Remote login method, device and system
A technology of remote login and bastion machine, applied in the computer field, can solve problems such as weak password strength, achieve strong password strength and improve security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
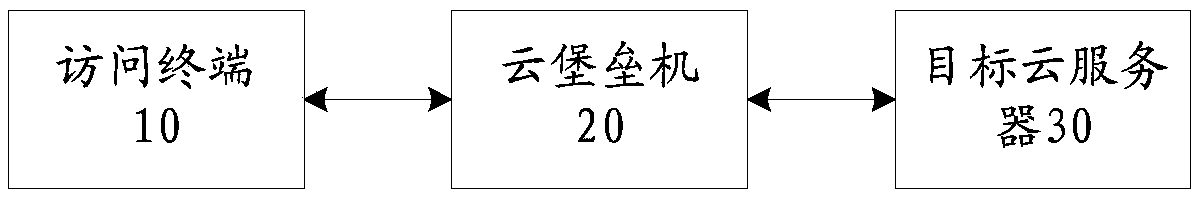
[0033] According to an embodiment of the present application, an embodiment of a remote login system is also provided, figure 1 It is a schematic diagram of a remote login system according to Embodiment 1 of the present application, combined with figure 1 As shown, the system includes:
[0034] The access terminal 10 is used to determine the target cloud server to be logged in.
[0035] Specifically, the above-mentioned access terminal may be a terminal used by the user to access the target cloud server, and the access terminal needs to determine the target cloud server to log in to the cloud bastion machine, so that the cloud bastion machine can establish communication with the target cloud server. After the cloud bastion machine establishes communication with the target cloud server, it can forward the access data of the access terminal to the target cloud server, and forward the response result returned by the target cloud server to the access terminal, thus realizing the ...
Embodiment 2
[0064] According to the embodiment of the present application, a method embodiment of a remote login method is also provided. It should be noted that the steps shown in the flow chart of the accompanying drawings can be executed in a computer system such as a set of computer-executable instructions, and , although a logical order is shown in the flowcharts, in some cases the steps shown or described may be performed in an order different from that shown or described herein.
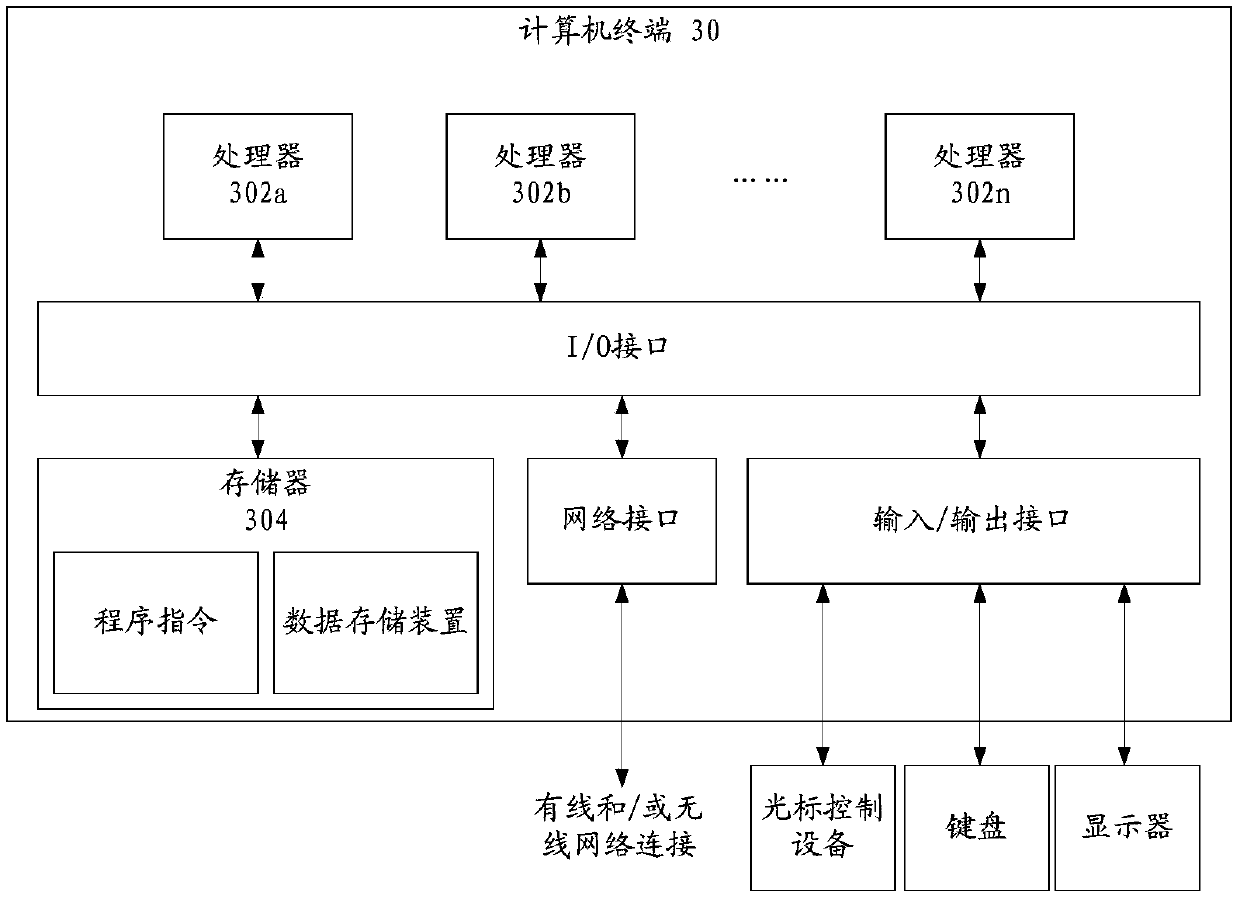
[0065] The method embodiment provided in Embodiment 1 of the present application may be executed in a mobile terminal, a computer terminal, or a similar computing device. image 3 A hardware structural block diagram of a computer terminal (or mobile device) for realizing the remote login method is shown. like image 3 As shown, the computer terminal 30 (or mobile device 30) may include one or more (shown by 302a, 302b, ..., 302n in the figure) processor 302 (the processor 302 may include but not limited ...
Embodiment 3
[0096] This application provides Figure 5 The remote login method shown. Figure 5 It is a flow chart of a remote login method according to Embodiment 3 of the present application.
[0097] In step S51, the target cloud server receives the public key in the key pair distributed by the cloud bastion host, wherein the key pair includes a public key and a private key corresponding to the public key, and the target cloud server is the cloud server to be logged in by the access terminal.
[0098] Specifically, the access terminal selects the target cloud server by logging into the cloud bastion host.
[0099] In the above step S51, the cloud bastion host distributes the public key to the target cloud server, and the private key of the target cloud server is saved by the cloud bastion host.
[0100]In an optional embodiment, when the cloud server registers with the cloud bastion machine, the cloud bastion machine will generate a key pair for the cloud server, including a public k...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More