Implementation method and application of security authentication function return value
A technology of security authentication and implementation method, applied in the field of information security, it can solve the problems of result reliability discount, no interaction, and inability to determine the validity of the return value of the called function, so as to reduce the possibility, prevent security attacks, and reduce the Tampering effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0027] The technical solutions in the embodiments of the present invention are clearly and completely described below in conjunction with the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are part of the embodiments of the present invention, but not all of them. Based on the embodiments of the present invention, all other embodiments obtained by those skilled in the art without making creative efforts belong to the protection scope of the present invention.
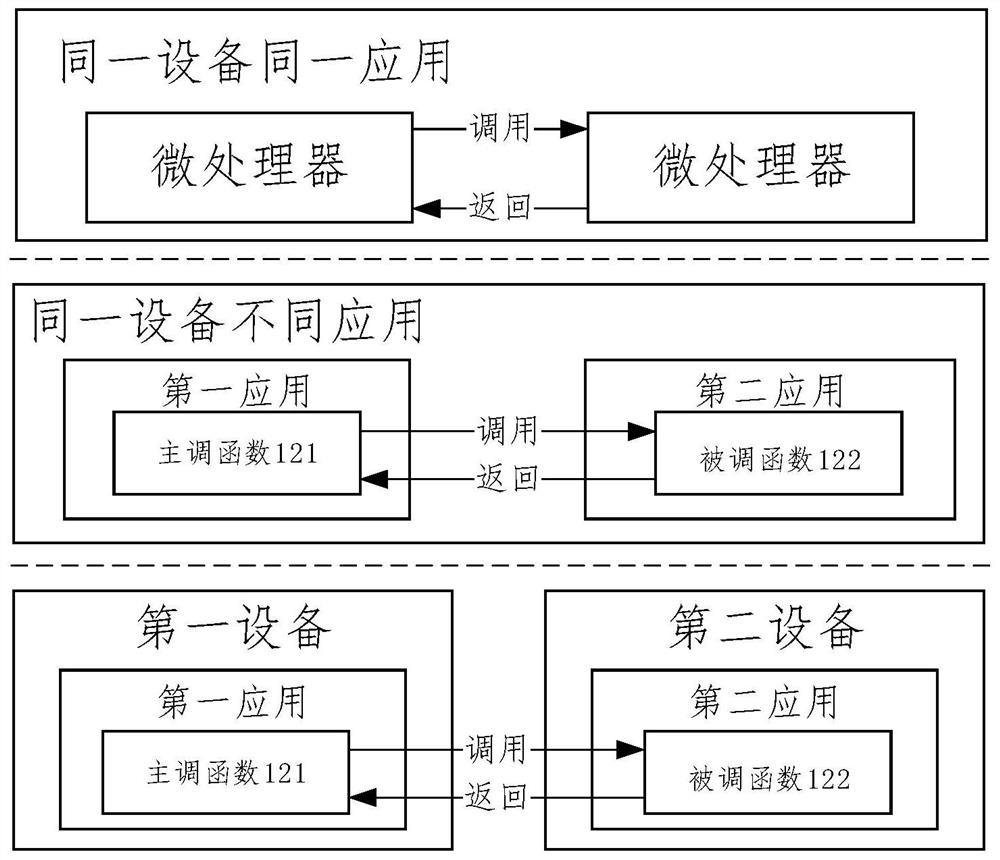
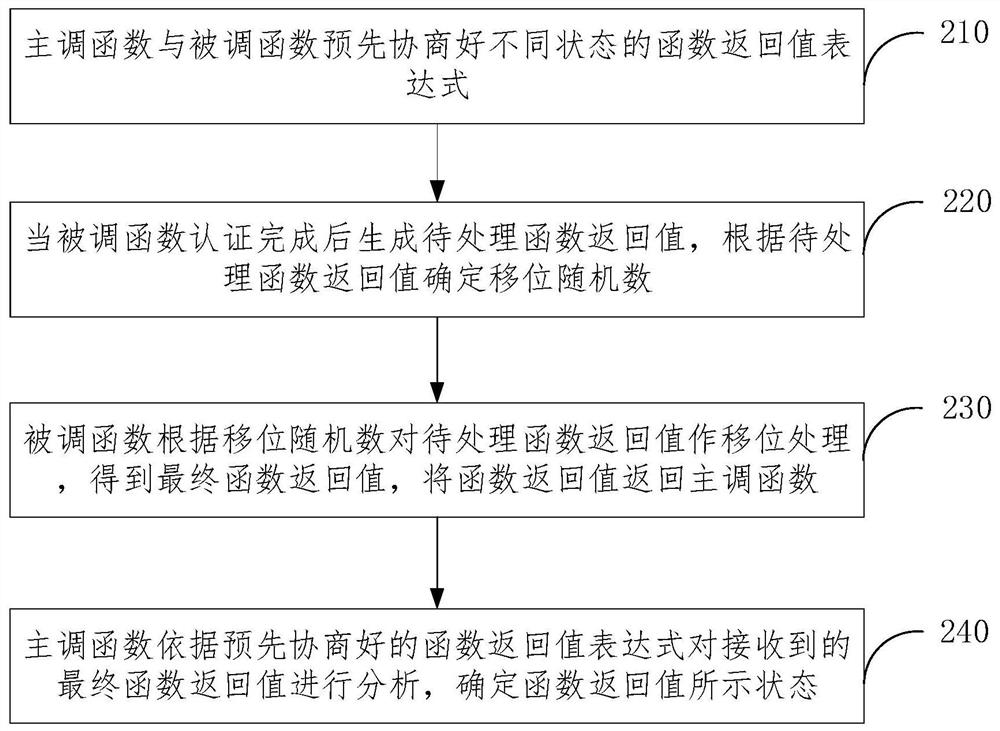
[0028] The embodiment of this application provides a method for realizing the return value of the security authentication function, such as figure 1 As shown, it is applicable to any application that requires the return value of the function, including function calls within the same application, function calls between different applications on the same device, and function calls between different applications on different devices.
[0029] For the function call in ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More