Block chain system user identity anonymity and traceability method, corresponding storage medium and electronic device
A system user and user identity technology, applied in user identity/authority verification, transmission system, digital transmission system, etc., can solve the problems of not considering user identity supervision, low proof efficiency, complex implementation, etc., and achieve traceability Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
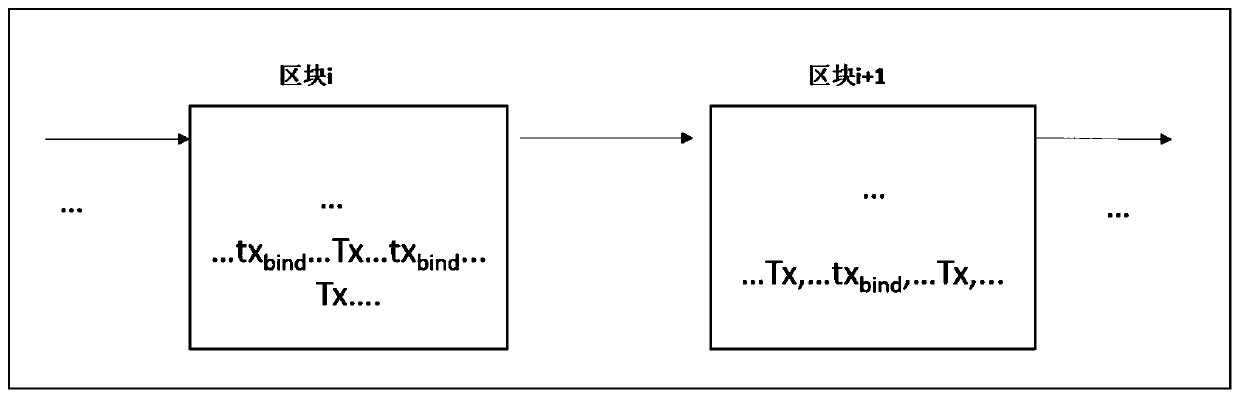
Embodiment Construction
[0034] In order to make the above objects, features and advantages of the present invention more obvious and understandable, the structure of this invention will be further described below through specific embodiments and accompanying drawings.
[0035] The present invention takes following technical scheme:
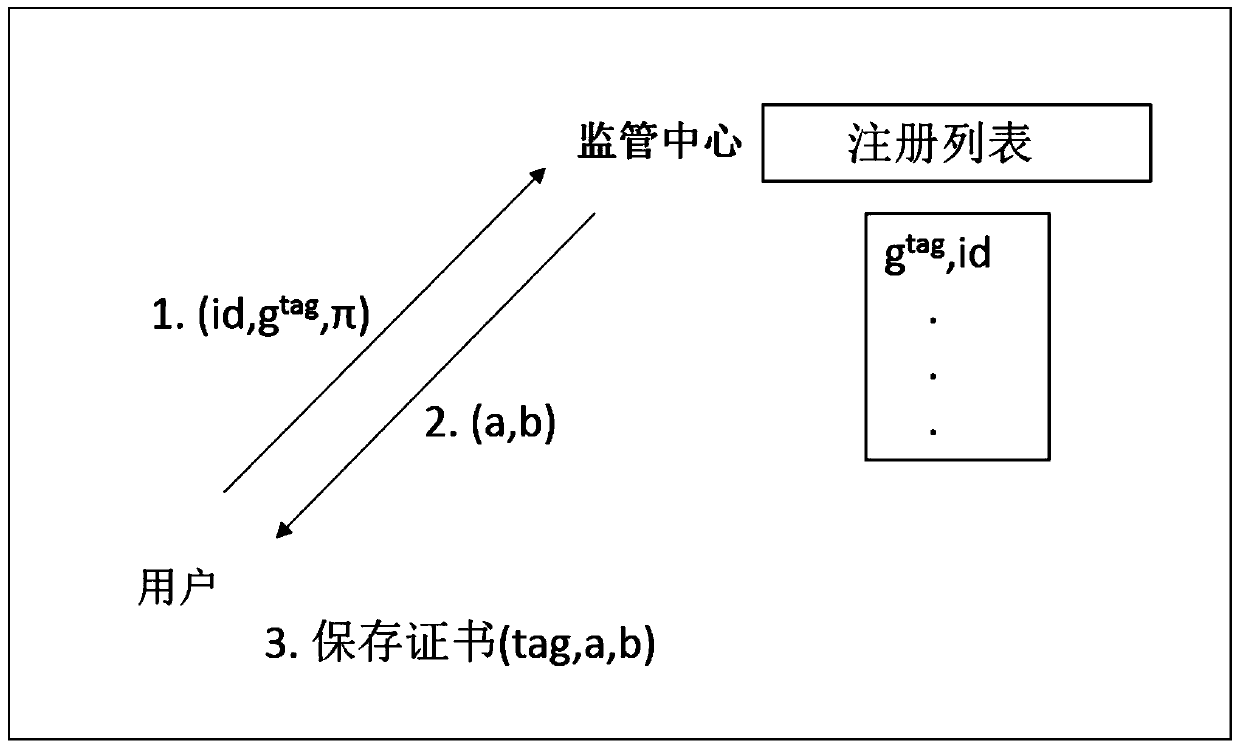
[0036] 1) Generation of certificate
[0037] The idea of a certified signature in Groth's 2007 paper "Fully Anonymous Group Signatures Without Random Oracles" is used to generate the user's certificate. Its certifiable signature scheme contains 4 algorithms (create, register, sign, verify). Wherein, the present invention only uses the certificate generation part of the scheme, that is, creation and registration.
[0038] A) Create Algorithm Setup(1 k ):
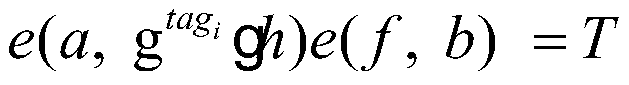
[0039] The central Issuer produces a bilinear group gk:=(p,G,G T ,e,g)←G(1 k ), where G is a bilinear group generation algorithm, k is a system security parameter, p is a large prime number, G, G T Both are gro...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More