Multi-host shared storage system and data integrity protection method
A data integrity and shared storage technology, applied in the field of information security, can solve problems such as restricted reading and writing, system crashes, data leakage, etc., to prevent illegal reading and tampering, enhance security, and protect integrity.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
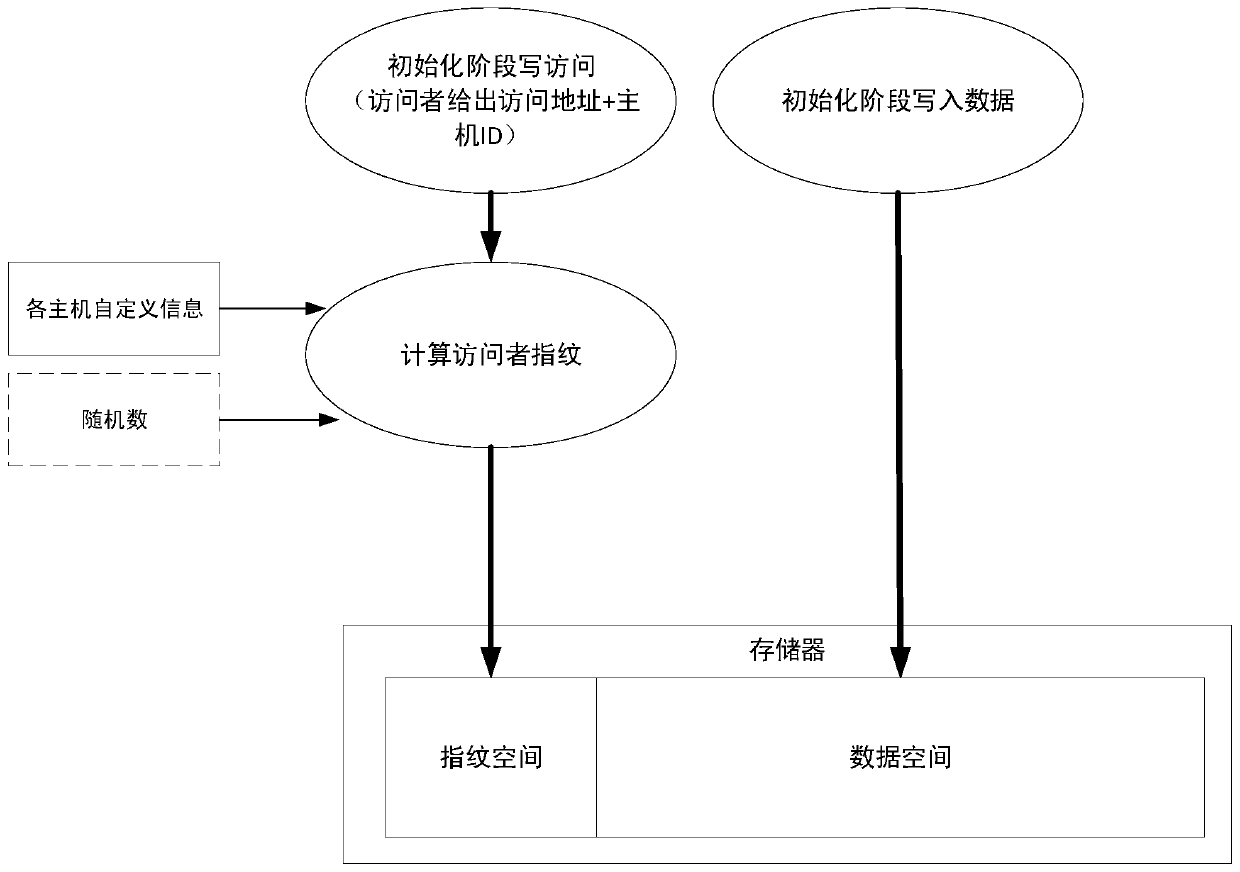
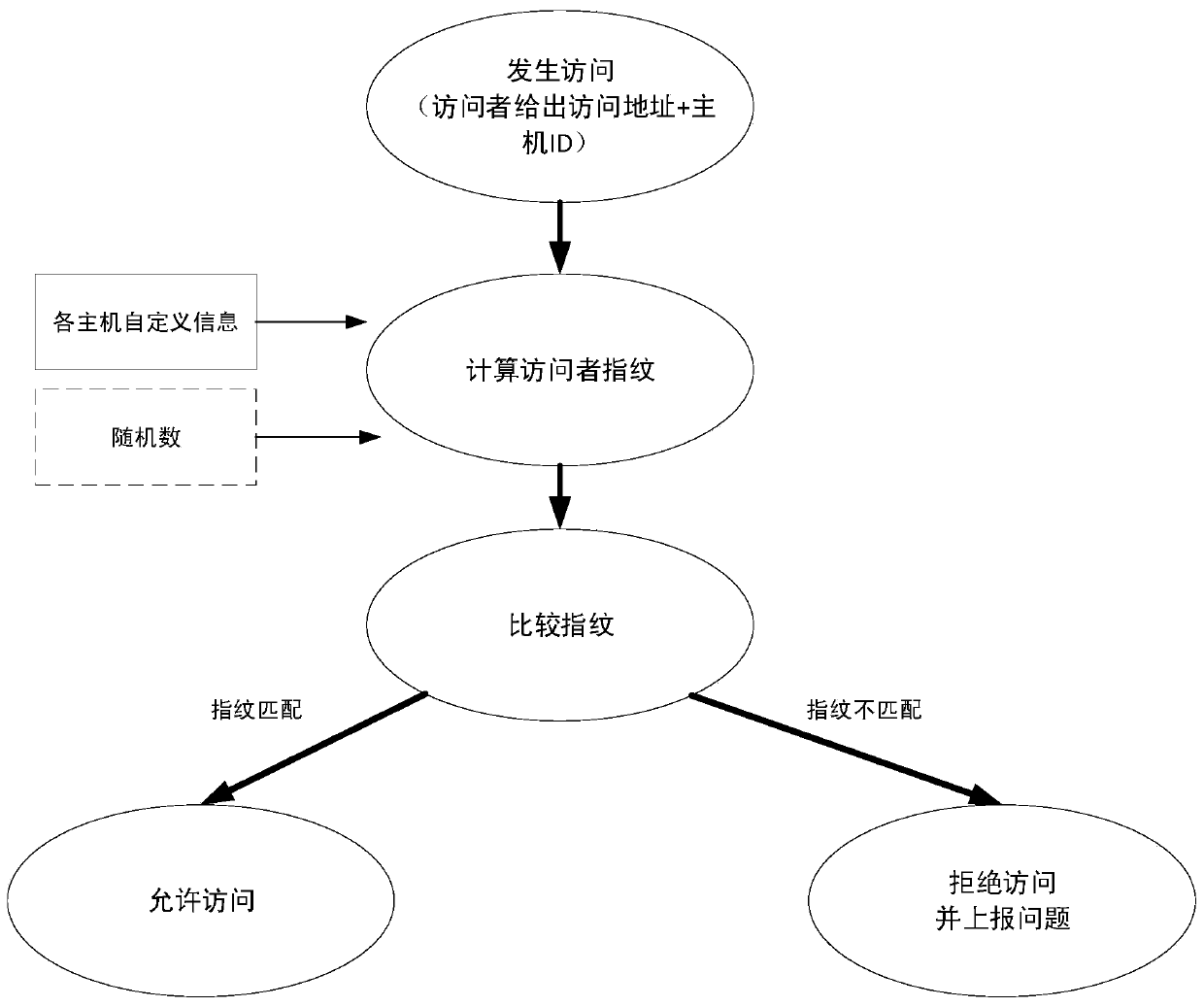
Method used
Image
Examples
Embodiment Construction
[0024] In order to make the purpose and technical solutions of the embodiments of the present invention clearer, the technical solutions of the embodiments of the present invention will be described clearly and completely in conjunction with the accompanying drawings of the embodiments of the present invention. Obviously, the described embodiments are part of the embodiments of the present invention, rather than all of the embodiments. Based on the described embodiments of the present invention, all other embodiments obtained by a person of ordinary skill in the art without creative work shall fall within the protection scope of the present invention.
[0025] Those skilled in the art can understand that, unless otherwise defined, all terms (including technical and scientific terms) used herein have the same meanings as those commonly understood by those of ordinary skill in the art to which the present invention belongs. It should also be understood that terms such as those defi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More