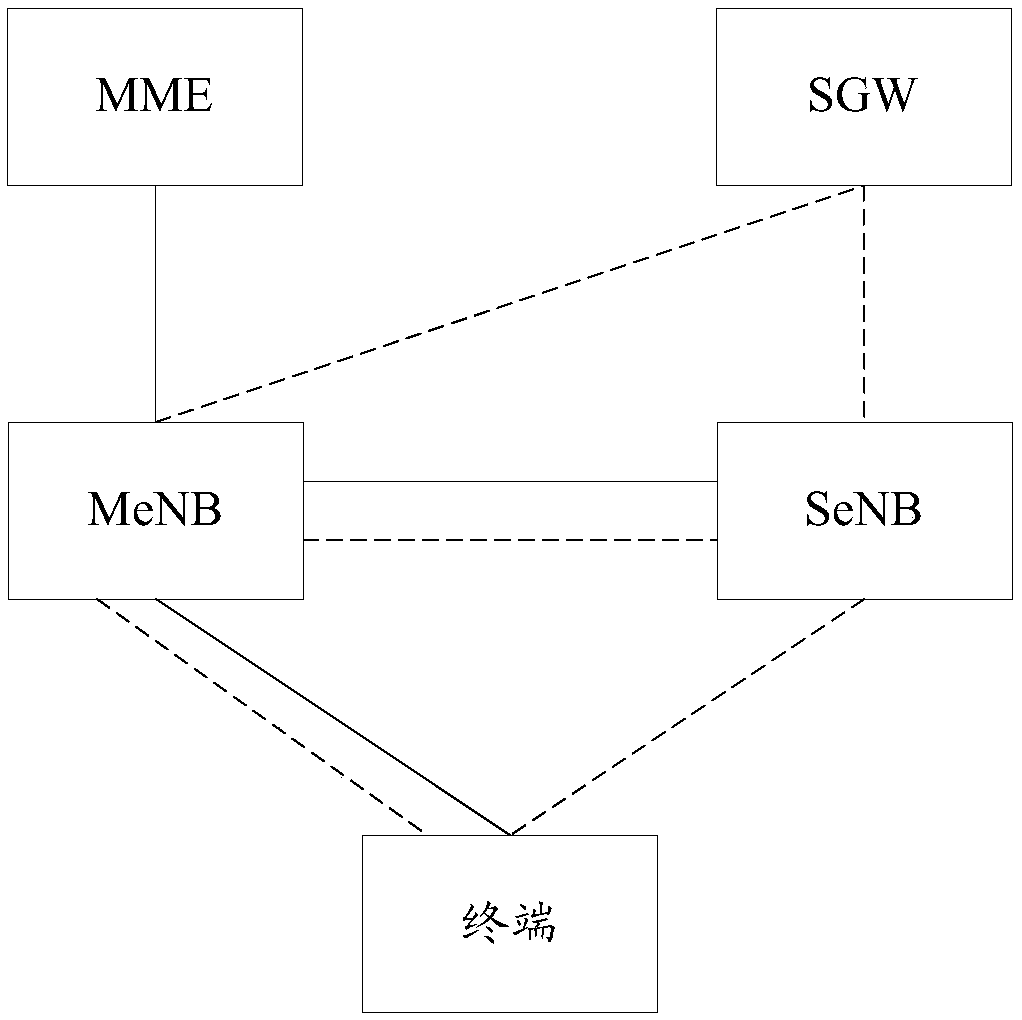
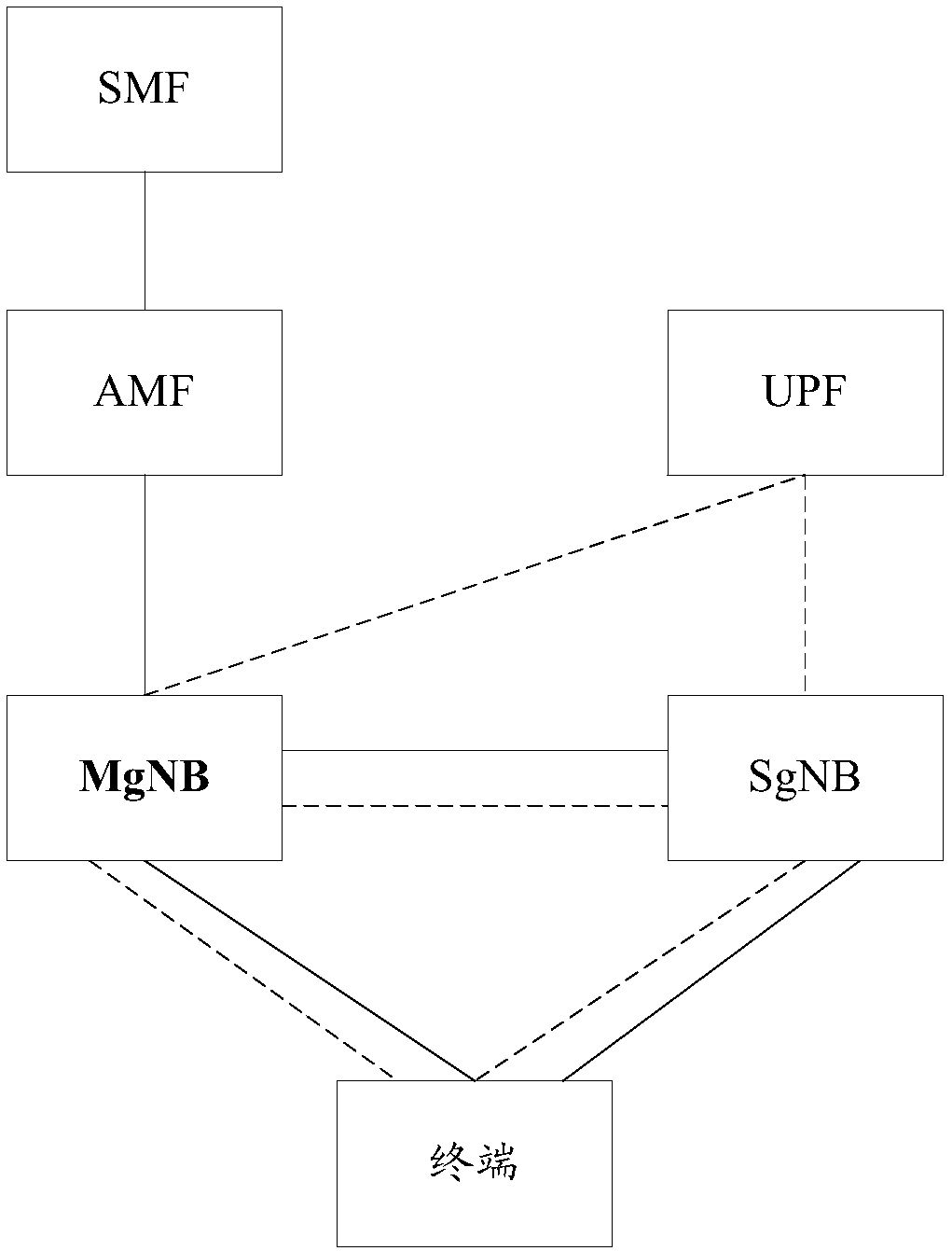
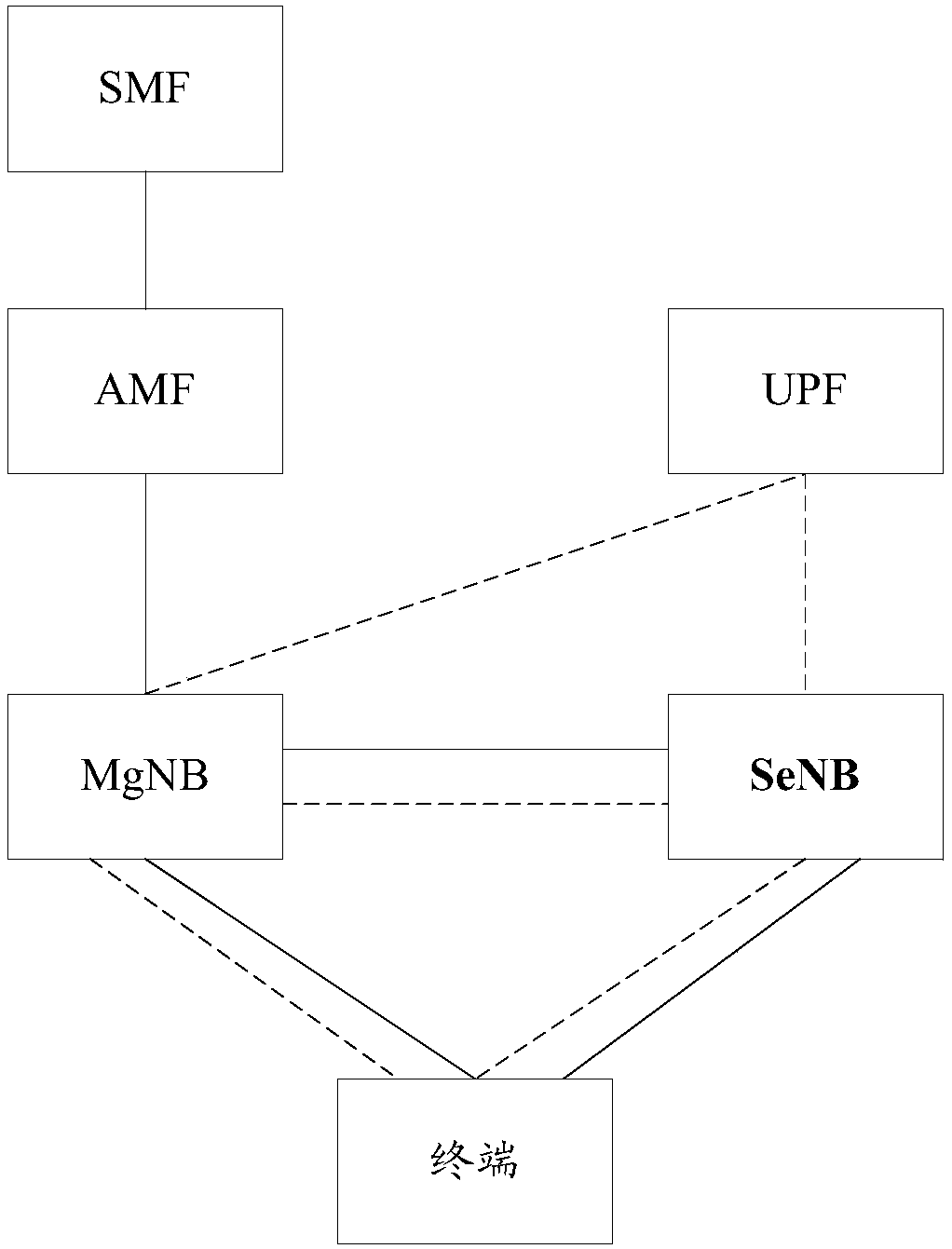
[0084] The application will be described in further detail below in conjunction with the accompanying drawings. The specific operation methods in the method embodiments can also be applied to the device embodiments or system embodiments. Wherein, in the description of the present application, unless otherwise specified, "at least one" means one or more, and "multiple" means two or more. " / " means or, for example, A / B can mean A or B; "and / or" in this article is just a description of the relationship between associated objects, which means that there can be three relationships, for example, A and / Or B, can mean: A exists alone, A and B exist at the same time, and B exists alone, where A and B can be singular or plural. "At least one of the following" or similar expressions refer to any combination of these items, including any combination of single or plural items. For example, at least one of a, b, and c can represent: a, b, c, a and b, a and c, b and c, or a, b and c, wher...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More